Introduction
Organizations today face increasing complexities in managing crises due to evolving threats and stringent regulatory requirements. The effective implementation of incident response management software can significantly enhance an organization’s ability to monitor events, automate workflows, and improve communication during crises. Organizations often find it challenging to seamlessly incorporate incident response management software into their established workflows. This lack of integration can result in delayed responses and heightened risks during critical incidents. Understanding and implementing best practices for incident response management software is essential for organizations to mitigate risks effectively.
Understand the Role of Incident Response Management Software
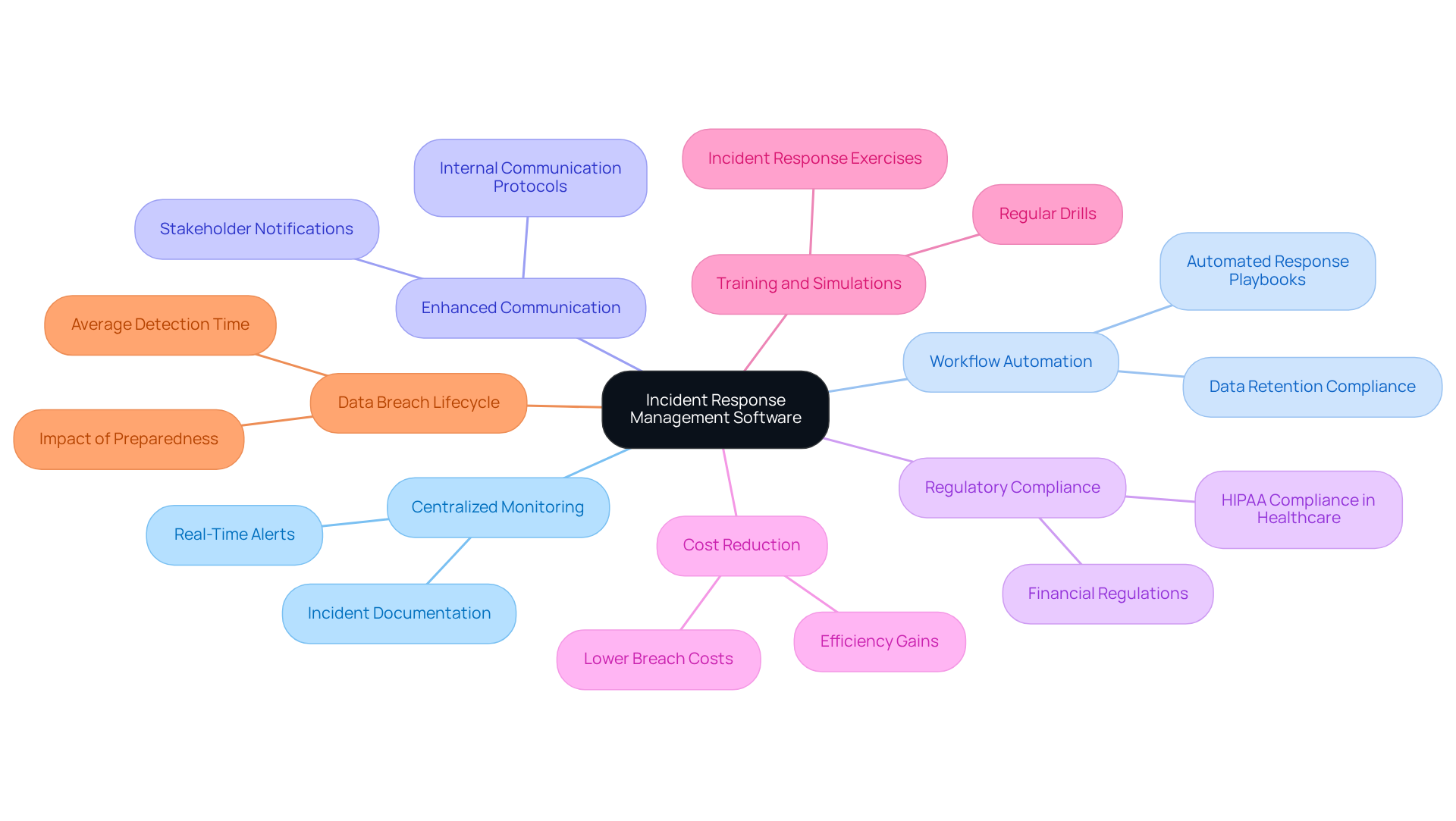
Crisis management software is essential for organizations that want to avoid the pitfalls of ineffective event response. A centralized platform for monitoring events, automating workflows, and enhancing communication is a key feature of crisis management software. Incorporating event management software into existing processes allows organizations to record, classify, and prioritize occurrences more effectively. This not only improves awareness of current situations but also aids in adhering to regulatory standards, especially in heavily regulated sectors such as finance and healthcare.
