Introduction
In an era marked by heightened scrutiny of financial institutions regarding their risk management practices, the selection of appropriate software is crucial. Effective risk management software not only assists in identifying and mitigating potential threats but also ensures compliance with the continuously evolving regulatory landscape. As banks navigate this intricate environment, the challenge lies in choosing a solution that aligns with their specific operational needs and regulatory obligations.
Key features differentiate top risk management software, enabling banks to leverage these tools effectively. By understanding these features, institutions can enhance their decision-making processes and maintain stability in an uncertain market.
Understanding Risk Management Software: Key Features and Functions
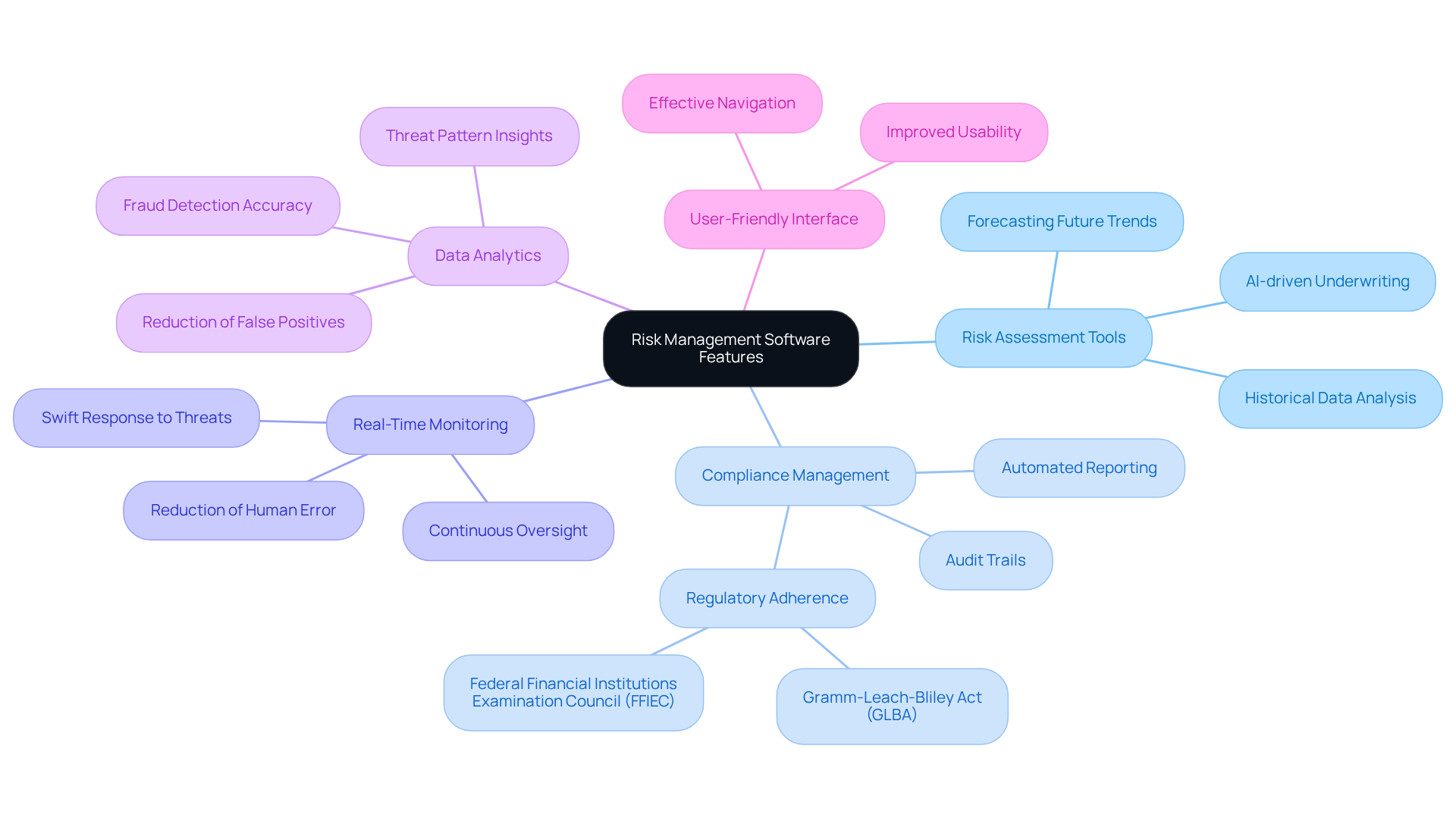
Software for banks plays a vital role in identifying, assessing, and mitigating risks associated with monetary operations. Key features include:
- Risk Assessment Tools: These tools empower banks to evaluate potential risks by analyzing historical data and forecasting future trends, thereby significantly enhancing decision-making processes. AI-driven underwriting tools, for instance, can double approval rates and reduce risk-related losses by 20%.
- Compliance Management: This feature guarantees adherence to regulatory requirements, such as the Dodd-Frank Act and the Federal Examination Council (FFIEC) standards. It provides automated reporting and maintains comprehensive audit trails. Banks typically allocate an estimated 6 to 10 percent of their revenue to compliance operations, underscoring the importance of effective systems.
- Exposure Monitoring: Continuous oversight of exposure enables banks to respond swiftly to threats, which is essential in today’s volatile financial landscape. Industry specialists note that “FinTech enables companies to identify threats much quicker, significantly reducing human error and facilitating compliance with constantly evolving regulations.”
- Advanced Analytics: Advanced analytics capabilities support informed decision-making by uncovering insights into threat patterns and potential impacts, which are crucial for proactive oversight. For example, machine learning algorithms enhance fraud detection accuracy and significantly reduce false positives.
- User-Friendly Interface: A well-designed user interface improves usability, making it easier for staff to navigate and effectively utilize the software.
Understanding these characteristics is essential for banks to select software for risk management that aligns with their strategies and regulatory requirements. As financial entities face increasing regulatory scrutiny and operational challenges, investing in robust mitigation solutions becomes critical for maintaining standards and ensuring operational stability. The evolving landscape of evaluation tools for 2026 further emphasizes the need for banks to adapt and innovate in their approach to managing uncertainties.
Comparing Leading Risk Management Solutions for Banks
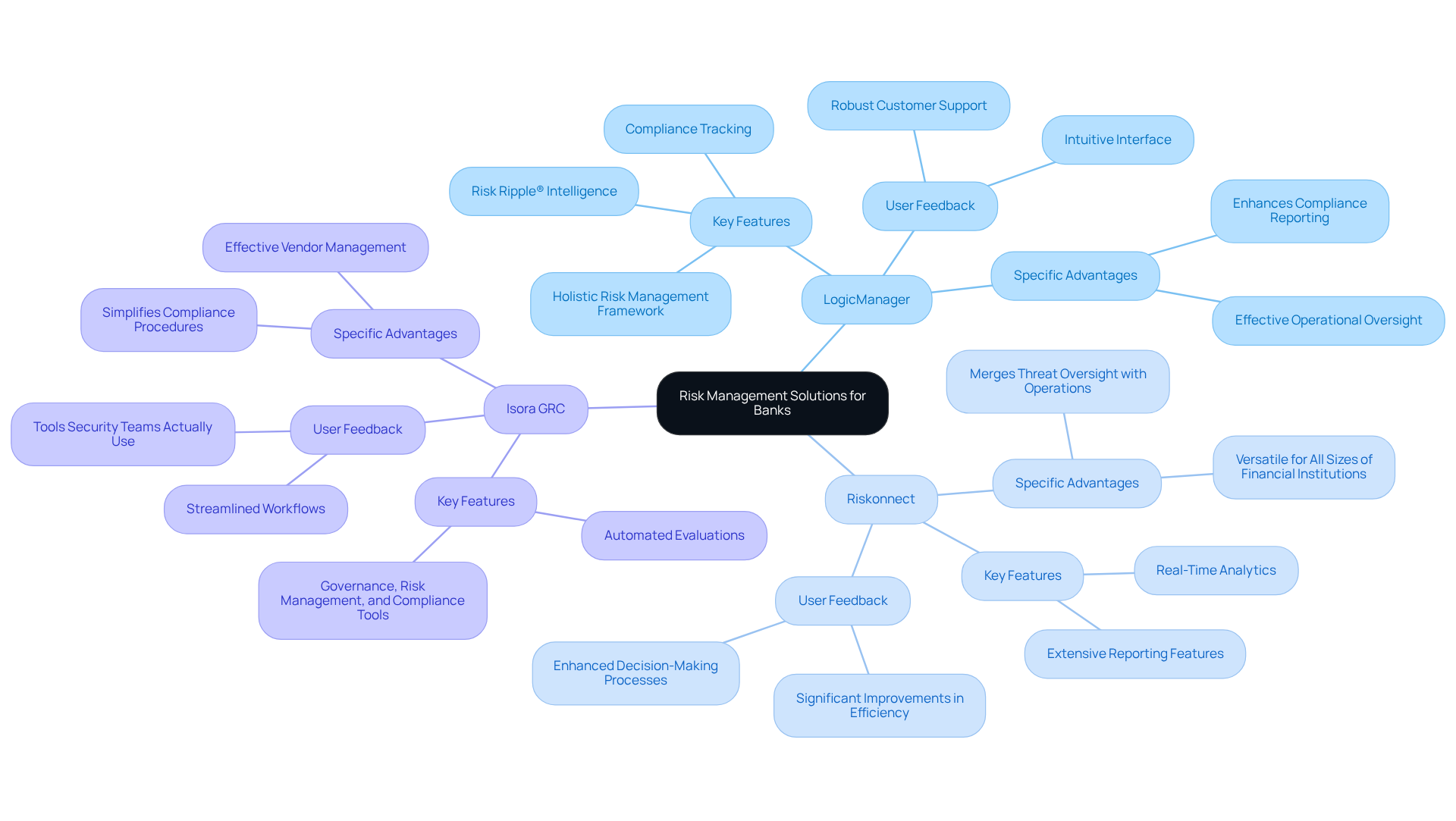
In the evolving landscape of risk management software, three solutions have emerged as frontrunners, each offering distinct capabilities and user satisfaction ratings.
LogicManager stands out for its holistic risk management framework, excelling in risk assessment. Users commend its intuitive interface and robust customer support, which facilitate seamless integration into existing workflows. Real-world applications in banks have demonstrated its effectiveness in mitigating risks. Notably, LogicManager features patented Risk Ripple® Intelligence, which charts connections between threats and controls, providing a comprehensive perspective on oversight.
Riskonnect distinguishes itself through its ability to merge threat oversight with operational processes, offering enhanced visibility. Its adaptability caters to organizations of all sizes, making it a versatile option for organizations aiming to enhance their risk handling capabilities. Users have reported significant improvements in efficiency and decision-making processes, highlighting its effectiveness within the financial sector.
Isora GRC focuses on governance, risk, and compliance, providing tailored tools for regulatory management. This solution is particularly advantageous for navigating complex regulatory environments, as it simplifies compliance procedures and enhances oversight. Users have noted its effectiveness in automating evaluations and managing vendor challenges, which is crucial in today’s regulatory landscape. As one user remarked, “Isora GRC offers the best tools for compliance.”
Each of these solutions presents distinct advantages, making it essential for banks to assess their specific requirements and operational environments when selecting risk management software. With the market projected to grow by 2031 at a CAGR of 16.55%, the importance of choosing the right solution cannot be overstated.
Evaluating Compliance and Efficiency: Pros and Cons of Each Solution
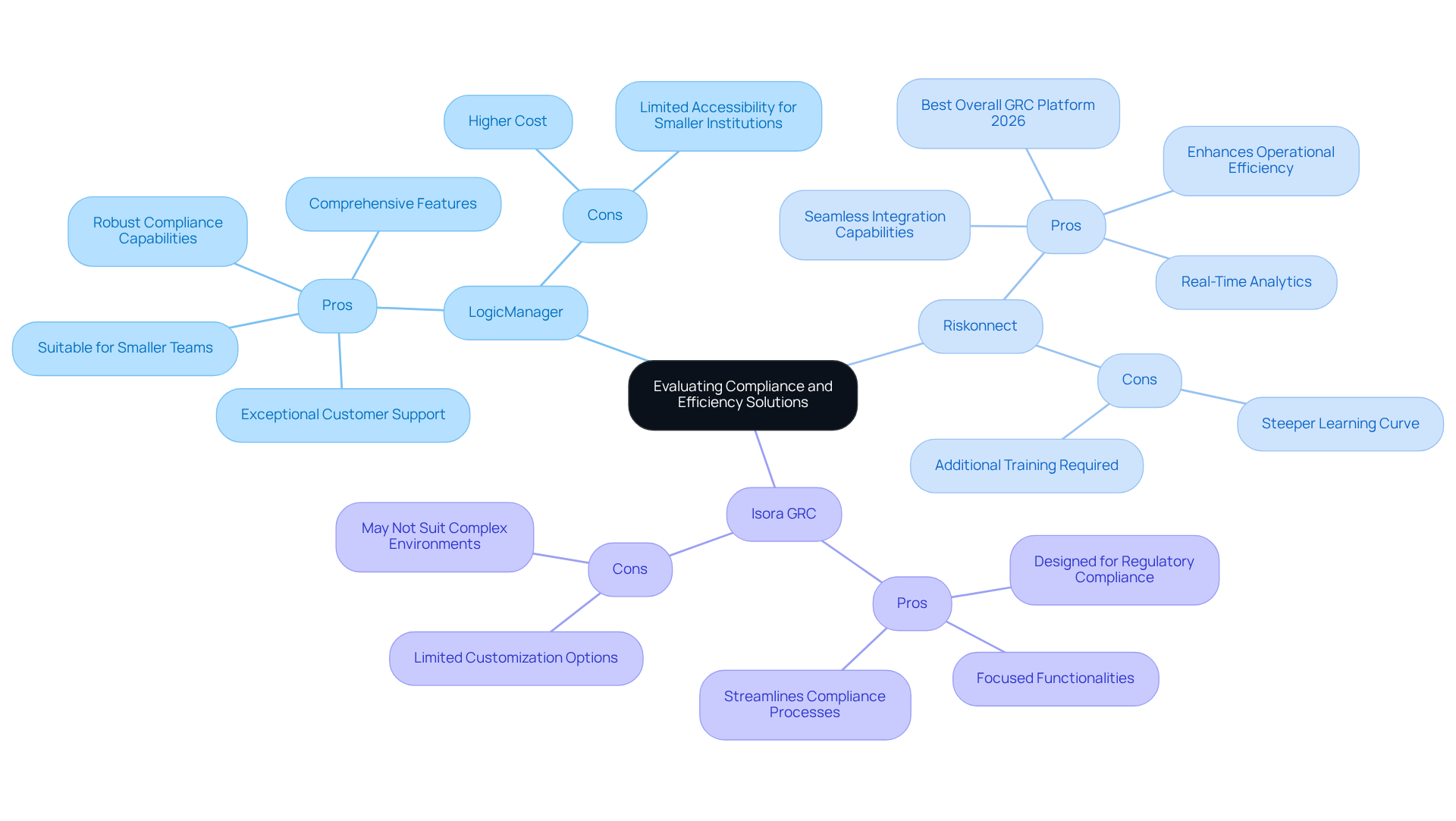
LogicManager:
Pros: LogicManager provides a user-friendly interface, exceptional customer support, and robust compliance capabilities. This makes it a strong contender for banks that prioritize risk management to ensure regulatory adherence. Additionally, it is suitable for smaller teams needing an easy start, which can be critical for institutions with limited resources.
Cons: However, its higher cost may pose a challenge for smaller institutions, potentially limiting accessibility for those with tighter budgets.
Riskonnect:
Pros: Recognized as the Best Overall GRC Platform in 2026, Riskonnect is noted for its advanced analytics and seamless integration capabilities. These features significantly enhance operational efficiency and enable banks to utilize data to respond swiftly to emerging risks.
Cons: On the downside, some users have reported a steeper learning curve due to the platform’s extensive features, which may necessitate additional training and adjustment time for teams.
Isora GRC:
Pros: Specifically designed for compliance management, Isora GRC is ideal for banks navigating stringent regulations. It provides focused functionalities that effectively address regulatory requirements.
Cons: Conversely, the platform’s limited customization options may not accommodate the diverse needs of all banks, potentially restricting its applicability in more complex environments.
Assessing these advantages and disadvantages enables banks to align their software selections with operational objectives and regulatory needs. This ensures they choose a solution that best suits their specific situations. Furthermore, as the compliance landscape evolves towards proactive strategies by 2026, understanding these factors becomes increasingly crucial.
Choosing the Right Risk Management Software: Recommendations for Banks
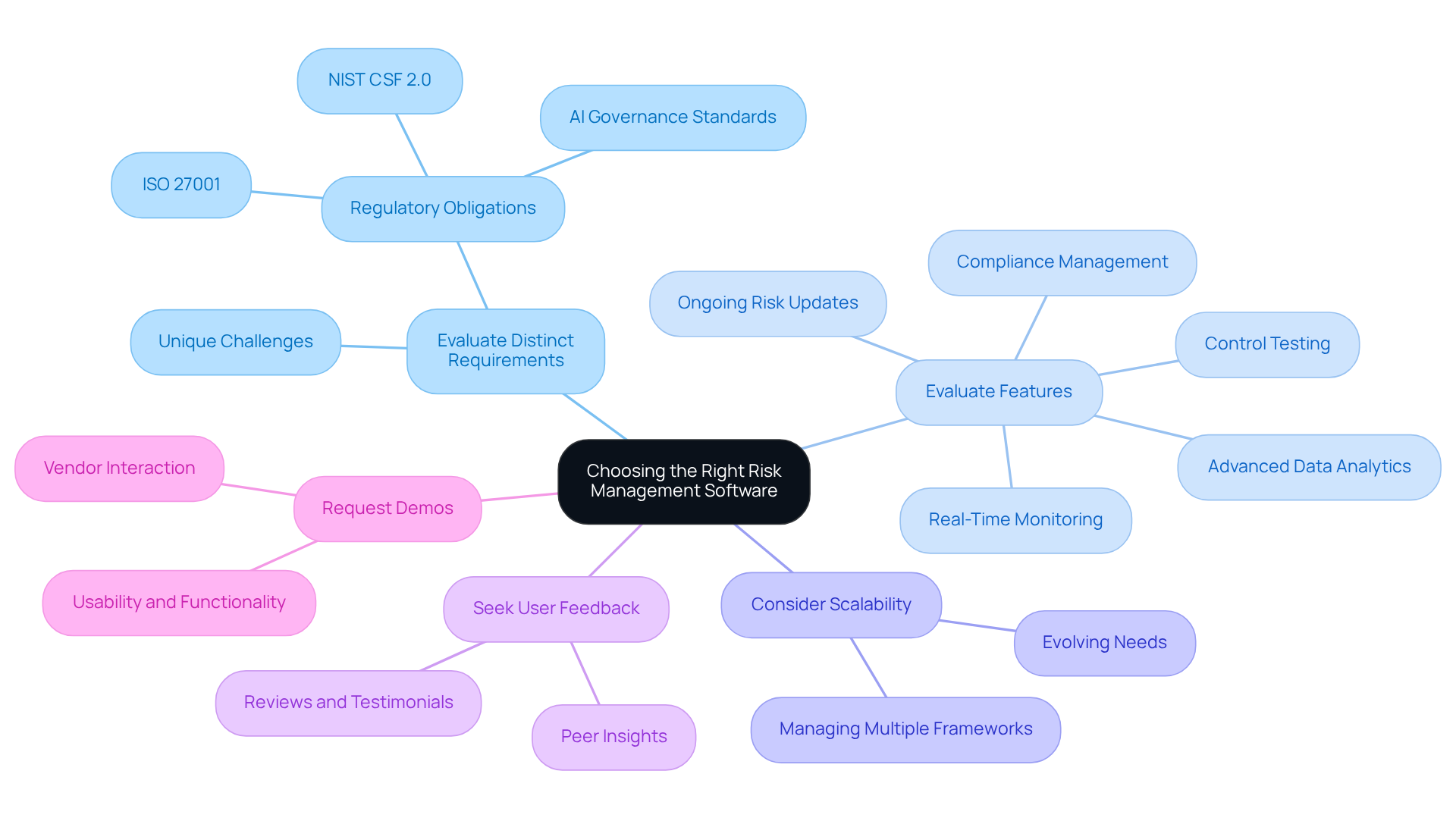
When selecting risk management software, banks should consider several key recommendations:
- Evaluate Distinct Requirements: It is crucial to determine the unique challenges your bank faces, including regulations such as NIST CSF 2.0, and cybersecurity threats. Understanding these complexities is vital for effective threat reduction, especially given the expectations from stakeholders regarding ongoing and documented due diligence processes.
- Evaluate Features: Prioritize software that provides essential features, including risk assessment, compliance management, and advanced analytics. Tools that facilitate data collection and control testing within a cohesive workflow model are particularly advantageous.
- Consider Scalability: Opt for a solution that can evolve alongside your institution, accommodating future needs and regulatory changes. By 2026, organizations will be managing multiple frameworks simultaneously, making scalability a critical factor in software selection.
- Seek Feedback: Investigate reviews and testimonials from other financial institutions to assess user satisfaction and the quality of support. Engaging with peers can yield valuable insights into the software’s effectiveness in practical applications.
- Request Demos: Interact with vendors to observe the software in action, ensuring it aligns with your usability and functionality expectations. This hands-on approach allows for a clearer understanding of how the software meets your institution’s operational requirements.
By adhering to these recommendations, banks can make informed decisions that enhance their risk management capabilities and ensure compliance with the evolving regulatory landscape.
Conclusion
Selecting the right risk management software for banks is of paramount importance, particularly in an environment marked by increasing regulatory pressures and operational complexities. Financial institutions must prioritize solutions that not only enhance compliance but also bolster overall risk management capabilities. By comprehensively understanding the unique features and functionalities of leading software options, banks can adeptly navigate the complex landscape of risk management.
Key features such as:
- Risk assessment tools
- Compliance management
- Real-time monitoring
- Data analytics
- User-friendly interfaces
are essential components of effective risk management software. A comparison of top solutions like LogicManager, Riskonnect, and Isora GRC reveals their distinct advantages and potential drawbacks, offering valuable insights for banks aiming to align their operational needs with regulatory requirements. Recommendations for evaluating software-including assessing specific needs, prioritizing essential features, and seeking user feedback-further empower institutions to make informed decisions.
As the financial sector continues to evolve, the selection of robust risk management software will be crucial in maintaining operational stability and ensuring compliance with dynamic regulatory frameworks. Financial institutions are encouraged to actively engage in evaluating their options, leveraging insights from peers, and prioritizing solutions that promote adaptability and innovation. By doing so, banks can effectively mitigate risks and enhance their resilience in an ever-changing landscape.
Frequently Asked Questions
What is the primary purpose of risk management software for financial institutions?
The primary purpose of risk management software for financial institutions is to identify, assess, and mitigate risks associated with monetary operations.
What are risk assessment tools, and how do they benefit banks?
Risk assessment tools enable banks to evaluate potential risks by analyzing historical data and forecasting future trends, enhancing decision-making processes. AI-driven underwriting tools can double approval rates and reduce risk-related losses by 20%.
How does compliance management work in risk management software?
Compliance management ensures adherence to regulatory requirements, such as the Gramm-Leach-Bliley Act (GLBA) and FFIEC standards, by providing automated reporting and maintaining comprehensive audit trails.
Why is real-time monitoring important for financial institutions?
Real-time monitoring allows banks to continuously oversee exposure to risks, enabling them to respond swiftly to emerging threats, which is crucial in today’s volatile financial landscape.
What role does data analytics play in risk management software?
Data analytics capabilities support informed decision-making by uncovering insights into threat patterns and potential impacts, which are essential for proactive oversight. AI-driven analytics enhance fraud detection accuracy and reduce false positives.
How does a user-friendly interface contribute to the effectiveness of risk management software?
A well-designed user interface improves usability, making it easier for staff to navigate and effectively utilize the software.
Why is it critical for financial institutions to invest in robust risk management solutions?
Investing in robust risk management solutions is critical for financial institutions to maintain standards and ensure operational stability, especially as they face increasing regulatory scrutiny and operational challenges.
List of Sources
- Understanding Risk Management Software: Key Features and Functions
- 2026 Bank Risk Outlook: What Banks Need to Watch Now (https://asurityadvisors.com/2026-risk-outlook-managing-uncertainty-across-a-shifting-risk-landscape)
- Banks race to adapt as traditional risks rebound and new threats accelerate, EY and IIF survey shows (https://ey.com/en_gl/newsroom/2026/02/banks-race-to-adapt-as-traditional-risks-rebound-and-new-threats-accelerate-ey-and-iif-survey-shows)
- Treasury issues new AI risk tools for banks (https://americanbanker.com/news/treasury-issues-new-ai-risk-tools-for-banks)
- Financial Technology Transforming Risk Management 2026 (https://sigmainfo.net/blog/how-financial-technology-is-transforming-risk-management-in-2026)
- The Best Compliance Management Systems of 2026 | 360factors (https://360factors.com/blog/compliance-management-systems-2026)
- Comparing Leading Risk Management Solutions for Banks
- Quantivate vs LogicManager vs Isora GRC: Which Platform Supports IT Risk Management Best? (https://saltycloud.com/isora-grc/compare/quantivate-vs-logicmanager-vs-isora-grc)
- Treasury issues new AI risk tools for banks (https://americanbanker.com/news/treasury-issues-new-ai-risk-tools-for-banks)
- It Risk Management Software Market Trends, Size & Brands 2026-2033 (https://linkedin.com/pulse/risk-management-software-market-trends-size-brands-rhs1f)
- Risk Management Software Market Size, Growth, Forecast Report & Share 2031 (https://mordorintelligence.com/industry-reports/risk-management-software-market)
- Compare LogicManager vs. Riskonnect in 2026 (https://slashdot.org/software/comparison/LogicManager-vs-Riskonnect)
- Evaluating Compliance and Efficiency: Pros and Cons of Each Solution
- The next era of compliance: How banks will stay ahead of financial crime in 2026 – Compliance Week (https://complianceweek.com/opinion/the-next-era-of-compliance-how-banks-will-stay-ahead-of-financial-crime-in-2026/36526.article)
- Best GRC Software Platforms in 2026 (https://riskonnect.com/best-grc-software-platforms-2026)
- Banks race to adapt as traditional risks rebound and new threats accelerate, EY and IIF survey shows (https://ey.com/en_gl/newsroom/2026/02/banks-race-to-adapt-as-traditional-risks-rebound-and-new-threats-accelerate-ey-and-iif-survey-shows)
- Quantivate vs LogicManager vs Isora GRC: Which Platform Supports IT Risk Management Best? (https://saltycloud.com/isora-grc/compare/quantivate-vs-logicmanager-vs-isora-grc)
- Choosing the Right Risk Management Software: Recommendations for Banks
- Best 5 Risk Compliance Software in 2026 (https://centraleyes.com/best-5-risk-compliance-software-in-2026)
- Best Risk Management Software for Banking 2026 | Riskonnect (https://linuxrockstar.com/risk-management-software-financial-services-banking)
- Treasury issues new AI risk tools for banks (https://americanbanker.com/news/treasury-issues-new-ai-risk-tools-for-banks)
- Top credit risk management tools in banks for 2026 | Kaltura (https://corp.kaltura.com/blog/top-credit-risk-management-tools-in-banks-for-2026)
- 10 Best Financial Risk Management Software Tools [2026] (https://hebbia.com/blog/financial-risk-management-software)
Introduction
In an industry characterized by high financial stakes and escalating cyber threats, hedge funds must prioritize software development security to protect their assets and reputation. By cultivating a security-first culture and embedding best practices throughout every phase of the software development life cycle, organizations can not only meet growing regulatory requirements but also strengthen their defenses against potential breaches.
Nevertheless, with many executives recognizing the infrequency of training on these essential practices, how can hedge funds effectively close the gap and establish a robust security framework that genuinely safeguards their operations?
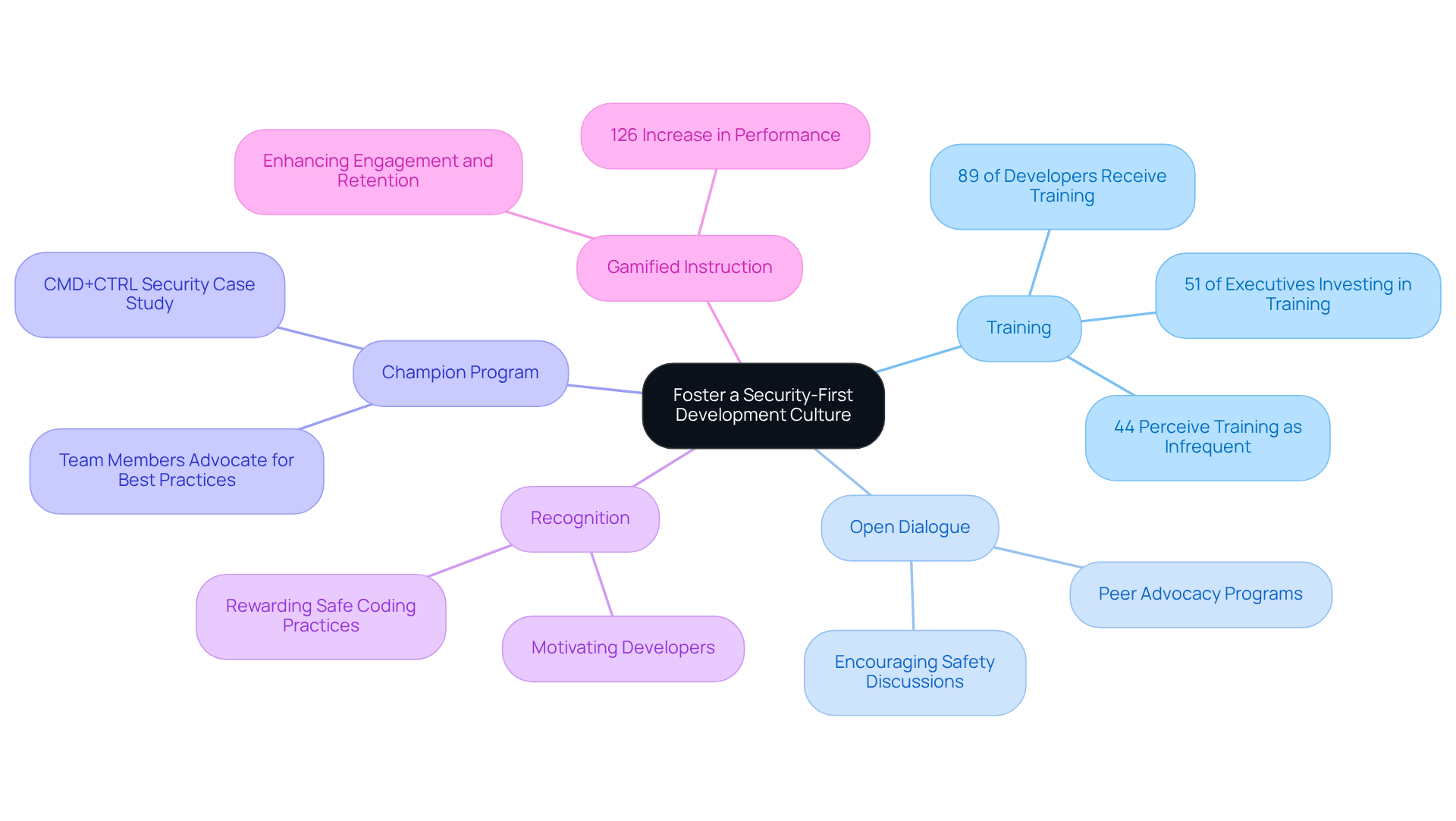
Foster a Security-First Development Culture
Promoting a safety-first culture within a organization requires integrating security into the organization’s core values. Regular training sessions are vital to underscore the significance of security awareness; notably, 51% of executives are investing in security initiatives.
