Introduction
In an industry where financial data security is critical, the stakes for software development teams have reached unprecedented levels. Implementing effective practices in software development and security not only protects sensitive information but also strengthens an organization’s reputation amid rising cyber threats. However, as organizations work to incorporate robust security measures, they frequently encounter challenges that can impede successful implementation. What essential strategies can be employed to navigate these complexities and ensure a secure software development lifecycle in finance?
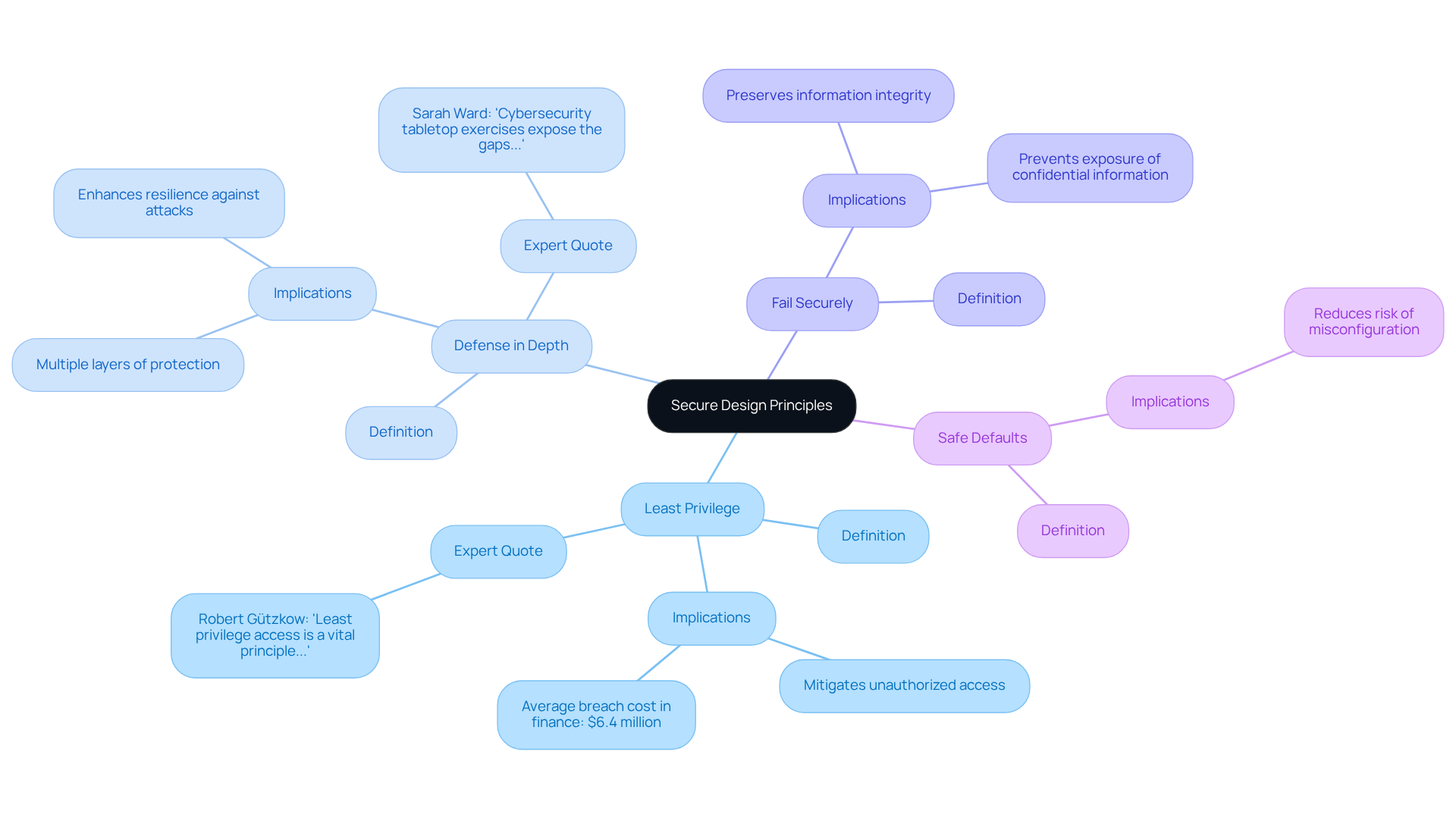
Establish Secure Design Principles
To establish secure design principles, organizations must adopt a security-by-design approach that integrates security considerations into every phase of the software development lifecycle (SDLC). Key principles include:
- Least Privilege: Users and systems should have only the permissions necessary to perform their functions, significantly reducing the potential damage from data breaches. Applying this principle can assist in mitigating risks related to unauthorized access, particularly in financial services where sensitive information is at stake. As Robert Gützkow, a Product Protection Engineer, emphasizes, ‘Least privilege access is a vital principle that organizations should prioritize to safeguard systems, information, and reputation.’ Furthermore, the average expense of a breach in the finance sector is recorded to be $6.4 million, underscoring the financial consequences of insufficient access controls.
