Introduction
Understanding and implementing HIPAA compliance in software development is not merely a regulatory necessity; it is a fundamental component of protecting patient privacy in an increasingly digital healthcare environment. As healthcare organizations face the challenges of evolving regulations and the complexities associated with managing Protected Health Information (PHI), the stakes have never been higher. This article delineates eleven essential steps that software developers can undertake to ensure compliance, ranging from conducting thorough risk assessments to enforcing stringent technical safeguards.
How can organizations effectively navigate these requirements to safeguard sensitive patient data while minimizing legal risks?
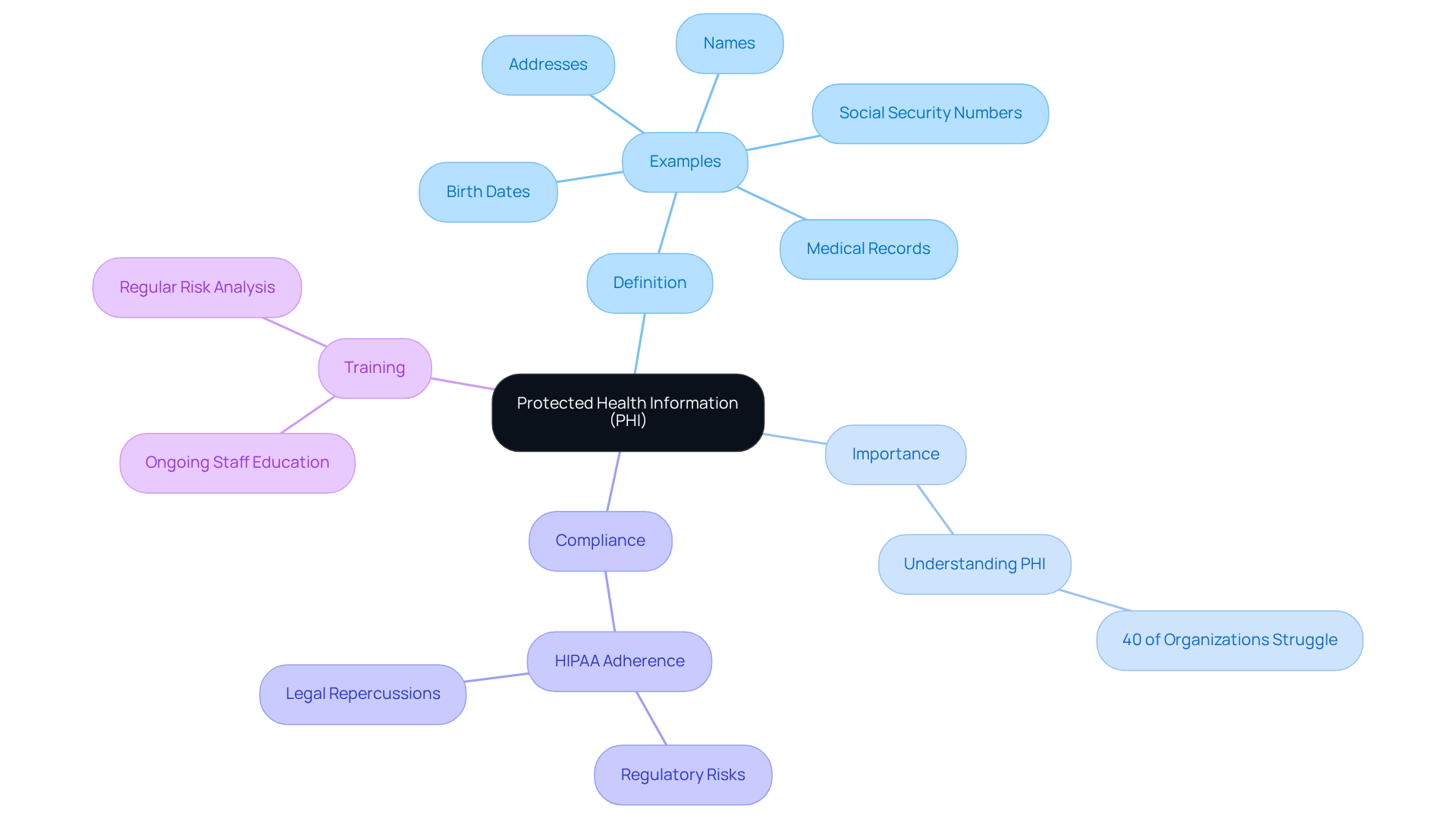
Define Protected Health Information (PHI)
Protected Health Information (PHI) refers to any individually identifiable health information that is transmitted or maintained in any form or medium. This includes, but is not limited to, names, addresses, birth dates, social security numbers, medical records, and any other information that can identify a patient.
As of 2026, healthcare organizations are increasingly acknowledging the critical importance of understanding PHI definitions. Studies indicate that approximately 40% of organizations still struggle to fully grasp these concepts. Recognizing what constitutes PHI is essential for ensuring HIPAA compliance for software development, as it defines the scope of data that must be protected.
Organizations must implement robust procedures to identify and manage PHI effectively. Failure to do so can lead to regulatory risks, increased complaints, and potential legal repercussions. Recent updates to HIPAA regulations highlight the evolving expectations surrounding healthcare privacy in 2026, emphasizing patient rights and stricter control over sensitive disclosures. This makes it imperative for software developers to incorporate HIPAA compliance for software development into their workflows.
Moreover, ongoing staff training and regular risk analysis are vital for maintaining compliance and effectively managing PHI.
Conduct a Comprehensive Risk Assessment
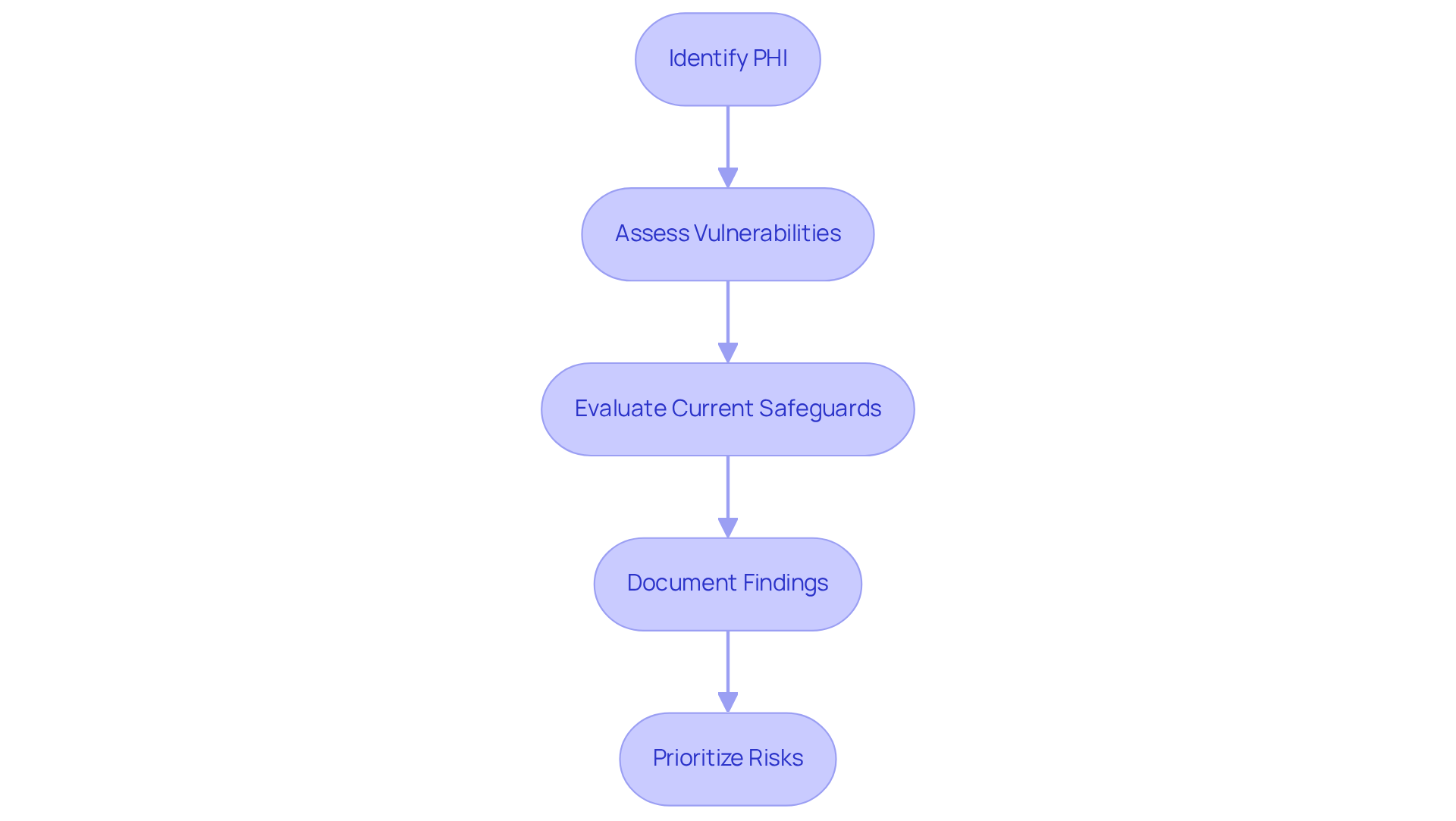
To conduct a comprehensive risk assessment, follow these steps:
- Identify PHI: Begin by cataloging all types of Protected Health Information (PHI) that your software will manage. This step ensures a thorough understanding of the information involved.