Encouraging open dialogue about safety issues is essential, alongside establishing a ‘champion’ program where team members advocate for best practices. For instance, organizations like CMD+CTRL Security have successfully implemented such programs, demonstrating the positive impact of peer advocacy on security awareness.
Recognizing and rewarding safe practices can motivate developers to prioritize protection in their work. Furthermore, ongoing education and retention of safety concepts among developers is crucial. In fact, organizations that embrace this educational approach report a 126% increase in performance, highlighting the tangible benefits of investing in safety training.
As organizations face increasing threats, including cyberattacks, prioritizing security becomes not just beneficial but essential for maintaining resilience and competitiveness in the industry. However, it is crucial to acknowledge that 44% of executives perceive training on security practices as infrequent, pointing to a common challenge that organizations must address.
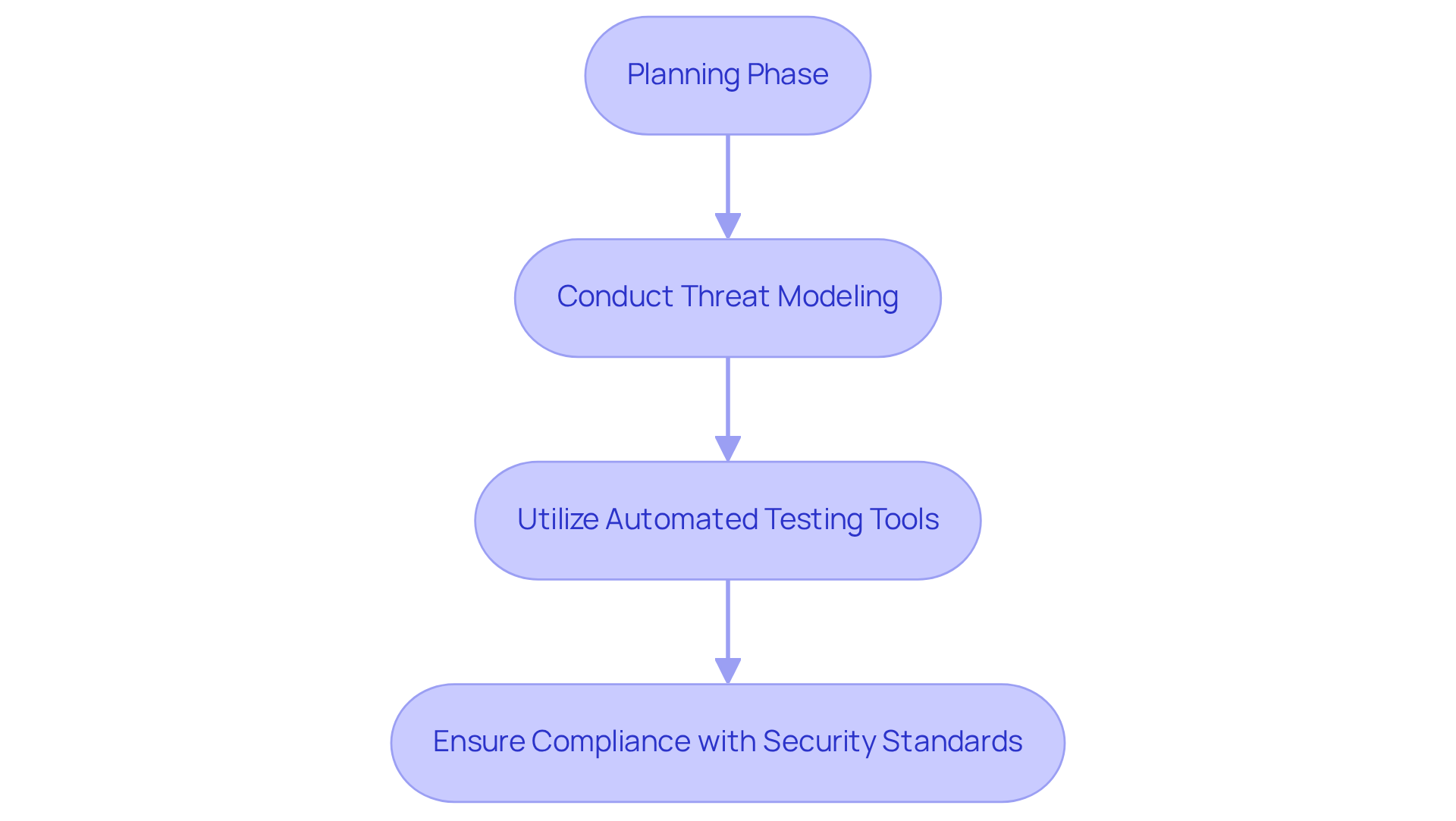
Secure Early in the Software Development Life Cycle
To secure the software development life cycle, hedge funds should adopt a ‘shift-left’ approach that aligns with software development practices, integrating security through to deployment. This strategy involves:
- Conducting assessments to identify potential weaknesses.
- Utilizing tools that can detect issues early in the process.
- Ensuring collaboration through communication and training.
For instance, employing tools such as static analysis can effectively identify vulnerabilities in the code prior to deployment, thereby mitigating the risk of exploitation.
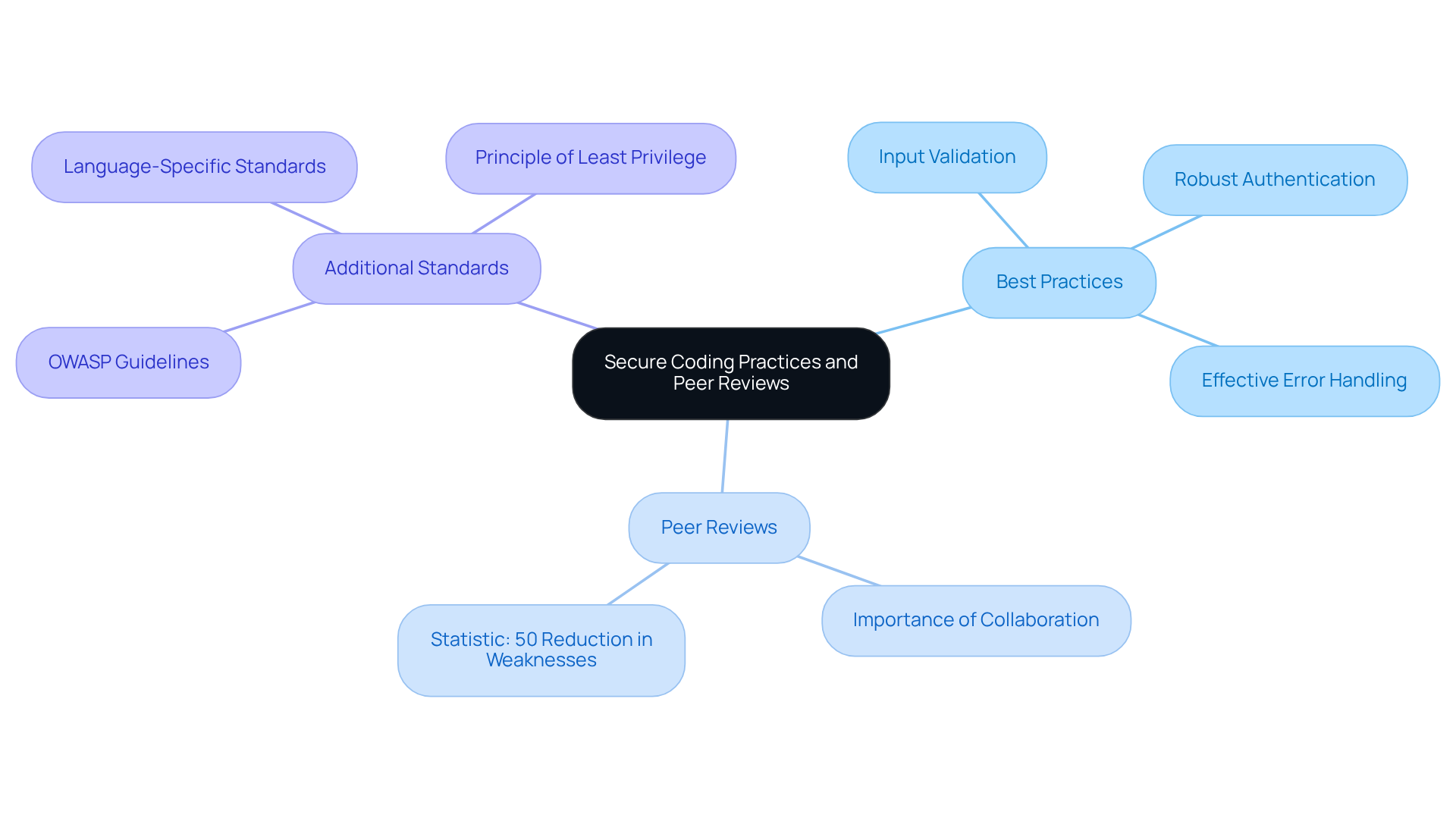
Adopt Secure Coding Practices and Peer Reviews
Hedge funds must adopt secure coding practices based on established guidelines, such as OWASP. These guidelines emphasize security measures, including:
Secure coding is not merely a one-time checklist; it is an ongoing process that requires continuous attention and improvement in line with industry standards.
Fostering an environment of collaboration is crucial for enhancing both code quality and adhering to security protocols. These evaluations enable team members to collaboratively identify potential vulnerabilities and propose enhancements based on best practices. Research indicates that implementing peer evaluations can lead to a reduction of weaknesses in production code by as much as 50%. This statistic underscores the importance of peer reviews as a fundamental practice for ensuring software security.
Additionally, adhering to secure coding standards are vital components that further strengthen protective measures.
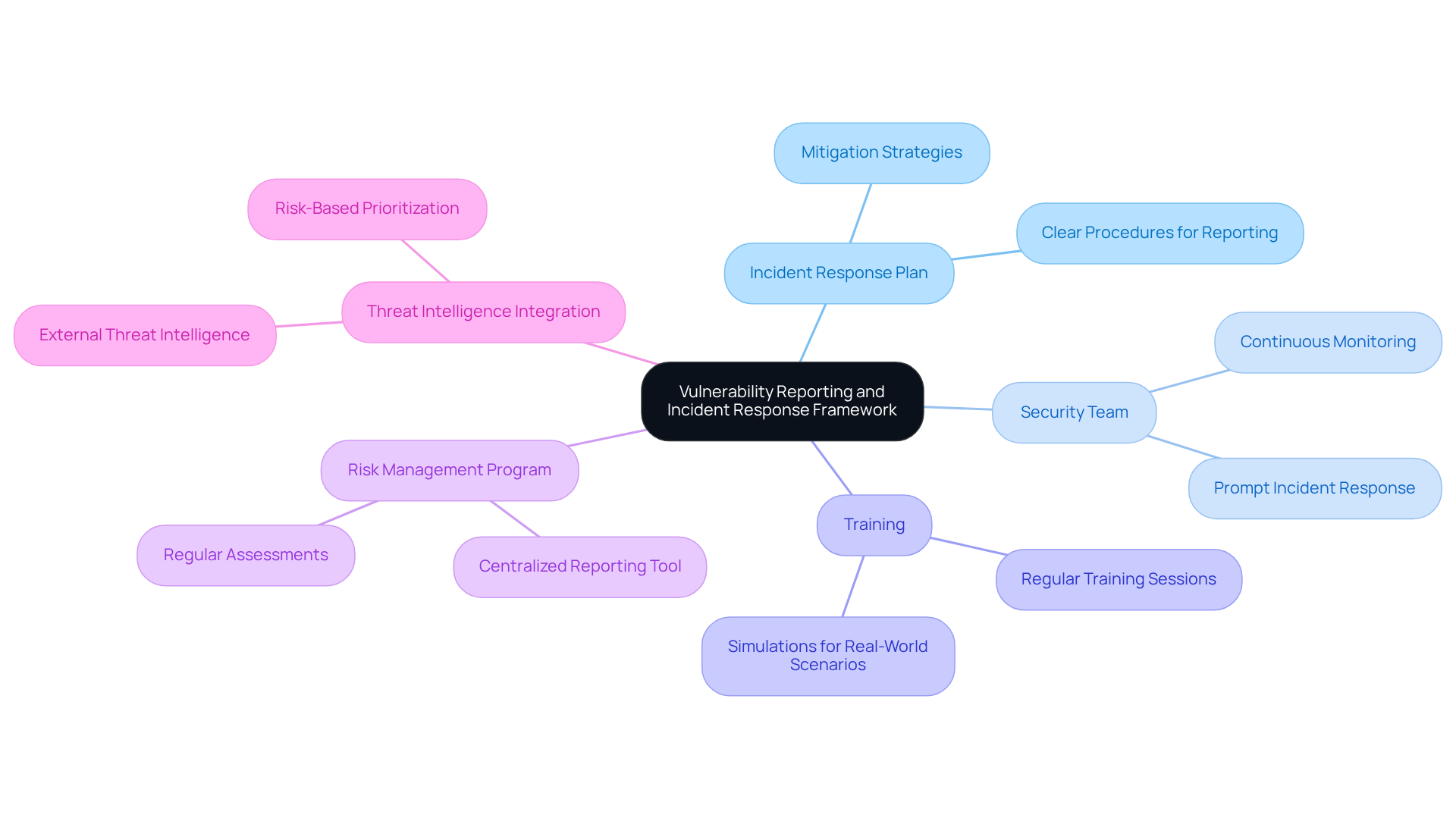
Establish a Strong Vulnerability Reporting and Incident Response Framework
Hedge funds must prioritize the establishment of a comprehensive framework that outlines clear procedures for identifying, reporting, and mitigating vulnerabilities. Central to this strategy is the formation of a team responsible for continuous monitoring of systems and prompt incident response. Regular training sessions and simulations are essential to prepare the team for real-world scenarios, thereby enhancing their readiness to address potential threats.
Furthermore, establishing a robust vulnerability management program is crucial. This program should include tools to proactively identify and address security issues. For instance, utilizing a ticketing system can significantly streamline the documentation and resolution of vulnerabilities, ensuring that no issue remains unaddressed.
As the sector confronts an increasingly complex threat landscape – evidenced by the fact that 74% of financial institutions experienced at least one ransomware attack in the past year – the importance of these measures cannot be overstated. Additionally, integrating external threat intelligence into the security framework is vital for effective risk-based prioritization, enabling hedge funds to concentrate on vulnerabilities that present the greatest immediate risk.
Conclusion
Fostering a culture of security within hedge funds is essential for navigating the complexities of software development in today’s digital landscape. By embedding security principles into the organizational ethos, hedge funds can not only comply with regulatory requirements but also enhance their resilience against emerging threats. Emphasizing a proactive approach to security at every stage of the software development life cycle ensures that protective measures are not an afterthought but an integral part of the development process.
Key strategies include:
- Implementing regular training sessions to promote safety awareness
- Adopting a ‘shift-left’ approach to integrate security early in the SDLC
- Establishing robust coding practices through peer reviews
Each of these measures significantly contributes to reducing vulnerabilities and fostering a more secure development environment. Furthermore, creating a strong incident response framework and encouraging open communication about security issues are vital components that enhance the overall security posture of hedge funds.
Ultimately, the significance of prioritizing software development security cannot be overstated. As cyber threats continue to evolve, hedge funds must adopt these best practices to safeguard their assets and maintain trust with clients and stakeholders. By committing to a security-first mindset, organizations can mitigate risks and position themselves as leaders in the financial sector, ensuring long-term success in an increasingly competitive landscape.
Frequently Asked Questions
What is the importance of fostering a security-first culture in hedge funds?
Fostering a security-first culture in hedge funds is essential for integrating protective principles into the organization’s core values, thereby enhancing software development security.
How are organizations promoting safety within their development teams?
Organizations promote safety by conducting regular training sessions on software development security best practices and encouraging open dialogue about safety issues.
What role do ‘champion’ programs play in promoting security best practices?
‘Champion’ programs involve team members advocating for safety best practices, which has been shown to positively impact awareness and engagement within the organization.
Can you provide an example of an organization that has successfully implemented advocacy programs?
CMD+CTRL Security is an example of an organization that has successfully implemented advocacy programs, demonstrating the benefits of peer advocacy on safety awareness.
How can recognizing and rewarding safe coding practices benefit developers?
Recognizing and rewarding safe coding practices can motivate developers to prioritize protection in their work, leading to a stronger focus on security.
What is the impact of gamified instruction on safety training for developers?
Gamified instruction has proven effective in enhancing engagement and retention of safety concepts among developers, resulting in a reported 126% increase in performance in organizations that adopt this approach.
Why is prioritizing safety education crucial for hedge funds?
Prioritizing safety education is crucial for hedge funds due to increasing regulatory scrutiny, such as compliance with the SEC’s revised Reg S-P regulations, which is essential for maintaining resilience and competitiveness in the industry.
What challenge do executives face regarding training on software development security best practices?
A common challenge is that 44% of executives perceive training on software development security best practices as infrequent, indicating a need for more consistent training efforts.
List of Sources
- Foster a Security-First Development Culture
- SEC’s 2026 Examination Priorities for Investment Advisers | JD Supra (https://jdsupra.com/legalnews/sec-s-2026-examination-priorities-for-4416584)
- New Study on Software Security Training Finds 89% of Developers Receive Training, Compared to Only 18% of Other SDLC Stakeholders (https://businesswire.com/news/home/20241029229591/en/New-Study-on-Software-Security-Training-Finds-89-of-Developers-Receive-Training-Compared-to-Only-18-of-Other-SDLC-Stakeholders)
- Hedge funds step up cybersecurity spending amid rising threats and regulatory pressure – Hedgeweek (https://hedgeweek.com/hedge-funds-step-up-cybersecurity-spending-amid-rising-threats-and-regulatory-pressure)
- Cybersecurity spend rises in hedge funds amid rising threats | David Cass posted on the topic | LinkedIn (https://linkedin.com/posts/dcass001_cybersecurity-financialservices-identity-activity-7421915718394327042-iccK)
- The Business Case for Developer Security Training and Why You Need It Now (https://appsecengineer.com/blog/the-business-case-for-developer-security-training-and-why-you-need-it-now)
- Secure Early in the Software Development Life Cycle
- The Importance of Threat Modeling for Developers (https://blog.secureflag.com/2024/12/17/threat-modeling-for-developers)
- Hedge funds step up cybersecurity spending amid rising threats and regulatory pressure – Hedgeweek (https://hedgeweek.com/hedge-funds-step-up-cybersecurity-spending-amid-rising-threats-and-regulatory-pressure)
- Threat Modeling Within the Software Development Life Cycle (https://versprite.com/blog/software-development-lifecycle-threat-modeling)
- Shifting left might improve software security, but developers are becoming overwhelmed – communication barriers, tool sprawl, and ‘vulnerability overload’ are causing serious headaches for development teams (https://itpro.com/software/development/software-security-shift-left-developer-overload)
- Best Quotes of Threat Modeling with Page Numbers By Adam Shostack (https://bookey.app/book/threat-modeling/quote)
- Adopt Secure Coding Practices and Peer Reviews
- 7 Best Practices for Secure Software Engineering in 2026 (https://computer.org/publications/tech-news/trends/secure-software)
- Toward effective secure code reviews: an empirical study of security-related coding weaknesses – Empirical Software Engineering (https://link.springer.com/article/10.1007/s10664-024-10496-y)
- 9 Best Practices for Secure Coding in 2026 (https://securityjourney.com/post/best-practices-for-secure-coding)
- Improve Security with Smarter Code Review Practices (https://artsyltech.com/blog/the-role-of-code-review-in-enhancing-cybersecurity)
- Establish a Strong Vulnerability Reporting and Incident Response Framework
- The 6 Biggest Cyber Threats for Financial Services in 2026 | UpGuard (https://upguard.com/blog/biggest-cyber-threats-for-financial-services)
- Threat and Vulnerability Management in 2026 (https://recordedfuture.com/blog/threat-and-vulnerability-management)
- 2026 Cyber Risk Management Strategies To Adopt Now (https://forbes.com/councils/forbestechcouncil/2026/03/02/2026-cyber-risk-management-strategies-to-adopt-now)
- For Financial Services, A New Approach to Incident Response is Essential – BreachRx (https://breachrx.com/2023/06/20/for-financial-services-a-new-approach-to-incident-response-is-essential)
- Hedge funds step up cybersecurity spending amid rising threats and regulatory pressure – Hedgeweek (https://hedgeweek.com/hedge-funds-step-up-cybersecurity-spending-amid-rising-threats-and-regulatory-pressure)
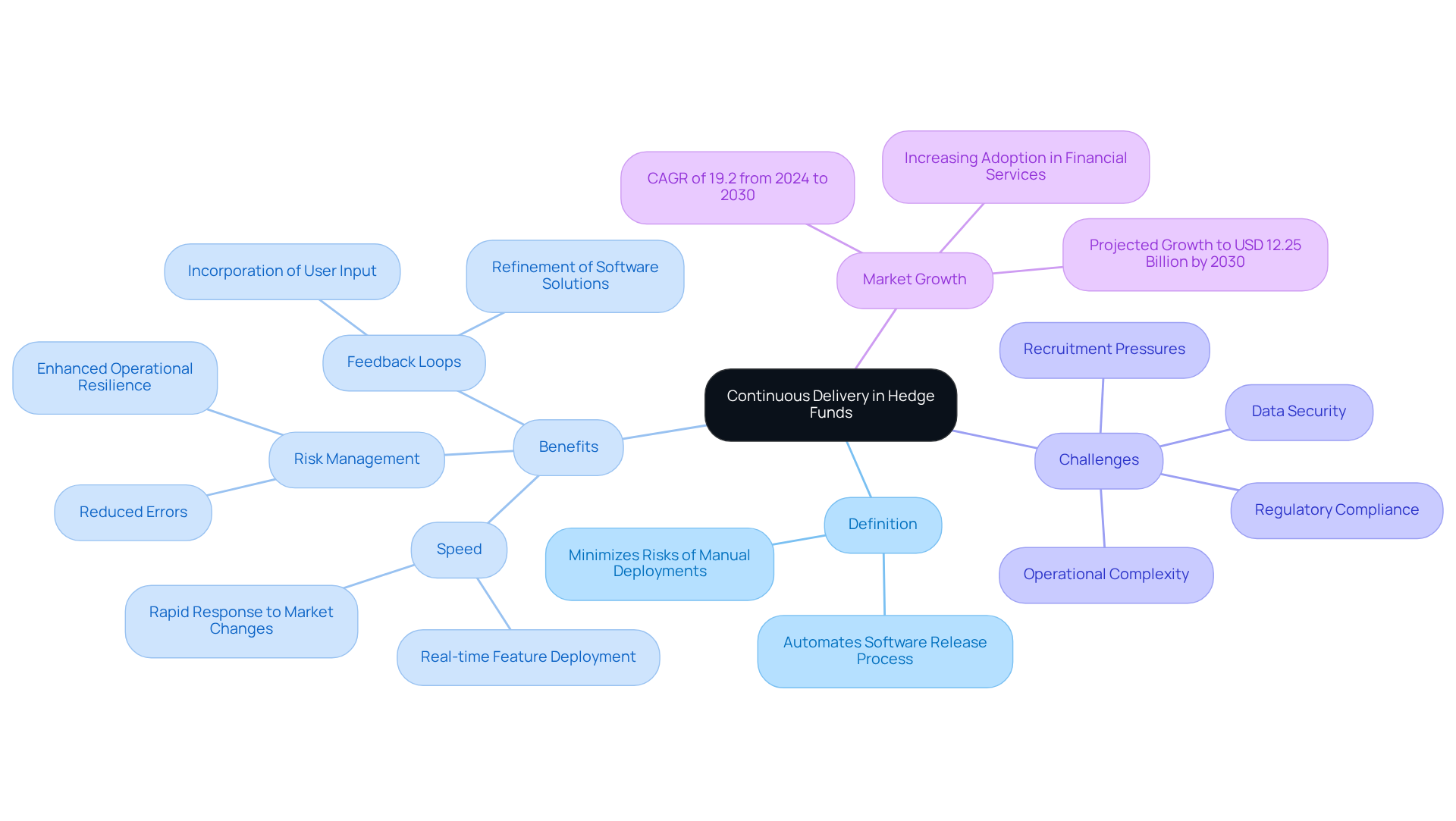
Introduction
Continuous delivery is transforming the operational landscape of hedge funds, enabling them to respond to market dynamics with remarkable speed and efficiency. By automating the software release process, hedge funds can significantly reduce the risks associated with manual deployments and bolster their operational resilience in an increasingly competitive environment.
However, the path to effectively implementing continuous delivery is not without its challenges. Hedge funds must navigate complexities such as regulatory compliance and the integration of legacy systems. To fully capitalize on the advantages of continuous delivery and secure their position in the rapidly evolving financial sector, hedge funds need to develop strategies that address these hurdles.
Understand Continuous Delivery in Hedge Fund Context
cloud represents a software development methodology that automates the release workflow, ensuring that code changes are consistently in a deployable state. This practice is particularly advantageous for hedge funds, where rapid adaptation to market fluctuations and regulatory requirements is crucial.
Definition of Continuous Delivery: CD automates the software release process, significantly minimizing the risks associated with manual deployments and facilitating frequent updates.
Benefits for Hedge Funds:
- Speed: Hedge funds can deploy new features or fixes in real-time, which is vital in a volatile environment.
- Reliability: The automation of testing and deployment diminishes the likelihood of errors that could lead to compliance issues or financial losses, thereby enhancing operational resilience.
- User Feedback: The continuous incorporation of user input allows hedge firms to refine software solutions based on actual user experiences and market demands, fostering innovation.
Challenges: Implementing CD within hedge portfolios necessitates navigating regulatory compliance, ensuring data security, and integrating legacy systems. Specific challenges encompass technical debt, resource allocation, and recruitment pressures, all of which are essential for a successful transition to CD practices. The market is projected to experience significant growth, anticipated to reach USD 12.25 billion by 2030, up from USD 4.92 billion in 2025, with a compound annual growth rate of 19.2% from 2024 to 2030. This growth highlights the increasing acknowledgment of CD’s advantages within the sector.
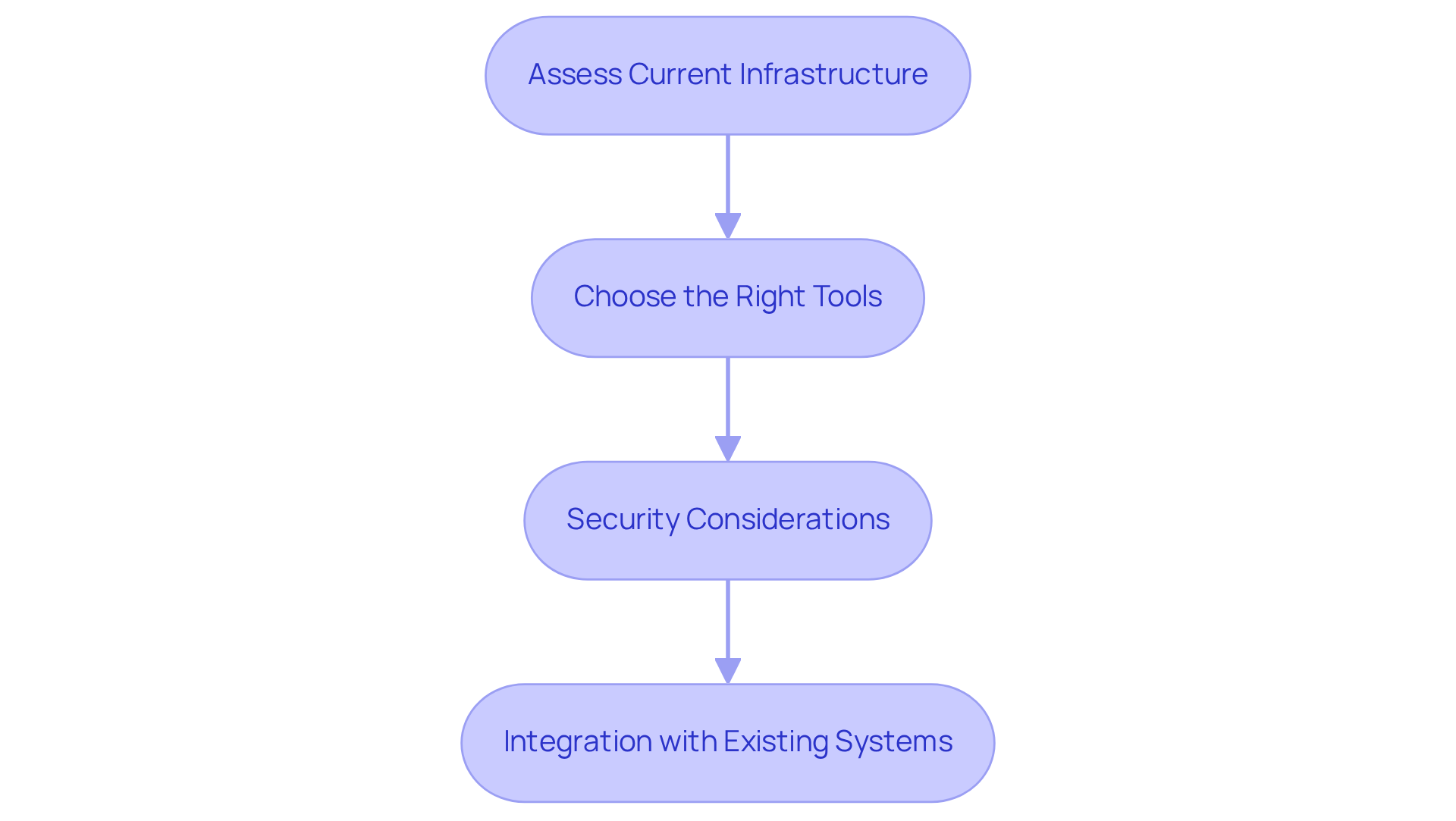
Identify Infrastructure and Tools for Continuous Delivery
To effectively implement continuous delivery in a hedge fund organization, identifying the appropriate infrastructure and tools is crucial. The industry reached a record high of $3.2 trillion in assets last year, underscoring the importance of robust CI/CD practices. Here’s a structured approach to achieve this:
-
Evaluate: Begin by evaluating existing systems and workflows to identify components that can be integrated or require replacement. Key considerations include scalability, security, and adherence to stringent financial regulations.
-
Identify:
- Version Control Systems: Implement tools like Git, which are vital for managing code changes and fostering collaboration among development teams.
- CI/CD Platforms: Opt for a platform such as Jenkins, GitLab CI, or CircleCI, which facilitate automated testing and deployment processes. Jenkins is notably the most popular CI tool for professional use, enhancing credibility in its effectiveness.
- Containerization: Utilize Docker or Kubernetes to create containers, ensuring consistency across various stages of development.
- Monitoring Tools: Utilize solutions like Prometheus or the ELK Stack to monitor application performance and log errors, which are essential for maintaining operational integrity.
-
Ensure: It is imperative that the selected tools comply with industry standards for data protection and security. This includes implementing authentication and encryption protocols for sensitive information. According to the Hutte Survey, about 68% of DevOps teams had incorporated security tools directly into their CI/CD pipelines by 2023, highlighting the significance of security in the hedge fund sector.