- Defense in Depth: Employ multiple layers of protective measures to safeguard sensitive data and systems. This strategy complicates an attacker’s efforts, as breaching one layer does not guarantee access to the next, thereby enhancing overall protection resilience. Sarah Ward, Chief Legal Officer, states, ‘Cybersecurity tabletop exercises expose the gaps. You can have a beautifully written incident response plan, but if you don’t test it, you’ll realize too late that key decision-makers are missing when a crisis hits.’ This highlights the importance of layered security in preparing for potential breaches.
- Fail Securely: Systems should be designed to fail in a secure manner, ensuring that failures do not expose confidential information or create new vulnerabilities. This principle is vital in preserving information integrity and confidentiality, particularly during unforeseen events.
- Safe Defaults: Set up systems with protection in mind, establishing safe settings as the default. This lowers the risk of misconfiguration, which is a frequent weakness that can result in data breaches.
While implementing these principles, organizations may encounter challenges such as resistance to change or lack of awareness among staff. Addressing these common pitfalls is essential for successful adoption. By embedding these principles into the software development and security design phase, organizations can create a robust protective framework that proactively addresses potential threats, ultimately safeguarding sensitive information and ensuring compliance with industry regulations.
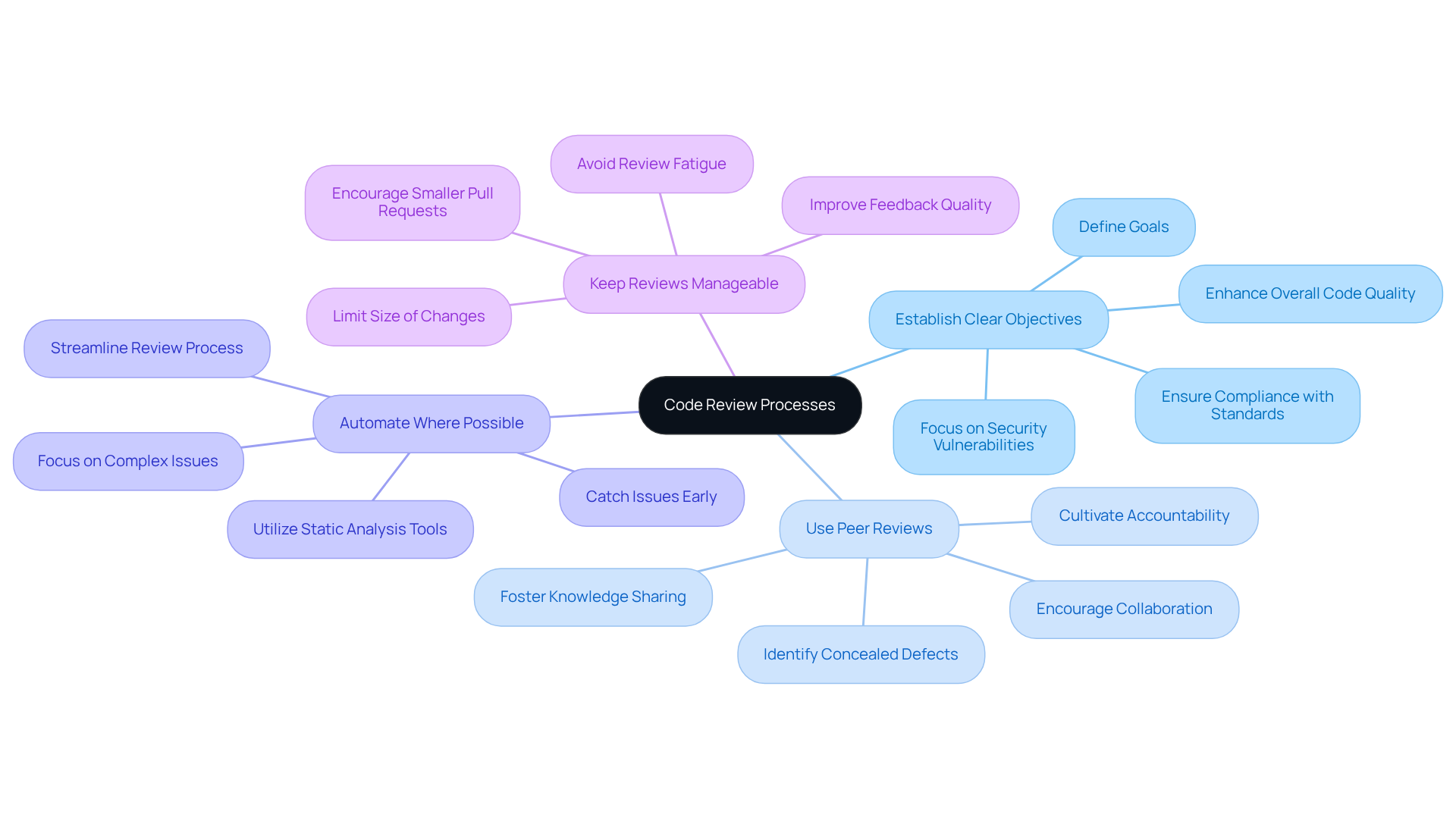
Implement Rigorous Code Review Processes
To implement effective code review processes, organizations should consider several best practices:
- Establish Clear Objectives: Clearly defining the goals of the code review process is essential. Focus on identifying security vulnerabilities within the context of software development and security, ensuring compliance with coding standards, and enhancing overall code quality. This clarity aligns team efforts and sets expectations.
- Use Peer Reviews: Encouraging developers to engage in peer reviews fosters collaboration and knowledge sharing. This practice not only helps identify issues that a single developer might overlook but also cultivates a culture of accountability and continuous improvement. Research indicates that formal reviews can identify 60-65% of concealed defects before they reach production, significantly enhancing software reliability.
- Automate Where Possible: Utilizing tools that automate aspects of the review process, such as static analysis tools, can quickly identify common vulnerabilities and uphold programming standards. Automation streamlines the review process, allowing teams to focus on more complex issues that require human insight. Static analysis aids in catching issues early, contributing to a more stable and secure codebase.
- Keep Reviews Manageable: It is crucial to limit the size of changes being reviewed to ensure thorough examination. Smaller pull requests are simpler to handle and less likely to burden reviewers, resulting in more effective feedback and improved work quality. Research shows that large pull requests often lead to lower-quality reviews, making it vital to encourage smaller, more frequent submissions.
By adopting these practices, organizations can significantly enhance their software development and security, ultimately leading to more dependable financial applications that meet the stringent demands of the industry. As Enrique Jose Tabuena points out, ‘Success in software and app development increasingly depends on the rigor of questioning, understanding, and refinement of the programming.