- Assess Vulnerabilities: Next, evaluate potential threats to this information, including unauthorized access, data breaches, and system failures. Regular vulnerability assessments are crucial; studies indicate that over 50% of healthcare organizations do not perform comprehensive risk assessments, leaving them exposed to significant risks.
- Evaluate Current Safeguards: Review existing security measures to determine their effectiveness against evolving threats. This evaluation should encompass technical protections such as encryption and access controls, which are now mandated under revised health privacy regulations.
- Document Findings: Create a detailed report that outlines identified risks and vulnerabilities, along with actionable recommendations for mitigation. This documentation is essential for compliance and should be regarded as a living document, frequently updated to reflect changes in the threat landscape.
- Prioritize Risks: Finally, rank the risks based on their potential impact and likelihood, focusing on those that pose the greatest threat to PHI. Organizations that proactively manage these risks are better positioned to protect sensitive information and achieve HIPAA compliance for software development.
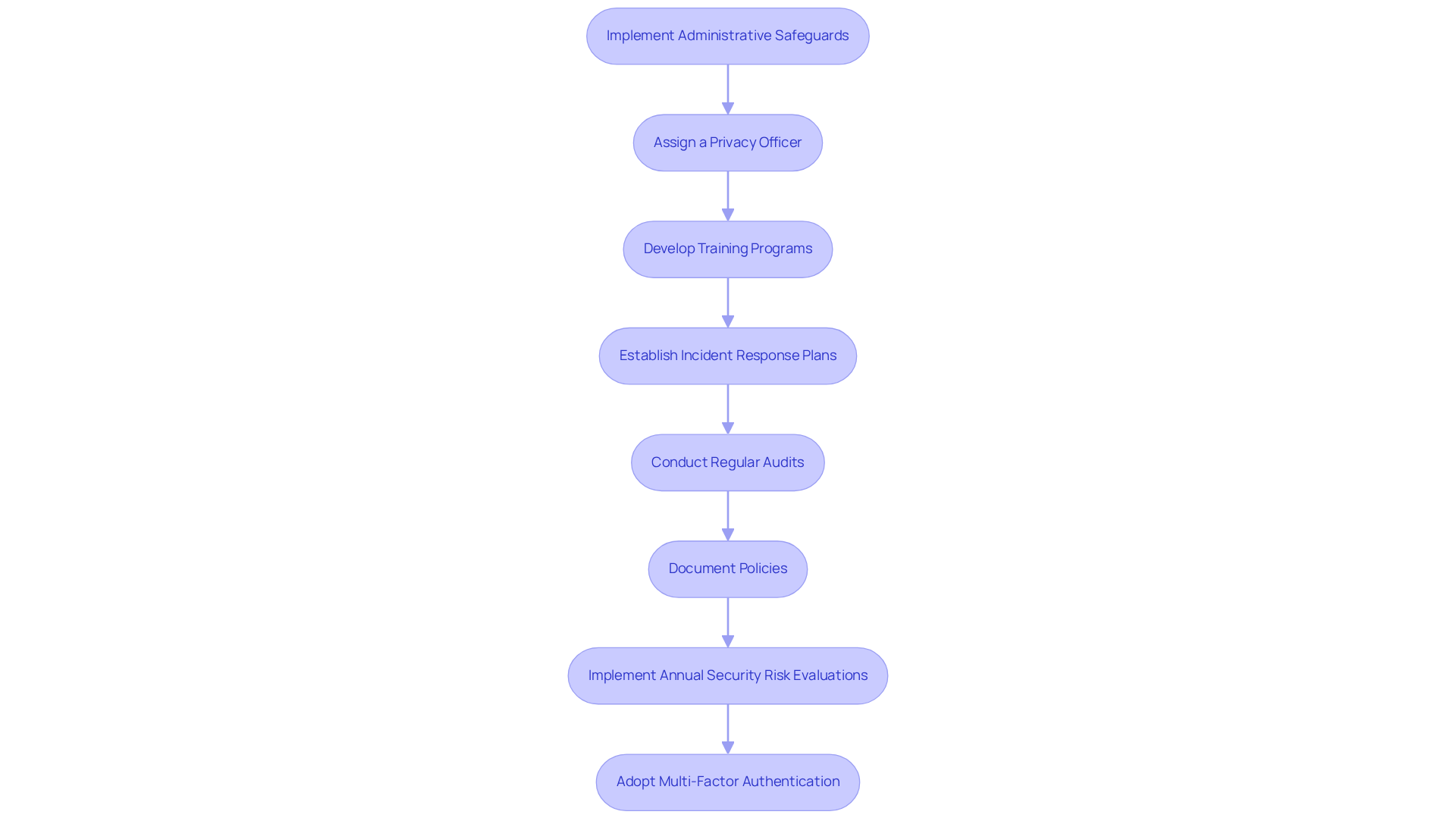
Implement Administrative Safeguards
Administrative safeguards encompass policies and procedures essential for managing the selection, development, and maintenance of security measures. Key steps include:
- Assign a Privacy Officer: Designate a specific individual responsible for overseeing adherence efforts, ensuring that all aspects of health information regulations are managed effectively.
- Develop Training Programs: Implement comprehensive training for all employees regarding HIPAA regulations and data protection practices. Consistent training is crucial; organizations that prioritize such programs report significantly lower rates of compliance violations. For example, a study revealed that healthcare organizations with robust training initiatives experienced a 30% reduction in HIPAA-related incidents.
- Establish Incident Response Plans: Formulate detailed protocols for addressing data breaches or security incidents. These plans should delineate immediate actions, communication strategies, and recovery processes to mitigate risks and ensure HIPAA compliance for software development.
- Conduct Regular Audits: Schedule periodic reviews of compliance practices to identify areas for enhancement. Regular audits enable organizations to stay ahead of regulatory changes and enhance their security posture, particularly for achieving HIPAA compliance for software development.
- Document Policies: Maintain clear, written policies that outline procedures for handling Protected Health Information (PHI). These documents should be readily accessible to all staff, ensuring that everyone comprehends their responsibilities in safeguarding sensitive data.
- Implement Annual Security Risk Evaluations: Conduct yearly assessments to identify vulnerabilities and ensure compliance with the latest Security Rule updates, which will be finalized in May 2026.
- Adopt Multi-Factor Authentication: In accordance with the updated HIPAA Security Rule, implement multi-factor authentication for all systems accessing electronic Protected Health Information (ePHI) to bolster security measures.