-
Integrate: Ensure that new tools can seamlessly integrate with legacy systems to prevent operational disruptions. This may require the creation of custom APIs or middleware solutions. Addressing the challenges faced by investment firms regarding compliance and security is critical in this context.
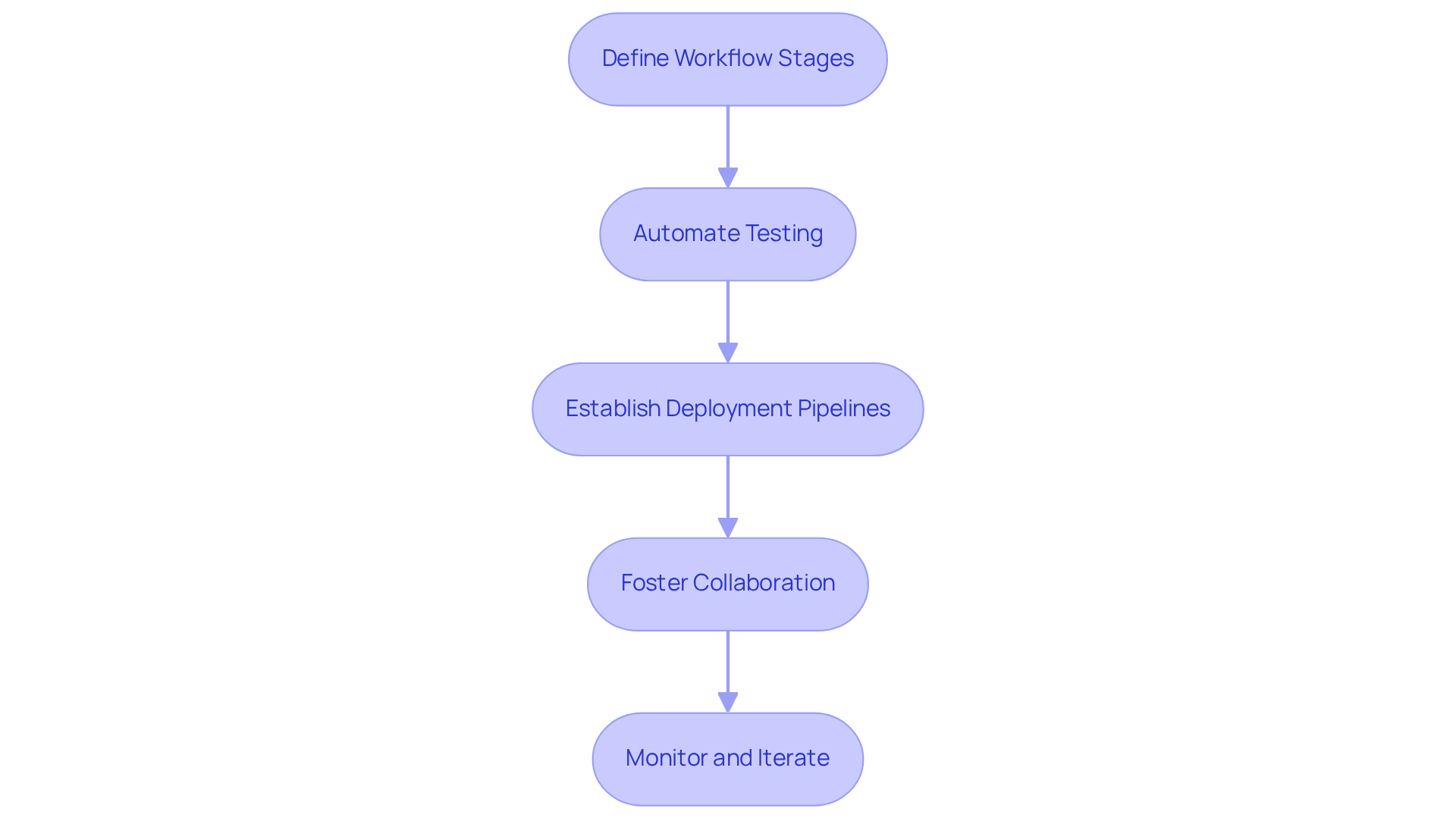
Integrate Continuous Delivery into Hedge Fund Workflows
Integrating Continuous Delivery into your hedge fund‘s workflows involves several key steps:
- Define Workflow: Clearly outline the stages of your project, which include planning, construction, testing, deployment, and monitoring. Each phase should have established procedures and responsibilities.
- Automate Testing: Implement testing at every phase of the development cycle. This encompasses unit tests, integration tests, and end-to-end tests to ensure that code changes do not introduce new issues.
- Establish Pipeline: Create pipelines that automate the process of transferring code from development to production. This should include automated build procedures, testing, and deployment to staging environments prior to going live.
- Foster Collaboration: Encourage collaboration among development, operations, and compliance teams. Consistent communication and shared goals will help ensure that everyone is aligned with the objectives of the cloud initiative.
- Monitor and Iterate: After implementing Continuous Delivery, continuously assess and improve the effectiveness of your workflows. Utilize metrics to identify areas for enhancement and refine your methods to optimize performance.
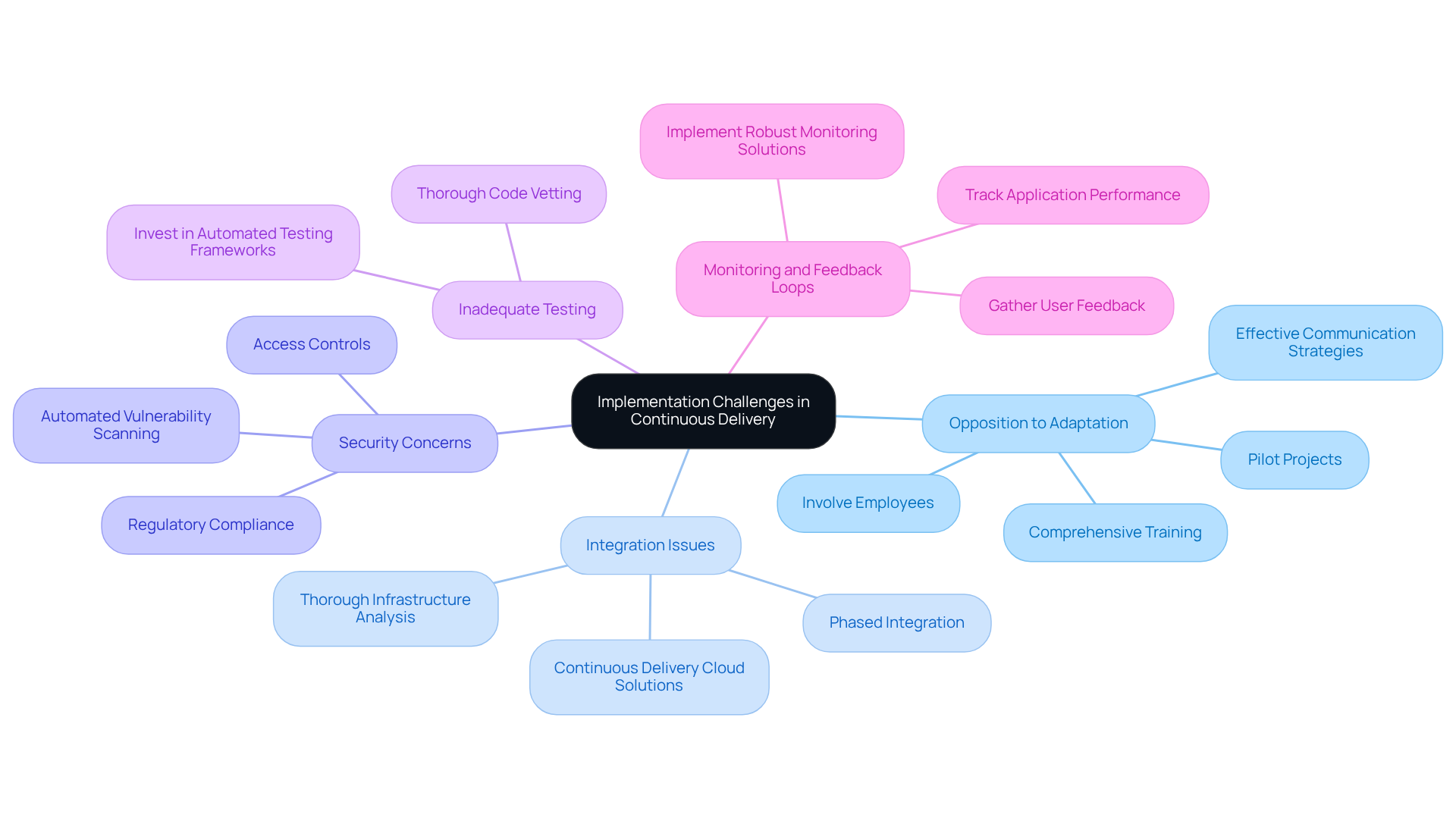
Troubleshoot Common Implementation Challenges
Implementing Continuous Delivery (CD) in hedge funds presents several challenges that require strategic solutions. Below are key strategies to address common issues:
- Opposition to Adaptation: Many employees may resist adopting new methods, with 71% feeling overwhelmed by workplace transformations. To address this, it is crucial to provide comprehensive training and demonstrate the benefits through pilot projects that showcase improved efficiency and reduced errors. Involving employees in the transition process can significantly enhance their willingness to adapt. Notably, 28% of employees actively oppose changes due to top-down communication, underscoring the need for effective communication strategies.
- Legacy Systems: Legacy systems frequently create obstacles. A thorough analysis of the existing infrastructure is essential. Organizations should consider phased integration or alternative solutions to bridge these gaps, as many struggle with outdated technology, which can lead to delays in transformation initiatives.
- Data Sensitivity: The sensitivity of data raises significant concerns when implementing CD. It is imperative to ensure that all tools and processes used in the organization comply with regulatory standards. Incorporating security measures such as automated vulnerability scanning and access controls is vital to safeguarding data integrity.
- Inadequate Testing: Insufficient testing often results in deployment failures, a common pitfall in many organizations. Investing in comprehensive testing processes is essential to ensure that all code modifications are thoroughly vetted prior to deployment, thereby reducing the risk of errors in production. It is important to recognize that testing is a critical need, highlighting the critical need for robust testing.
- Monitoring and Feedback Loops: A lack of monitoring can impede the identification of issues post-deployment. Implementing robust monitoring systems is necessary to track application performance and gather user feedback, facilitating continuous improvement and ensuring the effectiveness of the CD process.
Conclusion
The implementation of continuous delivery (CD) in hedge funds transcends a mere technological upgrade; it signifies a strategic transformation that enables firms to swiftly adapt to market dynamics and regulatory shifts. By adopting this methodology, hedge funds can automate their release processes, thereby significantly mitigating risks and bolstering their operational resilience in a competitive environment.
Key insights from this guide underscore the diverse advantages of continuous delivery, such as:
- Enhanced speed in deploying new features
- Improved risk management through automated testing
- Fostering of innovation via continuous feedback loops
Nevertheless, challenges like integration with legacy systems and the imperative of ensuring data security must be approached with diligence. A methodical strategy for identifying the appropriate infrastructure and tools, coupled with promoting collaboration among teams, is crucial for successful implementation.
As the continuous delivery cloud market expands, hedge funds must acknowledge the necessity of adapting to these practices. By emphasizing comprehensive training, rigorous testing, and effective monitoring, firms can not only surmount common implementation hurdles but also position themselves as frontrunners in the financial services sector. Embracing continuous delivery is not solely about the adoption of new tools; it represents a fundamental transformation in the operational framework of hedge funds, enabling them to thrive in an ever-evolving market landscape.
Frequently Asked Questions
What is Continuous Delivery (CD) in the context of hedge funds?
Continuous Delivery is a software development methodology that automates the release workflow, ensuring that code changes are consistently in a deployable state. It allows hedge funds to rapidly adapt to market fluctuations and regulatory requirements.
What are the main benefits of Continuous Delivery for hedge funds?
The main benefits include increased speed in responding to market changes, improved risk management by reducing errors in deployments, and enhanced feedback loops that allow for software refinement based on user input and market demands.
How does Continuous Delivery improve speed for hedge funds?
Continuous Delivery enables hedge funds to promptly deploy new features or fixes in real-time, which is essential in a volatile market environment.
In what ways does Continuous Delivery enhance risk management for hedge funds?
By automating testing and deployment processes, Continuous Delivery minimizes the likelihood of errors that could lead to compliance issues or financial losses, thereby enhancing operational resilience.
What challenges do hedge funds face when implementing Continuous Delivery?
Challenges include navigating regulatory compliance, ensuring data security, integrating legacy systems, managing operational complexity, and addressing recruitment pressures necessary for a successful transition to Continuous Delivery practices.
What is the projected growth of the Continuous Delivery cloud market?
The Continuous Delivery cloud market is projected to grow from USD 4.92 billion in 2025 to USD 12.25 billion by 2030, with a compound annual growth rate of 19.2% from 2024 to 2030. This growth indicates a growing recognition of CD’s advantages within the financial services sector.
List of Sources
- Understand Continuous Delivery in Hedge Fund Context
- am.jpmorgan.com (https://am.jpmorgan.com/us/en/asset-management/adv/insights/market-insights/market-updates/on-the-minds-of-investors/what-is-the-outlook-for-hedge-funds-in-2026)
- Multi-strategy funds set to remain fastest-growing hedge fund segment into 2026 – Hedgeweek (https://hedgeweek.com/multi-strategy-funds-set-to-remain-fastest-growing-hedge-fund-segment-into-2026)
- Continuous Delivery Market Size to Hit USD 20.17 Bn by 2035 (https://precedenceresearch.com/continuous-delivery-market)
- Continuous Delivery Market Size, Share, Growth Report 2030 (https://grandviewresearch.com/industry-analysis/continuous-delivery-market-report)
- Continuous Delivery Market Size, Share & Growth Report 2032 (https://snsinsider.com/reports/continuous-delivery-market-5712)
- Identify Infrastructure and Tools for Continuous Delivery
- Hedge Funds are Outsourcing to the Cloud (https://thehedgefundjournal.com/hedge-funds-are-outsourcing-to-the-cloud)
- One moment, please… (https://testrail.com/blog/continuous-integration-metrics)
- Best Continuous Integration Tools for 2025 ‒ Survey Results | The TeamCity Blog (https://blog.jetbrains.com/teamcity/2023/07/best-ci-tools)
- fortunebusinessinsights.com (https://fortunebusinessinsights.com/continuous-integration-ci-tools-market-111194)
- Integrate Continuous Delivery into Hedge Fund Workflows
- AI Use by Hedge Funds Made Tangible – From Lego Bots to Alpha Assistants (https://resonanzcapital.com/insights/ai-use-by-hedge-funds-made-tangible-from-lego-bots-to-alpha-assistants)
- AI scare turns software into hedge funds’ US$24 billion profit machine (https://wealthprofessional.ca/investments/equity-markets/ai-scare-turns-software-into-hedge-funds-us24-billion-profit-machine/391537)
- How Hedge Funds Can Approach and Implement Post-Trade Automation with Agentic AI – A Checklist | Arcesium (https://arcesium.com/blog/hedge-funds-post-trade-agentic-ai-implement-checklist)
- Troubleshoot Common Implementation Challenges
- 59 Change Management Statistics | Pollack Peacebuilding Systems (https://pollackpeacebuilding.com/blog/change-management-statistics)
- McKinsey: 70% of Change Programs Fail Due to Employee Resistance | Operational Innovations (San Diego) posted on the topic | LinkedIn (https://linkedin.com/posts/operational-innovations-san-diego_in-their-wellknown-article-changing-change-activity-7417277266025476096-Bvft)
- ‘Hedge Funds’ Got Clipped By Epic Fury. They Forgot To ‘Hedge’? (https://forbes.com/sites/georgecalhoun/2026/03/20/hedge-funds-got-clipped-by-epic-fury-they-forgot-to-hedge)
Introduction
Selecting the appropriate IoT application development company is crucial for achieving success in an increasingly dynamic digital environment. As the global IoT market is anticipated to expand significantly, businesses have a unique opportunity to harness innovative solutions that improve operational efficiency and enhance customer engagement. However, the challenge lies in navigating the vast array of options available and identifying a partner that not only meets specific business requirements but also possesses the technical expertise necessary to deliver impactful results. How can organizations ensure they are making the optimal choice in this vital component of their digital strategy?
Understand IoT Application Development Basics
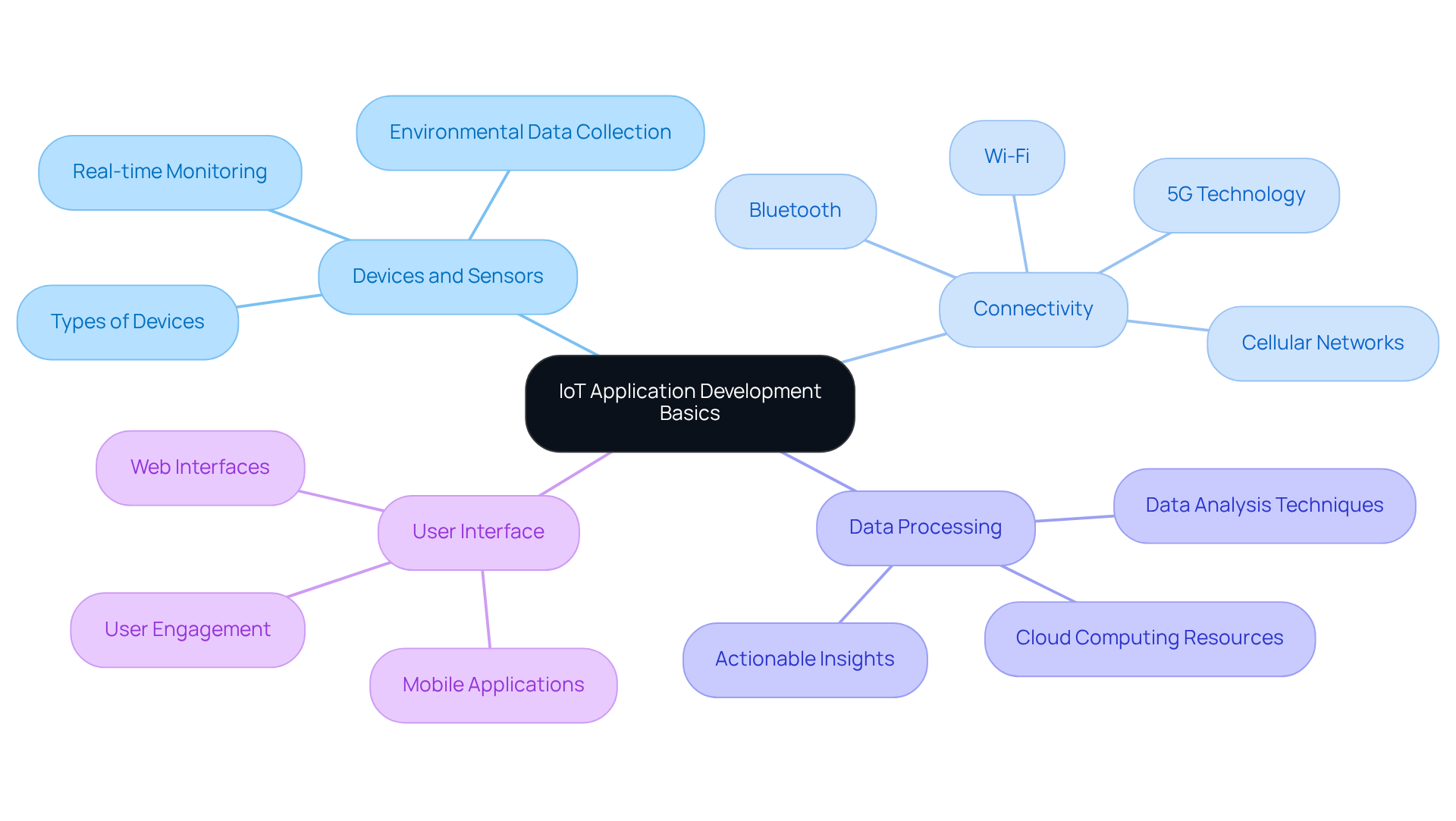
IoT (Internet of Things) application creation centers on developing software that enables the connection, communication, and interaction of devices over the internet. The key components of this process include:
- Devices and Sensors: These physical components are vital for collecting environmental data. They play a crucial role in facilitating communication, which are foundational for data collection.
- Connectivity: This encompasses the various methods and protocols that allow devices to communicate, including Wi-Fi, Bluetooth, and cellular networks. The connectivity options significantly improve speed and reliability for IoT applications.
- Data Processing: Following data collection, it must be processed and analyzed, often utilizing cloud computing resources. This step is essential for deriving actionable insights from the data gathered by IoT devices.
- User Interface: The user interface represents how individuals interact with the IoT system, typically through mobile applications or web interfaces. A well-designed interface is critical for user engagement and operational efficiency.
The growth of the industry is noteworthy, with projections indicating that the global IoT market, influenced by various technology companies, will reach approximately $471.3 billion in revenue by 2026, nearly doubling to $908 billion by 2034. Successful IoT initiatives, such as smart home or smart city efforts that optimize resource allocation, exemplify the transformative potential of IoT technology. Furthermore, as IoT systems become more prevalent, the importance of security cannot be overstated, as these factors are crucial for the success of IoT projects. Understanding these fundamentals will provide valuable insights into the intricacies of IoT endeavors and the specialized knowledge required from an IoT development company.
Define Your Business Needs and Goals
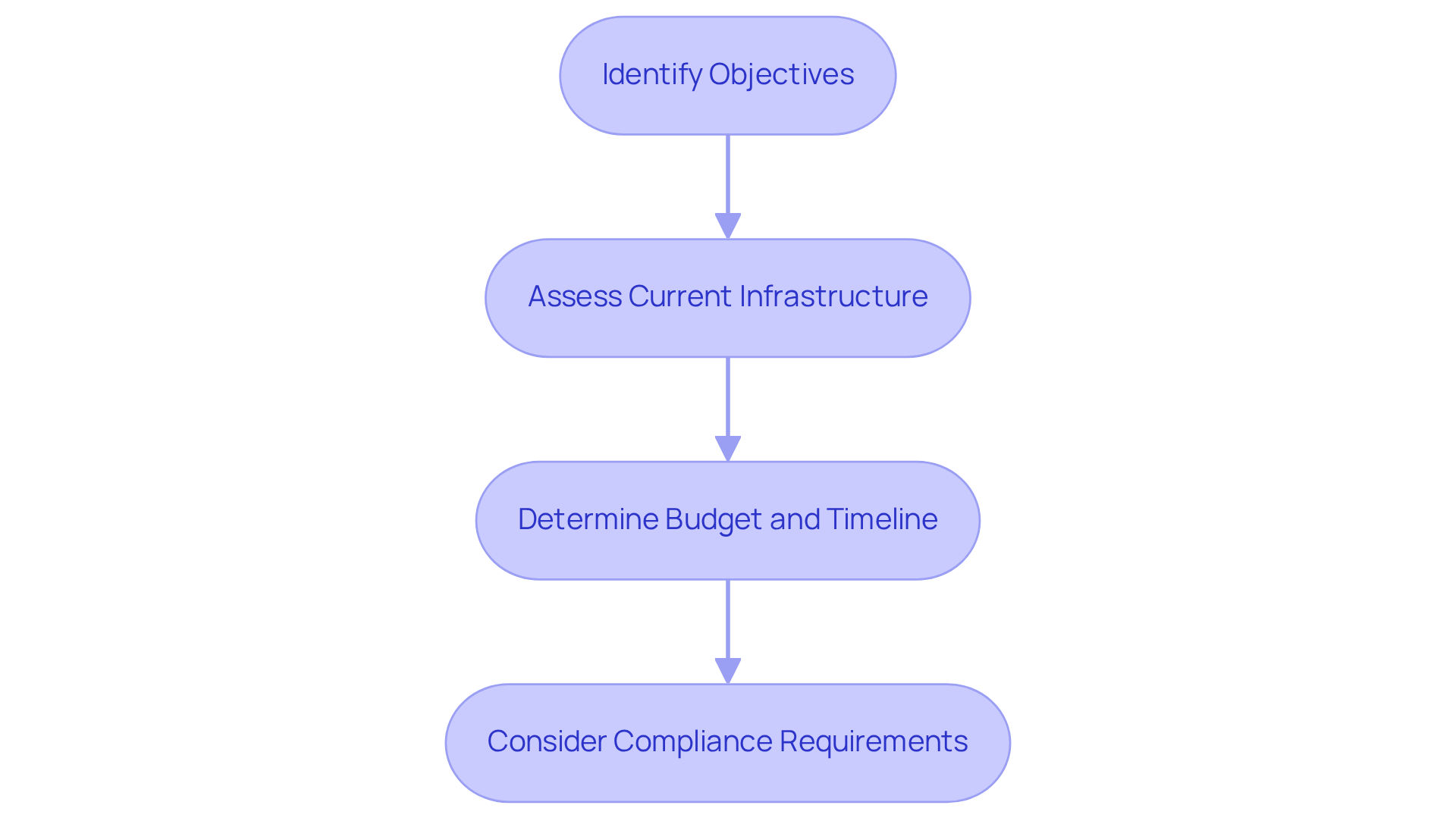
Before selecting an IoT application development company, it is crucial to clearly define your business needs. Consider the following steps:
- Identify Objectives: Clearly articulate what you aim to achieve with your IoT application. This may involve increasing efficiency, improving customer engagement, or automating processes.
- Assess Compatibility: Evaluate potential partners to understand how they can integrate with new IoT solutions. This assessment ensures a seamless transition and maximizes the potential of your investment.
- Set Parameters: Establish a realistic budget and timeline for your project. This framework will guide your selection process and help manage expectations with potential collaborators.
- Consider Compliance: In regulated industries, it is essential to ensure alignment with legal standards. This alignment ensures that your IoT solutions not only meet business objectives but also adhere to industry regulations.
By having a clear understanding of your business requirements, you can effectively communicate with potential collaborators, paving the way for successful partnerships.
Evaluate Potential IoT Development Companies
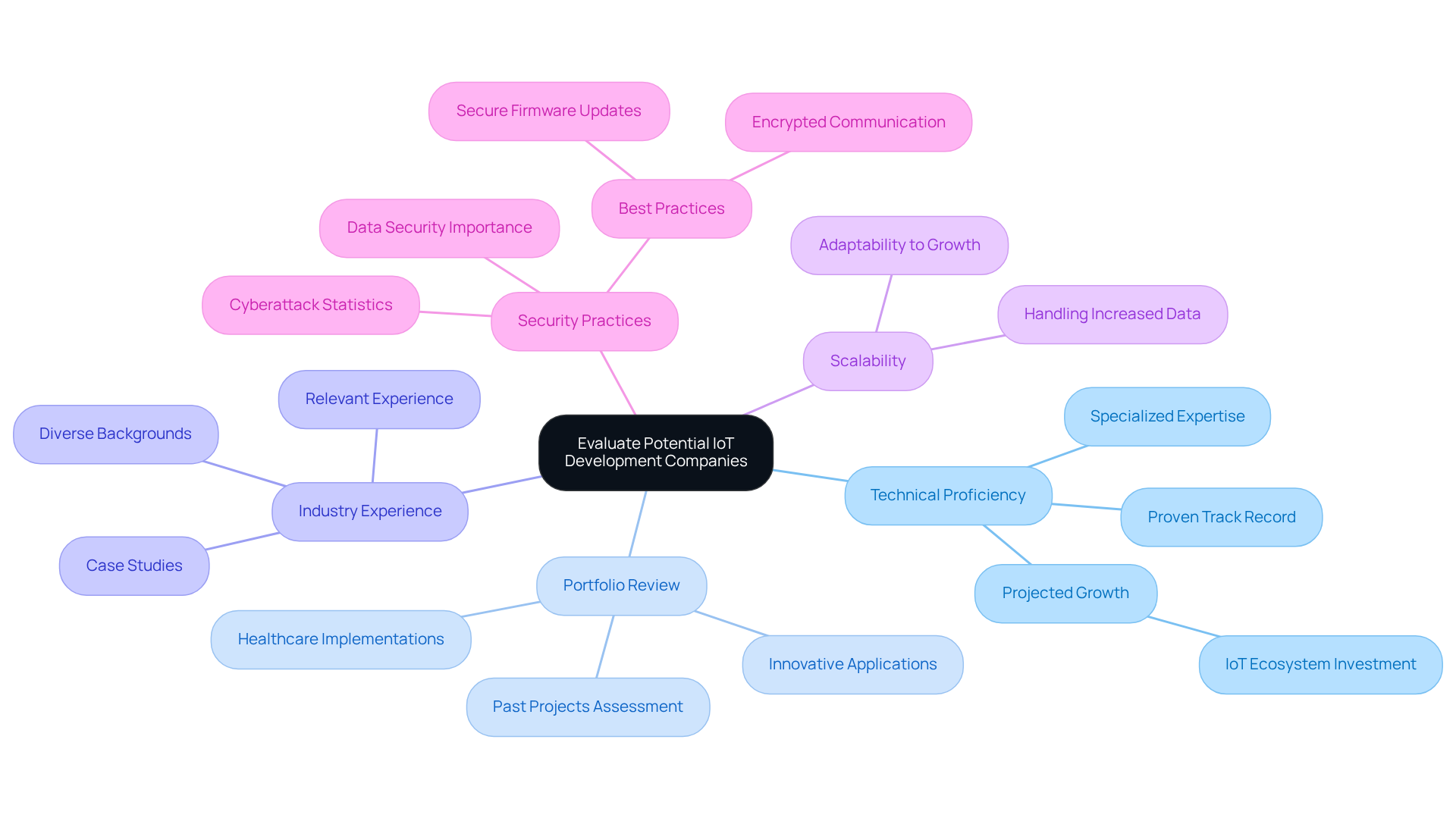
When evaluating potential IoT development companies, it is essential to consider several key criteria:
- Experience: Seek organizations with a proven track record in IoT development. By 2026, the IoT ecosystem is projected to surpass $1 trillion in investment, indicating a significant rise in the average number of projects completed by IoT application development companies. This trend underscores the importance of specialized expertise in the field.
- Portfolio: Examine their past projects to assess their capability to deliver solutions that meet your specific needs. Successful implementations often highlight innovative applications of IoT technology, providing insights into the competencies of an organization. For example, companies that have effectively integrated IoT solutions in healthcare have shown improvements in patient monitoring and operational efficiency.
- Industry Experience: Verify that the organization possesses relevant experience in your particular industry, especially if you operate within regulated sectors such as healthcare or finance. Firms with diverse industry backgrounds are better equipped to anticipate and address potential challenges during system deployment, as evidenced by their experience and the contributions of an expert team.
- Scalability: Assess whether they can modify their solutions as your business grows. The ability to scale is vital, particularly in environments where an organization may need to handle increasing numbers of devices and data volumes.
- Security Practices: Given the critical importance of security in IoT, ensure that the organization adheres to established best practices for securing applications. With data breaches globally in 2022, robust security is crucial for safeguarding your data and maintaining user trust. Comprehensive security practices, such as encrypted communication and secure firmware updates, significantly enhance the overall safety of IoT systems.
By thoroughly evaluating these factors, you can effectively narrow down organizations, such as a reputable firm, that align with your requirements, thereby ensuring a successful collaboration in your IoT initiatives.