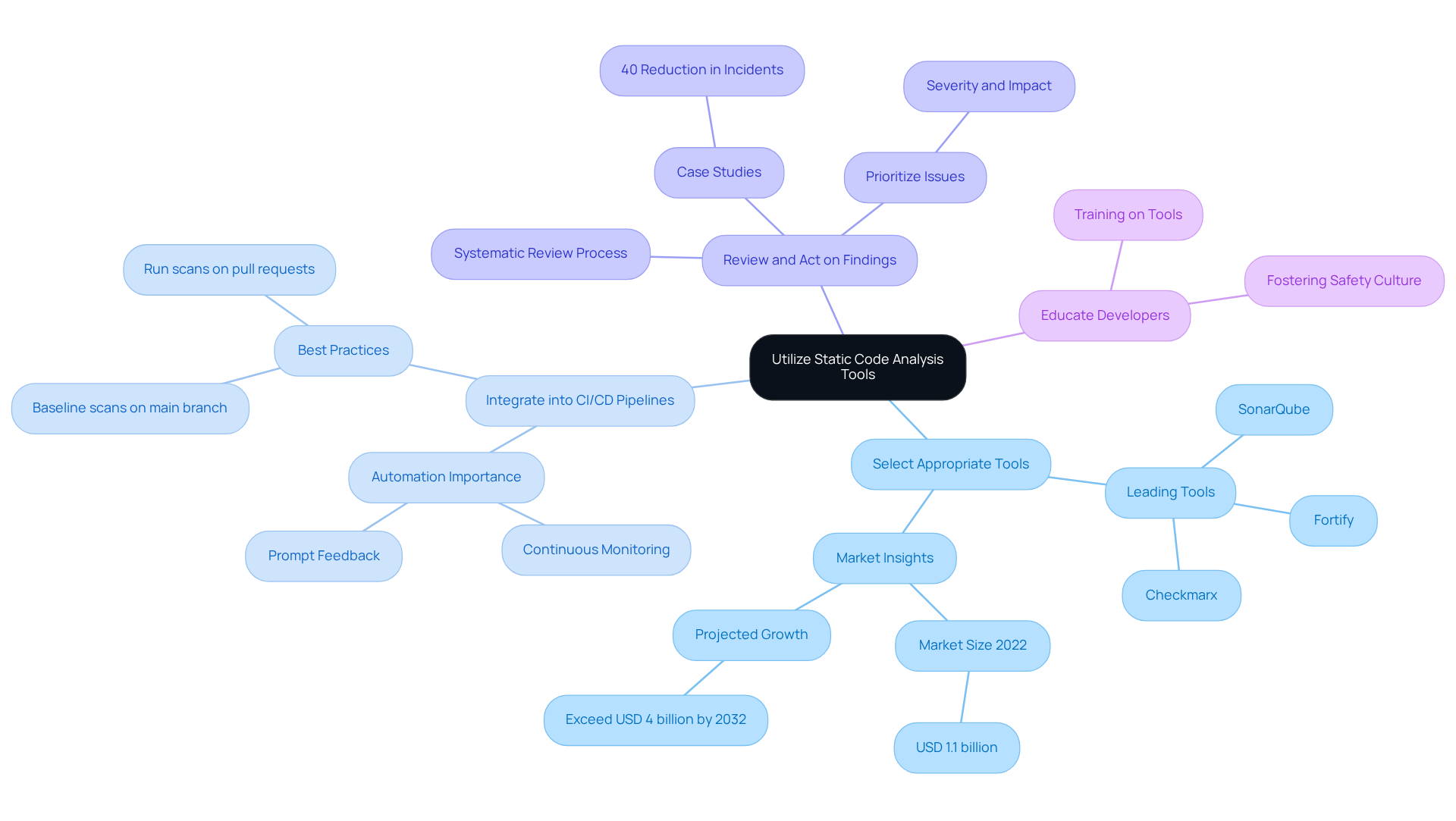
Utilize Static Code Analysis Tools
Integrating static program analysis tools into the software development and security process significantly enhances safety in financial applications. Key practices to consider include the following:
- Select Appropriate Tools: It is essential to choose static analysis tools that align with the programming languages and frameworks used in your projects. Leading options such as SonarQube, Checkmarx, and Fortify are recognized for their effectiveness in identifying vulnerabilities. Notably, the static analysis market size reached USD 1.1 billion in 2022 and is projected to exceed USD 4 billion by 2032, underscoring the growing importance of these tools in the financial sector.