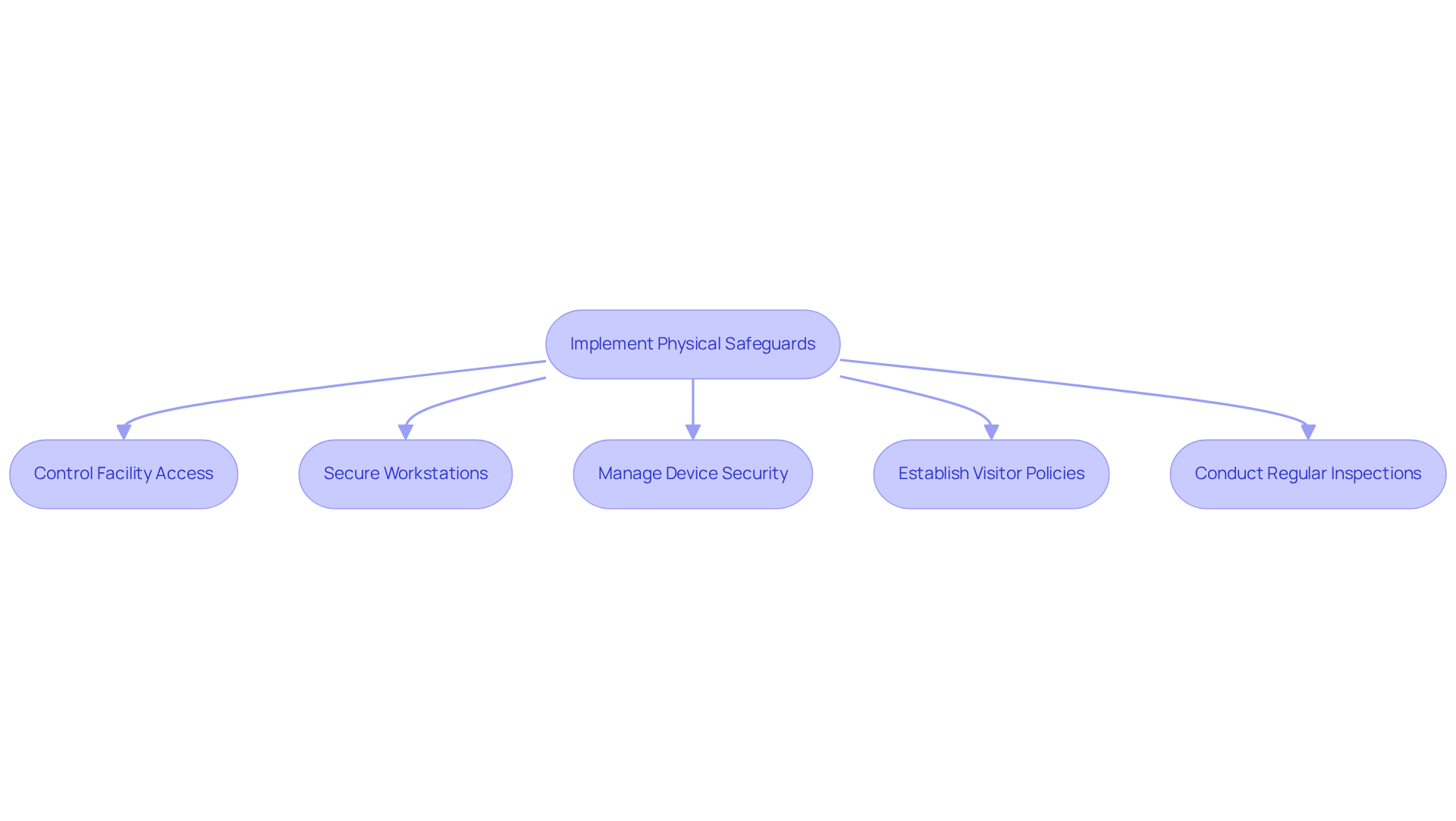
Apply Physical Safeguards
Physical safeguards are essential measures designed to protect the physical facilities and equipment that store or access protected health information (PHI). Key actions include:
- Control Facility Access: Implement robust security measures such as keycard access systems, trained security personnel, and surveillance cameras to monitor entry points and sensitive areas.
- Secure Workstations: Position workstations in secure locations, ensuring that screens are not visible to unauthorized personnel to prevent inadvertent exposure of PHI.
- Manage Device Security: Lock devices when not in use and enforce encryption protocols for portable devices to safeguard against unauthorized access and data breaches.
- Establish Visitor Policies: Develop clear protocols for managing visitors in areas where PHI is stored or accessed, ensuring that all visitors are logged and monitored.
- Conduct Regular Inspections: Periodically review and assess physical security measures to ensure their effectiveness and adherence to current regulations, adapting to any changes in operational needs or security threats.
As of 2026, a significant percentage of healthcare entities have begun implementing these physical safeguards, recognizing their critical role in achieving HIPAA compliance for software development and protecting sensitive patient information. Based on industry reports, around 70% of healthcare institutions have implemented physical safeguards to reduce risks related to unauthorized access and breaches of information. Organizations securing facilities that handle PHI are increasingly adopting these best practices to enhance their security posture. As Anna S. Kreamer notes, “Early action by covered entities and business associates will enable better positioning to manage risk, avoid operational disruption, and protect against cyber threats that continue to target the healthcare sector.” Furthermore, the proposed rule mandates encryption of ePHI at rest and in transit, emphasizing the need for comprehensive security measures.
Enforce Technical Safeguards
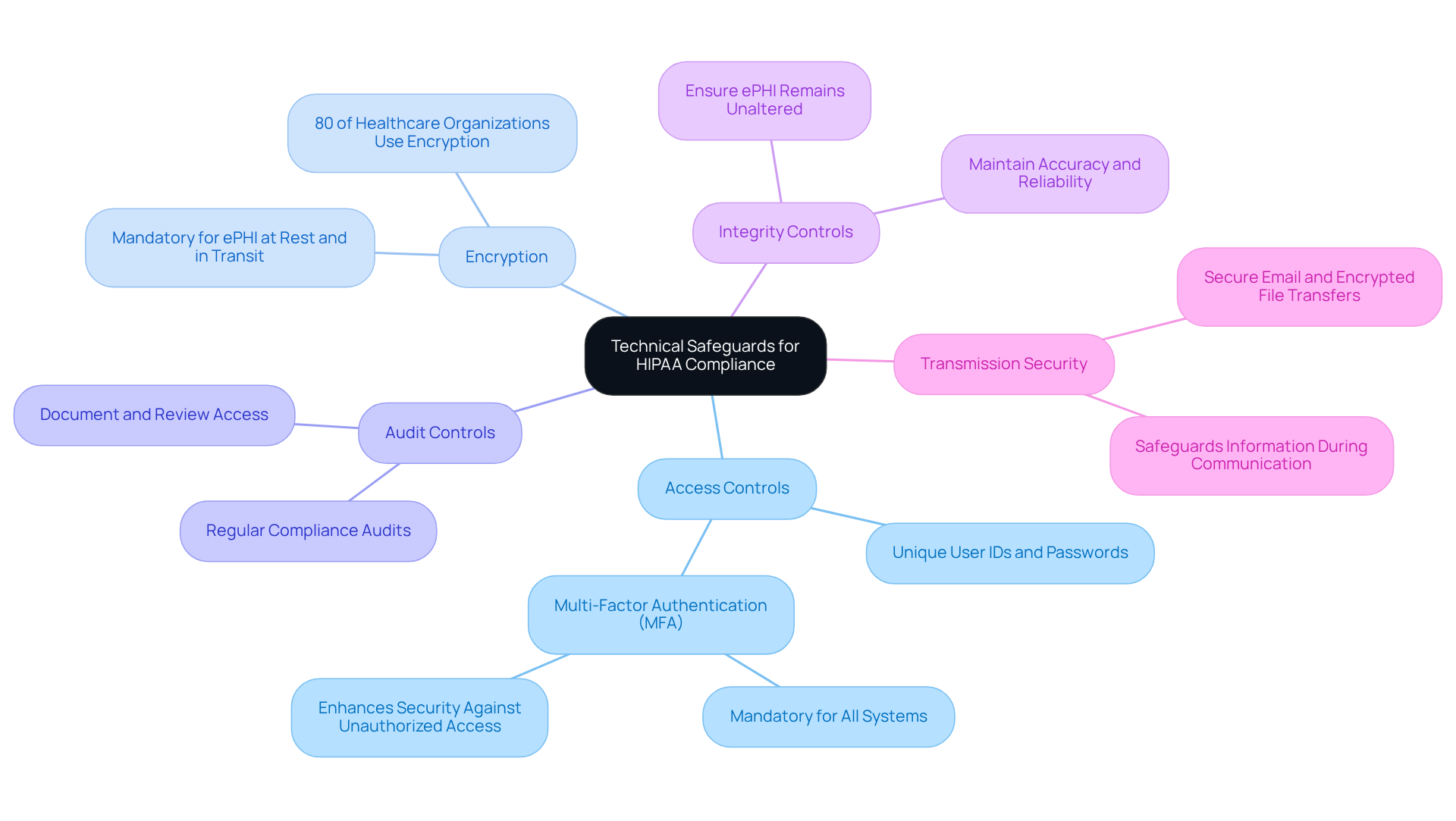
Technical safeguards are vital for ensuring HIPAA compliance for software development, encompassing the technology and policies essential for protecting electronic protected health information (ePHI). Key measures include:
- Access Controls: Implementing unique user IDs and passwords restricts access to ePHI, ensuring that only authorized personnel can view sensitive information.