Assess Communication and Collaboration Fit
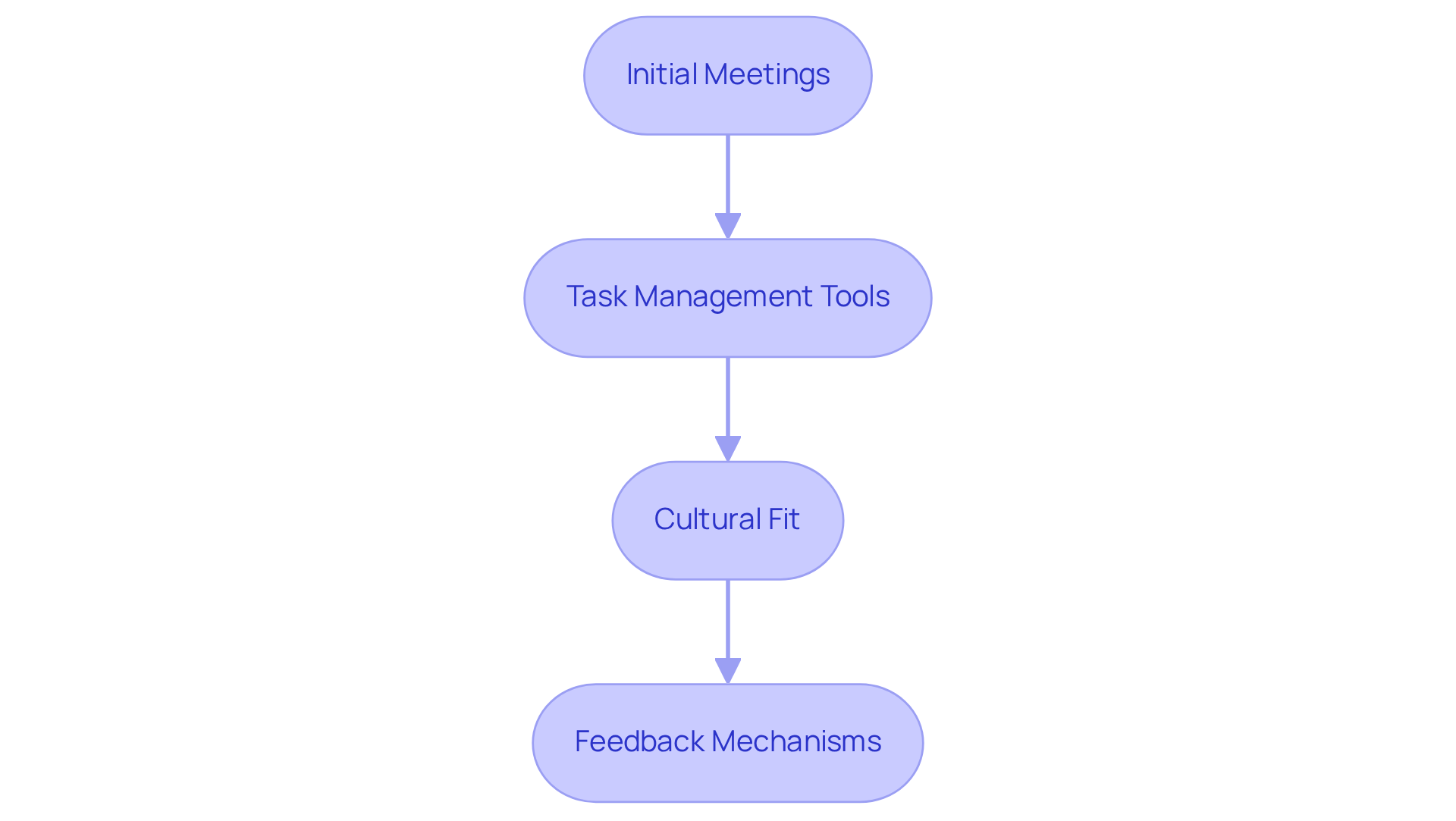
is crucial for successful collaboration with an IoT development firm like a reputable company. To assess this fit, consider the following key steps:
- Communication Assessment: Use surveys to evaluate the firm’s communication style and responsiveness. This assessment provides insight into how they engage with you and address your needs. At our company, we prioritize understanding your specific requirements to ensure we supply the right candidate designers and developers to integrate into your team.
- Task Management Tools: Inquire about the tools they utilize. It is essential that these tools align with your preferences, as they can significantly impact workflow and collaboration. For instance, 96% of leaders emphasize the importance of communication channels in remote and hybrid environments, underscoring the need for suitable tools.
- Cultural Fit: Evaluate whether their company culture aligns with yours. A compatible culture fosters better collaboration and enhances results.
- Feedback Mechanisms: Ensure they have established processes for regular feedback and updates throughout the project. This practice promotes transparency and keeps all stakeholders informed.
A strong communication strategy can greatly enhance collaboration and lead to successful project execution.
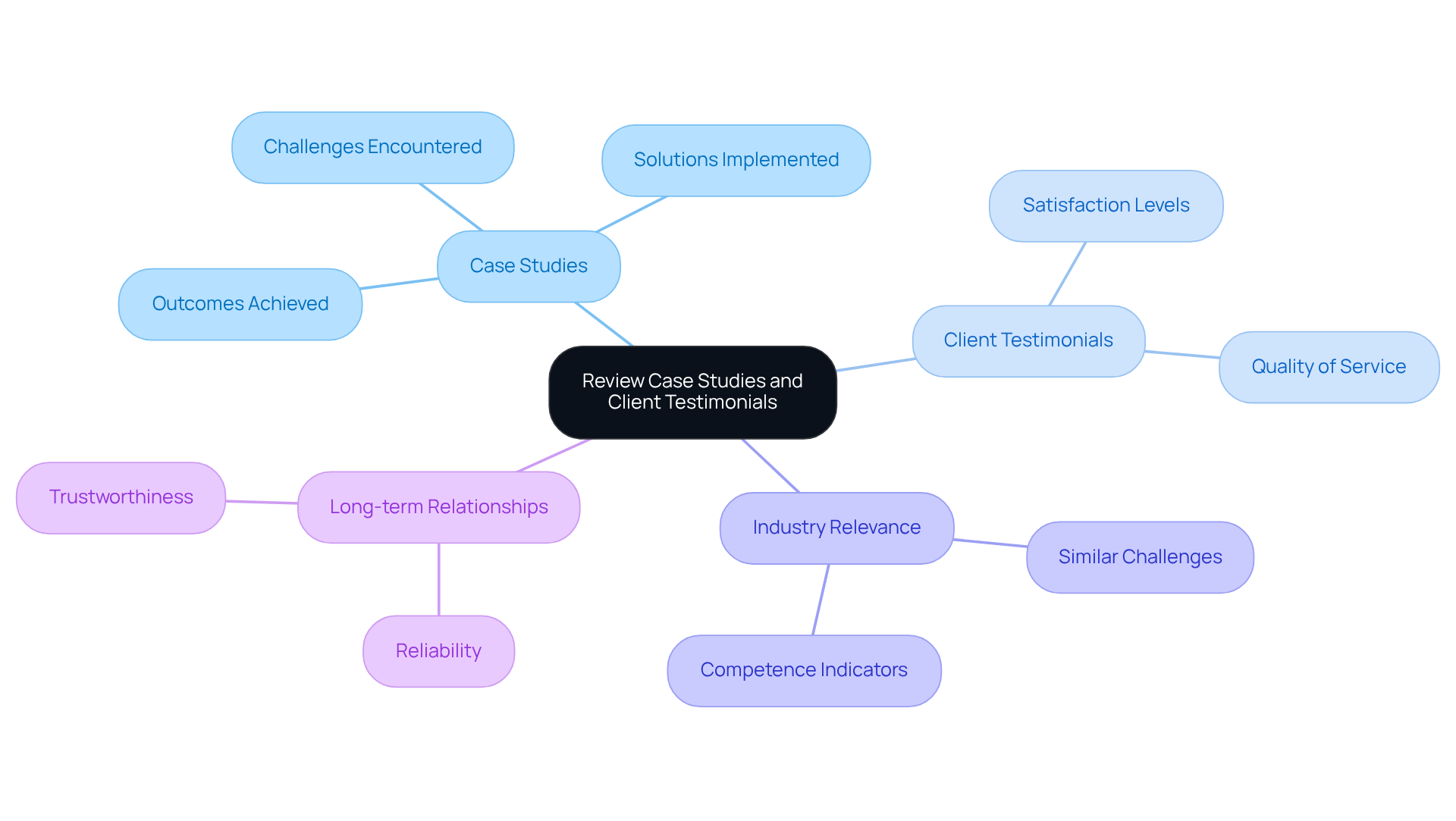
Review Case Studies and Client Testimonials
To establish confidence in your potential IoT development partner, it is crucial to conduct a thorough review of their case studies and testimonials.
- Case Studies: Look for detailed reports that outline the projects, the solutions implemented, and the outcomes achieved. This will provide valuable insights into the organization’s capabilities and their effectiveness in delivering results.
- Client Testimonials: Evaluate testimonials from previous clients to gauge satisfaction levels and the quality of service rendered. High satisfaction rates often reflect a strong track record of success.
- Industry Relevance: Focus on projects that are similar to yours. Understanding how the organization has effectively handled challenges similar to yours can serve as a strong indicator of their competence.
- Long-term Relationships: Identify organizations that have fostered enduring relationships with their clients. Such partnerships typically demonstrate reliability and trustworthiness, which are essential qualities in a collaborator.
These insights will empower you to evaluate the organization’s ability to meet your needs effectively, thereby ensuring a successful partnership.
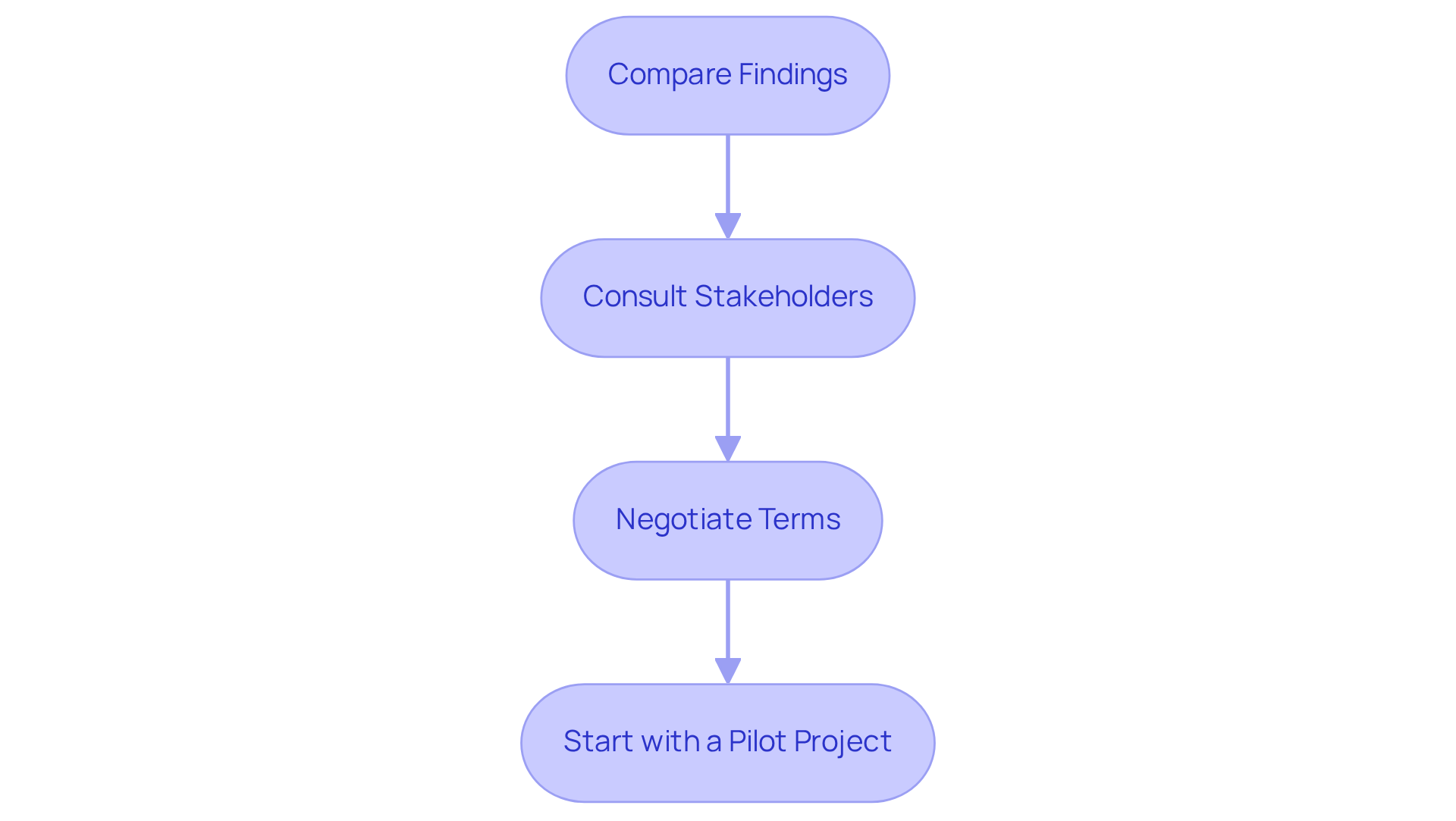
Make Your Final Decision
After assessing potential companies, it is crucial to make an informed decision. To achieve this, follow these steps:
- Compare Findings: Begin by reviewing your evaluation notes, focusing on the strengths of each candidate. This analysis will clarify which option is best.
- Consult Stakeholders: Engage with stakeholders. Their insights can provide valuable perspectives, ensuring that the selected organization aligns with your goals and the potential impact of the partnership is fully understood.
- Negotiate Terms: Once a partner is selected, negotiate terms that encompass timelines, deliverables, and costs. Clear agreements can prevent misunderstandings later on.
- Start with a pilot project: Consider launching a smaller pilot initiative to test the partnership before committing to a larger engagement. This approach allows you to assess their performance and adaptability in a controlled environment.
By adhering to these steps, you can confidently select the right company that meets your business needs and objectives.
Conclusion
Selecting the appropriate IoT application development company is crucial for the success of your IoT initiatives. As the IoT landscape continues to expand rapidly, it is essential to understand the key components, assess business needs, and evaluate potential partners. These steps are vital to ensure that your project not only meets its objectives but also excels in a competitive environment.
This guide has provided key insights into the fundamentals of IoT application development, emphasizing the significance of devices, connectivity, data processing, and user interfaces. Moreover, establishing clear business goals, assessing technical expertise, and ensuring effective communication are critical factors in choosing a development partner. The focus on security practices and the review of case studies further underscore the necessity of a thorough evaluation process to identify a trustworthy collaborator.
Ultimately, the selection of an IoT application development company can profoundly impact the success of your project. By adhering to the outlined steps, stakeholders can make informed decisions that align with their strategic objectives. This approach not only increases the likelihood of successful implementation but also positions your organization to fully harness the potential of IoT technology in transforming business operations.
Frequently Asked Questions
What is IoT application development?
IoT application development involves creating software that enables the connection, communication, and interaction of devices over the internet, utilizing components like devices and sensors, connectivity methods, data processing, and user interfaces.
What are the key components of IoT application development?
The key components include devices and sensors for data collection, connectivity methods such as Wi-Fi and Bluetooth, data processing often using cloud computing, and user interfaces for user interaction.
How does connectivity impact IoT applications?
Connectivity refers to the various methods and protocols that allow devices to communicate. Emerging technologies like 5G are enhancing these options, improving speed and reliability for IoT applications.
Why is data processing important in IoT?
Data processing is essential for analyzing the data collected by IoT devices, enabling the derivation of actionable insights that can inform decision-making and improve operational efficiency.
What role does the user interface play in IoT applications?
The user interface is how individuals interact with the IoT system, typically through mobile apps or web interfaces. A well-designed interface is critical for user engagement and operational efficiency.
What is the projected growth of the IoT market?
The global IoT market is projected to reach approximately $471.3 billion in revenue by 2026 and nearly double to $908 billion by 2034.
What are some successful examples of IoT initiatives?
Successful IoT initiatives include smart healthcare solutions that monitor patient vitals in real-time and smart city projects that optimize resource allocation.
Why is cybersecurity important in IoT development?
Cybersecurity is crucial for ensuring secure connectivity and scalability of IoT solutions, which are essential for their effectiveness and reliability.
What steps should be taken before selecting an IoT application development company?
Steps include identifying objectives, assessing current infrastructure, determining budget and timeline, and considering compliance requirements to ensure alignment with industry regulations.
How can clearly defining business needs benefit the IoT development process?
Clearly defining business needs allows for effective communication with potential collaborators, facilitating successful outcomes when working with an IoT application development company.
List of Sources
- Understand IoT Application Development Basics
- Number of connected IoT devices growing 14% to 21.1 billion (https://iot-analytics.com/number-connected-iot-devices)
- IoT trends in 2026 [UPDATED version] (https://telnyx.com/resources/must-watch-iot-trends)
- Trends 2026: The most important developments for businesses (https://ithinx.io/en/blog/iot-insights/iot-trends-2026)
- Juniper Research releases emerging IoT trends report for 2026 Internet of Things News % (https://iottechnews.com/news/juniper-research-releases-emerging-iot-trends-report-for-2026)
- IoT Use Cases Across Industries and Market Review for 2026 (https://itransition.com/iot/use-cases)
- Define Your Business Needs and Goals
- IoT News, Market Analysis & Industry Insights – IoT Business News (https://iotbusinessnews.com)
- Impact of Internet of Things on Business and the Economy in 2026 (https://sumatosoft.com/blog/impact-of-internet-of-things-iot-on-the-business-economy-trends)
- Ultimate IoT Implementation Guide for Businesses | TechTarget (https://techtarget.com/iotagenda/Ultimate-IoT-implementation-guide-for-businesses)
- What Your Company Needs To Know Before Investing In IoT (https://forbes.com/councils/forbestechcouncil/2021/07/16/what-your-company-needs-to-know-before-investing-in-iot)
- Evaluate Potential IoT Development Companies
- Choosing the Right IoT App Development Company in 2026 (https://spacetotech.com/blog/iot-app-development-company-2026)
- Impact of Internet of Things on Business and the Economy in 2026 (https://sumatosoft.com/blog/impact-of-internet-of-things-iot-on-the-business-economy-trends)
- IoT Device Growth Statistics & Trends (2026) (https://thenetworkinstallers.com/blog/iot-device-growth-statistics)
- Top Content on LinkedIn (https://linkedin.com/pulse/internet-things-iot-develop-services-market-from-2026-hv2ef)
- Assess Communication and Collaboration Fit
- 36+ essential workplace communication statistics for 2026 (https://zoom.com/en/blog/workplace-communication-statistics)
- How Internet of Things (IoT) is revolutionising project and programme management | ILX Group ILX USA | ILX Group US (https://ilxgroup.com/zar/blog/how-internet-of-things-iot-is-revolutionising-project-and-programme-management)
- 35 Quotes about Communication to Inspire Collaboration (https://vibe.us/blog/35-quotes-about-communication?srsltid=AfmBOorqhUcqn3v2ncUoPZpYaHfdU-PlX51gkg2Us7638RiWfrNO6YhB)
- sociabble.com (https://sociabble.com/blog/employee-communications/communications-statistics)
- Workplace Communication Statistics for 2026 (https://pumble.com/learn/communication/communication-statistics)
- Review Case Studies and Client Testimonials
- Top 25 Customer Experience Quotes to Inspire You in 2025 (https://racami.com/top-25-customer-experience-quotes-to-inspire-you-in-2021)
- IoT Market Growth: 50+ Must-Know Stats for Smart City Tech (https://patentpc.com/blog/iot-market-growth-50-must-know-stats-for-smart-city-tech)
- Enterprise IoT Statistics and Facts (2026) (https://scoop.market.us/enterprise-iot-statistics)
- Client Testimonials & Reviews – Promeraki IoT (https://promeraki.com/testimonials)
- IoT Device Growth Statistics & Trends (2026) (https://thenetworkinstallers.com/blog/iot-device-growth-statistics)
- Make Your Final Decision
- AT&T Launches Our First End-to-End IoT Solution on the AWS Marketplace (https://about.att.com/story/2026/connected-spaces-aws-marketplace.html)
- 75+ Latest IoT Statistics and Growth Trends 2026 (https://esparkinfo.com/iot/statistics)
- IoT Device Growth Statistics & Trends (2026) (https://thenetworkinstallers.com/blog/iot-device-growth-statistics)
- IoT Now Contract Win List – February 2026 | IoT Now News & Reports (https://iot-now.com/2026/03/06/155674-iot-now-contract-win-list-february-2026)
- IoT in 2026: the technologies driving the next wave of IoT growth (https://iotinsider.com/iot-insights/iot-in-2026-the-technologies-driving-the-next-wave-of-iot-growth)
Introduction
Effective PHP development outsourcing serves as a pivotal strategy for businesses aiming to enhance their digital capabilities while optimizing costs. By adhering to established best practices, organizations can streamline their project objectives and engage the right partners to actualize their vision. However, the journey toward successful outsourcing is often riddled with challenges, including ambiguous project requirements and ineffective communication.
How can companies effectively navigate these complexities to foster seamless collaboration and achieve high-quality outcomes?
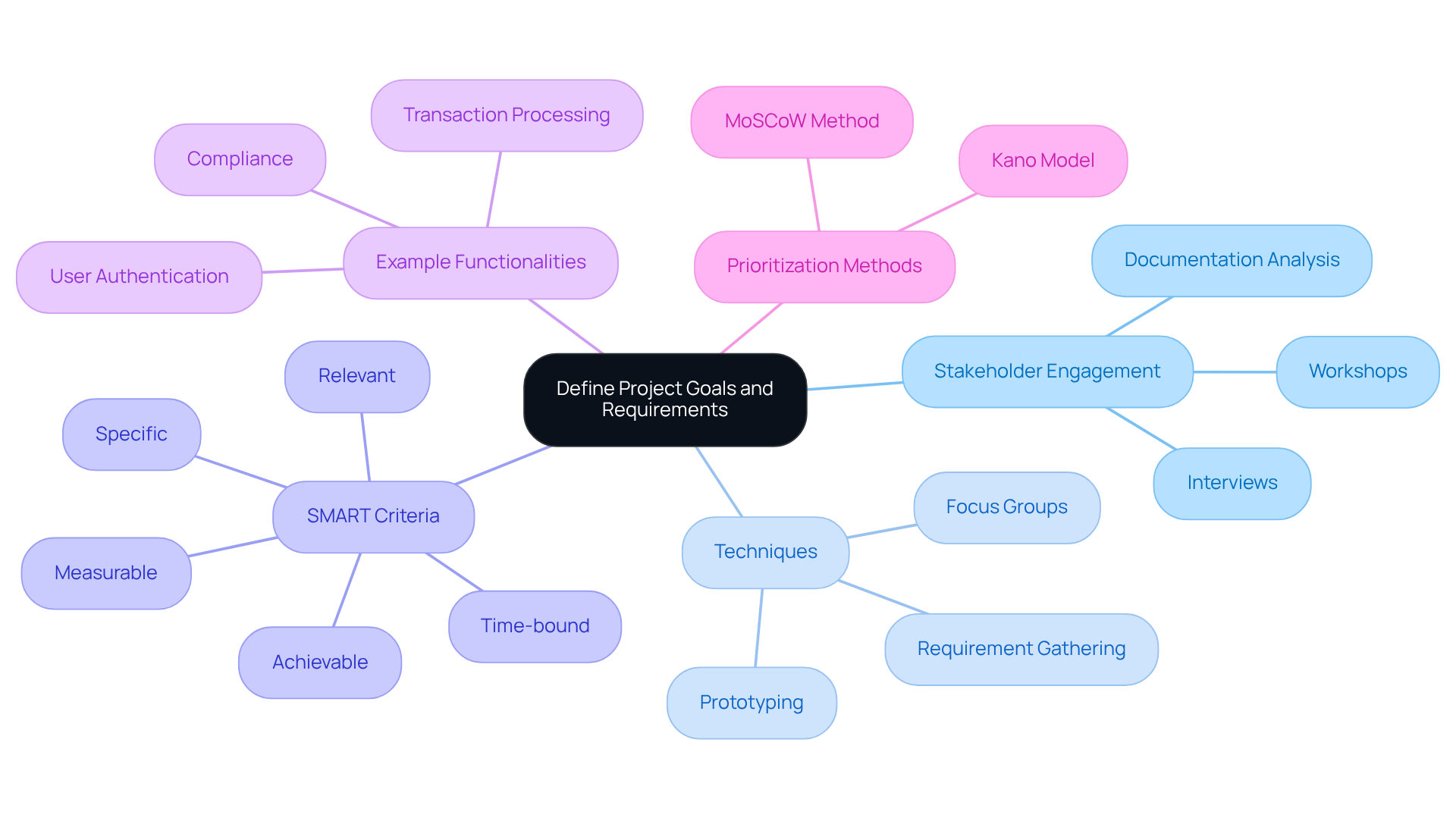
Define Project Goals and Requirements
To effectively outsource development, it is crucial to start with a project plan. Engaging all stakeholders is vital for capturing their requirements and expectations accurately. Techniques such as stakeholder interviews, workshops, and thorough documentation analysis can facilitate the requirements gathering process. By adopting the SMART criteria – Specific, Measurable, Achievable, Relevant, and Time-bound – you ensure that the scope of your initiative is well-defined. This clarity not only guides the progression process but also aids in selecting the appropriate outsourcing partner capable of fulfilling these specified needs.
Once we collaboratively identify your needs through our tailored methodologies, including assessments and consultations, we will provide you with a selection of candidate designers and developers to integrate into your team. This customized approach ensures that the engineering talent supplied aligns seamlessly with your requirements.
For example, when developing a financial application, it is essential to specify functionalities such as:
- Transaction processing
- User authentication
- Compliance with regulations like PCI DSS
This thorough approach not only assists in project planning but also lays the groundwork for effective management and quality assurance throughout the project lifecycle. By defining and establishing clear objectives, organizations can significantly improve the likelihood of successful outcomes in their initiatives related to software development. Furthermore, employing the MoSCoW method to prioritize needs can streamline the process, ensuring that critical features are addressed first. By acknowledging the challenges posed by unclear or insufficient requirements, teams can better prepare for potential misunderstandings and enhance overall success.
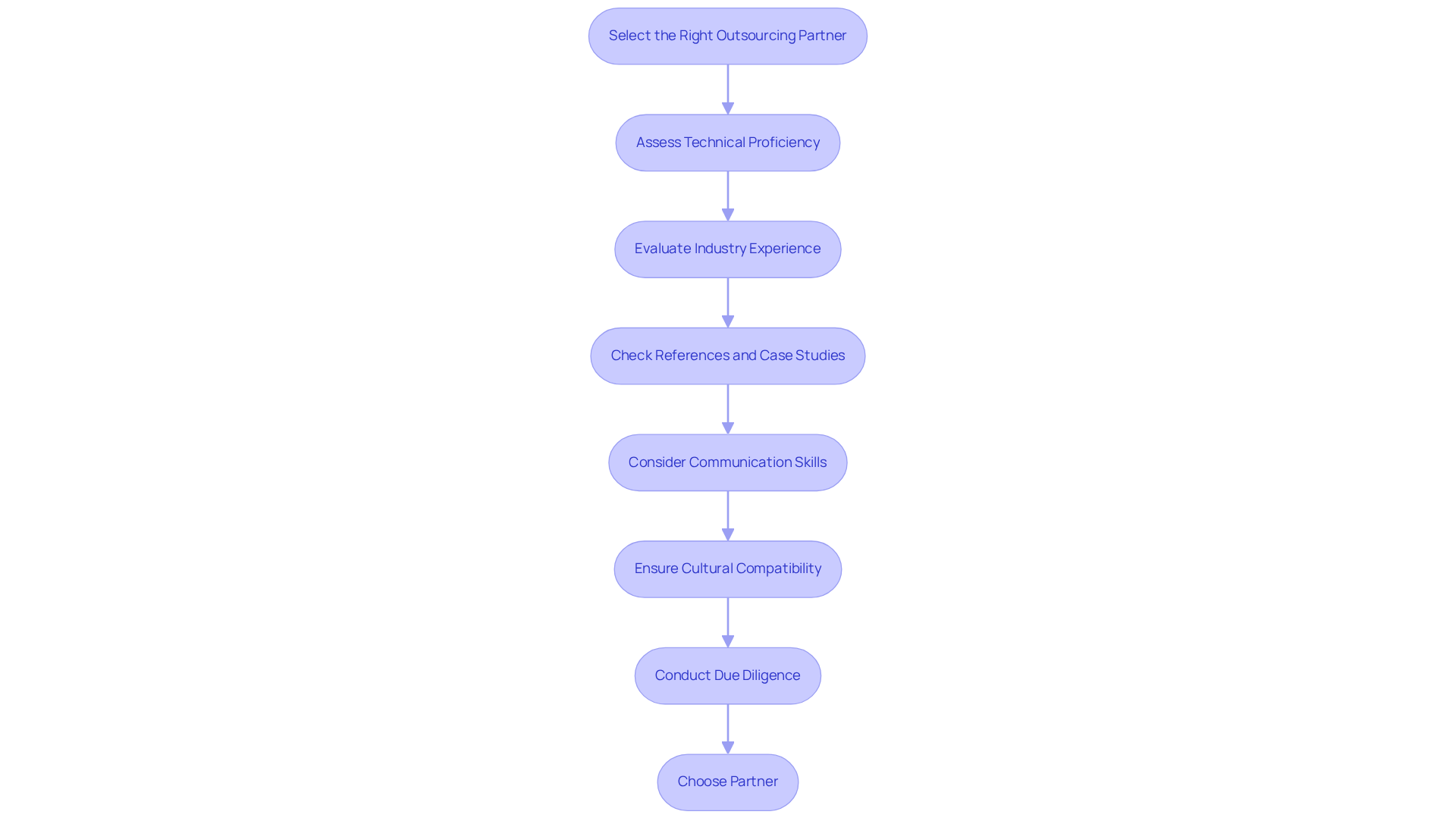
Select the Right Outsourcing Partner
Selecting the appropriate outsourcing partner necessitates a thorough evaluation of potential candidates. Begin by assessing their technical proficiency in programming and their experience within your specific industry. It is crucial to prioritize partners who have successfully executed initiatives similar to yours and can provide references that showcase their capabilities. Recent trends indicate that 80% of companies intend to maintain or increase their outsourcing efforts, highlighting the significance of careful partner selection.
In this context, we recognize that a tailored approach is vital. After collaboratively identifying your needs, we present several potential designers and developers who can seamlessly integrate into your team, ensuring their skills align with your requirements. Our services encompass assessing your specific needs and supplying specialized talent that meets your project goals.
Moreover, communication skills are essential for successful collaboration. A partner whose values and communication style resonate with your organization will facilitate smoother interactions. Conduct interviews and request proposals to gauge their understanding of your requirements. For instance, when engaging in outsourcing for a healthcare project, it is imperative to ensure that the partner is well-versed in HIPAA compliance and possesses a comprehensive understanding of the complexities involved in healthcare software development. Additionally, be vigilant about potential pitfalls such as inadequate customer service or missed deadlines, which can derail your plans. As Anna, a content manager, underscores, conducting thorough research is crucial to avoid common outsourcing mistakes.