- Integrate into CI/CD Pipelines: Automating the execution of static analysis tools within continuous integration and continuous deployment (CI/CD) pipelines is crucial. This integration ensures that code is examined with each commit, providing prompt feedback on potential vulnerabilities. As Corgea states, “CI/CD is your automation backbone,” highlighting the critical role of automation in maintaining security.
- Review and Act on Findings: Establishing a systematic process for reviewing the findings from static analysis tools is vital. Address identified vulnerabilities promptly by prioritizing issues based on their severity and potential impact on the application. Case studies have shown that organizations utilizing automated static analysis in DevSecOps environments experience up to a 40% reduction in security-related incidents.
- Educate Developers: Providing comprehensive training for developers on interpreting the results from static analysis tools and implementing necessary fixes is essential. This education enhances their ability to create secure code from the outset, fostering a culture of safety awareness. By incorporating these practices, organizations can enhance software development and security, allowing them to identify vulnerabilities early in the development process and significantly reducing the risk of breaches in their financial applications.
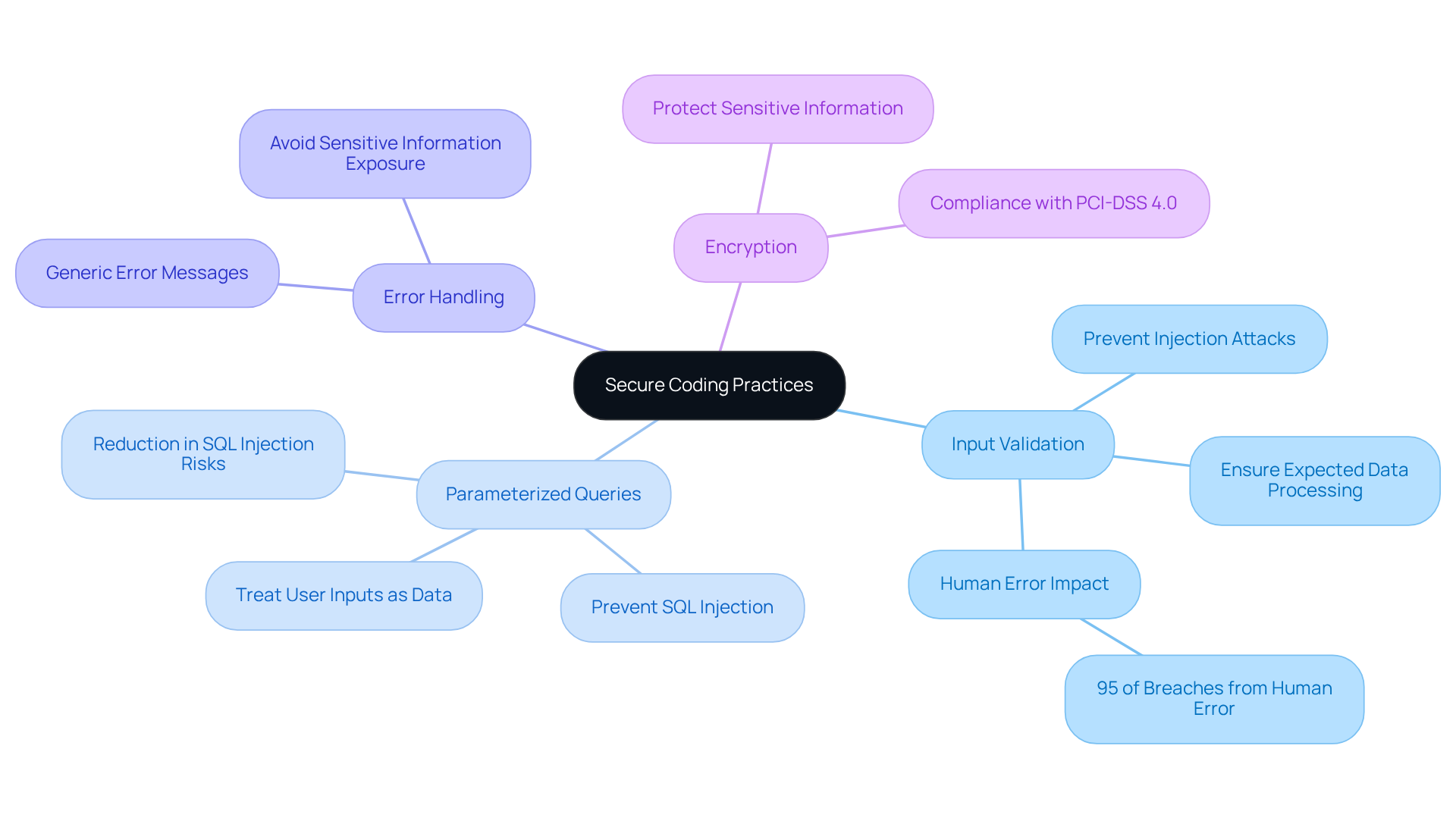
Adopt Secure Coding Practices
To adopt secure coding practices, developers should adhere to the following guidelines:
- Input Validation: Always validate user inputs to prevent injection attacks and ensure that only expected data is processed by the application. This practice is crucial in financial software development and security, where inadequate validation can result in serious vulnerabilities. Notably, 95 percent of security breaches result from human error, underscoring the critical need for robust input validation.
- Use Parameterized Queries: When interacting with databases, utilize parameterized queries to prevent SQL injection attacks. This approach ensures that user inputs are treated strictly as data, not executable code, significantly reducing the risk of exploitation. Research shows that organizations using parameterized queries encounter a significant reduction in SQL injection risks.
- Implement Proper Error Handling: Avoid exposing sensitive information in error messages. Instead, implement generic error messages that do not reveal details about the application’s internal workings. This practice helps to mitigate the risk of attackers gaining insights into potential vulnerabilities.
