Introduction
Custom business application development presents a complex landscape where success depends on various factors, including regulatory compliance and user engagement. Organizations encounter the significant challenge of navigating evolving regulations while ensuring their applications fulfill unique business needs and meet user expectations. This article explores four best practices that can substantially improve the development process, providing insights into how to balance compliance, user involvement, and security-ultimately leading to more effective and resilient software solutions.
How can businesses successfully integrate these elements to excel in an increasingly competitive market?
Understand Regulatory Requirements and Industry Standards
When engaging in development, particularly in regulated industries, it is essential to have a thorough understanding of relevant regulations and industry standards. This includes familiarizing oneself with frameworks such as HIPAA, PCI DSS for payment processing, and GDPR.
To effectively integrate these regulations into your development process, consider the following steps:
- Conduct a compliance assessment: Identify the specific regulations applicable to your project based on the industry and geographical location. This assessment should be revisited regularly, as regulations can evolve.
- Engage stakeholders: Collaborate with legal and compliance professionals who can provide insights into the implications of these regulations on your software design and functionality. As noted by Melanie Fontes Rainer, OCR Director, understanding the complexities of compliance is crucial for effective software development.
- Document compliance: Maintain detailed records of how your software meets regulatory standards. This documentation can be invaluable during audits or compliance reviews.