- Encryption: Mandatory encryption for ePHI, both at rest and in transit, is crucial for safeguarding sensitive information against unauthorized access. Currently, around 80% of healthcare organizations employ encryption technologies to enhance information security, which demonstrates a growing commitment to HIPAA compliance for software development and protection.
- Audit Controls: Establishing mechanisms to document and review access and activity within systems containing ePHI facilitates accountability and transparency in information handling.
- Integrity Controls: Ensuring that ePHI remains unaltered or undestroyed in an unauthorized manner is vital for maintaining the accuracy and reliability of patient information.
- Transmission Security: Utilizing secure methods for transmitting ePHI, such as secure email or encrypted file transfers, safeguards information during communication.
Organizations like CBIZ have successfully implemented encryption and access controls, demonstrating enhanced operational efficiency and security through adherence to industry standards. As the 2026 Security Rule updates approach, the emphasis on encryption and robust access controls will become increasingly critical for achieving HIPAA compliance for software development and protecting patient information.
Enforce Strong User Authentication
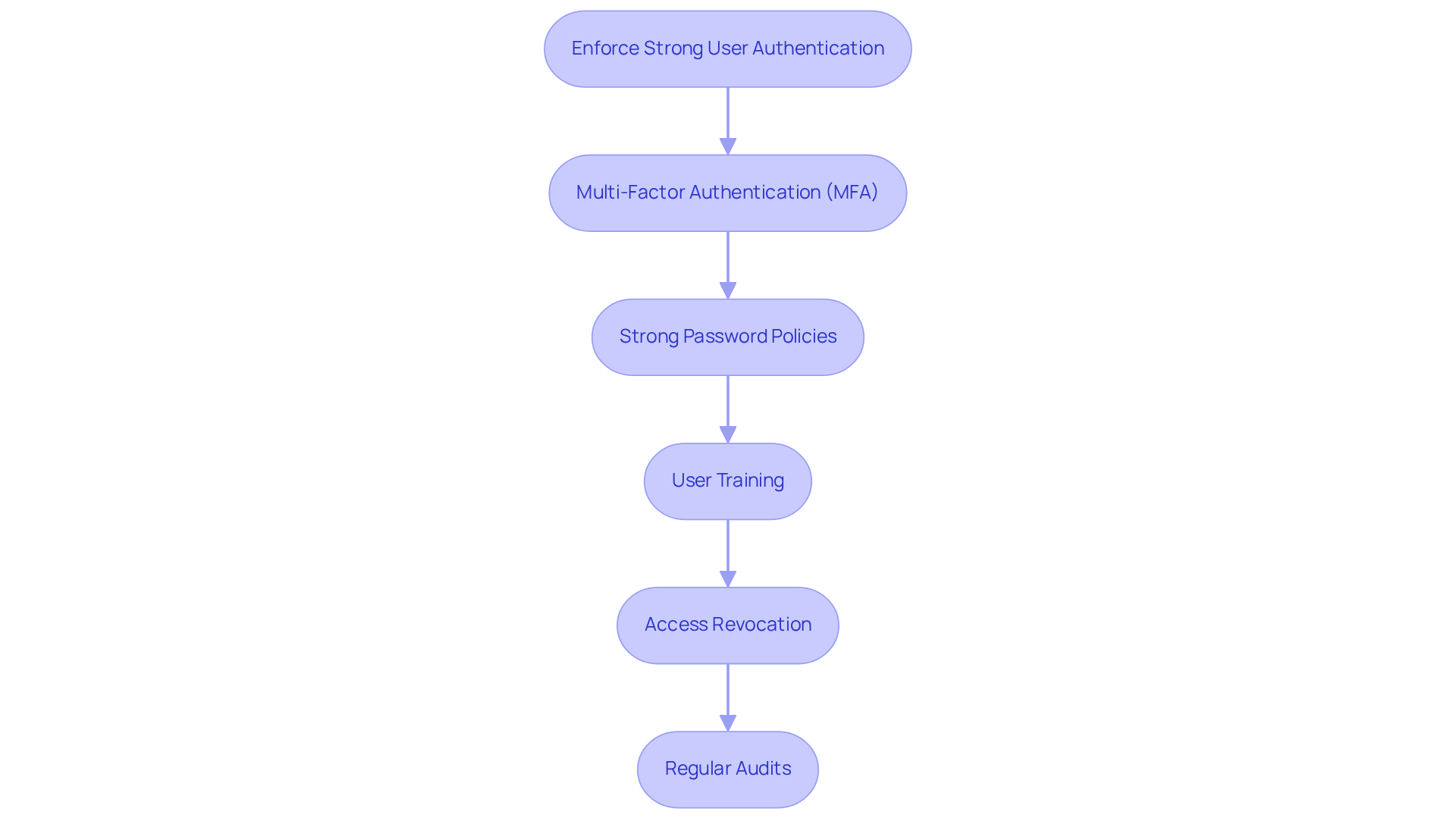
To enforce strong user authentication, consider implementing the following measures:
- Multi-Factor Authentication (MFA): It is essential to mandate that users provide at least two verification factors to access systems containing electronic Protected Health Information (ePHI). This requirement is particularly important as the forthcoming HIPAA regulations, expected to be finalized in May 2026, will mandate MFA for remote access and privileged accounts. This addresses vulnerabilities that have led to significant breaches in healthcare.
- Strong Password Policies: Establishing policies that enforce the use of complex passwords and require regular updates is crucial. Such measures help mitigate risks associated with unpatched software vulnerabilities, which were responsible for nearly 20% of healthcare ransomware attacks in 2024.
- User Training: Providing comprehensive training for users on secure authentication practices and how to recognize phishing attempts is vital. Many information breaches occur due to compromised credentials, underscoring the necessity for a well-informed workforce.
- Access Revocation: It is imperative to ensure that access rights are promptly revoked for users who no longer require them, such as former employees. This practice is essential for maintaining security and adhering to regulatory standards, particularly in environments where sensitive information is managed.
- Regular Audits: Conducting regular audits of user access logs to identify unauthorized access attempts is a proactive measure. This aligns with the proposed HIPAA updates, which will require healthcare entities to achieve HIPAA compliance for software development by performing vulnerability scanning every six months and penetration testing annually to enhance their security posture.