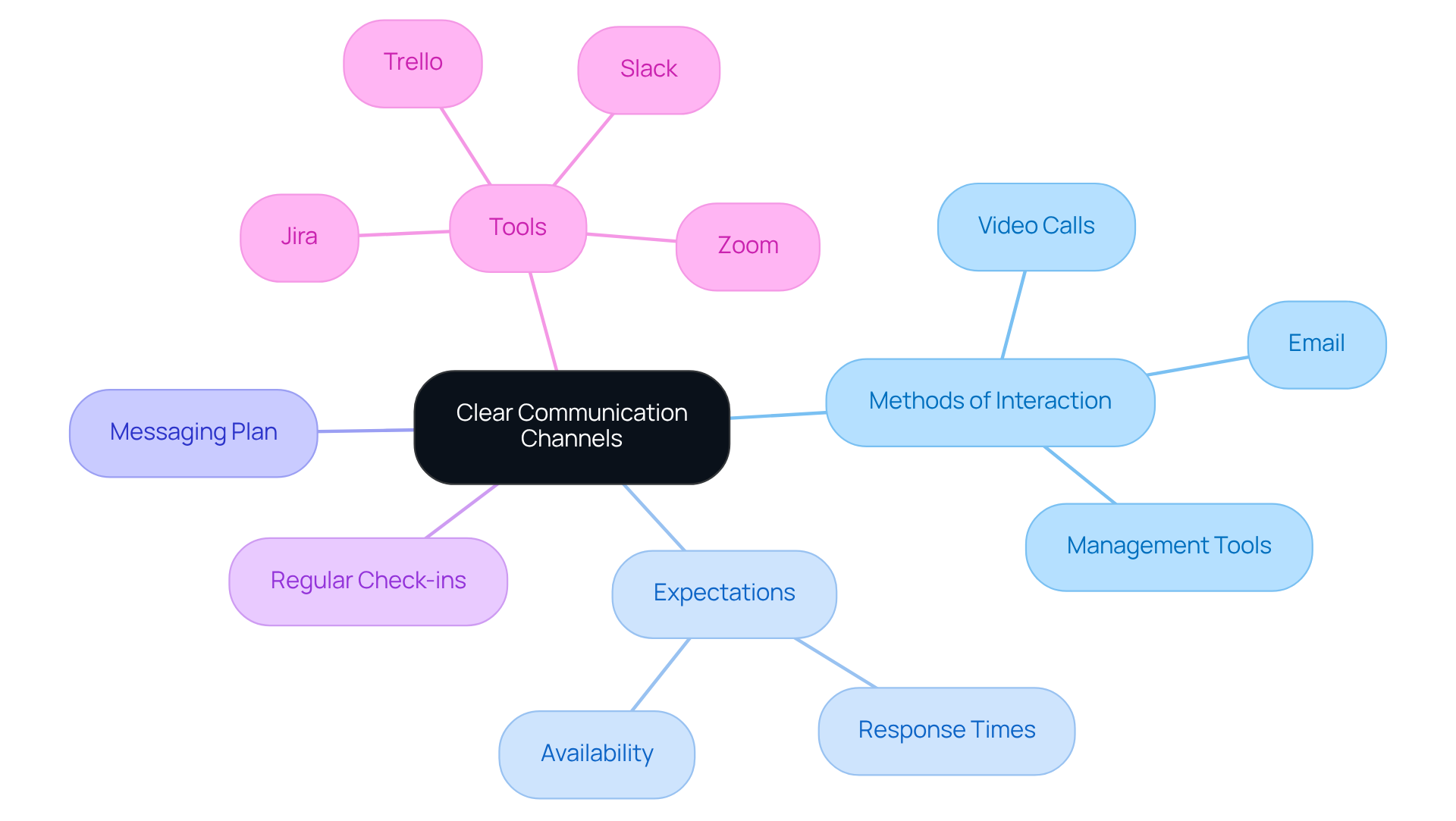
Establish Clear Communication Channels
To foster effective collaboration with your team, establishing clear information pathways from the outset is crucial. Begin by specifying the primary methods of interaction – such as email, video calls, and management tools – while also setting expectations for response times and availability. Additionally, develop a communication plan that delineates roles to ensure alignment among all parties involved.
Regular check-ins, including status updates, are vital for maintaining alignment and promptly addressing any emerging issues. Utilizing project management tools like Jira or Trello enhances visibility and facilitates progress monitoring. For teams operating across various time zones, employing scheduling tools can aid in coordinating meetings efficiently, while asynchronous interaction strategies ensure that updates and feedback are exchanged effectively.
This organized approach not only sustains momentum but also cultivates a collaborative environment, ultimately driving success. It is noteworthy that 70% of outsourced software projects fail due to miscommunication, underscoring the critical importance of these practices.
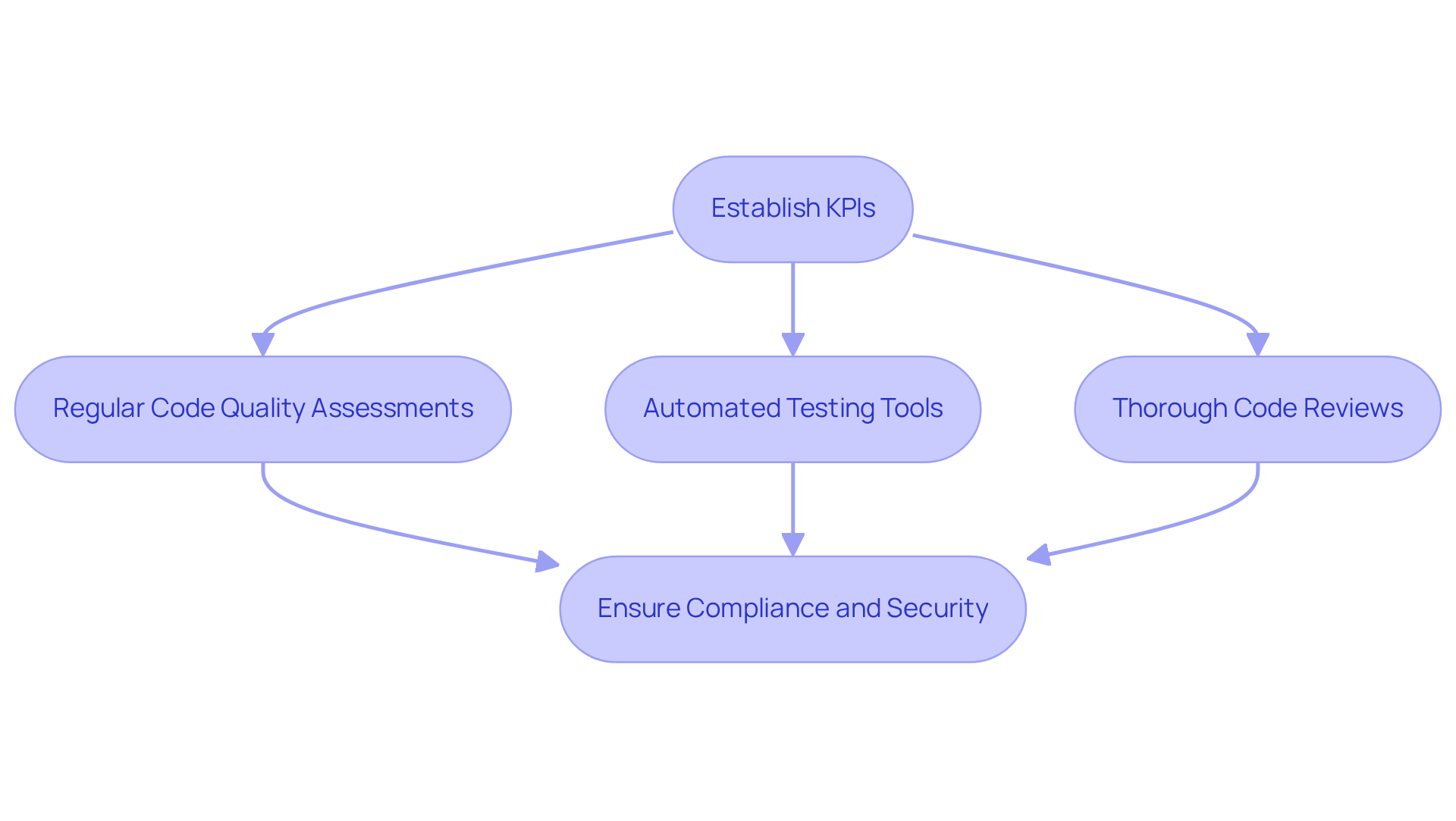
Monitor Progress and Ensure Quality Control
To uphold exceptional standards in software development, establishing a comprehensive quality control process is essential. Key performance indicators (KPIs) play a crucial role in evaluating progress and quality throughout various stages of development. Regular assessments of code quality and compliance with requirements are fundamental components of this process.
Employing best practices and conducting thorough code reviews can facilitate the early identification of issues within the development cycle. For example, in projects involving financial transactions, it is imperative to rigorously test security measures to mitigate vulnerabilities. Given that modern secure software practices necessitate testing during each sprint, adopting a proactive approach to monitoring progress and quality guarantees that the final product is not only reliable and secure but also compliant with all requisite standards.
Furthermore, establishing clear communication protocols can help bridge potential gaps, particularly when collaborating across different time zones. By maintaining a proactive stance on project updates, you can ensure that the final product is dependable, secure, and meets all necessary specifications.
Conclusion
Effective PHP development outsourcing relies on a structured approach that emphasizes clarity, communication, and quality control. By clearly defining project goals and requirements, organizations establish a solid foundation for successful collaboration with outsourcing partners. This clarity streamlines the selection process and ensures alignment among all stakeholders, significantly increasing the chances of achieving desired outcomes.
The article highlights several best practices, including:
- The selection of the right outsourcing partner who possesses the necessary technical skills and industry experience.
- The establishment of clear communication channels for seamless collaboration.
- The implementation of robust monitoring and quality control measures.
Each of these elements is crucial in navigating the complexities of outsourcing, ultimately leading to the delivery of reliable and secure PHP solutions.
As the landscape of PHP development outsourcing evolves, adopting these best practices becomes essential for organizations looking to leverage external expertise effectively. By committing to thorough planning, proactive communication, and diligent quality assurance, businesses can mitigate common pitfalls and fully realize the potential of their outsourcing initiatives. Implementing these strategies will foster successful partnerships that drive innovation and growth in the competitive digital marketplace.
Frequently Asked Questions
Why is it important to define project goals and requirements before outsourcing PHP development?
Defining project goals and requirements is crucial as it ensures clarity on objectives and needs, which helps in capturing stakeholder expectations accurately and guides the selection of an appropriate outsourcing partner.
What techniques can be used to gather comprehensive requirements for a project?
Techniques include stakeholder interviews, workshops, and thorough documentation analysis to facilitate the gathering of comprehensive requirements.
What does the SMART criteria stand for, and why is it important?
The SMART criteria stands for Specific, Measurable, Achievable, Relevant, and Time-bound. It is important because it helps ensure that the scope of the initiative is well-defined, guiding the project progression and aiding in vendor selection.
How does Neutech assist in identifying project needs for PHP development outsourcing?
Neutech engages stakeholders through tailored methodologies to identify needs and then provides a selection of candidate designers and developers that align with those requirements.
Can you provide an example of specific functionalities that should be defined when developing a financial application?
Examples of specific functionalities include transaction processing, user authentication, and compliance with regulations like PCI DSS.
How does prioritizing stakeholder input and establishing clear objectives contribute to project success?
Prioritizing stakeholder input and establishing clear objectives significantly improves the likelihood of successful outcomes by ensuring that all requirements are understood and addressed throughout the project lifecycle.
What is the MoSCoW method, and how does it help in project management?
The MoSCoW method is a prioritization technique that categorizes features into Must have, Should have, Could have, and Won’t have. It helps streamline the process by ensuring that critical features are addressed first.
What challenges can arise from unclear or insufficient project requirements?
Challenges include misunderstandings among team members, which can lead to project delays, increased costs, and ultimately, a higher likelihood of project failure.
List of Sources
- Define Project Goals and Requirements
- Best Practices for Outsourcing Software Development in 2026 (https://onix-systems.com/blog/best-practices-for-outsourcing-software-development)
- Outsourcing Software Development in 2026: Best Practices (https://futureforward.nl/blog/outsourcing-software-development-in-2026-best-practices)
- Gathering requirements for a development project in 2025 (https://developer-tech.com/news/gathering-requirements-for-a-development-project-in-2025)
- Top 50 Project Management Statistics for 2026 Success (https://ravetree.com/blog/top-50-project-management-statistics)
- How to Successfully Outsource Software Development Projects – nCube (https://ncube.com/how-to-outsource-software-development-projects-successfully)
- Select the Right Outsourcing Partner
- How To Choose Your Ideal Outsourcing Partner in 8 Steps (https://senlainc.com/blog/how-to-choose-your-ideal-outsourcing-partner)
- Software Development Outsourcing Statistics You Need To Know in 2026 (https://10pearls.com/software-development-outsourcing-statistics-2025)
- Belitsoft Reviews PHP Development Outsourcing Trends in the USA for 2026 (https://openpr.com/news/4428521/belitsoft-reviews-php-development-outsourcing-trends-in-the-usa)
- Development Outsourcing Partner Selection Guide for 2026 (https://vettedoutsource.com/blog/choose-outsourcing-partner)
- How to choose a software development outsourcing partner (https://fusionhit.com/blog/how-to-choose-a-software-development-outsourcing-partner)
- Establish Clear Communication Channels
- 7 Strategies for Effective Communication with Your Outsourcing Team (https://linkedin.com/pulse/7-strategies-effective-communication-your-outsourcing-team-coordea-yonhc)
- Effective Software Development and Outsourcing Tactics (https://acquirex.io/blog/effective-software-development-and-outsourcing-tactics)
- Communication in Software Development Outsourcing – TopDevelopers.co (https://topdevelopers.co/blog/communication-in-software-development)
- Effective Communication Strategies in Software Outsourcing (https://mltechsoft.com/blog/communication-strategies-in-software-outsourcing)
- Best Development Team Outsource Strategies for Successful Projects (https://cognativ.com/blogs/post/best-development-team-outsource-strategies-for-successful-projects/226)
- Monitor Progress and Ensure Quality Control
- The Importance of Monitoring and Managing Outsourced Software Developers! – Supply Chain Game Changer™ (https://supplychaingamechanger.com/the-importance-of-monitoring-and-managing-outsourced-software-developers)
- The 2026 Software Development Outsourcing Report: Quality, Cost, and Time-to-Market Benchmarks – Muddy River News (https://muddyrivernews.com/business/sponsored-content/the-2026-software-development-outsourcing-report-quality-cost-and-time-to-market-benchmarks/20260312070036)
- What are the most effective ways to monitor progress on outsourced software development projects? (https://linkedin.com/advice/1/what-most-effective-ways-monitor-progress-outsourced)
- A CTO’s Guide to Quality Control Systems in Outsourced Software Development (https://fullscale.io/blog/quality-control-system-outsourced-development)
- 14 Methods To Measure The Performance Of Outsourced Developers (https://forbes.com/councils/forbestechcouncil/2022/06/06/15-methods-to-measure-the-performance-of-outsourced-developers)
Introduction
As organizations increasingly rely on data to drive decision-making, the methods used to manage this information are undergoing a significant transformation. This article examines the comparative landscape of traditional data engineering techniques, which have dominated for decades, against the backdrop of modern innovations that promise greater flexibility and efficiency. With the rise of real-time processing and AI integration, a pressing question arises: can traditional methods keep pace with the demands of a rapidly evolving data landscape, or are they destined to become obsolete?
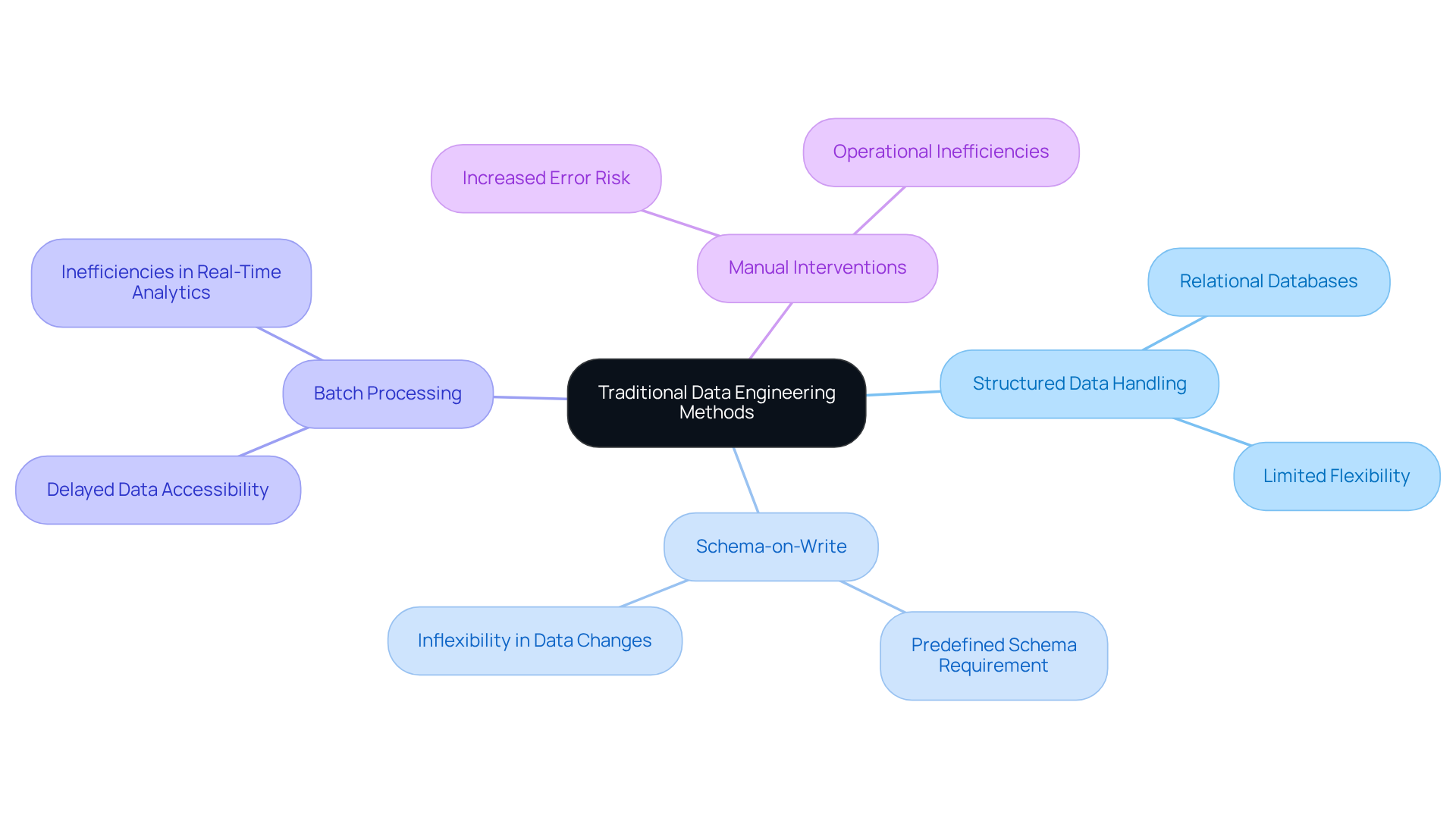
Overview of Traditional Data Engineering Methods
Conventional engineering approaches primarily revolve around the data pipeline. This method involves retrieving information from multiple sources, converting it into an appropriate format, and loading it into a repository for analysis. Key characteristics of this approach include:
- Structured Data Handling: Traditional methods excel in managing structured data, often relying on relational databases.
- Schema-on-Write: Data must conform to a predefined schema before being loaded, which can limit flexibility.
- Batch Processing: Information is processed in groups, resulting in delays in accessibility for immediate analytics.
- Manual Interventions: Many processes require manual oversight, increasing the risk of errors and inefficiencies.
While these methods have benefited industries for decades, they are increasingly viewed as outdated and inadequate for contemporary information requirements. This is particularly true in fields such as finance and healthcare, where real-time data access is critical. By 2026, over 70 percent of organizations are anticipated to employ modern data strategies, reflecting a significant shift towards more agile information handling practices. Specialists emphasize that the evolution of information processing necessitates a transition from traditional methods to align with the future, adapting to the rapid pace of change in data requirements and technology. Furthermore, 77 percent of organizations assess their data management capabilities as average or poorer, underscoring the challenges faced in conventional data engineering. Additionally, 55 percent of AI-driven applications require near-real-time information ingestion, highlighting the urgency for modern information solutions in regulated sectors. As noted by Shamnad Mohamed Shaffi, this approach eliminates the complexities associated with traditional ETL processes.
Exploration of Modern Innovations in Data Engineering
Contemporary advancements in data engineering underscore the importance of flexibility, scalability, and real-time processing, fundamentally transforming how organizations manage and utilize information. Key advancements include:
- ELT: This method enables data to be loaded into a data lake prior to transformation, facilitating quicker access to raw data for analytics. By 2026, the adoption of ELT is projected to surpass that of traditional ETL processes, as organizations recognize the efficiency gains from accessing raw information. Notably, the field of information science is anticipated to shift its focus away from micro-level quality management, reflecting the evolving practices in information development.
- Cloud platforms: Platforms such as AWS, Google Cloud, and Azure offer scalable infrastructure capable of dynamically supporting varying information workloads. Approximately 78% of organizations have centralized their data management, thereby enhancing the strategic role of data engineering within enterprises.
- Stream processing technologies: Technologies like Apache Kafka and Apache Flink facilitate continuous stream processing, enabling organizations to respond to incoming information instantaneously. This is becoming a baseline expectation, with companies leveraging these tools to secure competitive advantages.
- Data mesh: This decentralized approach encourages domain-oriented ownership of information, fostering collaboration and reducing bottlenecks in access and processing.
- AI integration: The integration of AI into information processing workflows automates routine tasks, thereby enhancing efficiency and precision. As generative AI continues to evolve, it is expected to become a fundamental layer in information processing, optimizing workflows and improving quality. Furthermore, roles related to information construction are being impacted more significantly by AI than other technology roles, indicating a profound transformation within the field.
These innovations effectively address the limitations of traditional approaches, rendering data engineering more adaptable to the needs of enterprises operating in dynamic environments.
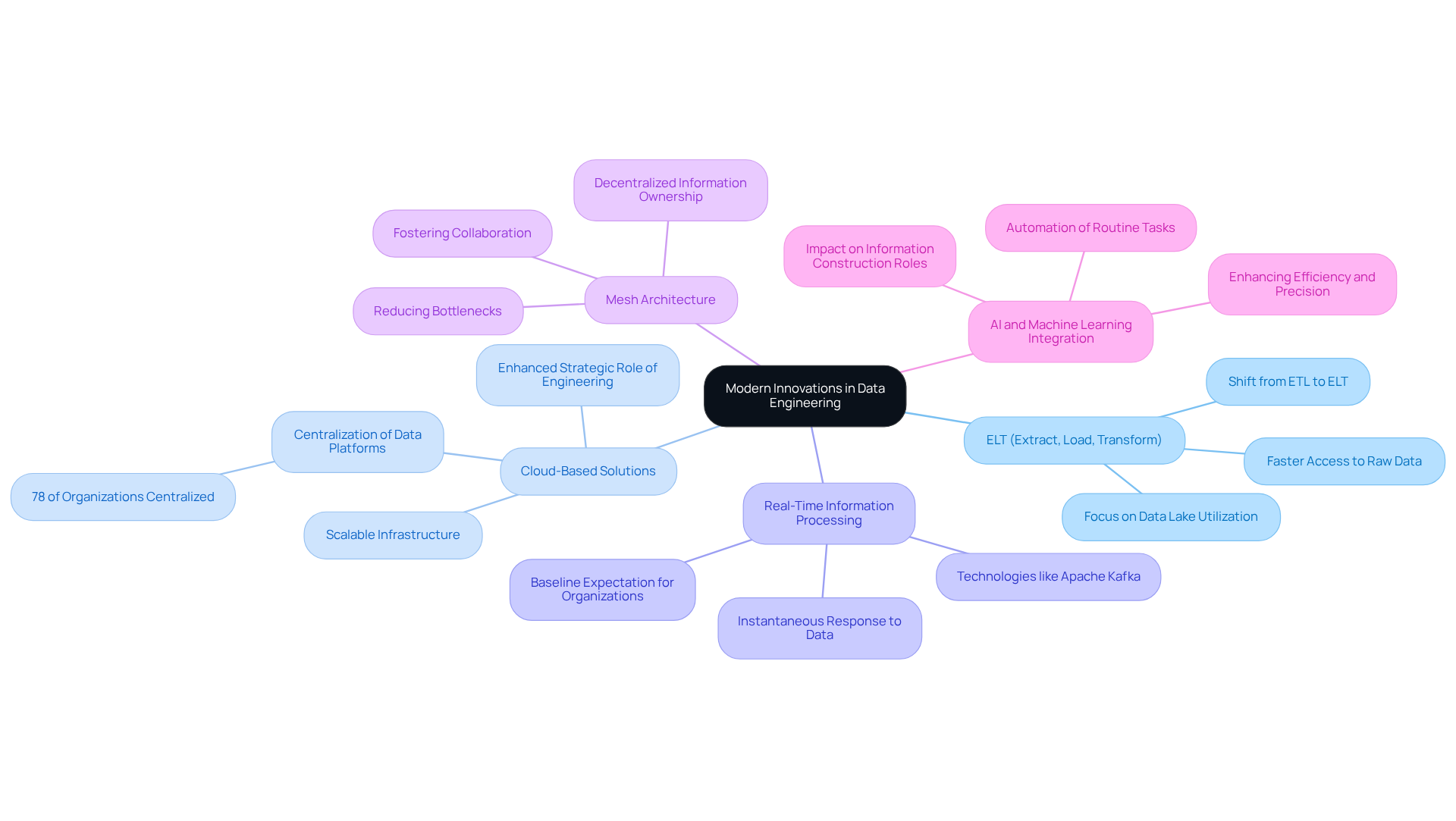
Comparative Analysis: Traditional Methods vs. Modern Innovations
- Criteria
- Data Handling
- Primarily structured data
- Supports unstructured data
- Processing Model
- Batch processing
- Real-time and stream processing
- Flexibility
- Rigid schema requirements
- Schema-on-read, allowing for greater flexibility
- Scalability
- Limited scalability
- Highly scalable through cloud solutions
- Automation
- Manual interventions required
- Automated workflows available
- Cost Efficiency
- Higher operational costs due to infrastructure
- Lower costs with pay-as-you-go models
- Data Handling
This analysis indicates that while traditional methods possess certain advantages, modern methods excel in flexibility, scalability, and efficiency. These attributes render modern approaches more suitable for contemporary data-driven organizations.
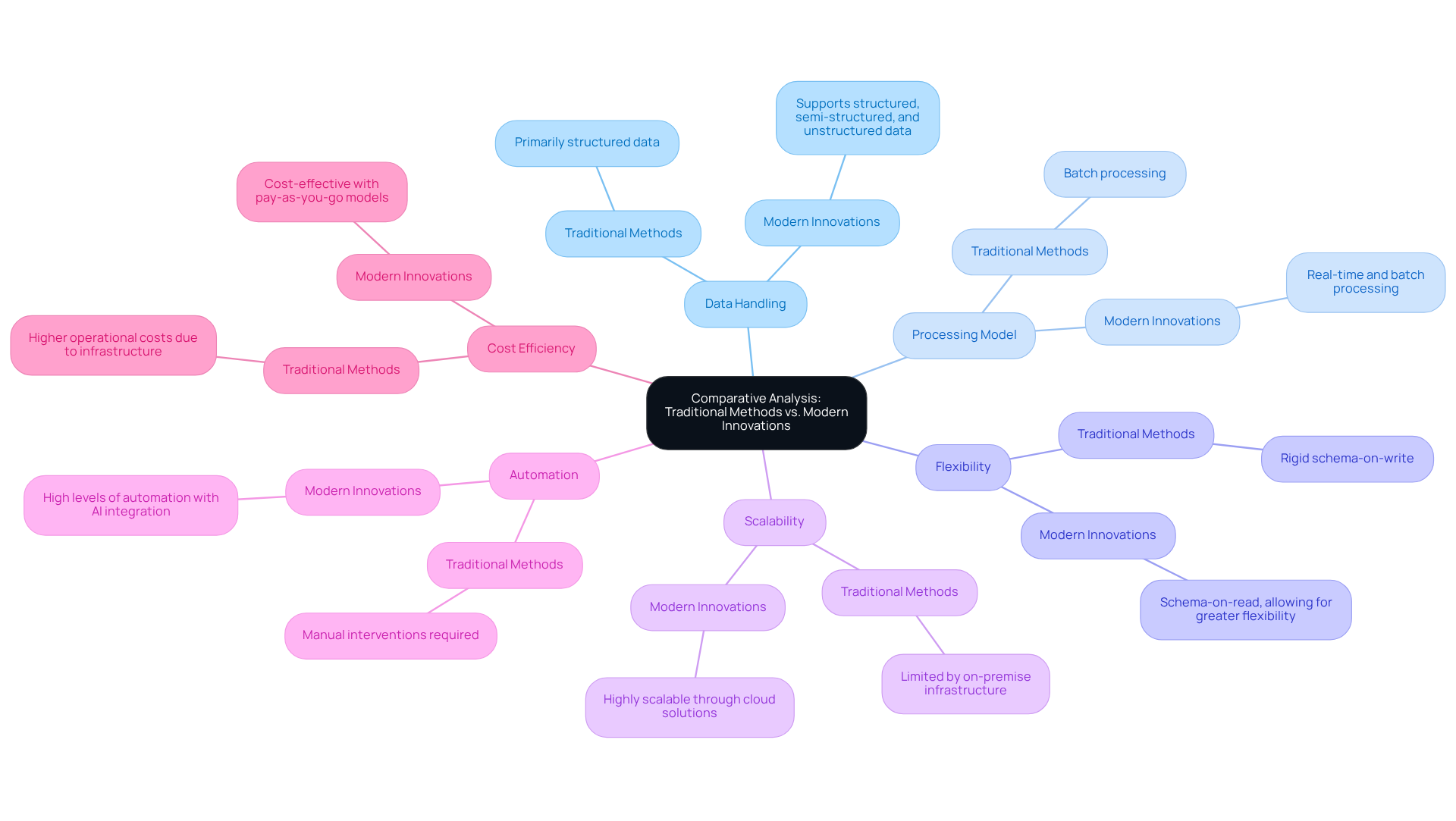
Choosing the Right Approach: Suitability for Different Industries
When selecting a data engineering approach, organizations must consider their specific industry requirements:
Financial Services: This sector demands security due to the sensitive nature of financial data. Innovations such as real-time processing and data analytics are critical for compliance. A team with strong work ethic and communication skills ensures that teams can navigate these complexities effectively. Additionally, our month-to-month staffing flexibility allows financial institutions to scale resources as needed.
Healthcare: Managing sensitive patient information necessitates robust security measures. A secure infrastructure can protect information integrity while enabling prompt insights. Neutech’s commitment to leadership and teamwork among its engineers fosters a collaborative environment crucial for meeting these regulatory demands. Furthermore, our staffing solutions enable healthcare providers to adjust their teams based on fluctuating needs.
Retail: This industry flourishes on customer insights. Contemporary information processing techniques are especially efficient for handling significant amounts of transactional information swiftly, allowing retailers to react to consumer behavior and preferences instantly. Neutech’s ability to provide resources on a month-to-month basis allows retailers to scale their development resources efficiently.
Manufacturing: The incorporation of IoT information for predictive maintenance is vital in this sector. Contemporary methods that support data integration are essential for operational efficiency, enabling manufacturers to foresee equipment failures and enhance production processes. Neutech’s flexible staffing model helps manufacturers adapt to changing technological landscapes with ease.
By understanding the unique needs of their industry and leveraging Neutech’s expertise, organizations can make informed decisions about which data engineering future methods to adopt, ensuring they remain competitive and compliant.