- Encrypt Sensitive Information: Employ strong encryption standards to protect sensitive information both at rest and in transit. This is crucial for safeguarding financial information from unauthorized access, ensuring compliance with industry regulations such as PCI-DSS 4.0, which mandates secure coding training for developers handling payment data.
By incorporating these secure coding practices into the software development and security process, organizations can significantly lower the risk of weaknesses and enhance the security of their financial applications. Additionally, referencing OWASP Secure Coding Practices can provide further guidance on minimizing vulnerabilities and protecting applications effectively.
Conclusion
In the finance industry, adopting effective practices in software development and security is paramount, given the high stakes involved. Organizations can establish a resilient framework that safeguards sensitive information and ensures compliance with industry regulations by integrating secure design principles, rigorous code review processes, static code analysis tools, and secure coding practices.
Key strategies highlighted include:
- The implementation of the principle of least privilege
- The maintenance of a defense-in-depth approach
- The assurance of fail-safe designs
Furthermore, the importance of conducting thorough code reviews, utilizing automated tools for static analysis, and adhering to secure coding guidelines-such as input validation and encryption-cannot be overstated. Each of these elements is crucial in mitigating risks associated with data breaches and enhancing the overall security posture of financial applications.
As cyber threats become increasingly sophisticated, organizations must prioritize these best practices to protect their systems and customer data. By fostering a culture of security awareness and continuous improvement, financial institutions not only shield themselves from potential breaches but also cultivate trust with their clients. Proactive measures taken today will lay the groundwork for a more secure and resilient future in finance.
Frequently Asked Questions
What is the security-by-design approach in software development?
The security-by-design approach integrates security considerations into every phase of the software development lifecycle (SDLC), ensuring that security is a fundamental aspect of the development process.