Sign Business Associate Agreements (BAAs)
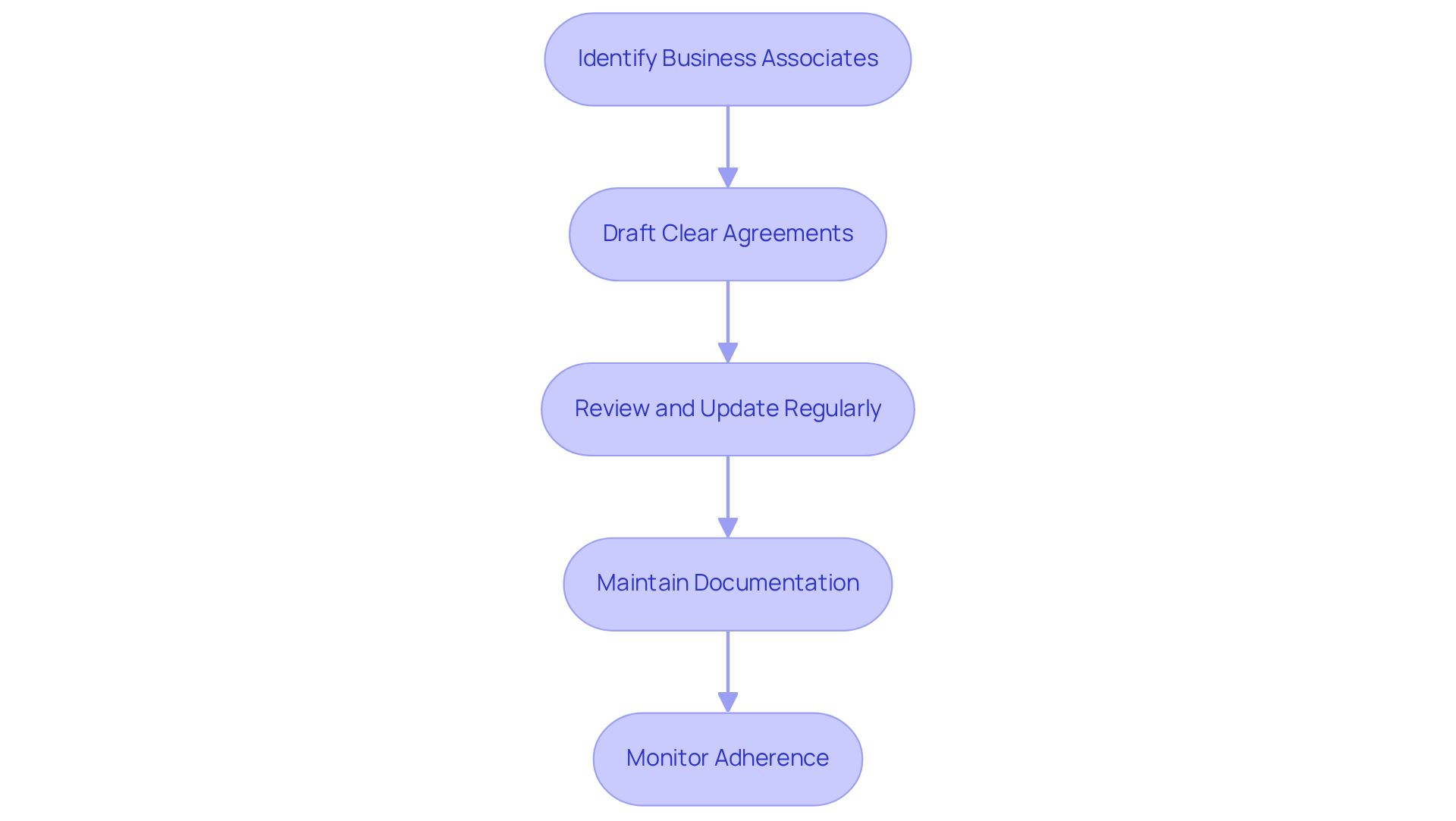
Business Associate Agreements (BAAs) are essential contracts that define the responsibilities of third-party vendors handling Protected Health Information (PHI). To ensure compliance and safeguard patient data, organizations should adhere to the following key steps:
- Identify Business Associates: Organizations must determine which vendors will access PHI and require a BAA to formalize their obligations.
- Draft Clear Agreements: BAAs should explicitly outline the permitted uses and disclosures of PHI, along with the necessary security measures that the business associate must implement to protect this information.
- Review and Update Regularly: Periodic reviews of BAAs are crucial to ensure compliance with current regulations and to reflect any changes in business practices or technology. Statistics indicate that only a small fraction of healthcare organizations routinely assess their BAAs, which can lead to significant regulatory risks.
- Maintain Documentation: It is important to keep thorough records of all signed BAAs and any communications related to adherence, facilitating audits and oversight.
- Monitor Adherence: Organizations should regularly evaluate business associates’ compliance with the terms of the BAA, including conducting annual risk assessments and verifying adherence to security protocols.
Neglecting to establish a proper BAA can result in severe legal and financial repercussions, with penalties potentially reaching up to $1.5 million annually. The importance of BAAs extends beyond mere compliance; they are vital for effectively managing vendor relationships. Furthermore, entities are encouraged to ensure that their BAAs include critical components such as breach notification timelines, security requirements, and clauses for subcontractor adherence. Collaborating with a healthcare lawyer who is well-versed in privacy regulations is advisable to avoid pitfalls, such as relying on outdated templates or AI-generated agreements. This proactive approach not only protects patient privacy but also enhances the organization’s reputation and trustworthiness in managing sensitive information.
Comply with Key HIPAA Rules
Key HIPAA rules that must be complied with include:
- Privacy Rule: This rule safeguards the confidentiality of protected health information (PHI) and delineates patients’ rights regarding their health information. Understanding this rule is crucial for healthcare organizations to foster patient trust and ensure compliance.
- Security Rule: This rule establishes standards for the protection of electronic PHI (ePHI) through a combination of administrative, physical, and technical safeguards. Organizations are required to implement robust security measures to mitigate risks associated with data breaches, particularly as incidents of healthcare data breaches continue to escalate. In 2020, 19 cases of privacy law violations were settled with the Office for Civil Rights (OCR), underscoring the importance of compliance.
- Breach Notification Rule: This rule mandates that covered entities inform affected individuals and the Department of Health and Human Services (HHS) of breaches involving unsecured PHI. Awareness of this rule is vital, as studies reveal that a significant percentage of healthcare organizations remain unaware of their obligations. For example, the $2.4 million fine imposed on Memorial Hermann Health System for privacy rule violations highlights the serious consequences of non-compliance.
- Enforcement Rule: This rule outlines the procedures for investigations and penalties associated with HIPAA violations. Recent enforcement actions have underscored the increasing scrutiny of compliance, with penalties for violations becoming increasingly severe.
- Omnibus Rule: This rule broadens the responsibilities of business associates and enhances protections for patient privacy. Organizations must ensure that their Business Associate Agreements (BAAs) clearly articulate security responsibilities and breach reporting timelines to mitigate regulatory risks. Additionally, entities are required to conduct new risk evaluations utilizing current information streams to ensure compliance.
Staying informed about these key rules is essential for healthcare software developers and organizations to achieve HIPAA compliance for software development while effectively navigating the complex regulatory landscape.

Implement Secure Data Storage & Backup
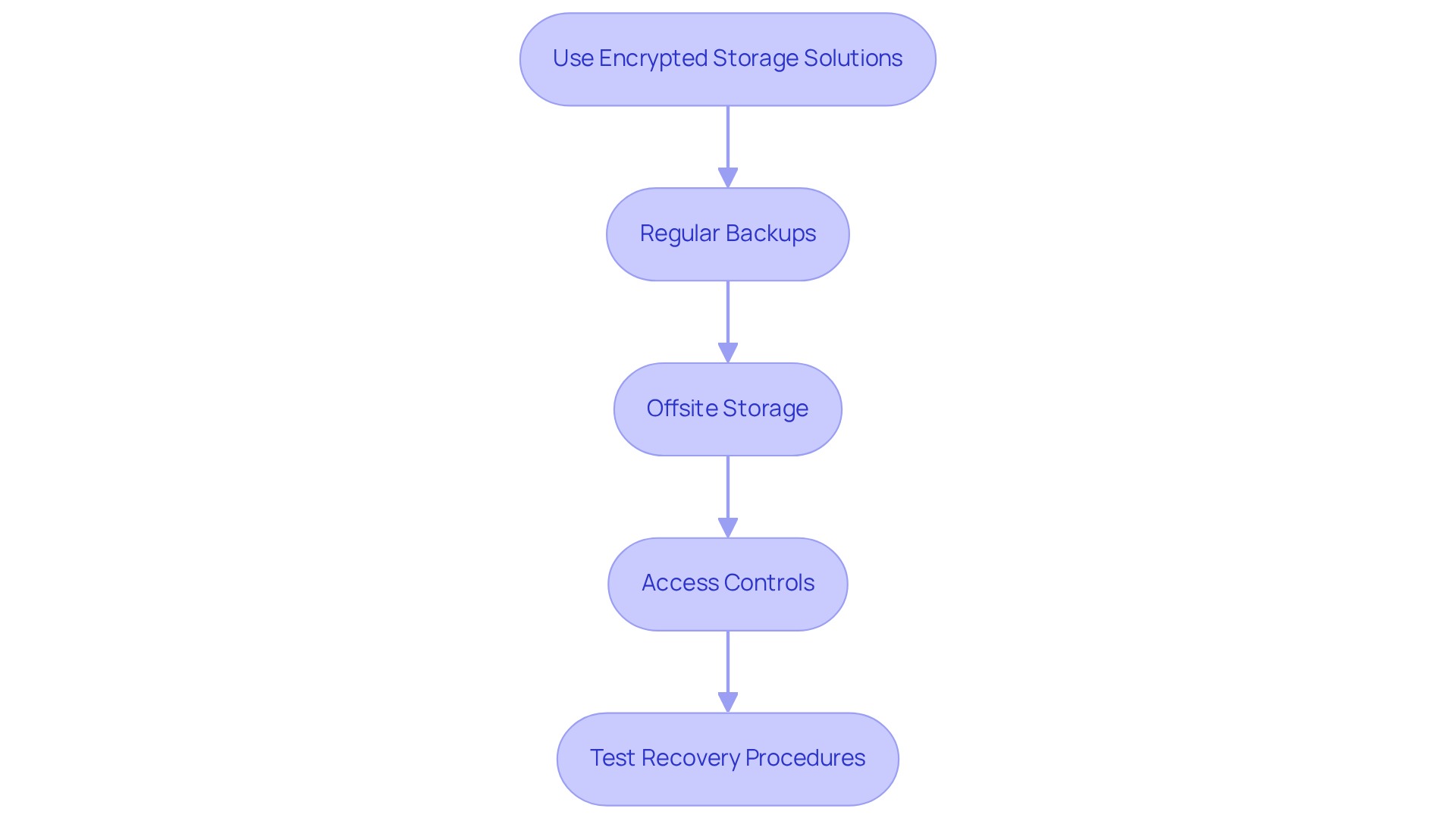
To implement secure data storage and backup practices, adhere to the following guidelines:
- Use Encrypted Storage Solutions: All protected health information (PHI) must be stored in encrypted formats. This is essential for safeguarding against unauthorized access and is a mandatory requirement under the upcoming HIPAA regulations, expected to take effect in July or August 2026.