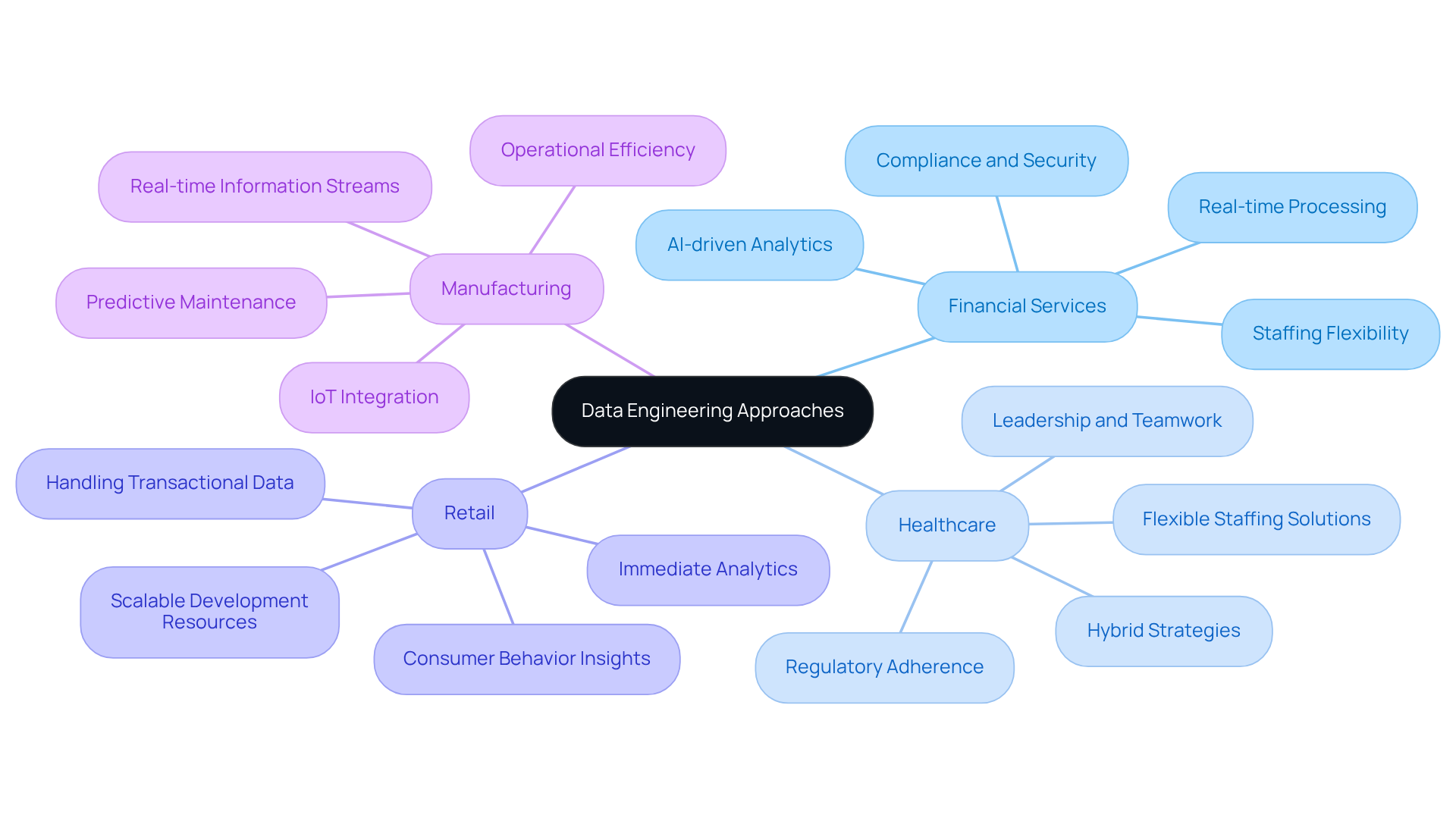
Conclusion
The landscape of data engineering is evolving rapidly, necessitating a shift from traditional methods to modern innovations that better meet the demands of today’s data-driven environments. While conventional approaches like ETL have served organizations well for years, their limitations in flexibility, scalability, and real-time processing highlight the urgent need for more adaptive solutions. Embracing modern methodologies allows organizations to harness the full potential of their data, ensuring they remain competitive in an increasingly complex market.
Key insights from the comparative analysis reveal that modern innovations, such as ELT, cloud-based solutions, and real-time processing, significantly enhance data management capabilities. These advancements not only improve efficiency but also facilitate better decision-making across various industries, from finance to healthcare. Moreover, the integration of AI and machine learning into data workflows automates routine tasks, further streamlining operations and reducing the risk of human error.
As organizations navigate their data engineering futures, it is crucial to recognize the specific needs of their sectors and choose the appropriate methodologies accordingly. By leveraging the strengths of modern data engineering techniques, businesses can enhance their operational efficiency, ensure compliance with industry regulations, and ultimately drive innovation. The transition to contemporary data practices is not merely advantageous; it is essential for thriving in an era defined by rapid technological change and increasing data complexity.
Frequently Asked Questions
What is the traditional data engineering method primarily based on?
The traditional data engineering method is primarily based on the Extract, Transform, Load (ETL) process, which involves retrieving information from multiple sources, converting it into an appropriate format, and loading it into a repository for analysis.
What are the key characteristics of traditional data engineering methods?
Key characteristics include structured data handling, schema-on-write requirements, batch processing, and the need for manual interventions.
How do traditional methods handle structured data?
Traditional methods excel in managing structured data and often rely on relational databases for this purpose.
What does schema-on-write mean in the context of traditional data engineering?
Schema-on-write means that data must conform to a predefined schema before being loaded into the system, which can limit flexibility.
What is the impact of batch processing in traditional data engineering?
Batch processing involves processing information in groups, which can lead to delays in accessibility for immediate analytics.
Why are manual interventions a concern in traditional data engineering methods?
Manual interventions increase the risk of errors and inefficiencies in the data processing workflow.
Why are traditional data engineering methods considered insufficient for modern needs?
They are viewed as insufficient because they struggle to meet the demands for real-time insights, particularly in industries like finance and healthcare.
What is the anticipated trend for organizations regarding cloud repositories by 2026?
By 2026, over 90 percent of mid-to-large organizations are expected to employ cloud repositories, indicating a shift towards more agile information handling practices.
What challenges do organizations face with conventional information management?
77 percent of organizations assess their information quality as average or poorer, highlighting challenges in conventional information management.
What is zero-ETL, and why is it significant?
Zero-ETL is a transformative approach that eliminates the complexities associated with traditional ETL processes, making it significant for adapting to the evolving needs of data engineering.
List of Sources
- Overview of Traditional Data Engineering Methods
- Industry News 2025 The Zero ETL Paradigm Transforming Enterprise Data Integration in Real Time (https://isaca.org/resources/news-and-trends/industry-news/2025/the-zero-etl-paradigm-transforming-enterprise-data-integration-in-real-time)
- Data Engineering Stats 2026: Latest Market Insights & Trends (https://data.folio3.com/blog/data-engineering-stats)
- How AI is Transforming Data Engineering (https://databricks.com/blog/how-ai-transforming-data-engineering)
- How the last 6 months of AI rewrote the rules of data engineering (https://datapro.news/p/how-last-6-months-of-ai-rewrote-the-rules-of-data-engineering)
- ETL to dbt: Evolution of Data Engineering | Sumit Gupta posted on the topic | LinkedIn (https://linkedin.com/posts/sumonigupta_for-years-etl-was-the-standard-extract-activity-7432401162567335936-ND2p)
- Exploration of Modern Innovations in Data Engineering
- Data Engineering Trends in 2026: Key Innovations & Future Insights (https://softwebsolutions.com/resources/data-engineering-trends)
- Data Engineering in 2026: What Changes? (https://gradientflow.substack.com/p/data-engineering-for-machine-users)
- Refonte Learning : Data Engineering in 2026: Trends, Tools, and How to Thrive (https://refontelearning.com/blog/data-engineering-in-2026-trends-tools-and-how-to-thrive)
- Data Engineering in 2026: 12 Predictions (https://datafold.com/blog/data-engineering-in-2026-predictions)
- From ETL to Autonomy: Data Engineering in 2026 (https://thenewstack.io/from-etl-to-autonomy-data-engineering-in-2026)
- Comparative Analysis: Traditional Methods vs. Modern Innovations
- Modern Data Platform Vs. Traditional Data Platform: Where To Invest Your Time And Money? (https://affine.medium.com/modern-data-platform-vs-traditional-data-platform-where-to-invest-your-time-and-money-6c4ddb5543a9)
- Modern Data Stack 2026: Building the Foundation for AI Success (https://alation.com/blog/modern-data-stack-explained)
- The battle of old and new: Traditional vs modern data platforms (https://visium.com/articles/the-battle-of-old-and-new-traditional-vs-modern-data-platforms)
- Refonte Learning : Data Engineering in 2026: Trends, Tools, and How to Thrive (https://refontelearning.com/blog/data-engineering-in-2026-trends-tools-and-how-to-thrive)
- Choosing the Right Approach: Suitability for Different Industries
- Major Healthcare Data Security Trends in 2025 – Bluesight (https://bluesight.com/news/major-healthcare-data-security-trends-in-2025)
- How Advanced Data Analytics Drives Decision-Making in Financial Services (https://biztechmagazine.com/article/2025/08/how-advanced-data-analytics-drives-decision-making-financial-services)
- How Financial Firms Are Transforming Data Management (https://dtcc.com/dtcc-connection/articles/2025/september/30/how-financial-firms-are-transforming-data-management)
- Providers Evaluate Security as Updated HIPAA Compliance Looms (https://healthtechmagazine.net/article/2026/01/providers-evaluate-security-updated-hipaa-compliance-looms)
Introduction
Mastering a software development budget is a significant challenge, particularly in an environment where accurate financial planning can determine the success or failure of a project. As organizations aim to deliver high-quality software within specified timelines and budgets, grasping the best practices for effective budgeting becomes essential. This article explores four fundamental strategies that not only improve financial oversight but also foster alignment among stakeholders and optimize resource allocation. Given the multitude of variables involved, how can teams effectively navigate the intricacies of budgeting while achieving their project objectives?
Establish Clear Budgeting Goals and Parameters
To master your finances, start by establishing clear budgeting goals and parameters. This involves outlining the initiative’s scope, identifying key deliverables, and setting the budget. Engage early to gather input and ensure alignment on expectations.
For instance, when developing a software project, consider expenses as part of your overall budget, especially with anticipated updates to features. By defining quantifiable goals, such as a maximum financial limit or a timeline for deliverables, you create a framework that guides decision-making throughout the budget process.
As Teceze states, “The companies that will outperform are those that spend with clarity and purpose.” This clarity not only aids in managing expectations but also enhances communication among team members and stakeholders.
Furthermore, a recent case study revealed that a consulting firm saved nearly $240,000 annually by optimizing their budgeting process, highlighting the significance of careful financial planning. Avoiding common pitfalls, such as neglecting compliance expenses or failing to involve key stakeholders, can significantly enhance the success of your initiative.
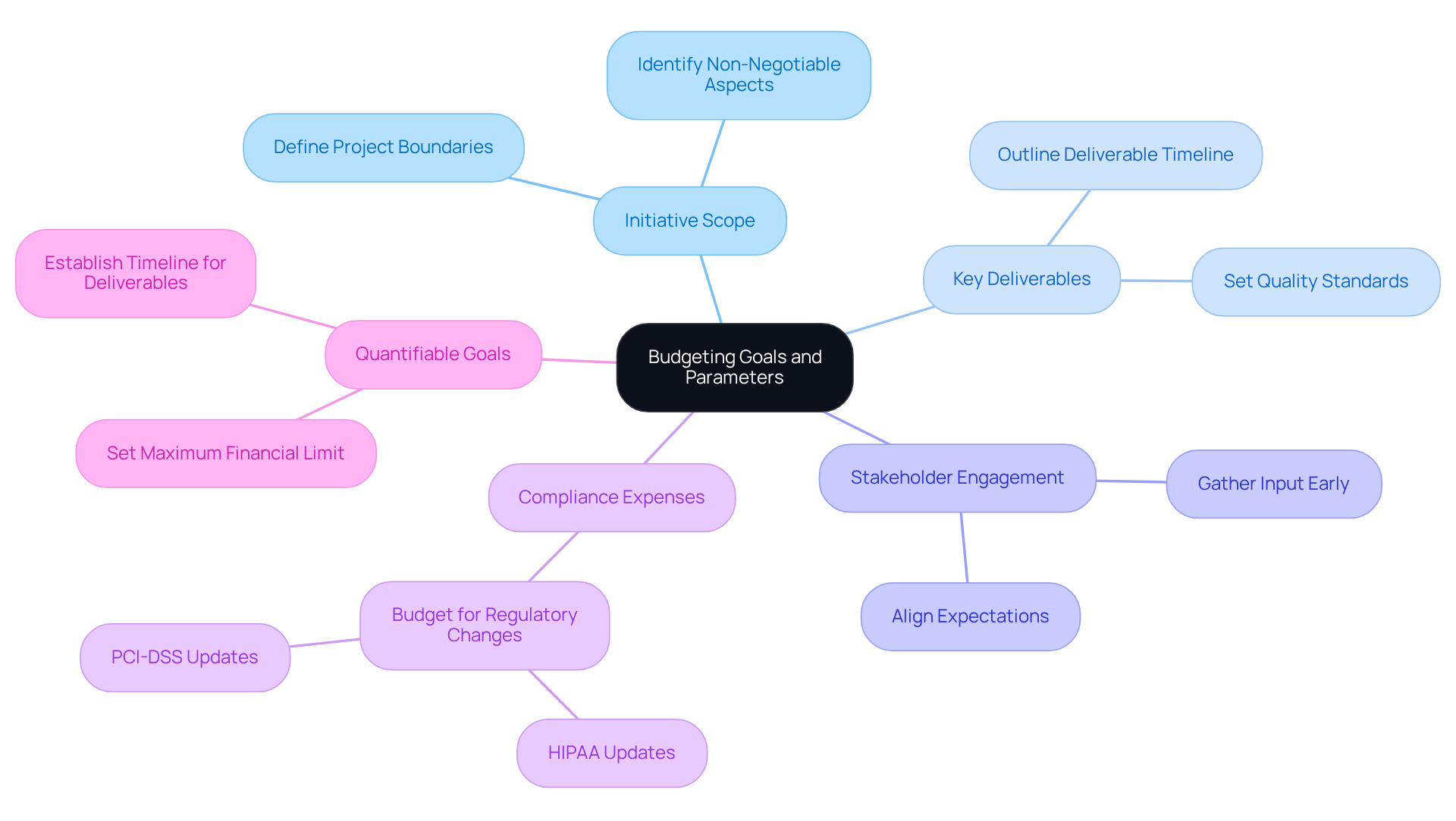
Implement Accurate Cost Estimation Techniques
Precise expenditure estimation is crucial for the success of the project. One of the most reliable techniques is bottom-up estimating, which involves decomposing the project scope and estimating costs for each component. This method proves particularly effective, as it allows for high accuracy in scope estimation and aids in identifying potential bottlenecks early in the process. Organizations that utilize bottom-up estimating often report benefits such as:
- Enhanced accuracy
- Time savings
- Risk reduction
- Improved success rates
- Increased productivity
due to its detailed approach.
Incorporating historical data can further refine your estimates, providing a benchmark for anticipated costs. For example, if a previous task required a specific number of developer hours for a comparable feature, that information can inform your current budget. Moreover, 61% of respondents expect AI to reduce the budget by 10-25%, underscoring the significance of historical data in relation to AI’s impact on budgeting.
Statistics indicate that 66% of firms typically request between $30,000 and $100,000 for small to mid-sized software projects, which illustrates the typical budget reflecting the economic landscape you may encounter.
Additionally, it is wise to allocate a contingency fund, generally 10-20% of the total budget, to cover unforeseen expenses. Most projects benefit from this contingency buffer to accommodate unexpected costs. This proactive approach to budgeting not only aids in maintaining financial control throughout the development process but also prepares you for the challenges that often arise in software projects.
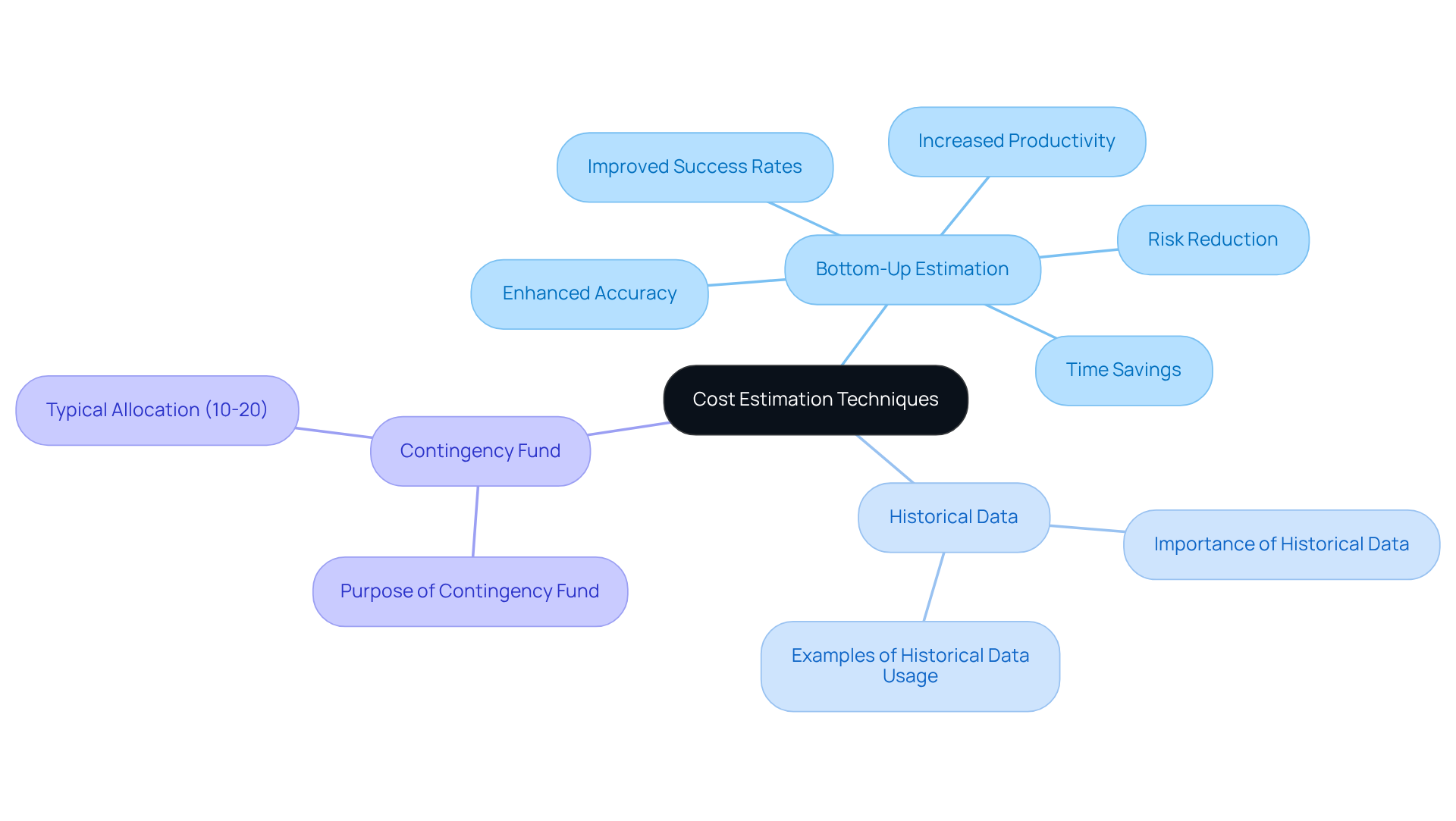
Monitor and Adjust Budget Throughout Development
To effectively manage your budget, it is essential to implement a system for tracking expenses. Management tools such as Zoho Projects or Microsoft Project can facilitate budget management, allowing you to compare expenditures against your financial goals.
Regular reviews of your budget with your team are crucial for identifying discrepancies or areas where the spending may exceed expectations. For instance, if a specific feature requires more time than anticipated, it is important to assess whether adjustments can be made to other aspects of the task.
This iterative approach not only aids in budget control but also fosters a culture of accountability and transparency within the team. As industry experts note, “Monitoring is essential for recognizing financial issues early, allowing for timely interventions and ensuring tasks stay on course.”
Furthermore, a PwC study revealed that only 2.5 percent of firms successfully finalize their projects, underscoring the importance of effective budget management.
![]()
Leverage Specialized Talent for Budget Optimization
Leveraging specialized talent is essential to optimize your budget. Involving specialists with the necessary skills and experience leads to more efficient execution and project outcomes. For example, when addressing software challenges, hiring a developer with a strong background in financial software can significantly enhance output quality and reduce revision time.
Moreover, employing consultants, such as collaborating with a staffing agency, grants access to a pool of vetted engineers ready to meet your specific needs. This strategy not only ensures quality but also allows for the budget to scale as project demands evolve.

Conclusion
Mastering the software development budget requires the implementation of effective practices that ensure financial clarity and control. By establishing clear budgeting goals and parameters, organizations can align their projects with stakeholder expectations, ultimately leading to more successful outcomes. This foundational step lays the groundwork for a disciplined approach to managing finances throughout the development process.
Accurate cost estimation techniques, such as bottom-up estimation and the use of historical data, provide a roadmap for anticipating expenses and mitigating risks. Regular monitoring and adjustments to the budget enable teams to remain agile, responding to challenges as they arise while fostering a culture of accountability. Furthermore, leveraging specialized talent ensures that projects benefit from the expertise necessary to optimize both quality and cost efficiency.
Incorporating these best practices not only enhances budget management but also positions organizations to navigate the complexities of software development with greater confidence. As the landscape of software projects continues to evolve, adopting a strategic approach to budgeting becomes increasingly vital. Embracing these principles can lead to financial savings and improved project success rates, ultimately driving innovation and growth in the competitive software market.
Frequently Asked Questions
What is the first step in mastering software development finances?
The first step is to establish clear budgeting goals and parameters, which involves outlining the initiative’s scope, identifying key deliverables, and setting the software development budget.
Why is stakeholder engagement important in the budgeting process?
Engaging stakeholders early helps gather input and ensures alignment on expectations, which is crucial for successful budgeting.
What should be considered when developing a financial application?
When developing a financial application, it is important to consider regulatory compliance expenses as part of the financial plan, especially with anticipated updates to compliance frameworks like HIPAA and PCI-DSS in 2026.
How can defining quantifiable goals benefit the budgeting process?
Defining quantifiable goals, such as a maximum financial limit or a timeline for deliverables, creates a framework that guides decision-making throughout the software development budget process.
What did Teceze say about companies that manage their spending?
Teceze stated, “The companies that will outperform are those that spend with clarity and purpose,” indicating that clarity in budgeting aids in managing expectations and enhances communication among team members and stakeholders.
What did a recent case study reveal about intentional budgeting practices?
A recent case study showed that a consulting firm saved nearly $240,000 annually by optimizing workloads and automating scaling, highlighting the significance of intentional budgeting practices.
What common pitfalls should be avoided in the budgeting process?
Common pitfalls to avoid include neglecting compliance expenses and failing to involve stakeholders, as these can significantly hinder the success of the initiative.
List of Sources
- Establish Clear Budgeting Goals and Parameters
- Exploring the Relationship Between Project Scope and Budget Control – Pinrom Blog (https://pinrom.co/blog/relationship-between-project-scope-and-budget-control)
- IT Budget Planning 2026: A Simplified Guide for Tech Leaders | Teceze (https://teceze.com/it-budgeting-strategies)
- Tech Spending Trends to Watch in 2026 (https://pcatechsolutions.com/tech-spending-trends-to-watch-in-2026)
- 2026 IT Budget Planning: Where To Cut, Where To Invest (https://axxys.com/blog/it-budgeting-for-2026-where-to-cut-where-to-invest)
- The Importance of Scope Management to Delivering Projects on time and on budget | Recruitment Outsourcing Specialists (https://guidantglobal.com/news/the-importance-of-scope-management-to-delivering-projects-on-time-and-on-budget)
- Implement Accurate Cost Estimation Techniques
- Top-Down vs. Bottom-Up Costing in Smart Projects | CEDIA (https://cedia.org/en-us/smart-home-professionals/news/cost-estimating-bottom-up-vs-top-down)
- Goodfirms Survey: 91% of Software Companies Use AI to Cut Development Costs in 2026 (https://finance.yahoo.com/news/goodfirms-survey-91-software-companies-133000343.html)
- Software Development Cost Estimation Guide 2026 (https://oski.site/blog/software-development-cost-estimation)
- Bottom-Up Estimating in Project Management: A Guide | Wrike (https://wrike.com/blog/bottom-up-estimating-project-management)
- Bottom-Up Estimating: Guide to Accurate Project Costing (https://nomitech.com/cost-estimating/what-is-bottom-up-estimating)
- Monitor and Adjust Budget Throughout Development
- Top 7 Project Budget Management Tools for Cost Control in 2026 (https://productive.io/blog/project-budget-management-tools)
- Project Management Budgeting and Tracking Tools | PMTraining (https://pmtraining.com/about/five-excellent-tools-for-project-managers-to-stay-on-budget)
- 24 Best Project Budget Software Reviewed In 2026 (https://thedigitalprojectmanager.com/tools/best-project-budget-software)
- Top Project Management Software with Financial Tracking in 2026 (https://mastt.com/software/project-management-software-with-financial-tracking)
- Financial Project Management Software: Top Tools for 2026 (https://bigtime.net/blogs/financial-project-management-software)
- Leverage Specialized Talent for Budget Optimization
- Analysis: Why 65% of Tech Leaders are Pivoting to Specialized Contract Talent in 2026 (https://coloradoan.com/press-release/story/63375/analysis-why-65-of-tech-leaders-are-pivoting-to-specialized-contract-talent-in-2026)
- Analysis: Why 65% of Tech Leaders are Pivoting to Specialized Contract Talent in 2026 (https://jacksonville.com/press-release/story/1004961/analysis-why-65-of-tech-leaders-are-pivoting-to-specialized-contract-talent-in-2026)
- Recruiting platforms get HR tech budget priority for 2026. Plus, people move news (https://hrexecutive.com/recruiting-platforms-get-hr-tech-budget-priority-for-2026-plus-people-move-news)
- Software Development Statistics for 2026: Key Facts & Trends (https://itransition.com/software-development/statistics)
Introduction
PHP has become an essential tool in the development of applications within regulated industries, where compliance and security are of utmost importance. As organizations in finance and healthcare increasingly depend on PHP for their critical systems, it is crucial to understand its capabilities and best practices to ensure success. The challenge lies in how developers can guarantee that their PHP applications not only adhere to stringent regulatory standards but also perform optimally in a rapidly changing technological landscape.
Understand the Importance of PHP in Regulated Industries
PHP is a versatile scripting language that serves as a cornerstone for creating solutions in regulated industries, including finance and healthcare. Its capacity for complex data processing, combined with robust security features, positions it as an ideal choice for applications requiring compliance.
In the finance sector, PHP facilitates the development of financial applications, risk management tools, and reporting applications. This enables organizations to effectively manage their data.
In healthcare, PHP powers healthcare applications and telemedicine platforms, safeguarding sensitive patient information while adhering to industry standards. The language’s extensive adoption and strong community support further enhance its reliability in these critical sectors.
Additionally, Neutech provides a variety of development services, including:
- React development
- Python development
- .NET development
This comprehensive suite of services underscores Neutech’s commitment to supporting regulated industries.
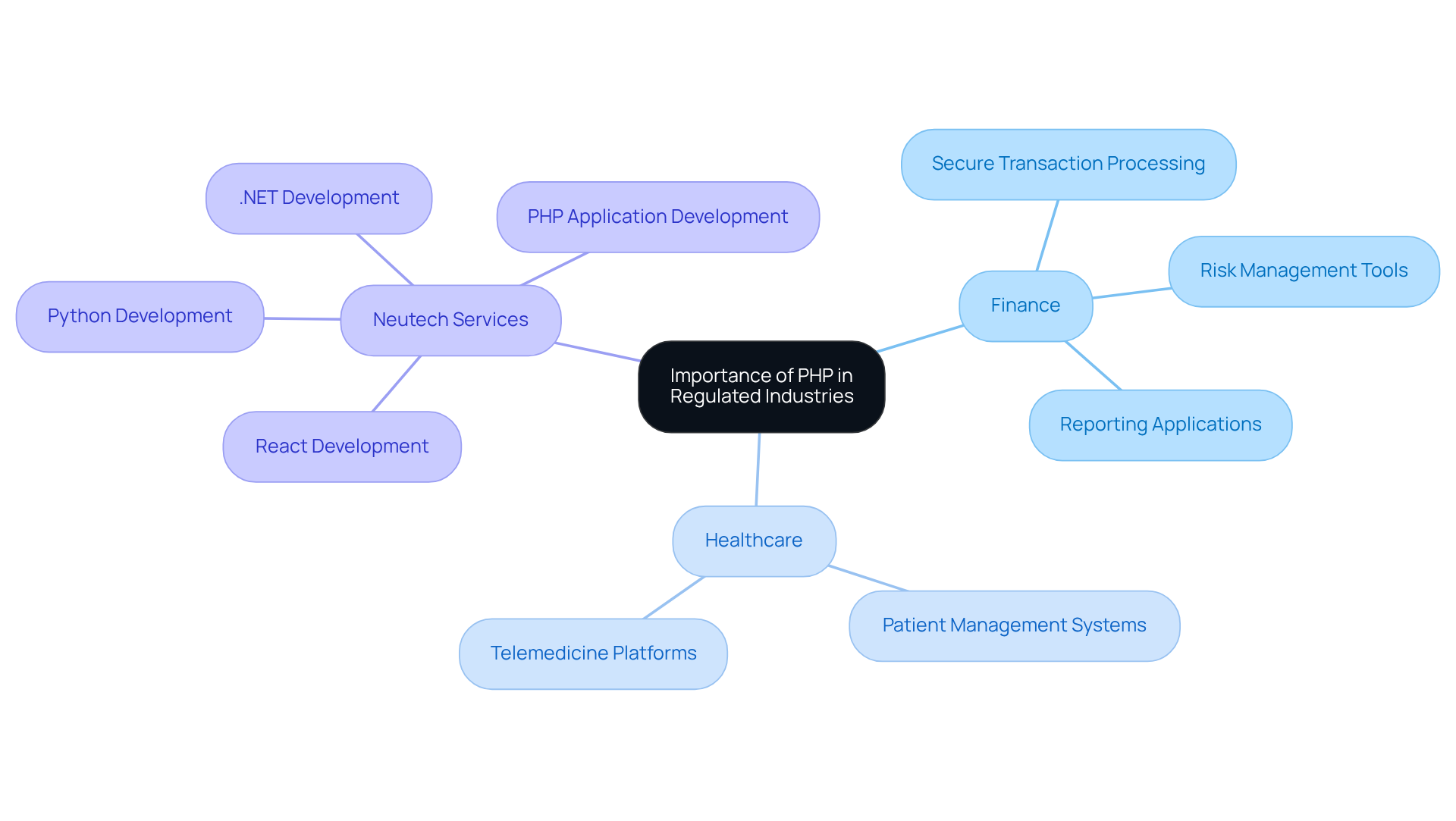
Implement Best Practices for Performance and Compliance
To ensure optimal performance of PHP programs while adhering to regulations, developers must adopt a range of best practices. Selecting the right framework is crucial; frameworks like Laravel and Symfony offer built-in features that enhance security and facilitate development.