By prioritizing regulatory understanding in the context of software development, you not only mitigate risks but also enhance the reliability of your system among users and stakeholders. Notably, 21% of C-Suite executives have identified compliance as their top strategic priority, underscoring its significance in organizational strategy. As the compliance landscape evolves, particularly with new regulations, staying informed will be key to successful application development.
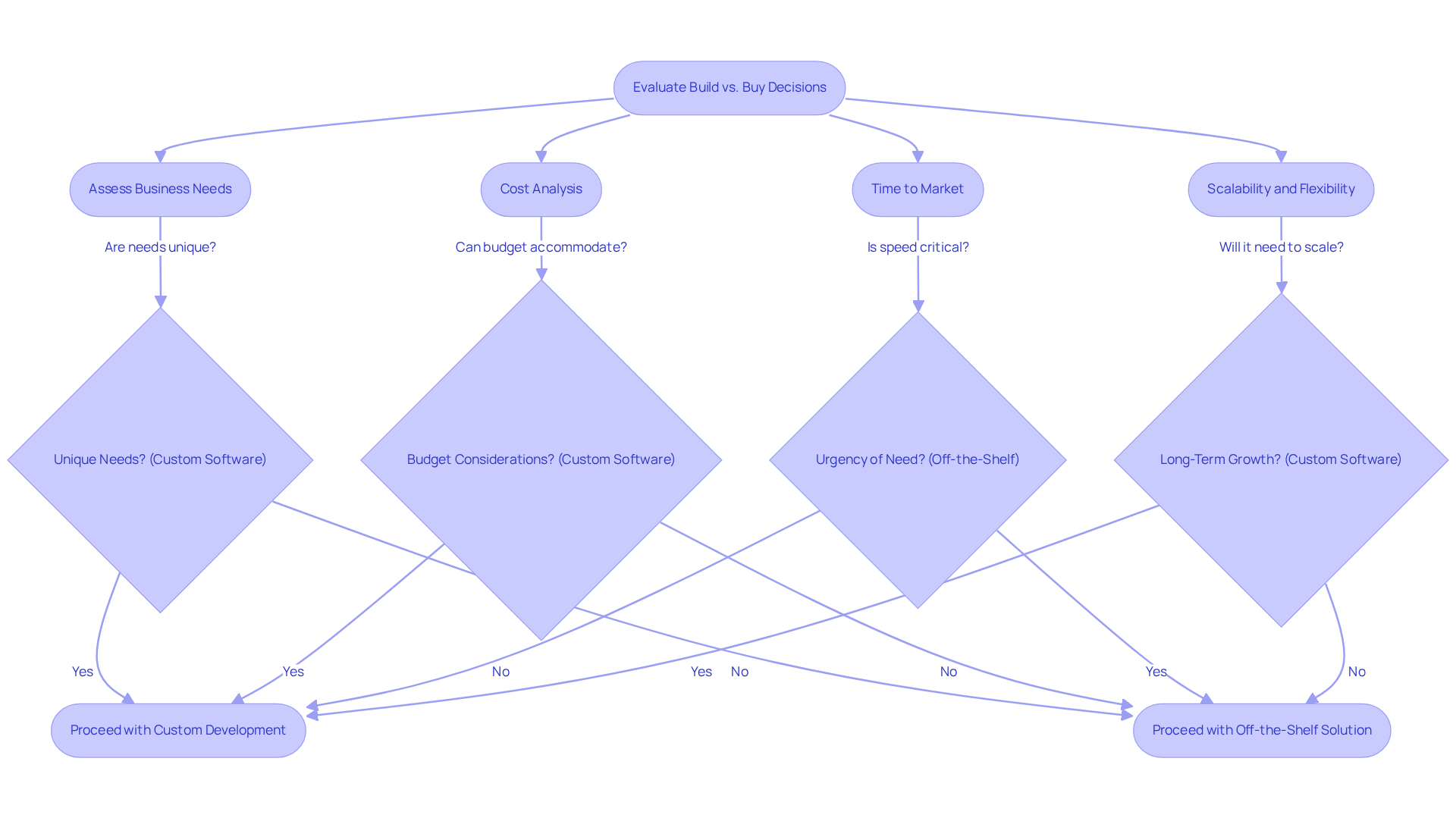
Evaluate Build vs. Buy Decisions for Custom Applications
Determining whether to create custom software or purchase a pre-existing solution is a decision that can significantly impact project success. Here are essential considerations to guide your decision:
- Clearly define your organization’s specific requirements. If your needs are unique and cannot be met by existing solutions, custom software may be the most effective choice. At Neutech, we prioritize understanding your specific requirements, allowing us to connect you with experts who can seamlessly integrate into your team.
- Conduct a comprehensive cost analysis. While custom software typically requires a larger investment in development and ongoing maintenance, purchasing a solution may involve licensing fees but can be implemented more quickly. Importantly, custom solutions can lead to a lower total cost of ownership over time, despite higher upfront costs.
- Evaluate how quickly you need the solution. Off-the-shelf products can generally be deployed within weeks or months, whereas custom builds may take several months or even years to complete, potentially delaying critical initiatives.
- Consider whether the solution can adapt as your business grows. Custom software can be tailored to evolve with your changing needs, while purchased solutions may have inherent limitations that could hinder future development.
By carefully weighing these factors, organizations can make informed decisions that align with their strategic objectives, ensuring that their software solutions effectively support their operational goals.