For instance, research from the Ponemon Institute shows that companies with developed response processes incur 72% lower costs related to data breaches compared to those without established protocols. In healthcare, effective event management is crucial for complying with HIPAA regulations, ensuring that occurrences involving protected health information are documented and reported accurately.
Additionally, organizations that regularly conduct training and simulations are able to respond to events 35% faster, underscoring the importance of readiness for compliance and data protection. Cybersecurity expert Sean Blanton highlights that organizations without a formal breach plan face a lifecycle of 258 days, compared to just 189 days for those with a strategy, reinforcing the necessity of proactive management for risk reduction and compliance.
Ultimately, the implementation of structured crisis management processes is not just beneficial; it is essential for maintaining compliance and protecting sensitive information.
Identify Key Features for Effective Incident Response Management
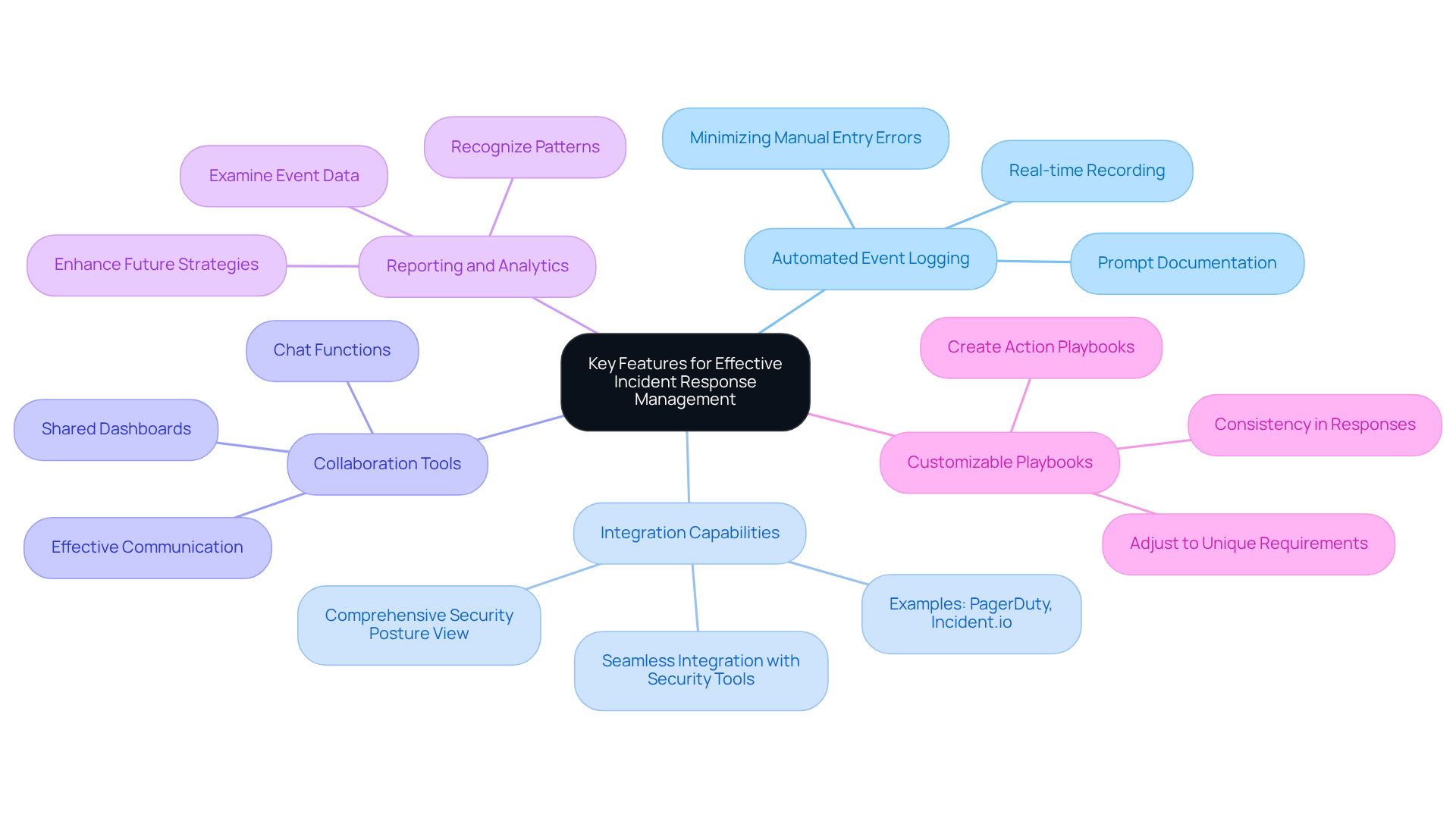
When selecting event management software, organizations must focus on features that significantly enhance their operational capabilities. Key features include:
- Automated Event Logging: This essential feature enables real-time recording of occurrences, minimizing manual entry errors and ensuring prompt documentation of all events. Since data exfiltration can happen within 72 minutes of initial access, it is vital to log events quickly and accurately for an effective response. As observed by Daria Yankevich, “A contemporary management platform should function as a control center-strongly linked with your stack, automating wherever possible, and allowing individuals to concentrate on the decisions that are most important.”