Additionally, implementing caching strategies can significantly boost system performance by alleviating server load and reducing response times. Tools such as Redis or Memcached are instrumental in achieving this.
Moreover, conducting regular security audits is essential for identifying vulnerabilities and ensuring compliance.
Lastly, keeping libraries and frameworks up to date is vital for safeguarding against security threats and compliance issues. By adhering to these practices, developers can create robust software that meets the stringent standards required in regulated industries.
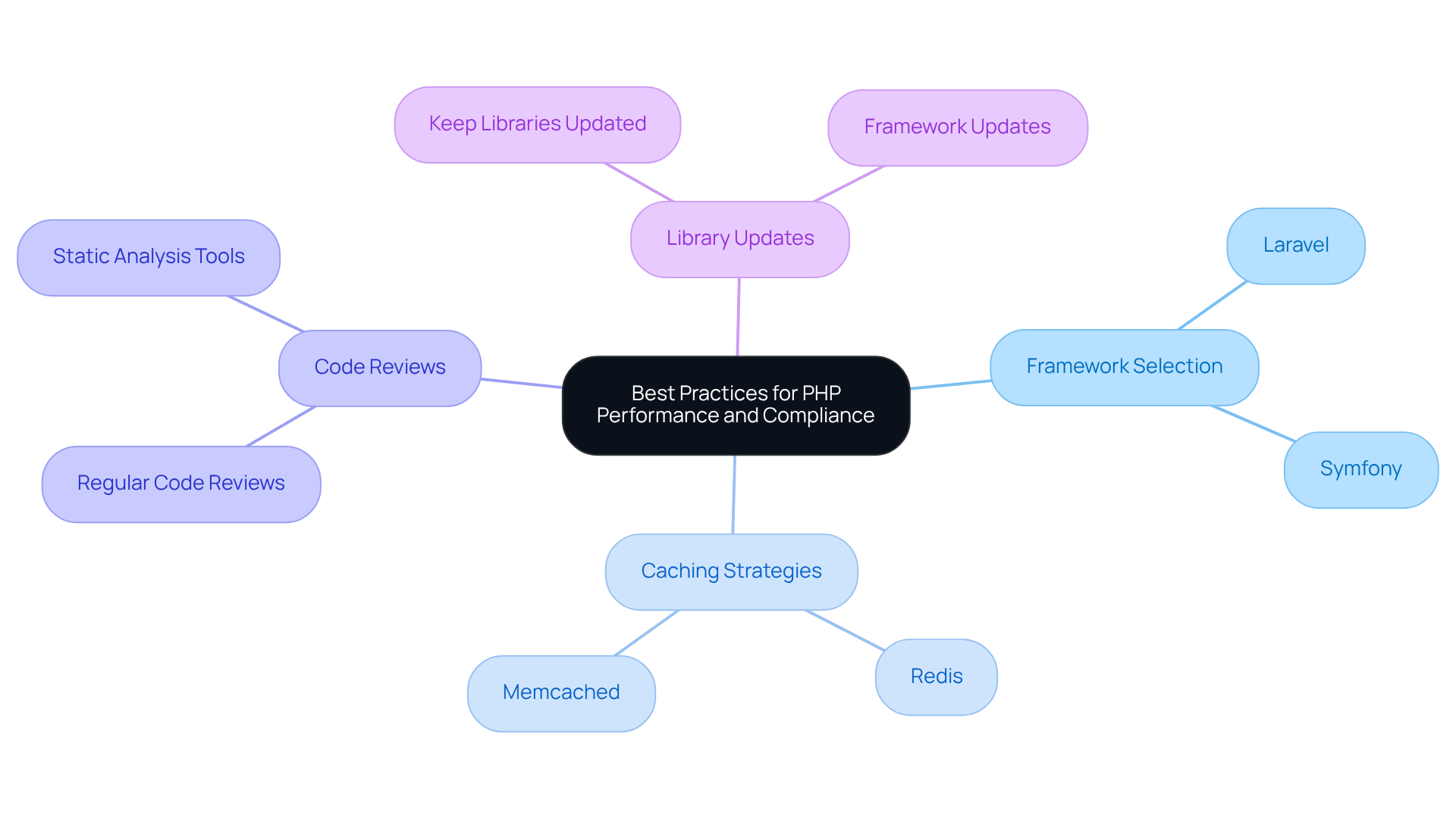
Integrate PHP Solutions with Existing Systems for Seamless Operations
Integrating PHP software with existing systems is essential for maintaining and ensuring operational efficiency. Developers should start by evaluating the current architecture to pinpoint key integration points. Utilizing APIs is a common strategy; PHP’s capability in data exchange enables effective communication between diverse systems.
For instance, many organizations implement middleware, allowing legacy systems to interact seamlessly with modern applications without requiring extensive modifications. Furthermore, establishing robust error handling and logging mechanisms is critical, as these tools assist in monitoring and promptly addressing any issues that may arise.
By prioritizing integration, organizations can optimize their workflows while maximizing the value of their new solutions. This strategy not only streamlines operations but also supports the scalability and adaptability necessary in regulated industries.
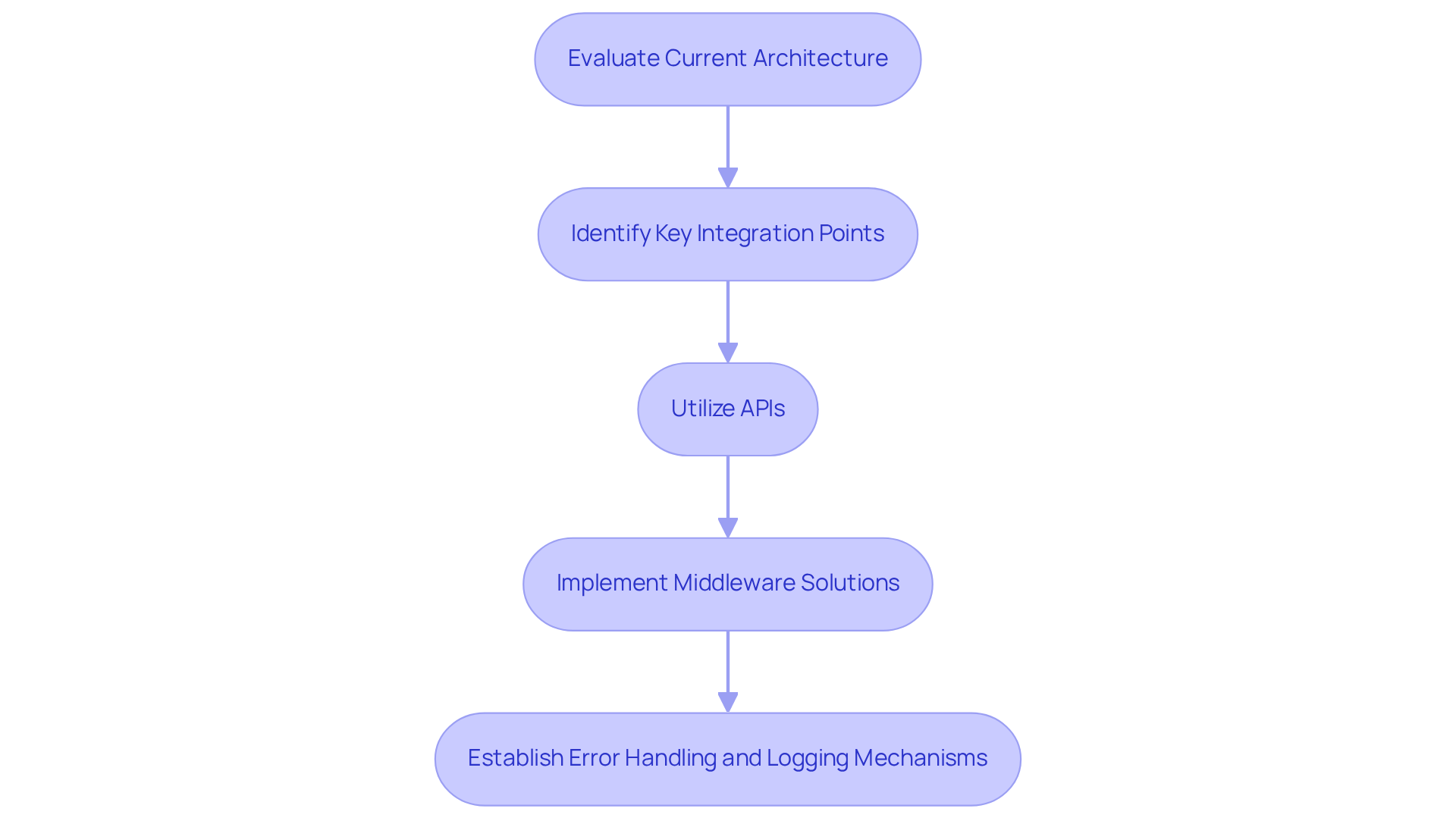
Ensure Continuous Management and Support for PHP Applications
To ensure optimal performance and adherence to regulations, entities must adopt a proactive strategy for management and support. Regular updates to the software and its associated libraries are crucial for mitigating risks. Outdated applications can expose systems to known exploits, making a critical business decision. Notably, 35.68% of PHP teams are still using PHP 7.4, underscoring the competitive advantage of staying current with technologies. Establishing a robust monitoring system to track software performance and user activity enables organizations to identify potential issues before they escalate, thereby enhancing overall reliability.
Regular audits are essential for evaluating compliance with standards, ensuring that submissions align with industry requirements. As Bruce Schneier aptly stated, “Security is a process, not a product,” highlighting the necessity for ongoing vigilance. Moreover, adopting a DevOps approach fosters collaboration between development and operations teams, facilitating quicker updates and more efficient issue resolution. This integrated methodology not only streamlines the update process but also strengthens the overall security posture of applications. By prioritizing continuous management and regular updates through best practices, organizations can uphold the integrity and compliance of their PHP applications over time, while avoiding common pitfalls such as neglecting security checks and patches.
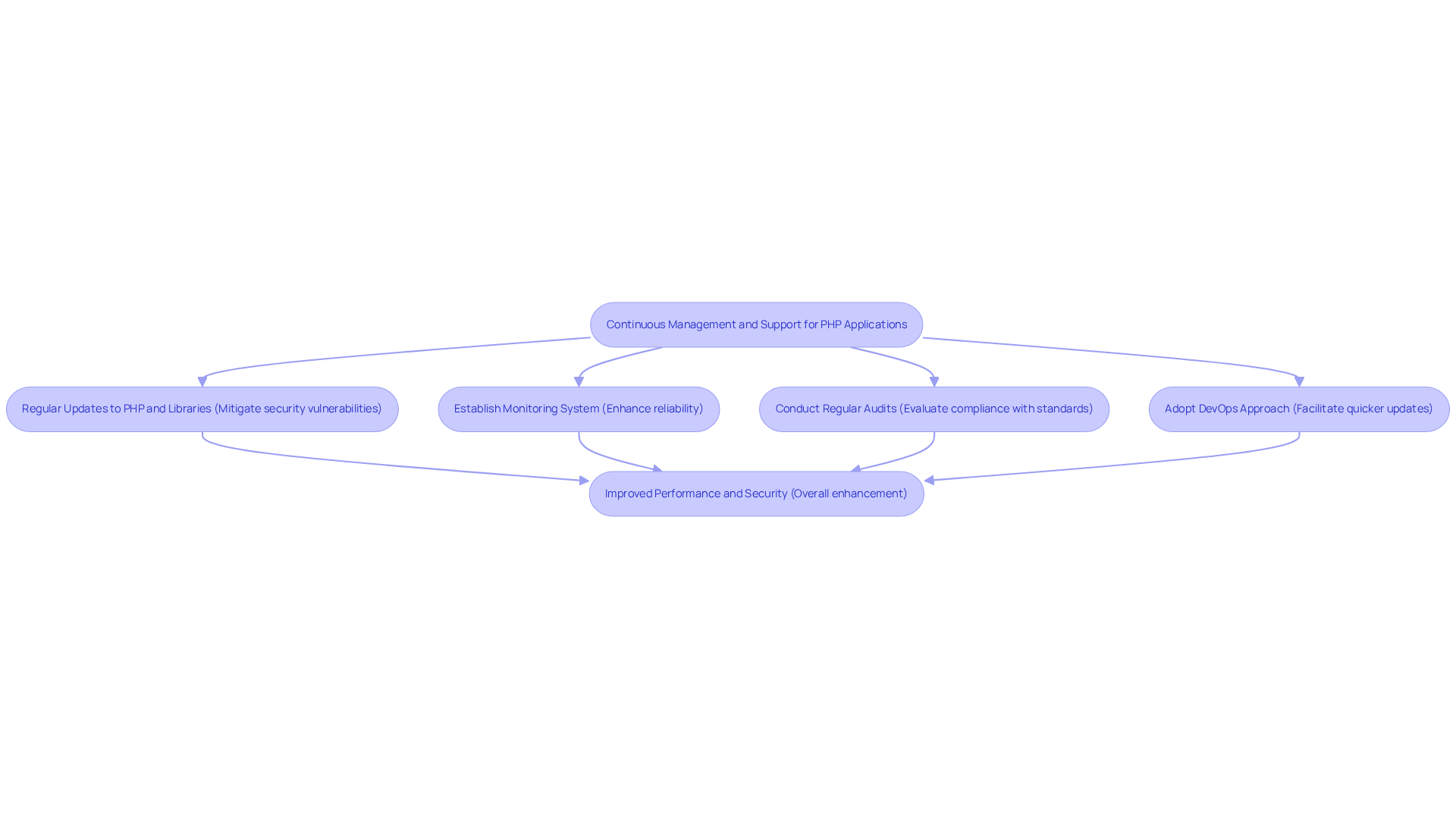
Conclusion
PHP is a crucial technology in regulated industries, particularly in finance and healthcare, where its data processing and security capabilities are essential. By utilizing PHP application development services, organizations can achieve compliance with stringent regulations such as GDPR, HIPAA, and PCI DSS, thereby protecting sensitive information while improving operational efficiency.
The importance of adopting best practices in PHP development has been highlighted throughout this article. Selecting appropriate frameworks, implementing effective caching strategies, and ensuring seamless integration with existing systems are all vital approaches that contribute to maintaining performance and compliance. Furthermore, the need for continuous management and timely updates is critical, as these measures are necessary to safeguard against vulnerabilities and ensure adherence to industry standards.
In conclusion, the message is unequivocal: investing in PHP application development services designed for regulated industries is not merely a technical decision but a strategic necessity. Organizations should prioritize the integration of PHP into their systems, embrace best practices for performance and compliance, and commit to ongoing management and support. This proactive strategy not only enhances operational capabilities but also strengthens the security and integrity of applications within an ever-evolving regulatory landscape.
Frequently Asked Questions
What is PHP and why is it important in regulated industries?
PHP is a versatile scripting language that is essential for creating solutions in regulated industries such as finance and healthcare due to its capability for complex data processing and robust security features.
How does PHP support compliance with regulations?
PHP helps organizations comply with regulations like GDPR, HIPAA, and PCI DSS by facilitating the development of secure applications that ensure data protection and regulatory adherence.
In what ways is PHP utilized in the financial sector?
In the financial sector, PHP is used to develop secure transaction processing systems, risk management tools, and reporting applications, which help organizations navigate regulatory landscapes effectively.
What applications does PHP support in the healthcare industry?
PHP powers secure patient management systems and telemedicine platforms in healthcare, ensuring the protection of sensitive patient information while meeting industry standards.
What advantages does PHP offer in regulated industries?
PHP’s extensive adoption, strong community support, and robust security features make it a reliable choice for applications in regulated industries, enhancing compliance and security.
What software development services does Neutech provide?
Neutech offers various software development services, including React development, Python development, .NET development, and PHP application development services.
List of Sources
- Understand the Importance of PHP in Regulated Industries
- Healthcare Compliance News Archives (https://hfma.org/topic/legal-and-regulatory-compliance/compliance)
- PHP Market Share (https://kinsta.com/php-market-share)
- Healthcare Compliance News (https://hipaajournal.com/category/healthcare-compliance)
- Implement Best Practices for Performance and Compliance
- From Global Threats to Security-First Backend: The Growing Demand of PHP Developers is Strengthening Startups’ Architectures | OCNJ Daily (https://ocnjdaily.com/news/2026/feb/10/from-global-threats-to-security-first-backend-the-growing-demand-of-php-developers-is-strengthening-startups-architectures)
- Laravel vs. Symfony: Which PHP Framework to Choose? (https://cloudpanel.io/blog/laravel-vs-symfony)
- duplextech.com (https://duplextech.com/blogs/case-studies-for-successful-php-project.html)
- Symfony vs Laravel: Battle of the PHP Frameworks (https://kinsta.com/blog/symfony-vs-laravel)
- Laravel Security Advisory: phpunit/phpunit, psy/psysh, symfony/process Vulnerabilities | Ali Babaeian posted on the topic | LinkedIn (https://linkedin.com/posts/ibabae_laravel-php-devsecops-activity-7432345375853686784-nZb8)
- Integrate PHP Solutions with Existing Systems for Seamless Operations
- PHP API Integration Solutions | Connect Systems Seamlessly (https://yugasa.com/blog/php-api-integration)
- PHP Market Share (https://kinsta.com/php-market-share)
- Simple Case Study : PHP Data base + API connection usage (https://medium.com/@leoFacci/simple-case-study-php-data-base-api-connection-usage-f393924c25bf)
- duplextech.com (https://duplextech.com/blogs/case-studies-for-successful-php-project.html)
- PHP Web Development in 2026: Trends, Tools, and Best Practices (https://websolutionsllc.co/blog/php-web-development-trends)
- Ensure Continuous Management and Support for PHP Applications
- duplextech.com (https://duplextech.com/blogs/case-studies-for-successful-php-project.html)
- Software Engineering Great Quotes (https://dev.to/mcsee/software-engineering-great-quotes-26ci)
- PHP Version Updates: Critical Security Guide for Websites (https://inmotionhosting.com/support/security/why-keep-php-version-updated)
Introduction
In the high-stakes arena of finance, where regulations evolve as rapidly as technology, the development of web applications presents both challenges and opportunities. Compliance with regulatory requirements is not merely a legal obligation; it is a vital component that can enhance user trust and protect sensitive data. As financial institutions navigate the complexities of regulatory frameworks and security threats, developers face the critical task of ensuring their applications not only meet compliance standards but also excel in functionality and security. This article explores four best practices that will guide developers in effectively navigating the intricate landscape of financial web application development, ensuring both compliance and robust performance.
Understand Compliance Requirements for Regulated Industries
In the finance sector, compliance transcends being a mere legal checkbox; it stands as a fundamental aspect of business operations. Financial applications must adhere to various regulations, including GDPR, PCI DSS, and AML, which are vital for safeguarding consumer data and ensuring privacy. As policy changes continue to reshape the landscape, developers must remain vigilant. The Financial Conduct Authority emphasizes that guidelines are crucial for detecting and ensuring accurate disclosures.
To navigate these requirements effectively, developers should adopt several best practices:
- Stay Informed: Regularly review updates from regulatory bodies to ensure that your application meets current standards. This includes monitoring changes in legislation, which are becoming increasingly stringent.
- Conduct Risk Assessments: Identify potential vulnerabilities. Implementing proactive strategies to mitigate these risks can prevent costly fines and operational disruptions.
- Engage Regulatory Experts: Collaborate with legal and regulatory professionals throughout the development process. Their expertise is invaluable in ensuring that your application adheres to all necessary regulations, especially as new governance frameworks emerge.
- Document Everything: Maintain thorough documentation of regulatory processes and decisions. This practice not only facilitates audits and inspections but also demonstrates a commitment to compliance.
Moreover, statistics indicate that 77% of companies believe regulatory complexity adversely affects their operations, highlighting the challenges faced in maintaining compliance with evolving regulations. By prioritizing adherence from the outset, developers can enhance user confidence in their software while avoiding significant financial repercussions associated with non-compliance. As the landscape of financial regulations continues to evolve, staying ahead of compliance requirements will be essential for success.
Choose an Appropriate Technology Stack for Development
Selecting the appropriate technology stack is essential for the success of web applications. The following key considerations should guide this decision:
- Scalability: It is crucial to choose technologies that can scale in accordance with your business needs. For example, leveraging cloud services such as AWS offers the flexibility necessary to accommodate fluctuating workloads.
- Protection Features: Opt for frameworks that incorporate integrated protection features, including encryption and secure authentication methods. Technologies like .NET and Java are recognized for their robust security features.
- Community Support: A strong developer community can provide invaluable resources and support. Popular stacks, such as MERN (MongoDB, Express.js, React, Node.js), boast extensive documentation and community engagement.
- Compliance Readiness: It is imperative to ensure that the selected stack supports regulatory compliance. For instance, utilizing frameworks that facilitate data protection can assist in meeting GDPR requirements.
By carefully selecting a technology stack, developers can create solutions that are not only functional but also secure and compliant.
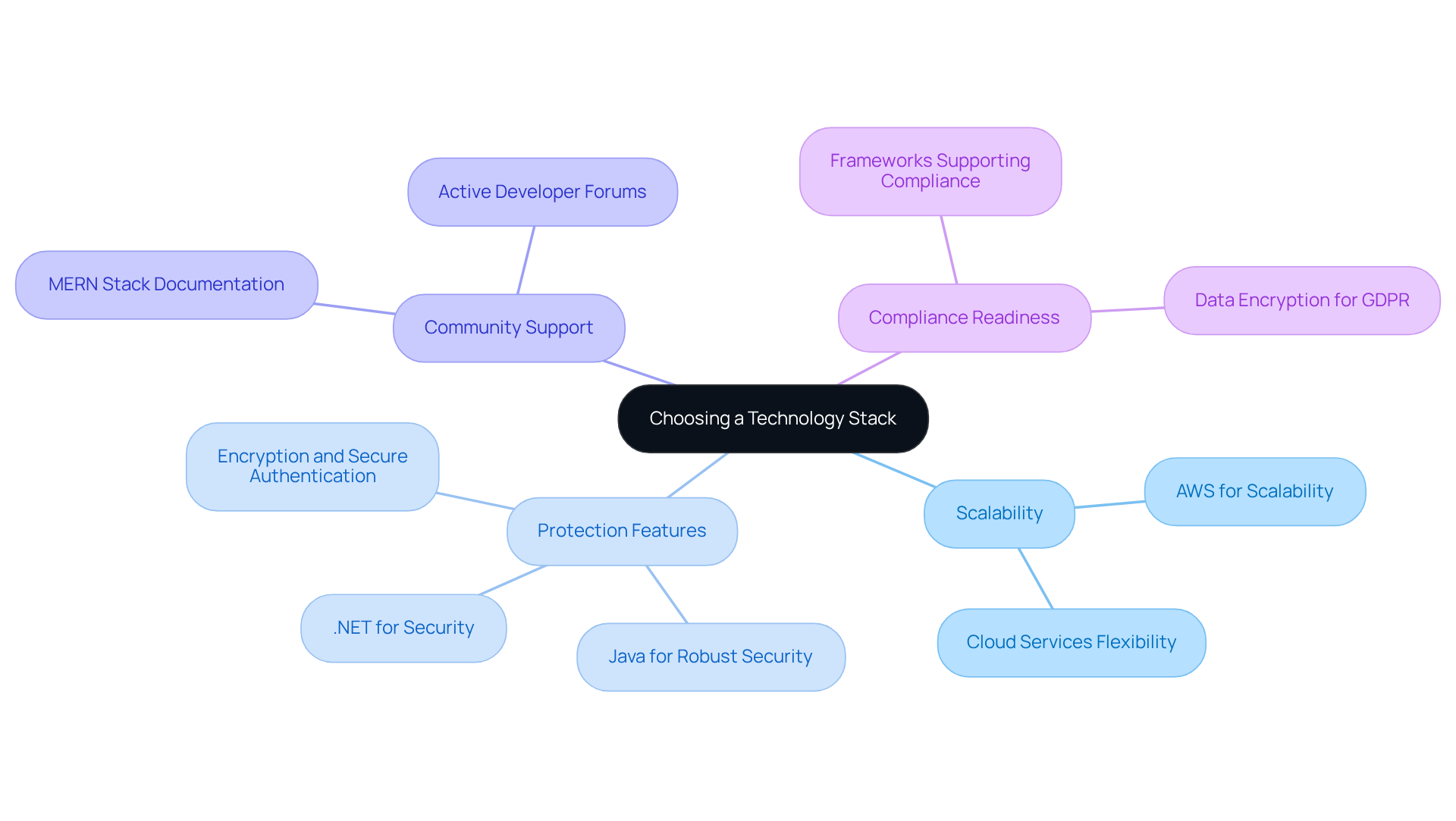
Implement Robust Security Measures in Development
Security is paramount in business web application development. To ensure robust protection, organizations should implement the following measures:
- Employ robust encryption standards, such as AES-256, for both data at rest and in transit. This is crucial for safeguarding sensitive information against unauthorized access and breaches. Notably, involving cloud resources have increased by 25% year-over-year. Furthermore, third-party involvement in breaches has doubled to 30% year-over-year, underscoring the growing risk associated with external vendors.
- Implement MFA to provide an additional layer of protection for user accounts. This significantly reduces the risk of unauthorized access. MFA is now required for all individuals accessing any information system, not just for remote access or privileged accounts, as emphasized by cybersecurity expert Michael Soohoo.
- Conduct periodic assessments and penetration testing to identify and rectify vulnerabilities. Continuous monitoring and threat intelligence are vital for the early detection of potential threats, enabling faster containment and minimizing operational costs.
- Train developers in secure coding techniques to prevent common vulnerabilities such as SQL injection and cross-site scripting (XSS). Incorporating protection into the software development lifecycle is essential for reducing risks and enhancing the overall safety stance of applications.
By integrating these practices throughout the development process, organizations can significantly decrease the likelihood of breaches and strengthen their defenses against evolving cyber threats.
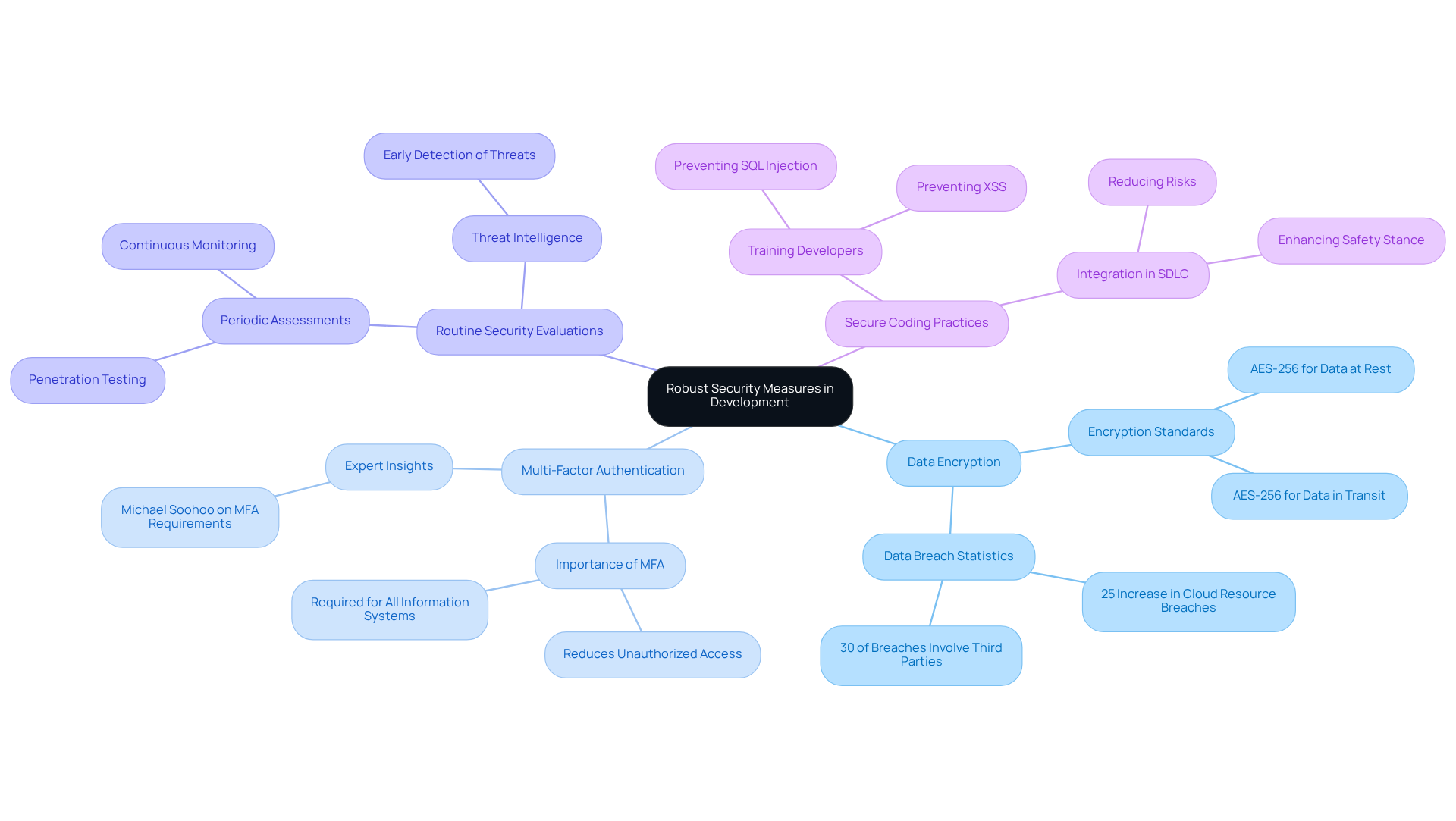
Conduct Continuous Testing and Monitoring for Compliance
To ensure compliance, applications must undergo testing and monitoring. Here are key strategies:
- Automated Testing: Implement automated processes to regularly verify compliance with industry and security standards. Industry reports indicate that organizations employing automated testing experience a 30% reduction in regulatory-related errors, significantly enhancing efficiency and minimizing the risk of human error in compliance checks.
- Monitoring Tools: Utilize monitoring tools, such as Splunk and New Relic, to track program performance and security in real-time. This capability allows for immediate responses to potential issues, greatly reducing risks associated with operational disruptions. For example, a leading fintech company reported a 40% decrease in downtime following the implementation of solutions.
- Feedback Loops: Establish robust feedback loops. This iterative process fosters continuous improvement in application security and compliance measures, ensuring that systems evolve alongside regulatory changes. A recent study found that organizations with effective feedback loops improved their compliance scores by 25% over the course of a year.
- Adherence Dashboards: Develop comprehensive dashboards that provide visibility into compliance metrics. These dashboards facilitate the identification of areas needing attention, enabling proactive management of regulatory obligations. Organizations utilizing monitoring dashboards report a 50% faster response time to compliance issues.
By integrating ongoing testing and monitoring into the development process, organizations can maintain the integrity of their applications over time, positioning themselves favorably in a rapidly evolving regulatory landscape. However, it is essential to avoid common pitfalls, such as neglecting to update testing frameworks in accordance with regulatory changes or failing to train staff on new monitoring tools. A case study from a prominent hedge fund demonstrates that firms addressing these challenges proactively can enhance their operational resilience and sustain investor trust.
Conclusion
In the realm of business web application development within the finance sector, the significance of compliance, security, and technology selection is paramount. Financial applications must not only adhere to stringent regulatory requirements but also be built on a robust technological foundation that guarantees scalability and security. By prioritizing these elements, developers can create applications that instill trust and reliability among users.