- Regular Backups: Schedule frequent backups of all information containing PHI, ensuring these backups are also encrypted. This practice mitigates the risk of information loss and enhances recovery capabilities in the event of a breach or system failure.
- Offsite Storage: Backup copies should be stored in a secure offsite location to protect against physical disasters. Utilizing cloud solutions designed for healthcare can provide granular controls and ensure HIPAA compliance for software development.
- Access Controls: Implement strict access controls to limit storage system access to authorized personnel only. This includes role-based permissions and distinct user identifiers, which are vital for maintaining integrity and security.
- Test Recovery Procedures: Regularly test data recovery procedures to ensure that data can be restored quickly and effectively in case of loss. The 2026 updates require entities to demonstrate their capability to restore systems within a 72-hour period, making this testing essential for compliance.
Monitor and Audit Regularly
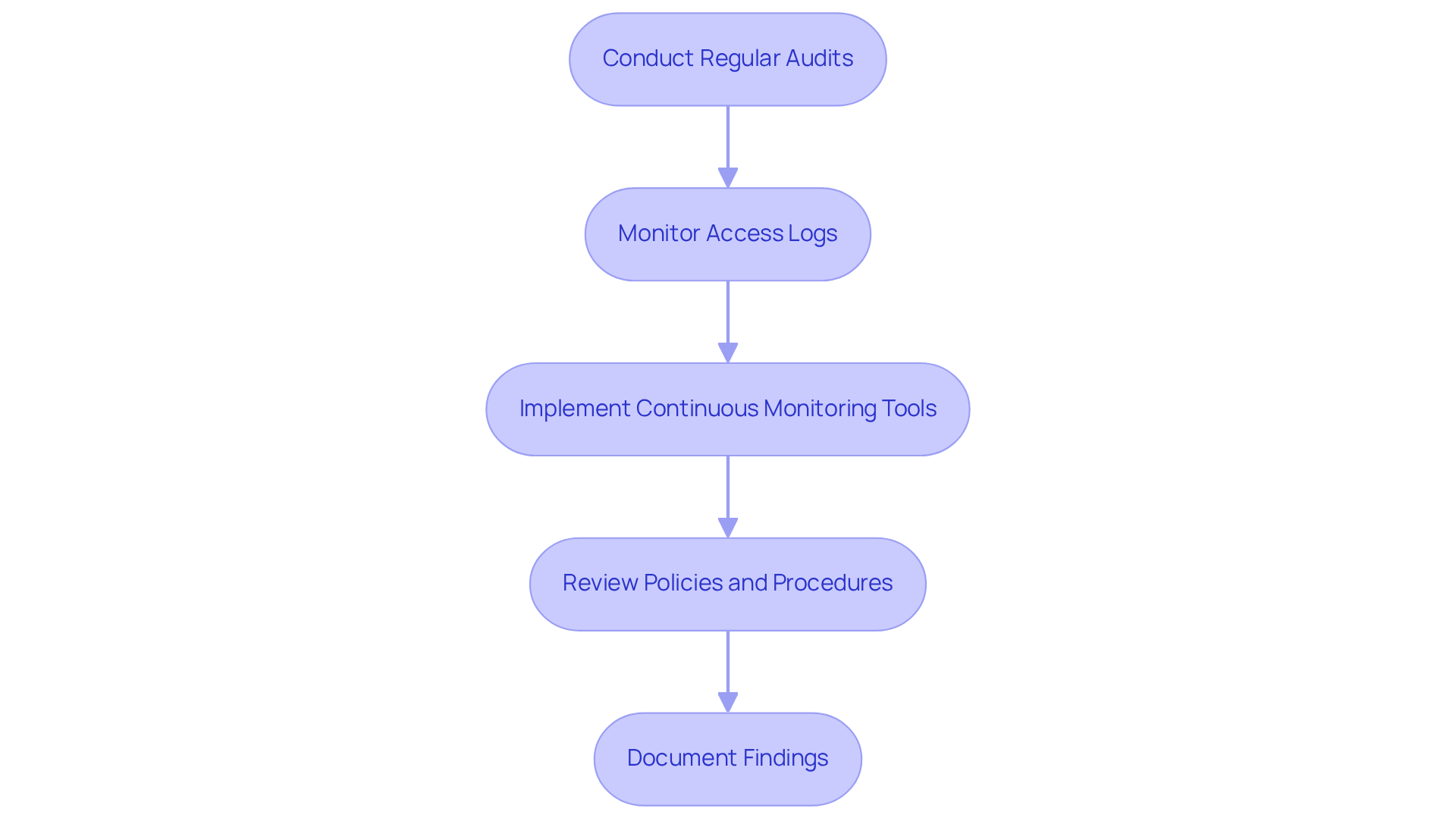
To ensure ongoing compliance with HIPAA regulations, organizations should adopt several key monitoring and auditing practices:
- Conduct Regular Audits: Organizations must schedule periodic audits to evaluate their systems and processes against HIPAA standards. Research indicates that many entities fail not due to a lack of controls, but because those controls do not withstand scrutiny during audits. This underscores the critical need for effective controls that can endure examination.
- Monitor Access Logs: It is essential to regularly review access logs to detect unauthorized access attempts or anomalies. This proactive approach aids in identifying potential security breaches before they escalate, thereby enhancing overall security posture.
- Implement Continuous Monitoring Tools: Utilizing automated tools for real-time monitoring of systems is vital for identifying security breaches or vulnerabilities. Continuous monitoring is particularly crucial in the healthcare sector, which has become a prime target for cyberattacks, especially ransomware. This proactive measure is essential for protecting patients and mitigating organizational risk.
- Review Policies and Procedures: Organizations should regularly update their adherence policies to reflect changes in regulations or business practices. This ensures that they maintain HIPAA compliance for software development while remaining compliant with evolving regulatory expectations, particularly with the forthcoming modifications to HIPAA rules in 2026.
- Document Findings: Maintaining comprehensive records of audits and monitoring activities is imperative. This documentation is essential for demonstrating adherence during audits and can significantly enhance a company’s operational resilience. As specialists emphasize, effective documentation is crucial for showcasing compliance and ensuring that entities can respond appropriately to audits.