- Integration Capabilities: The software should seamlessly integrate with existing security tools and systems, providing a comprehensive view of the organization’s security posture. Tools like PagerDuty and Incident.io are noted for their robust integration capabilities, which are vital for maintaining operational efficiency and ensuring that all incident-related data is easily accessible.
- Collaboration Tools: Effective communication features, such as chat functions and shared dashboards, facilitate teamwork among team members during issue resolution. Clear communication is essential for coordinated actions, especially in high-pressure situations.
- Reporting and Analytics: Strong reporting features enable organizations to examine event data, recognize patterns, and enhance future action strategies. This approach drives continuous improvement in event management practices.
- Customizable Playbooks: Organizations should have the capability to create and adjust action playbooks suited to their unique requirements. This customization guarantees that responses are consistent and effective, aligning with the unique challenges encountered in regulated industries.
By concentrating on these attributes, companies can greatly improve their ability to manage occurrences with incident response management software, ensuring they are adequately equipped to address situations proficiently and successfully. Organizations often face challenges with integration complexity and system misalignment, which can undermine software effectiveness. Addressing these challenges is essential for ensuring that organizations can respond effectively to incidents and maintain operational integrity.
Develop a Comprehensive Incident Response Plan
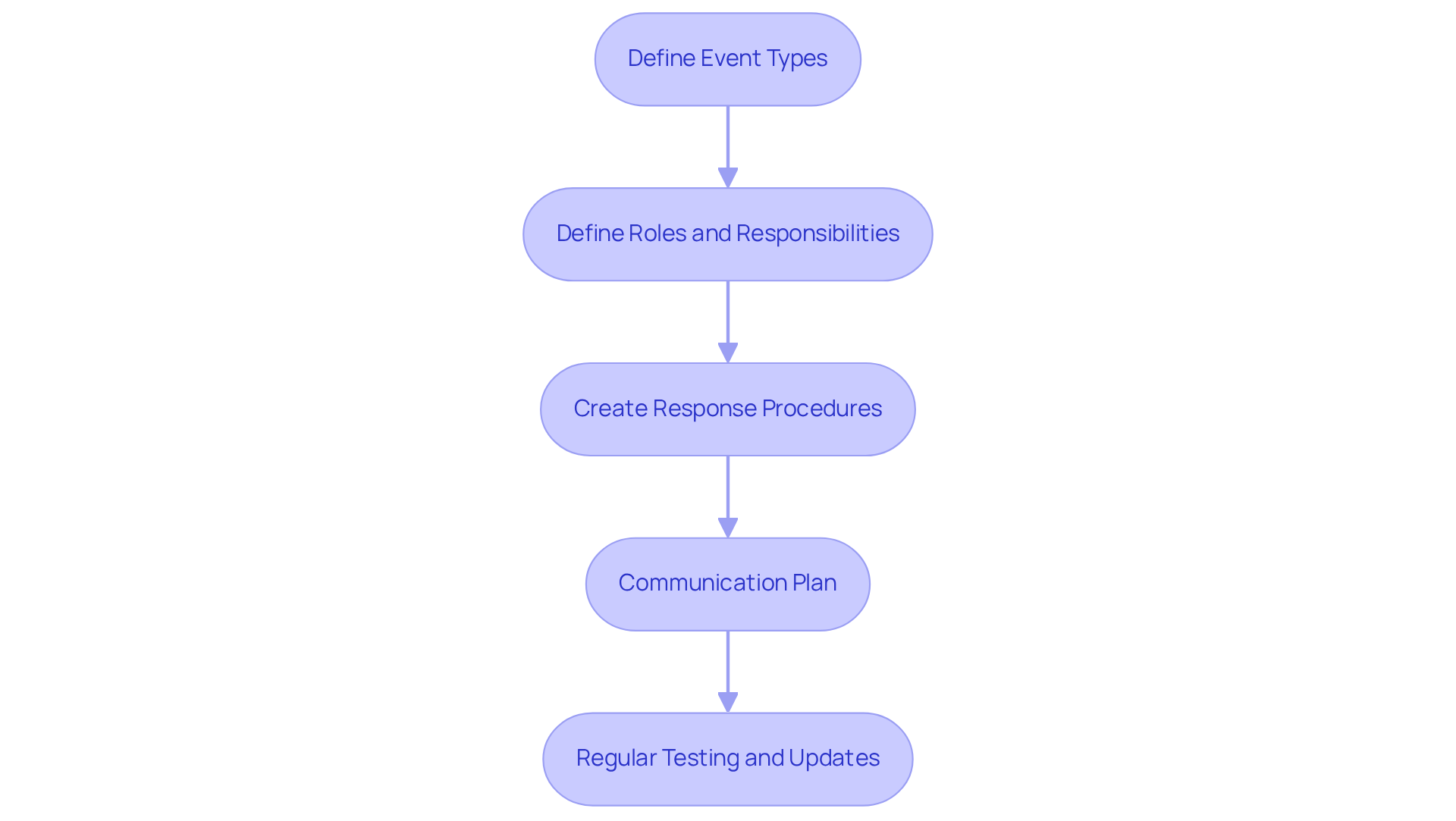
Without a thorough incident response management software strategy, organizations risk inadequate handling of critical occurrences that can lead to significant repercussions. To develop an effective incident response plan (IRP), organizations must consider the following key steps:
- Define Event Types: Clearly categorize what constitutes an occurrence within your organization, including data breaches, system outages, and security threats.
- Define Roles and Responsibilities: Allocate specific roles to team members, ensuring everyone understands their duties during an event.
- Create Response Procedures: Develop detailed protocols for addressing various types of occurrences, including detection, containment, eradication, and recovery steps.
- Communication Plan: Outline how information will be conveyed internally and externally during an event, including stakeholder notifications and public relations strategies.
- Regular Testing and Updates: Conduct regular drills and revise the IRP based on lessons learned from previous events and evolving threats.
Ultimately, implementing incident response management software not only enhances an organization’s resilience but also safeguards its reputation and operational integrity during crises.
Implement Continuous Training and Improvement Strategies
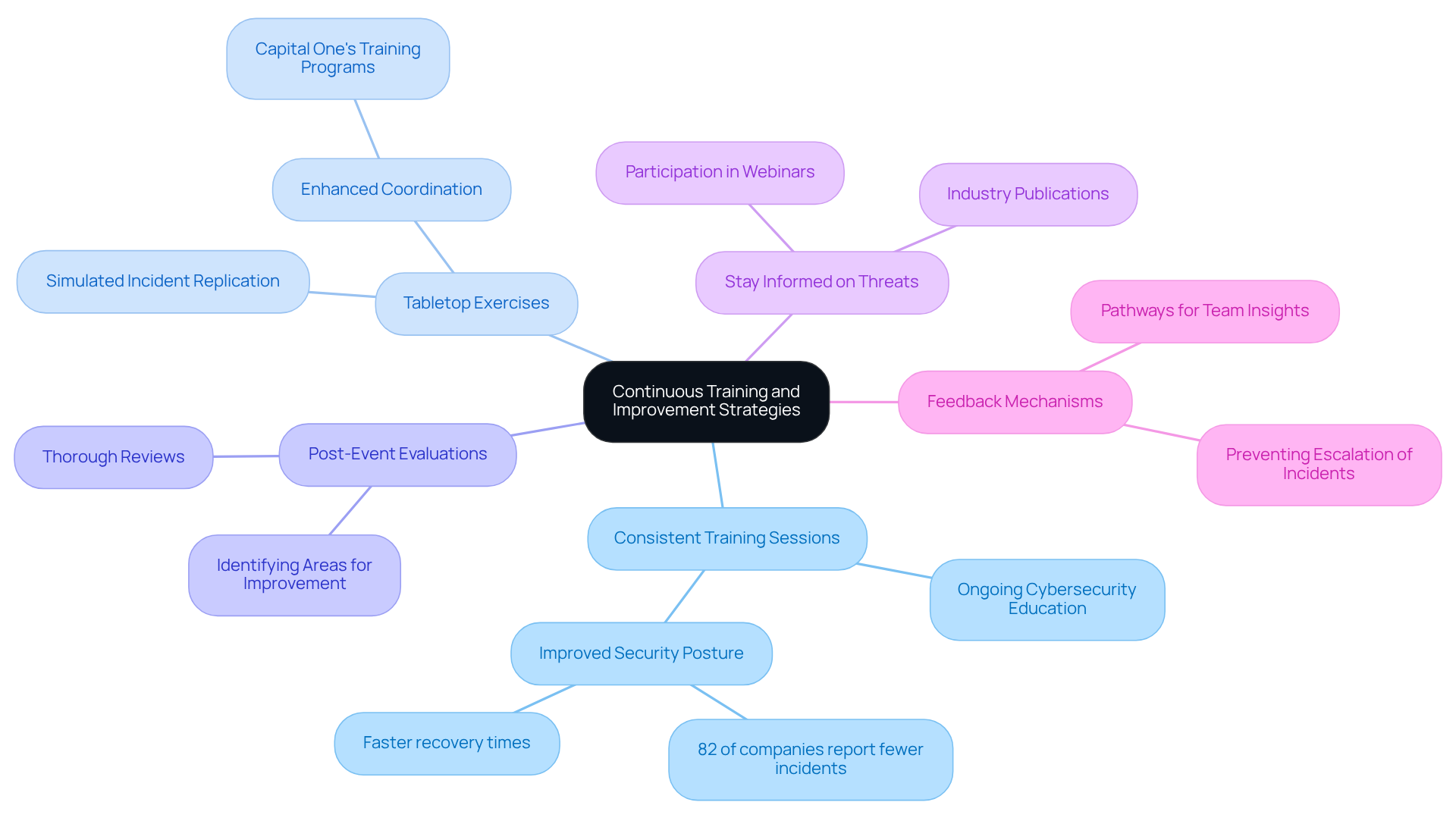
To enhance crisis management efficiency, organizations must prioritize continuous training and development. Here are key strategies to implement:
- Consistent Training Sessions: Continuous education for all personnel engaged in emergency management is crucial. This should cover new tools, techniques, and evolving threat landscapes to ensure preparedness. According to ISACA, 82% of companies with ongoing cybersecurity education reported improvements in their security posture, leading to fewer incidents and faster recovery.
- Arranging tabletop exercises allows groups to replicate incidents and evaluate the effectiveness of their incident response management software. These controlled environments allow group members to practice their roles and enhance coordination. For example, following a significant data breach in 2019, Capital One established more regular training programs for its cybersecurity teams, which greatly improved their ability to react.