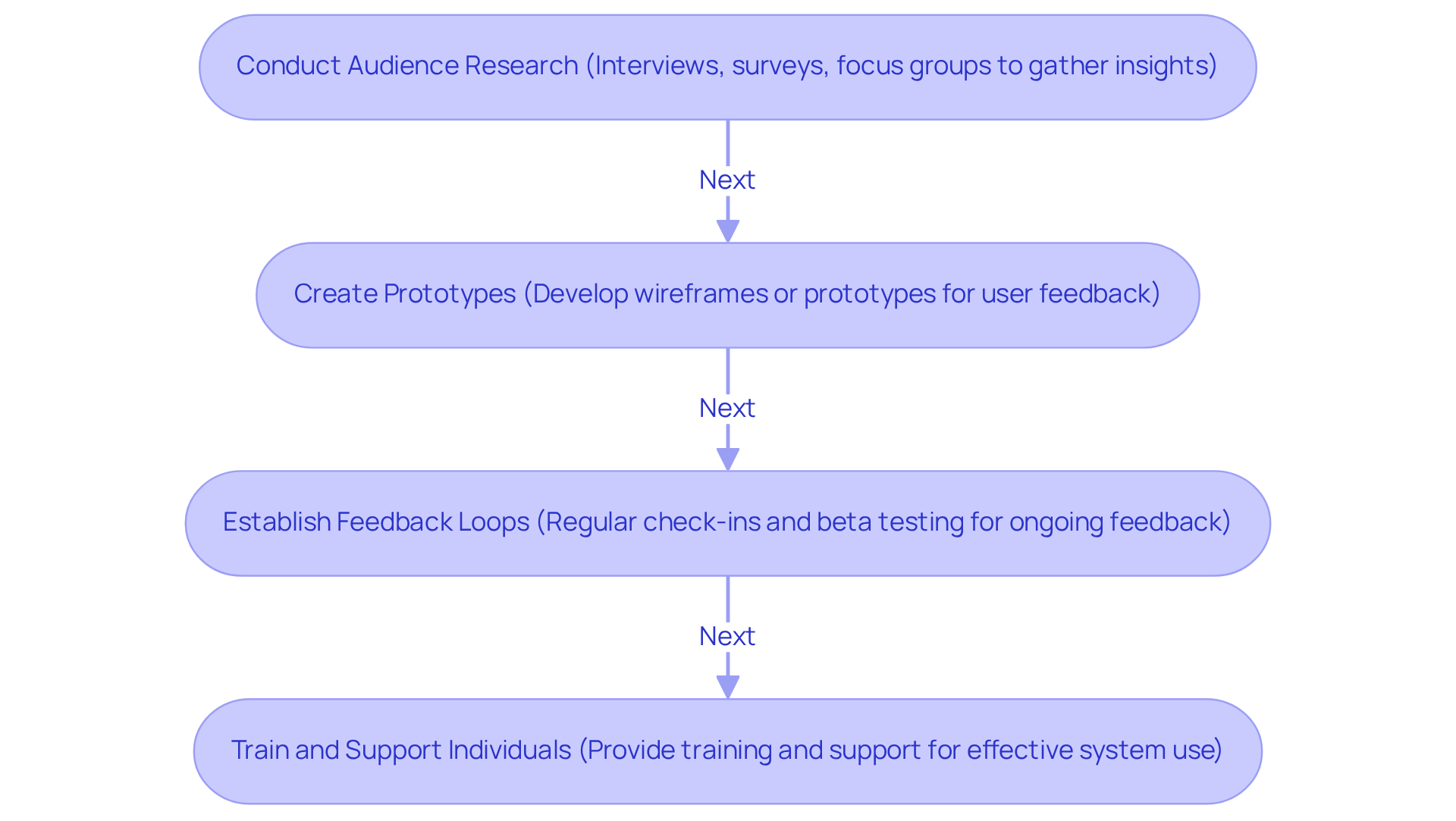
Involve End-Users in the Development Process
Involving end-users during the development process is crucial for creating applications that genuinely satisfy their requirements. To effectively engage users, consider the following strategies:
- Conduct Audience Research: Initiate the process with interviews, surveys, and focus groups to gather insights. This information should guide your design and functionality decisions. Notably, this feedback is essential, underscoring the importance of understanding customer expectations.
- Create Prototypes: Develop wireframes or prototypes early in the process and share them with users for feedback. This iterative approach allows for modifications based on actual participant input before large-scale implementation. A Job To Be Done (JTBD) analysis can reveal individual motivations, ensuring that prototypes align with user needs.
- Establish Feedback Channels: Set up mechanisms to gather ongoing feedback. This can be facilitated through beta testing or User Acceptance Testing (UAT). Consistent involvement fosters a collaborative environment that values participant feedback, which is essential for success.
- Provide Training: After the software is developed, offer training sessions to ensure users can effectively utilize the new system. Their success will reflect the tool’s effectiveness. As UX researchers emphasize, user involvement is key to achieving a positive outcome.