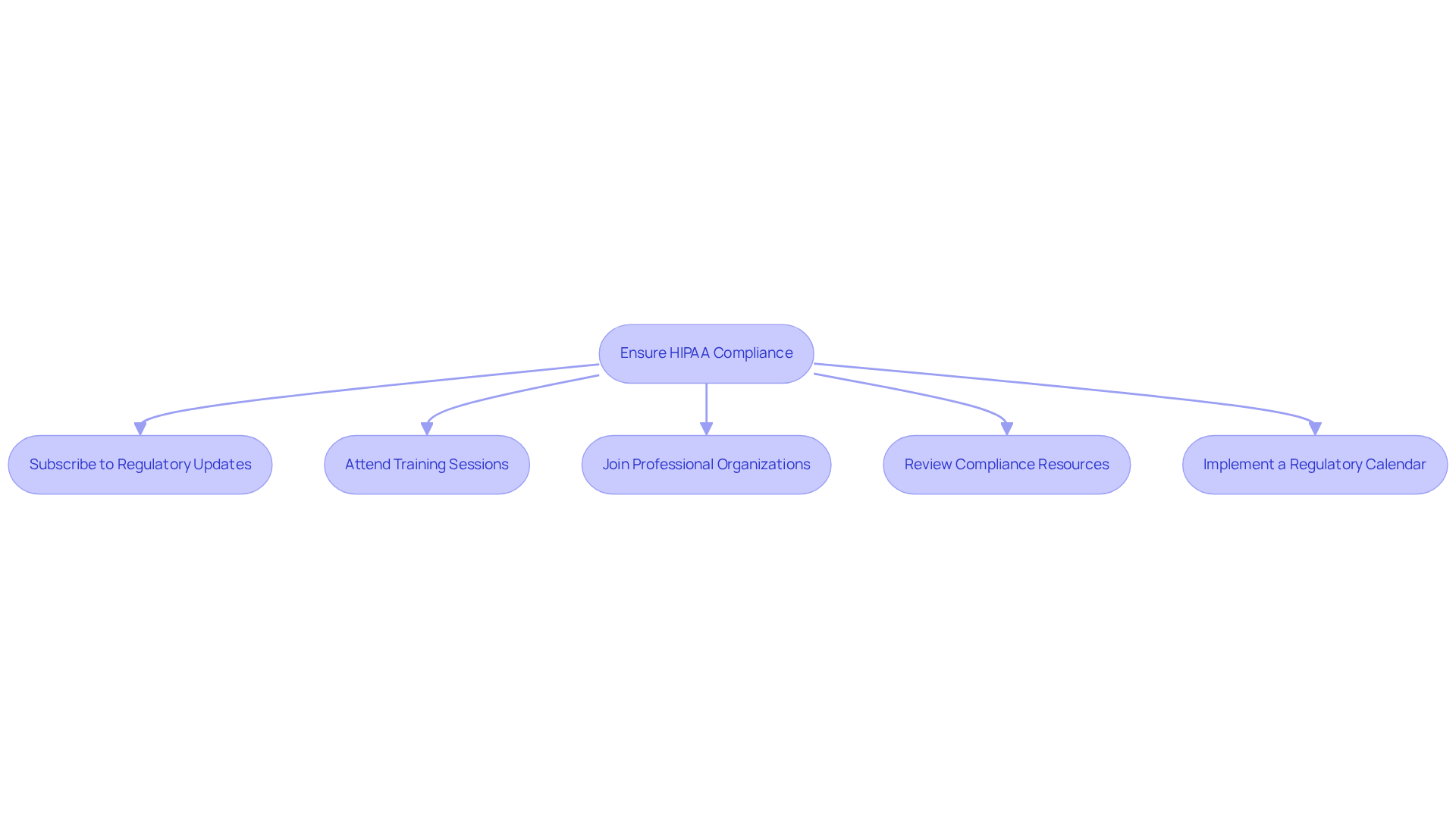
Stay Up to Date with Enforcement Guidelines
To ensure compliance with HIPAA enforcement guidelines, organizations should take the following steps:
- Subscribe to Regulatory Updates: Organizations should sign up for newsletters or notifications from the Department of Health and Human Services (HHS) to receive timely information on changes to privacy laws. Approximately 70% of healthcare organizations rely on such updates to maintain compliance, making this step essential.
- Attend Training Sessions: Regular participation in training sessions or webinars focused on health information privacy regulations and the latest updates is crucial. Continuous education enables software developers to grasp evolving requirements and implement necessary changes effectively, particularly in relation to HIPAA compliance for software development. As Jeremy Price, Managing Director, notes, “By clarifying requirements and removing ‘addressable’ flexibility, these changes shift health information privacy adherence from a checklist task to a proactive, measurable process.”
- Join Professional Organizations: Membership in professional groups that provide resources and updates on health information privacy regulations can be beneficial. These organizations often offer valuable insights and networking opportunities that enhance compliance efforts.
- Review Compliance Resources: Organizations should regularly consult reputable sources for updates on HIPAA enforcement actions and guidelines. Staying informed about recent developments allows organizations to adapt their practices accordingly. Utilizing tools such as regulatory management software can streamline this process.
- Implement a Regulatory Calendar: Establishing a regulatory calendar to monitor important deadlines and updates is advisable. This structured approach ensures that organizations remain vigilant and compliant with health privacy requirements, thereby minimizing the risk of violations. With significant changes to HIPAA compliance expected in 2026, maintaining an organized schedule is increasingly important.
Conclusion
Ensuring HIPAA compliance in software development is a complex process that necessitates a comprehensive understanding of Protected Health Information (PHI) and the implementation of various safeguards. Recognizing the significance of PHI and establishing robust administrative, physical, and technical measures enables organizations to effectively protect sensitive patient data and adhere to regulatory standards. These steps not only enhance compliance but also cultivate a culture of security within the organization.
Key strategies include:
- Conducting thorough risk assessments to identify vulnerabilities.
- Implementing administrative safeguards such as staff training and incident response plans.
- Enforcing stringent technical measures like encryption and access controls.
Furthermore, the importance of Business Associate Agreements (BAAs) is paramount, as they delineate the responsibilities of third-party vendors in safeguarding PHI. Regular audits and continuous monitoring are essential to ensure that organizations remain vigilant against potential breaches and adapt to evolving regulations.
With the impending changes to HIPAA regulations in 2026, it is imperative for healthcare organizations and software developers to prioritize compliance efforts. By adopting best practices and staying informed about enforcement guidelines, organizations can avoid substantial penalties while building trust with patients and stakeholders. Embracing these compliance measures is not merely a legal obligation; it represents a commitment to the ethical handling of sensitive health information, ultimately benefiting the entire healthcare ecosystem.
Frequently Asked Questions
What is Protected Health Information (PHI)?
Protected Health Information (PHI) refers to any individually identifiable health information that is transmitted or maintained in any form or medium. This includes names, addresses, birth dates, social security numbers, medical records, and any other information that can identify a patient.
Why is understanding PHI important for healthcare organizations?
Understanding PHI is critical for ensuring HIPAA compliance, as it defines the scope of data that must be protected. Many organizations struggle with these concepts, which can lead to regulatory risks and potential legal repercussions.
What steps should organizations take to identify and manage PHI?
Organizations should implement robust procedures to identify and manage PHI effectively, including conducting comprehensive risk assessments, ongoing staff training, and regular risk analysis.
What are the steps involved in conducting a comprehensive risk assessment?
The steps include identifying PHI, assessing vulnerabilities, evaluating current safeguards, documenting findings, and prioritizing risks based on their potential impact and likelihood.
What should organizations do to assess vulnerabilities in their PHI management?
Organizations should evaluate potential threats such as unauthorized access, data breaches, and system failures, and conduct regular vulnerability assessments to stay protected.
How can organizations ensure their current safeguards are effective?
Organizations should review existing security measures, including technical protections like encryption and access controls, to determine their effectiveness against evolving threats.
What are administrative safeguards in the context of PHI management?
Administrative safeguards are policies and procedures essential for managing the selection, development, and maintenance of security measures to protect PHI.
What key roles should be established for managing PHI compliance?
Organizations should assign a Privacy Officer to oversee adherence efforts and develop comprehensive training programs for all employees regarding HIPAA regulations and data protection practices.
What should incident response plans include?
Incident response plans should outline immediate actions, communication strategies, and recovery processes to address data breaches or security incidents.
Why are regular audits important for organizations handling PHI?
Regular audits help identify areas for enhancement in compliance practices, enabling organizations to stay ahead of regulatory changes and improve their security posture.