- Post-Event Evaluations: Following an occurrence, conducting thorough reviews is crucial. Examining what was effective and recognizing areas for enhancement aids in recording lessons learned and improving the response plan (IRP). These reviews should focus on both what went wrong and how the incident management process performed, where delays occurred, and what can be improved.
- Stay Informed on Threats: Encourage group members to remain updated on the latest cybersecurity threats and trends. Participation in webinars, conferences, and industry publications fosters a proactive approach to threat management. As cyber threats develop, companies must modify their training to incorporate these changes, ensuring that their groups are ready for new challenges.
- Feedback Mechanisms: Creating pathways for team members to share insights on the event handling procedure encourages continuous improvement in incident management. Miscommunication and lack of clarity can escalate minor incidents into major crises.
These strategies empower organizations to enhance their incident response management software and adapt to the evolving cybersecurity landscape.
Conclusion
Effective incident response management is not merely beneficial; it is essential for organizations navigating crises successfully. Centralizing event monitoring and automating workflows enhances communication, allowing organizations to improve their response capabilities and comply with regulatory standards. The integration of structured processes and the right software tools not only protects sensitive information but also strengthens an organization’s overall resilience.
Key insights from this article highlight the importance of selecting software with essential features such as:
- Automated event logging
- Seamless integration capabilities
- Robust collaboration tools
Moreover, a comprehensive incident response plan and ongoing training significantly boost an organization’s incident management efficiency. Organizations that prioritize these practices are better positioned to respond to crises swiftly and effectively, minimizing potential damage and ensuring operational integrity.