Key practices include:
- A thorough understanding of compliance requirements
- Careful selection of an appropriate technology stack
- Implementation of robust security measures
- Ongoing testing and monitoring
These strategies collectively contribute to a secure and compliant application environment, ultimately safeguarding sensitive financial data and enhancing operational integrity. Engaging regulatory experts, utilizing secure frameworks, and maintaining rigorous testing protocols are essential steps in navigating the complex landscape of financial regulations.
The evolving nature of compliance and security in financial web applications necessitates a proactive approach. As regulations shift and cyber threats grow more sophisticated, organizations must remain vigilant and adaptable. Embracing these best practices not only mitigates risks but also positions businesses to thrive in a competitive market, reinforcing the critical role of compliance and security in the development of financial technology solutions.
Frequently Asked Questions
Why is compliance important in the financial services sector?
Compliance is fundamental in the financial services sector as it ensures that software applications adhere to regulations like GDPR, PCI DSS, and AML, which are vital for safeguarding consumer data and maintaining operational integrity.
What are some key regulations financial applications must comply with?
Financial applications must comply with various regulations, including GDPR (General Data Protection Regulation), PCI DSS (Payment Card Industry Data Security Standard), and AML (Anti-Money Laundering).
What best practices should developers follow to navigate compliance requirements?
Developers should follow best practices such as staying informed about regulatory updates, conducting risk assessments, engaging regulatory experts, and maintaining thorough documentation of regulatory processes and decisions.
How can developers stay informed about compliance updates?
Developers can stay informed by regularly reviewing updates from regulatory bodies to ensure their applications meet current standards, particularly monitoring changes in GDPR and PCI DSS regulations.
Why are risk assessments important during the development phase?
Conducting risk assessments during the development phase helps identify potential regulatory risks and allows developers to implement proactive strategies to mitigate these risks, preventing costly fines and operational disruptions.
What role do regulatory experts play in the development process?
Regulatory experts provide invaluable guidance to ensure that applications adhere to necessary regulations, especially as new governance frameworks emerge, thus enhancing compliance efforts.
Why is documentation important for compliance?
Maintaining thorough documentation of regulatory processes and decisions facilitates audits and inspections and demonstrates a commitment to regulatory adherence.
What challenges do companies face regarding regulatory compliance?
Statistics indicate that 77% of companies believe regulatory complexity adversely affects their operations, highlighting the challenges of maintaining compliance with evolving regulations.
How can prioritizing compliance benefit developers?
By prioritizing compliance from the outset, developers can enhance user confidence in their software and avoid significant financial repercussions associated with non-compliance.
List of Sources
- Understand Compliance Requirements for Regulated Industries
- Key 2025-2026 Regulatory Compliance and Lending Law Changes: Data Privacy, AI, and Consumer Protection — Winnow (https://winnow.law/news/key-2025-2026-regulatory-compliance-and-lending-law-changes)
- Fintech Security: Protecting Digital Finance in 2026 – The Codest (https://thecodest.co/en/blog/fintech-security-protecting-digital-finance-in-2026)
- Financial Services Compliance: Complete 2026 Guide | Xantrion (https://xantrion.com/article/financial-services-regulatory-compliance)
- Compliance Horizon 2026: When Regulatory Change Moves Faster Than Your Disclosure Process (https://insightsoftware.com/blog/compliance-horizon-2026-when-regulatory-change-moves-faster-than-your-disclosure-process)
- Regulatory Changes Affecting Financial Services in 2026 – Read More (https://citrincooperman.com/In-Focus-Resource-Center/Regulatory-Changes-Affecting-Financial-Services-in-2026)
- Choose an Appropriate Technology Stack for Development
- The Best Fintech Tech Stack in 2026 | ServerMania (https://blog.servermania.com/fintech-tech-stack)
- Five technology trends redefining financial services (https://fintechfutures.com/bankingtech/five-technology-trends-redefining-financial-services)
- Fintech Stacks: Tools Fintech Teams Use to Build Scalable Financial Apps in 2026 (https://index.dev/blog/fintech-tech-stack-tools-remote-teams)
- Building a FinTech App in 2026: Best Tech Stacks and Architecture Choices (https://medium.com/meetcyber/building-a-fintech-app-in-2026-best-tech-stacks-and-architecture-choices-f3dc7cecb350)
- The 3 Ways Fintechs Are Making AI Work in Financial Services (https://forbes.com/sites/davidparker/2026/03/04/how-fintechs-are-helping-banks-scale-ai-faster)
- Implement Robust Security Measures in Development
- Most Common Cybersecurity Threats for FinTech Companies in 2026 (https://quixxi.com/most-common-cybersecurity-threats-for-fintech-companies-in-2026)
- Cybersecurity Regulations for Financial Services for 2026 and Beyond (https://hypr.com/blog/top-financial-services-cybersecurity-regulations)
- Top Cybersecurity Trends for 2026 Every Financial Leader Must Know (https://jackhenry.com/fintalk/top-cybersecurity-trends-for-2026-every-financial-leader-must-know)
- Fintech Security: Protecting Digital Finance in 2026 – The Codest (https://thecodest.co/en/blog/fintech-security-protecting-digital-finance-in-2026)
- Conduct Continuous Testing and Monitoring for Compliance
- Proof, Not Promises — Will Fintechs Survive the 2026 Compliance Test? (https://corporatecomplianceinsights.com/proof-not-promises-will-fintechs-survive-2026-compliance-test)
- Best AML monitoring solutions leading compliance in 2026 (https://fintech.global/2025/12/08/best-aml-monitoring-solutions-leading-compliance-in-2026)
- 4 US regulatory trends for 2026: A guide for compliance leaders (https://complyadvantage.com/insights/four-us-regulatory-trends-for-2026-for-compliance-leaders)
- Continuous Compliance in 2026: A Strategic Playbook for Regional Banks (https://bank-vantage.com/2025/08/03/continuous-compliance-in-2026-a-strategic-playbook-for-regional-banks)
- Financial Organizations Navigate Heightened Regulatory Security Requirements (https://biztechmagazine.com/article/2026/02/financial-organizations-navigate-heightened-regulatory-security-requirements)
Introduction
Mastering Angular application development transcends mere coding; it involves grasping a sophisticated architecture that enables developers to create scalable and maintainable software. Understanding the core principles of Angular – its components, modules, and services – equips programmers to deliver high-quality applications that satisfy the demands of modern users. As the web development landscape evolves rapidly, developers must not only keep pace but also set standards for excellence. This article examines:
- Best practices
- Testing strategies
- CI/CD methodologies
that are crucial for achieving outstanding results in Angular development.
Understand Angular Architecture and Core Principles
Mastering framework development requires a deep understanding of its architecture, which is fundamentally organized around components, modules, and services. Components serve as the essential building blocks of framework-based projects, encapsulating both the user interface and its associated behavior. Modules are critical for organizing these components into cohesive units of functionality, which facilitates better management and scalability. In contrast, services provide reusable business logic and functionality, enhancing the overall efficiency of the system.
A key aspect of this architecture is the component-based structure, which fosters modularity and testability. Recent surveys indicate that approximately 75% of programmers are familiar with the framework’s core principles, underscoring its importance in modern application development. This system enables developers to easily manage dependencies, simplifying the process of swapping out implementations for testing or scaling purposes. Additionally, understanding the change detection mechanism of this framework is crucial, as it optimizes performance by efficiently updating the UI in response to data changes.
Recent updates to the framework have introduced enhancements that streamline the development process, including improved tooling and the integration of Signals for state management. These advancements not only facilitate the learning process for new programmers but also promote best practices in creating scalable applications. As industry leader Syed Khizaruddin noted, ‘Quality is no longer optional but a necessity for forward-thinking professionals.’ By grasping these fundamental principles, programmers can develop robust software that meets industry standards and effectively addresses user needs.
However, programmers must remain vigilant about common pitfalls, such as mismanaging state or failing to implement proper typing in TypeScript, which can lead to bugs and maintenance challenges. Case studies, such as the successful application of a framework in healthcare software, demonstrate how these principles can enhance patient care and data management. By understanding and applying these foundational principles, programmers can navigate the complexities of this framework and deliver high-quality software.
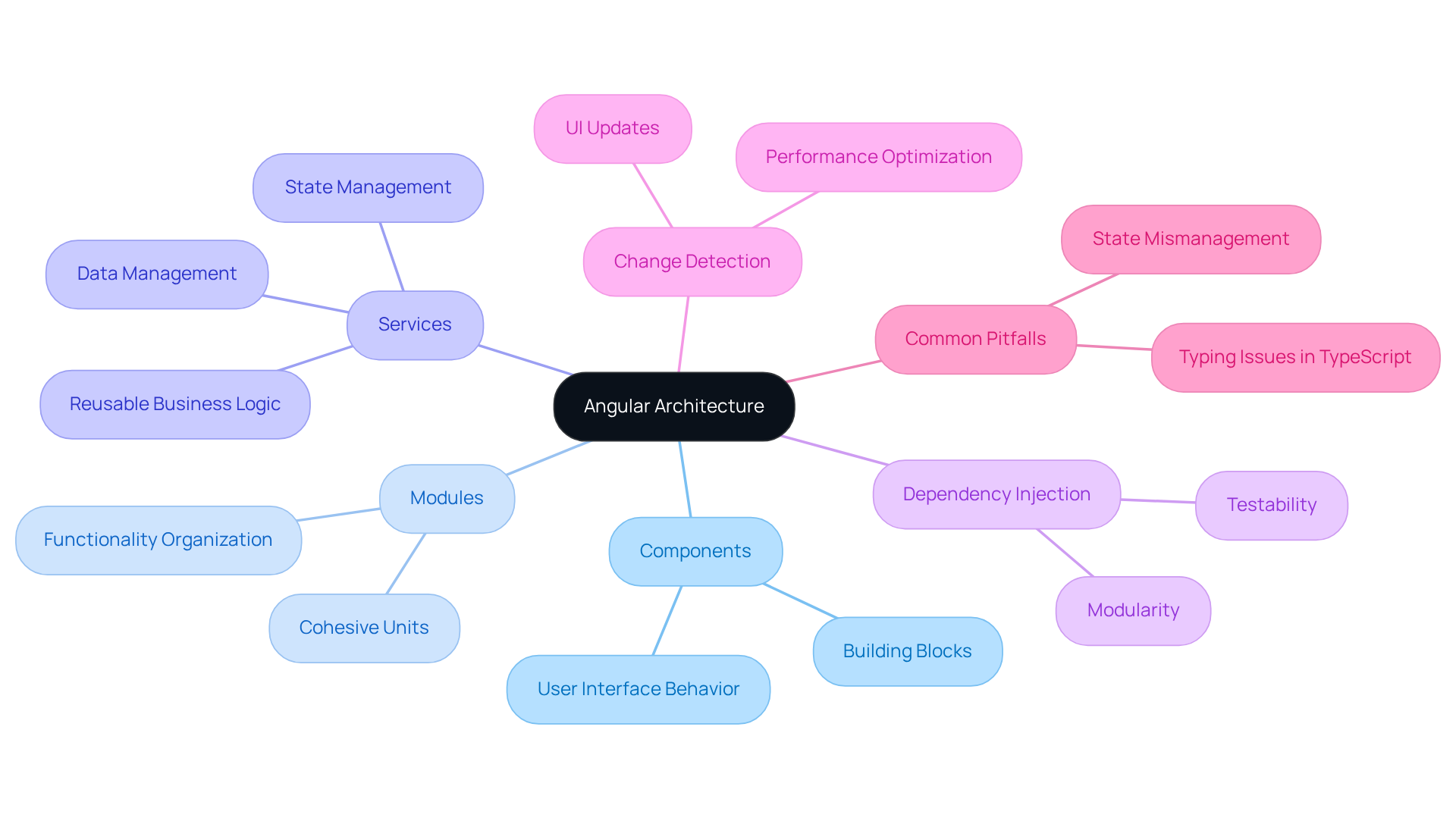
Implement Best Practices for Code Quality and Project Management
To ensure success in web projects, developers must adopt several best practices. First and foremost, code quality is essential. This tool enforces a consistent structure and coding standards across projects, which not only streamlines development but also enhances collaboration among team members.
Implementing a modular architecture is another critical practice. By breaking applications into smaller, reusable components, developers significantly improve maintainability and scalability. Adhering to the Single Responsibility Principle (SRP) is vital, as it ensures that each component or service has a distinct purpose. This approach reduces complexity and enhances clarity within the codebase.
Furthermore, code reviews enhance readability. Such practices make it simpler for developers to navigate and comprehend the codebase effectively. Frequent reviews of programming and engaging in pair programming sessions encourage collaboration and knowledge sharing, ultimately resulting in improved quality and a more unified development process.
Optimizing change detection and component architecture is crucial for performance, as it can significantly enhance application responsiveness. Additionally, including automated testing is essential for verifying functionality and preserving quality. Refactoring is another best practice that helps prevent complex and hard-to-manage code.
By incorporating these methods, teams can efficiently oversee their projects and deliver high-quality applications.
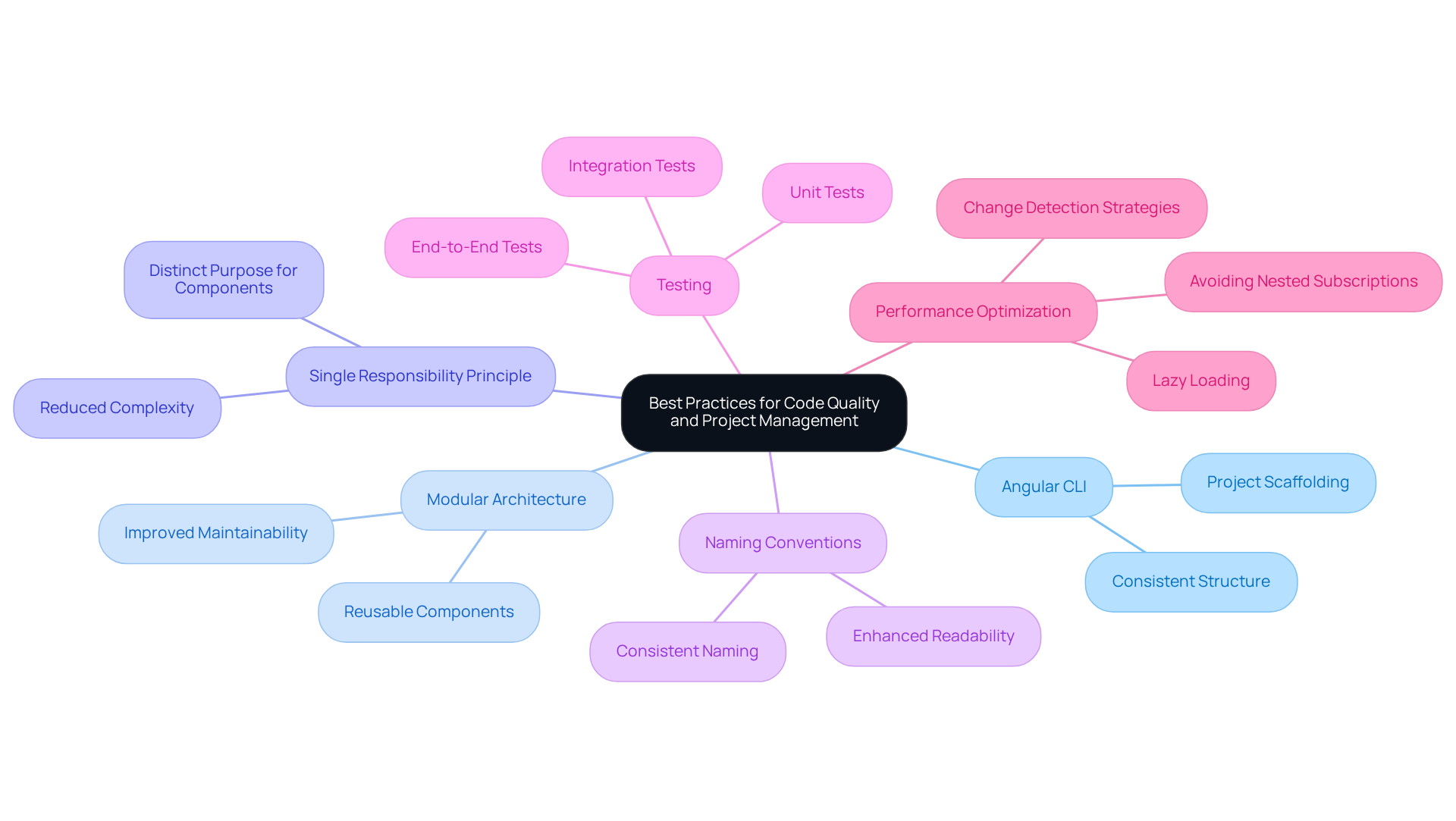
Prioritize Testing and Validation for Reliable Applications
To ensure the reliability of frameworks, developers must adopt a comprehensive testing strategy. Start with utilizing frameworks such as Vitest. Vitest offers advantages compared to its predecessor, Karma, enabling effective testing of individual components and services in isolation to confirm that each unit operates correctly.
Following this, integrate integration tests to validate that different components of the system interact smoothly. This step is vital for uncovering issues that may occur when components collaborate. Testing frameworks can simulate user interactions, thereby validating the application’s overall functionality and user experience.
Incorporating test-driven development into the workflow can significantly elevate code quality. By writing tests prior to implementing features, developers can construct better-organized programs that fulfill requirements from the outset. Data suggests that teams employing TDD in projects utilizing Angular achieve higher code quality and experience fewer defects.
Regularly executing tests as part of a continuous integration process is crucial for identifying regressions early, thus preserving the system’s integrity. This proactive testing strategy not only enhances reliability but also fosters a culture of quality within development teams, ultimately leading to more successful applications.
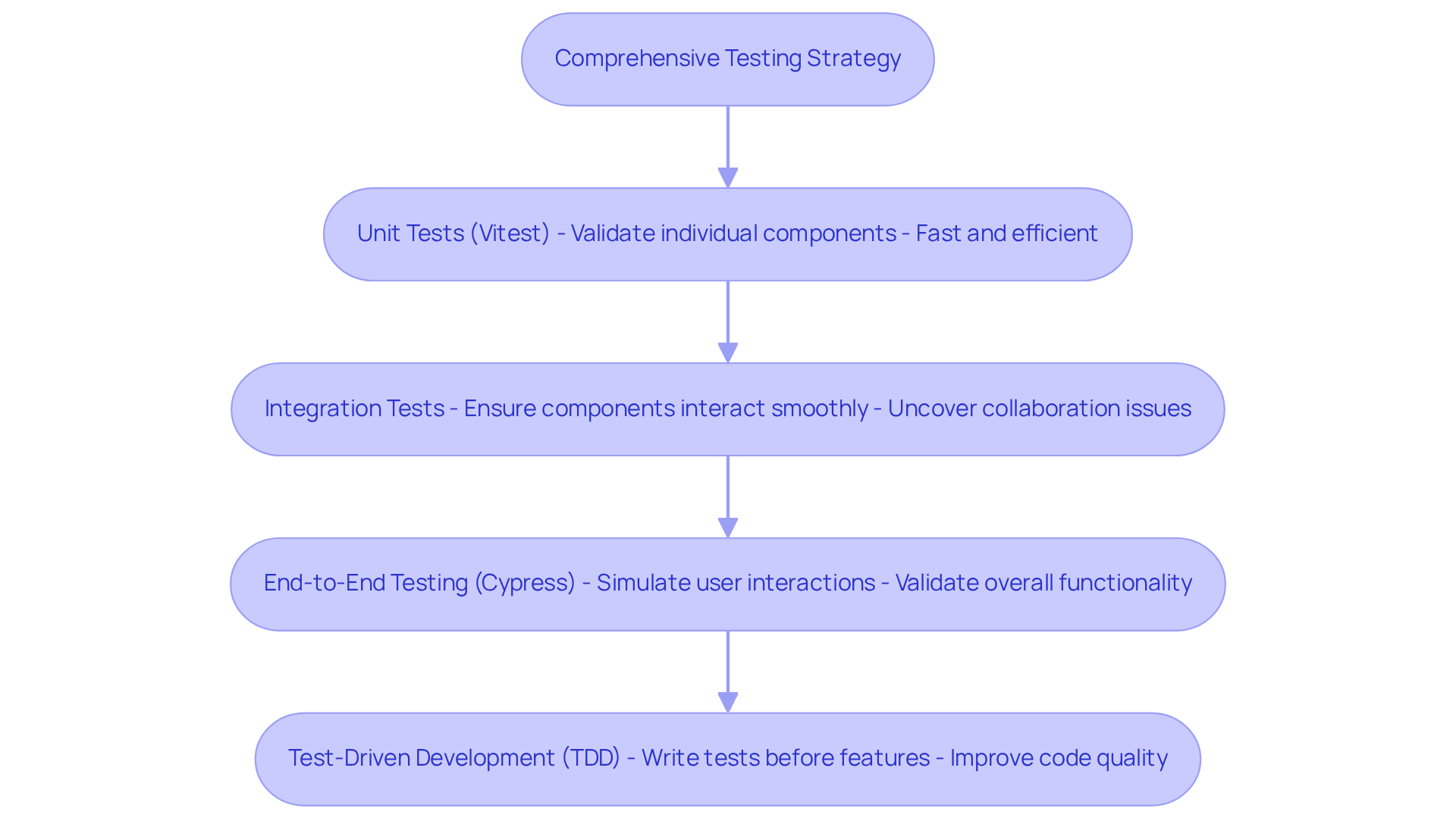
Adopt Continuous Integration and Deployment Practices
To implement effective continuous integration and deployment, it is essential to establish a version control system, such as Git, for managing changes. This foundational step allows teams to track modifications systematically. Next, utilizing automation tools automates the build and testing procedures, ensuring that the software is validated with every commit. This automation not only streamlines the development process but also enhances reliability.
Furthermore, establishing a deployment strategy is crucial for consistency across various environments, including staging and production. Tools such as Docker facilitate containerization, while Kubernetes provides orchestration capabilities, ensuring that applications are deployed consistently and efficiently.
Additionally, integrating testing into the CI/CD pipeline is vital for identifying issues early and maintaining software quality. By adopting these practices, teams can significantly enhance collaboration, reduce deployment times, and improve overall software quality.
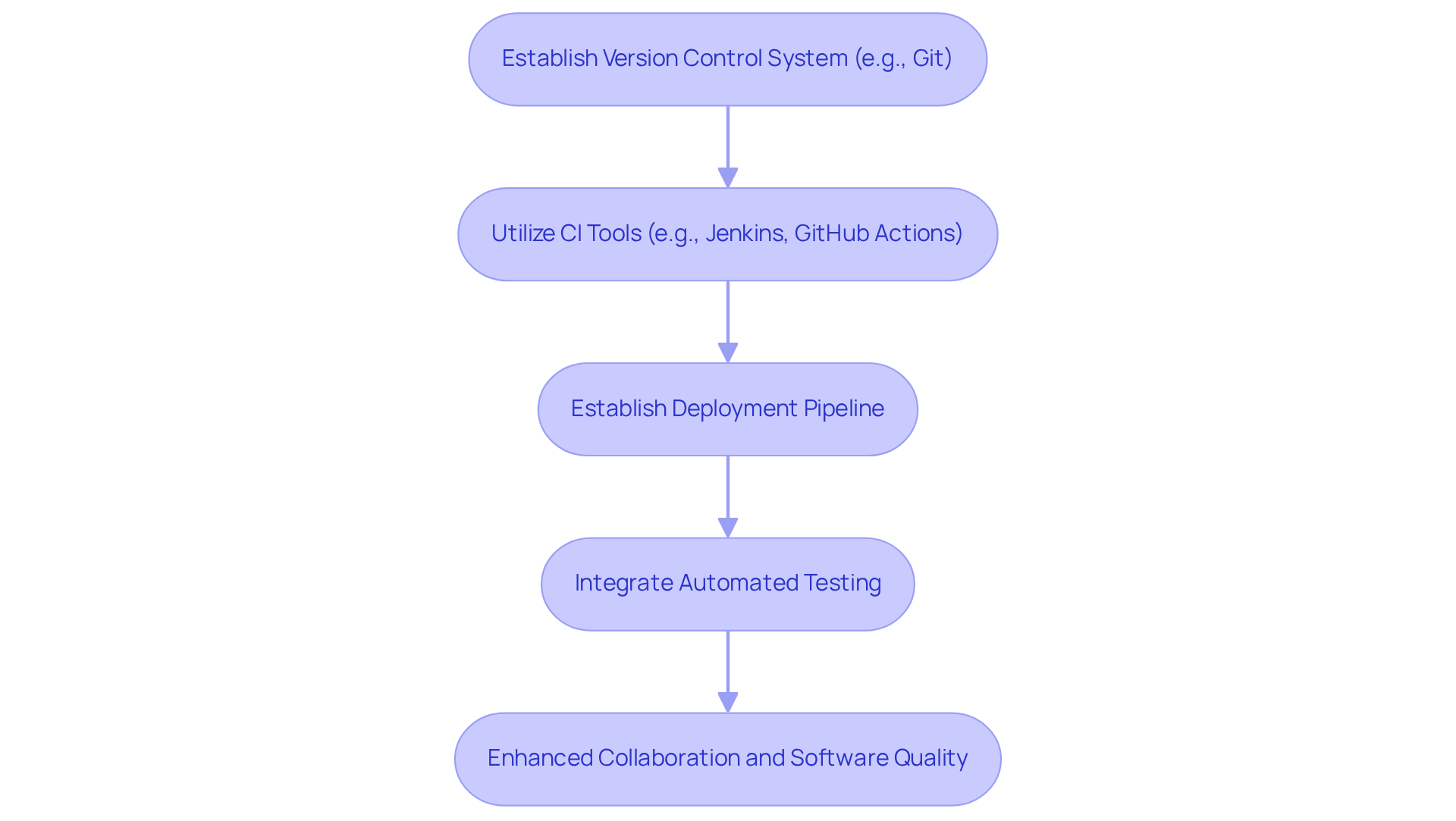
Conclusion
Mastering Angular application development is crucial for delivering high-quality software that aligns with contemporary standards. A deep understanding of the framework’s architecture – comprising components, modules, and services – enables developers to create efficient and scalable applications. Emphasizing best practices, such as leveraging Angular CLI, maintaining a modular architecture, and implementing robust testing strategies, ensures that projects remain manageable and maintainable.
Key insights from this discussion underscore the necessity of adopting a comprehensive approach to development. From grasping Angular’s core principles to implementing continuous integration and deployment practices, each aspect plays a vital role in the overall success of a project. By prioritizing code quality, establishing a consistent testing framework, and utilizing CI/CD tools, developers can enhance collaboration and streamline their workflows.
Ultimately, the importance of mastering Angular development cannot be overstated. As the software development landscape evolves, embracing these best practices will not only yield better project outcomes but also position developers as leaders in their field. The future of Angular application development is promising for those willing to invest in their skills and adopt these strategies, paving the way for innovative and reliable software solutions.
Frequently Asked Questions
What are the main components of Angular architecture?
Angular architecture is fundamentally organized around components, modules, and services. Components are the essential building blocks that encapsulate the user interface and its behavior, while modules organize these components into cohesive units of functionality. Services provide reusable business logic and data management capabilities.
How does dependency injection work in Angular?
The dependency injection system in Angular fosters modularity and testability by allowing developers to manage dependencies easily. This system simplifies the process of swapping out implementations for testing or scaling purposes, enhancing overall application efficiency.
Why is understanding change detection important in Angular?
Understanding the change detection mechanism in Angular is crucial because it optimizes performance by efficiently updating the user interface in response to data changes, ensuring that the application runs smoothly and responsively.
What recent updates have been made to Angular?
Recent updates to Angular have introduced enhancements that streamline the development process, including improved support for standalone components and the integration of Signals for state management, which facilitate learning and promote best practices for scalable and maintainable software.
What common pitfalls should programmers be aware of when using Angular?
Programmers should remain vigilant about common pitfalls such as mismanaging state or failing to implement proper typing in TypeScript, as these issues can lead to bugs and maintenance challenges.
How can Angular principles be applied in real-world scenarios?
Real-world examples, such as the application of Angular in healthcare software, demonstrate how understanding and applying its principles can enhance patient care and data management, showcasing the framework’s effectiveness in addressing user requirements.
Why is mastering Angular considered essential for professionals?
Mastering Angular is viewed as a necessity for forward-thinking professionals, as it enables them to develop robust software that meets industry standards and effectively addresses user needs.
List of Sources
- Understand Angular Architecture and Core Principles
- Modern Angular Enterprise Architecture (2026) (https://medium.com/front-end-weekly/modern-angular-enterprise-architecture-2026-beff3d0b928f)
- Technology: The Ultimate Guide to Angular in 2026 | Compl… | Manju Hiremath (https://manjuhiremath.in/blog/technology/angular)
- Angular 20 Is the Framework Update We’ve Been Waiting For (https://newmathdata.com/blog/angular-20-features-standalone-components-signals)
- Why Choose Angular for Web Development in 2026? – VT Netzwelt (https://vtnetzwelt.com/web-development/why-choose-angular-for-web-development-in-2026)
- Angular Best Practices 2026: Clean & Scalable Code (https://ideas2it.com/blogs/angular-development-best-practices)
- Implement Best Practices for Code Quality and Project Management
- Best Practices for Angular Websites in 2026 (https://onewebcare.com/blog/angular-website-best-practices)
- Angular Best Practices for Building Apps in 2026 (https://esparkinfo.com/software-development/technologies/angular/best-practices)
- Mastering Angular: Best Practices to Code Like a Pro in 2026 (https://javascript.plainenglish.io/mastering-angular-best-practices-to-code-like-a-pro-in-2026-16528c3a7a4e)
- Top 12 Angular Best Practices that you need to consider in 2026 (https://faun.dev/c/stories/alberthiltonn/top-12-angular-best-practices-that-you-need-to-consider-in-2026)
- Angular: 10 Best Practices Every Developer Can’t Ignore (https://bootstrapdash.com/blog/angular-10-best-practices)
- Prioritize Testing and Validation for Reliable Applications
- Angular’s Testing Revolution: Vitest, Fake Timers & Testronaut (https://dev.to/rainerhahnekamp/angulars-testing-revolution-vitest-fake-timers-testronaut-2bnj)
- Top Software Testing Trends in 2026: The Future of Software – testomat.io (https://testomat.io/blog/software-testing-trends)
- The Future of Angular Testing Has Arrived (https://levelup.gitconnected.com/the-future-of-angular-testing-has-arrived-81072717393f)
- Announcing Angular v21 (https://blog.angular.dev/announcing-angular-v21-57946c34f14b)
- Adopt Continuous Integration and Deployment Practices
- CI/CD Best Practices & DevOps Pipeline 2026 | Kellton (https://kellton.com/kellton-tech-blog/continuous-integration-deployment-best-practices-2025)
- Unlock Seamless Deployment With CI/CD Pipelines For Angular Applications (https://innoraft.ai/blog/unlock-seamless-deployment-cicd-pipelines-angular-applications)
- Kubernetes Is Taking Over: Deploy Smarter With 4 New Techniques (https://thenewstack.io/kubernetes-is-taking-over-deploy-smarter-with-4-new-techniques)
- Refonte Learning : DevOps Engineering in 2026: Top CI/CD Tools, Trends, and Best Practices (GitHub Actions vs Jenkins) (https://refontelearning.com/blog/devops-engineering-in-2026-top-ci-cd-tools-trends-and-best-practices-github-actions-vs-jenkins)