What is the principle of Least Privilege?
The principle of Least Privilege states that users and systems should have only the permissions necessary to perform their functions, reducing the potential damage from data breaches and unauthorized access.
Why is the principle of Least Privilege particularly important in financial services?
It is crucial in financial services because sensitive information is at stake, and the average expense of a breach in this sector is $6.4 million, highlighting the financial consequences of insufficient access controls.
What does Defense in Depth entail?
Defense in Depth involves employing multiple layers of protective measures to safeguard sensitive data and systems, making it more difficult for attackers to breach all layers of security.
How does the principle of Fail Securely contribute to system security?
Fail Securely ensures that systems are designed to fail in a secure manner, preventing the exposure of confidential information or the creation of new vulnerabilities during unforeseen events.
What are Safe Defaults in the context of secure design principles?
Safe Defaults refer to setting up systems with protection in mind by establishing safe settings as the default, which helps lower the risk of misconfiguration that can lead to data breaches.
What challenges might organizations face when implementing secure design principles?
Organizations may encounter challenges such as resistance to change and a lack of awareness among staff, which are common pitfalls that need to be addressed for successful adoption.
How can organizations ensure compliance with industry regulations while implementing secure design principles?
By embedding secure design principles into the software development and security design phases, organizations can create a robust protective framework that proactively addresses potential threats and ensures compliance with industry regulations.
List of Sources
- Establish Secure Design Principles
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- bigid.com (https://bigid.com/blog/principle-of-least-privilege-access)
- betasystems.com (https://betasystems.com/resources/blog/principle-of-least-privilege)
- cloudaware.com (https://cloudaware.com/blog/devsecops-statistics)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- Implement Rigorous Code Review Processes
- Top 12 Code Quality Metrics to Measure Software Performance (https://axify.io/blog/code-quality-metrics)
- 46% Distrust Rate in AI Coding Puts Human Code Review Back in Spotlight (https://news.designrush.com/46-percent-developers-distrust-ai-coding-cools-human-code-review)
- Measuring Code Review Effectiveness: KPIs & Metrics Guide 2025 (https://propelcode.ai/learn/measuring-code-review-effectiveness)
- fintechweekly.com (https://fintechweekly.com/magazine/articles/why-every-development-team-needs-a-code-review-strategy)
- Improve Security with Smarter Code Review Practices (https://artsyltech.com/blog/the-role-of-code-review-in-enhancing-cybersecurity)
- Utilize Static Code Analysis Tools
- Static Code Detection Tool Market Outlook 2025-2032 (https://intelmarketresearch.com/static-code-detection-tool-2025-2032-288-5358)
- How to Integrate Static Analysis Tools into Your CI/CD Pipeline | Corgea (https://corgea.com/learn/how-to-integrate-static-analysis-tools-into-your-ci-cd-pipeline)
- Static Analysis Market Size & Share | Statistics Report, 2032 (https://gminsights.com/industry-analysis/static-analysis-market)
- AI-Driven Static Analysis Remediation for CI/CD Pipelines – Parasoft (https://parasoft.com/blog/bringing-ai-driven-static-analysis-remediation-into-ci-cd)
- CI/CD Pipelines for Core Banking Applications (https://oceanobe.com/news/ci-cd-pipelines-for-core-banking-applications/1536)
- Adopt Secure Coding Practices
- 9 Best Practices for Secure Coding in 2026 (https://securityjourney.com/post/best-practices-for-secure-coding)
- The top 20 expert quotes from the Cyber Risk Virtual Summit (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- OWASP Secure Coding Practices | App Security Master Guide 2026 (https://appsecmaster.net/blog/owasp-secure-coding-practices-building-bulletproof-software-in-2026)
- Solutions Review: Cybersecurity Awareness Month Quotes from Industry Experts in 2024 – Mark43 (https://mark43.com/press/solutions-review-cybersecurity-awareness-month-quotes-from-industry-experts-in-2024)
- Medium (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