In a landscape where incidents can escalate rapidly, the significance of proactive incident response management cannot be overstated. Organizations should embrace these best practices, invest in the right software, and cultivate a culture of continuous learning. By doing so, they will not only protect their assets but also build trust with stakeholders and maintain their reputation in the face of adversity. Adopting these strategies is imperative for organizations aiming to thrive in an unpredictable environment.
Frequently Asked Questions
What is the purpose of incident response management software?
Incident response management software is designed to help organizations effectively monitor events, automate workflows, and enhance communication to avoid ineffective event responses.
How does crisis management software benefit organizations?
It provides a centralized platform for recording, classifying, and prioritizing occurrences, improving awareness of current situations and aiding in adherence to regulatory standards, particularly in regulated sectors like finance and healthcare.
What impact do developed response processes have on data breach costs?
Research from the Ponemon Institute indicates that companies with established response processes incur 72% lower costs related to data breaches compared to those without such protocols.
Why is effective event management important in healthcare?
Effective event management is crucial in healthcare for complying with HIPAA regulations, ensuring accurate documentation and reporting of occurrences involving protected health information.
How does regular training and simulations affect event response times?
Organizations that regularly conduct training and simulations can respond to events 35% faster, highlighting the importance of preparedness for compliance and data protection.
What is the difference in breach lifecycle between organizations with and without a formal breach plan?
Organizations without a formal breach plan face an average lifecycle of 258 days, while those with a strategy have a lifecycle of just 189 days, emphasizing the need for proactive management.
Why are structured crisis management processes essential?
Structured crisis management processes are essential for maintaining compliance and protecting sensitive information within organizations.
List of Sources
- Understand the Role of Incident Response Management Software
- Tech Incident Management Software: Essential Capabilities for Regulated Industries (https://qredible.com/tech-incident-management-software-essential-capabilities-for-regulated-industries)
- The future of digital incident management (https://pwc.co.uk/industries/financial-services/understanding-regulatory-developments/the-future-of-digital-incident-management.html)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- 2026 Unit 42 Global Incident Response Report (https://paloaltonetworks.com/resources/research/unit-42-incident-response-report)
- Enhancing Compliance and Incident Management in Regulated Industries with Angelcam (https://angelcam.com/blog/enhancing-compliance-and-incident-management-in-regulated-industries-with-angelcam)
- Identify Key Features for Effective Incident Response Management
- Top Incident Response Tools 2026 (https://cybertriage.com/blog/best-incident-response-tools-2026)
- ilert.com (https://ilert.com/blog/top-5-incident-response-platforms-for-2026)
- Best Incident Response Tools for 2026 Security Needs (https://vmray.com/best-incident-response-tools-comprehensive-guide-2026)
- 10 Best Incident Response Softwares & Tools in 2026 (https://atlassystems.com/blog/incident-response-softwares)
- Incident Response in 2026: A Complete Enterprise Guide (https://uscsinstitute.org/cybersecurity-insights/resources/incident-response-in-2026-a-complete-enterprise-guide)
- Develop a Comprehensive Incident Response Plan
- frsecure.com (https://frsecure.com/blog/incident-response-statistics-how-do-you-compare)
- The National Cyber Incident Response Plan (NCIRP) | CISA (https://cisa.gov/national-cyber-incident-response-plan-ncirp)
- Incident Response Statistics to Know in 2025 (https://jumpcloud.com/blog/incident-response-statistics)
- Are you ready? Incident response planning and best practices – Smartria (https://smart-ria.com/blog/are-you-ready-incident-response-planning-and-best-practices)
- Implement Continuous Training and Improvement Strategies
- Why Annual Security Training Isn’t Enough in 2026 | NINJIO (https://ninjio.com/blog/why-cisos-are-moving-beyond-annual-security-awareness-training)
- Top 10 Incident Management Best Practices For IT Teams 2026 (https://cyble.com/knowledge-hub/top-10-incident-management-best-practices)
- Managing Cyber Risk in 2026 With Incident Response Training and Drills (https://cm-alliance.com/cybersecurity-blog/managing-cyber-risk-in-2026-with-incident-response-training-and-drills)
- Cyber Risk Is a Board Responsibility and Training Is the Missing Link | Fortinet Blog (https://fortinet.com/blog/industry-trends/cyber-risk-is-a-board-responsibility-and-training-is-the-missing-link)
- Building Cyber Resilience: How Continuous Training Fortifies Organizational Security | OffSec (https://offsec.com/blog/cyber-resilience-and-continuous-training)