What is the significance of documenting policies related to PHI?
Clear, written policies that outline procedures for handling PHI ensure that all staff are aware of their responsibilities in safeguarding sensitive data.
What is multi-factor authentication, and why is it important?
Multi-factor authentication is a security measure that requires multiple forms of verification for systems accessing electronic Protected Health Information (ePHI). It is important for enhancing security in compliance with updated HIPAA regulations.
List of Sources
- Define Protected Health Information (PHI)
- Health Care Privacy Law Takeaways for a Compliant 2026: Pay Attention to Patient Concerns | Hall Render (https://hallrender.com/2026/03/18/health-care-privacy-law-takeaways-for-a-compliant-2026-pay-attention-to-patient-concerns)
- What is Protected Health Information? 2026 Update (https://hipaajournal.com/what-is-protected-health-information)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- HIPAA Compliance 2026: PHI Security & Patient Trust (https://cookie-script.com/privacy-laws/hipaa-guide-2026)
- 2026 Healthcare Privacy Regulations: What’s New and How to Stay Compliant (https://accountablehq.com/post/2026-healthcare-privacy-regulations-what-s-new-and-how-to-stay-compliant)
- Conduct a Comprehensive Risk Assessment
- 2026 HIPAA Compliance Guide: NPP Updates & Penalty Tiers (https://hellonote.com/2026-hipaa-compliance-guide-therapy-practices)
- January 2026 OCR Cybersecurity Newsletter (https://hhs.gov/hipaa/for-professionals/security/guidance/cybersecurity-newsletter-january-2026)
- HIPAA Risk Analysis Enforcement in 2026 (https://healthcarecompliancepros.com/hipaa-risk-analysis-enforcement-in-2026)
- Best HIPAA Compliance Software 2026: 25 Requirements Satisfied Before You Do Anything (https://patient-protect.com/post/best-hipaa-compliance-software-2026-25-requirements-satisfied-before-you-do-anything)
- HIPAA Risk Assessment – updated for 2026 (https://hipaajournal.com/hipaa-risk-assessment)
- Implement Administrative Safeguards
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- 2026 HIPAA Security Rule Update: New Requirements (https://medcurity.com/hipaa-security-rule-2026-update)
- 2026 Healthcare Privacy Regulations: What’s New and How to Stay Compliant (https://accountablehq.com/post/2026-healthcare-privacy-regulations-what-s-new-and-how-to-stay-compliant)
- 5 HIPAA Security Rule Changes in 2026 and How to Prepare | CBIZ (https://cbiz.com/insights/article/5-hipaa-security-rule-changes-in-2026-and-how-to-prepare)
- Apply Physical Safeguards
- HIPAA Security Rule Updates: What Healthcare Organizations Should Be Doing Now (https://deandorton.com/hipaa-security-rule-updates-what-healthcare-organizations-should-be-doing-now)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- HIPAA Security Rule Cybersecurity Changes (https://constangy.com/sp_resources-blogpost-hipaas-next-era-new-rules-for-new-technologies-and-risks)
- HIPAA Security Rule Notice of Proposed Rulemaking to Strengthen Cybersecurity for Electronic Protected Health Information (https://hhs.gov/hipaa/for-professionals/security/hipaa-security-rule-nprm/factsheet)
- HIPAA Compliance in 2026: Everything You Need to Know (https://venn.com/learn/hipaa-compliance)
- Enforce Technical Safeguards
- News | News Article – The 2026 HIPAA Security Rule Overhaul: What Healthcare Providers Should Know (https://cca.lbccc.org/NewsArticle.aspx?dbid2=PALBC&newsid=35399312)
- 2026 HIPAA Security Rule Update: New Requirements (https://medcurity.com/hipaa-security-rule-2026-update)
- 5 HIPAA Security Rule Changes in 2026 and How to Prepare | CBIZ (https://cbiz.com/insights/article/5-hipaa-security-rule-changes-in-2026-and-how-to-prepare)
- hipaavault.com (https://hipaavault.com/resources/2026-hipaa-changes)
- Enforce Strong User Authentication
- 3 Must Know Changes in the New HIPAA Security Rule NPRM (https://halock.com/3-must-know-changes-in-the-new-hipaa-security-rule-nprm)
- HIPAA 2026 MFA Changes (https://rhinogram.com/post/hipaa-2026-mfa-changes)
- HIPAA’s Changing MFA Requirements (https://txsystems.com/hipaa)
- How Identity Shapes The Next Phase Of Digital Care (https://forbes.com/councils/forbestechcouncil/2026/03/19/the-end-of-the-password-the-start-of-trust-how-identity-shapes-the-next-phase-of-digital-care)
- Sign Business Associate Agreements (BAAs)
- Why Business Associate Agreements Matter in HIPAA Compliance (https://flblaw.com/the-importance-of-business-associate-agreements-in-hipaa-compliance)
- The Complete Guide to Business Associate Agreements: What You Need to Know About BAA Compliance (https://dilitrust.com/business-associate-agreements)
- Preparing for the February 16, 2026 42 CFR Part 2 (SUD) Deadline (https://totalhipaa.com/preparing-for-the-february-16-2026-42-cfr-part-2-sud-deadline)
- 5 HIPAA Security Rule Changes in 2026 and How to Prepare | CBIZ (https://cbiz.com/insights/article/5-hipaa-security-rule-changes-in-2026-and-how-to-prepare)
- Update Business Associate Agreements to Comply with New Substance Use Disorder Record Rules (https://hollandhart.com/update-business-associate-agreements-to-comply-with-new-substance-use-disorder-record-rules)
- Comply with Key HIPAA Rules
- HIPAA Violation Cases – Updated 2026 (https://hipaajournal.com/hipaa-violation-cases)
- HIPAA UPDATES 2026: KEY REGULATORY CHANGES, NEW RULES, AND COMPLIANCE IMPACT EXPLAINED (https://certpro.com/hipaa-updates-2026-explained)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- Implement Secure Data Storage & Backup
- Getting ahead of the new HIPAA security rule: practical steps you can take now (https://healthcareitnews.com/blog/getting-ahead-new-hipaa-security-rule-practical-steps-you-can-take-now)
- 2026 HIPAA Security Rule: New Cloud Storage Requirements – Medical ITG (https://medicalitg.com/healthcare-it-services/2026-hipaa-security-rule-new-cloud-storage-requirements-7)
- The HIPAA Security Rule 2026: What Hospital CISOs Must Do in 240 Days (https://elisity.com/blog/hipaa-security-rule-2026-240-days)
- You Wont Believe How HIPAA and Cloud Storage Are Revolutionizing Healthcare Security! – Treasure Valley Movers (https://treasurevalleymoverz.com/news/you-wont-believe-how-hipaa-and-cloud-storage-are-revolutionizing-healthcare-security-7662726)
- 2026 HIPAA Cloud Storage Rules: New Encryption Requirements – Medical ITG (https://medicalitg.com/healthcare-it-services/2026-hipaa-cloud-storage-rules-new-encryption-requirements)
- Monitor and Audit Regularly
- The New Era of HIPAA: Why Audits Are Getting Stricter in 2026 (https://appliedinnovation.com/general/the-new-era-of-hipaa-why-audits-are-getting-stricter-in-2026)
- 5 HIPAA Security Rule Changes in 2026 and How to Prepare | CBIZ (https://cbiz.com/insights/article/5-hipaa-security-rule-changes-in-2026-and-how-to-prepare)
- HIPAA Security Rule 2026: New Gaps & Compliance Risks You Can’t Ignore (https://accorian.com/hipaa-security-rule-2026-this-is-going-to-expose-some-gaps)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- 3 Reasons to Invest in Healthcare Continuous Monitoring – Verisys (https://verisys.com/blog/reasons-to-invest-in-healthcare-continuous-monitoring)
- Stay Up to Date with Enforcement Guidelines
- 5 HIPAA Security Rule Changes in 2026 and How to Prepare | CBIZ (https://cbiz.com/insights/article/5-hipaa-security-rule-changes-in-2026-and-how-to-prepare)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- 2026 HIPAA Security Rule Update: New Requirements (https://medcurity.com/hipaa-security-rule-2026-update)
- Critical HIPAA Updates for 2026 (https://corsicatech.com/blog/hipaa-updates-security-rules)