By prioritizing participant involvement, developers can enhance application quality to ensure the final product is aligned with the needs of their target audience. This approach significantly enhances software creation success rates, particularly in sectors where user satisfaction is paramount.
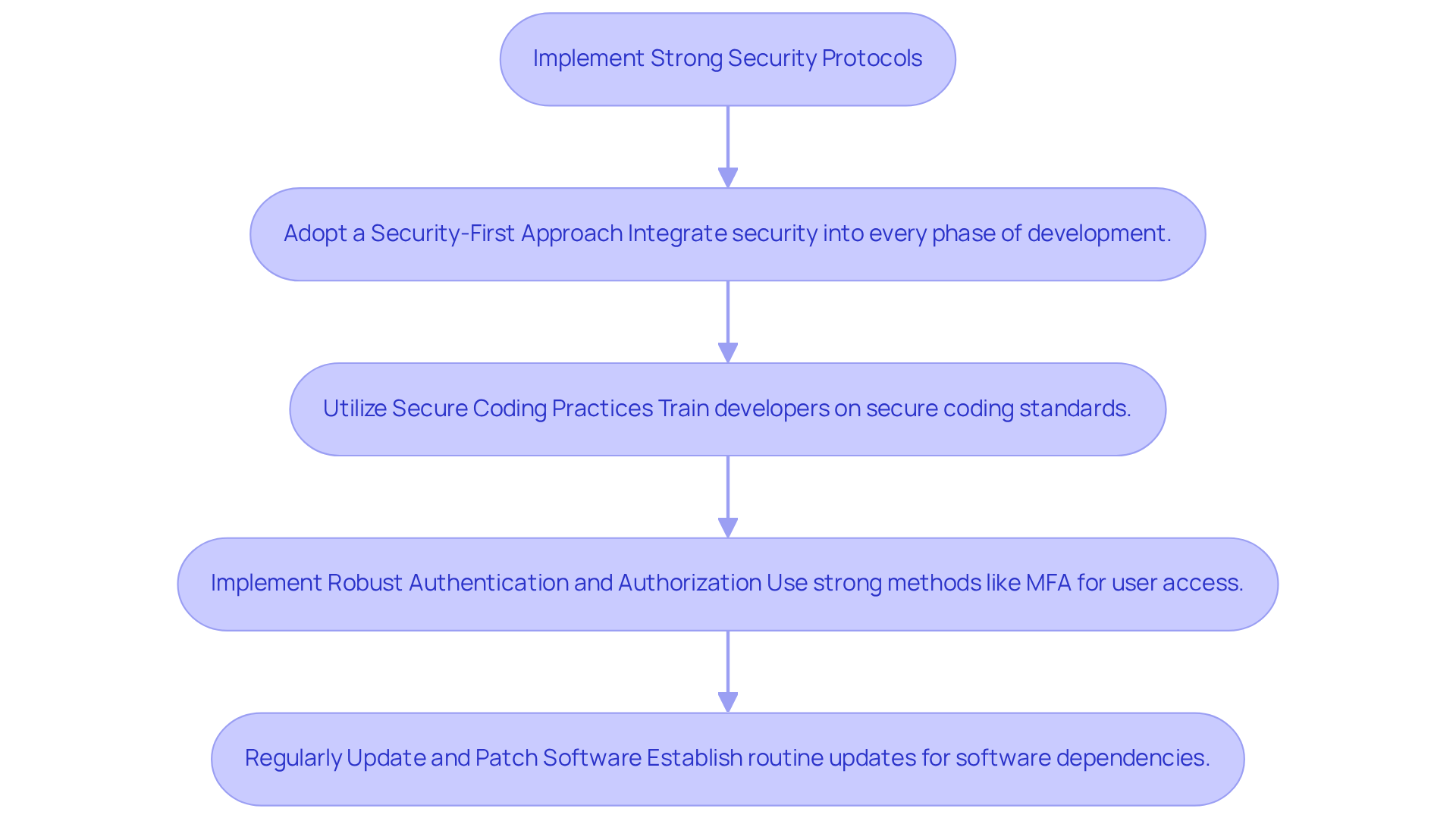
Implement Strong Security Protocols from the Start
Security must be a foundational element of any project. Implementing robust security measures from the outset is essential for safeguarding sensitive data and ensuring compliance with industry regulations. Here are key best practices to enhance security in your development process:
- Adopt a Security-First Approach: Integrate security considerations into every phase of the development lifecycle, from planning to deployment. This includes security reviews and risk assessments to identify potential vulnerabilities early on. Experts emphasize that a proactive security strategy can significantly reduce the risk of breaches, especially in the financial sector where the stakes are high.
- Utilize Secure Coding Practices: Equip your development team with training on secure coding standards to mitigate common vulnerabilities such as SQL injection and cross-site scripting (XSS). Research indicates that 83% of applications exhibit at least one security issue during their initial vulnerability assessment, underscoring the need for proactive measures. As cybersecurity professionals note, adopting secure coding practices is crucial for preventing costly breaches.
- Implement Strong Authentication: Employ strong authentication methods, including multi-factor authentication (MFA), to enhance security. Ensure that users have appropriate access levels based on their roles, as 61% of SaaS accounts have MFA disabled or inactive, creating significant security gaps. A case study involving a financial institution highlighted how the absence of MFA led to a major data breach, emphasizing the importance of robust authentication protocols.
- Maintain Regular Updates: Establish a routine for updating and applying security patches promptly. With the average time to detect a vulnerability exceeding 200 days, timely updates are crucial for addressing vulnerabilities before they can be exploited. Furthermore, experts predict a 25% rise in common vulnerabilities and exposures (CVEs) over the next year, making it imperative to stay ahead of potential threats.
By embedding security into the development process, organizations can significantly reduce the risk of breaches and enhance their overall security posture, ultimately leading to greater success in software development projects in 2026.
Conclusion
Custom business application development is a multifaceted process that demands careful consideration of various factors to ensure success. Organizations can create applications that not only meet their operational needs but also comply with industry standards and regulations by understanding regulatory requirements, evaluating build versus buy decisions, involving end-users, and implementing robust security protocols.
This article outlines four best practices essential for effective development:
- A comprehensive understanding of regulatory requirements ensures compliance and mitigates risks.
- Making informed decisions about whether to build custom applications or purchase existing solutions can significantly influence the project’s success.
- Involving end-users throughout the development process fosters collaboration and results in applications that genuinely address user needs.
- Embedding security measures from the outset protects sensitive data and enhances overall application integrity.
As the landscape of custom business application development continues to evolve, embracing these best practices is crucial. Organizations are encouraged to prioritize compliance, user involvement, and security to enhance their software solutions and position themselves for future challenges and opportunities in 2025 and beyond. By doing so, they can ensure that their applications are not only functional but also resilient, user-friendly, and aligned with strategic business goals.
Frequently Asked Questions
Why is it important to understand regulatory requirements in custom business application development?
Understanding regulatory requirements is crucial to ensure compliance with industry standards, mitigate risks, and enhance the reliability of the software among users and stakeholders.
What are some key regulations to be aware of in regulated industries?
Key regulations include GDPR for data protection, PCI DSS for payment processing, and HIPAA for healthcare purposes.
What is the first step to integrate regulations into the development process?
The first step is to conduct a regulatory assessment to identify the specific regulations applicable to the project based on the industry and geographical location.
Why should compliance experts be engaged during the development process?
Compliance experts provide insights into the implications of regulations on software design and functionality, which is essential for effective software development.
How should compliance efforts be documented?
Compliance efforts should be documented by maintaining detailed records of how the software meets regulatory standards, which can be valuable during audits or compliance reviews.
What percentage of C-Suite executives prioritize regulatory compliance?
21% of C-Suite executives have identified regulatory compliance as their top strategic priority.
Why is it important to stay informed about regulatory changes?
Staying informed about regulatory changes, especially with anticipated updates to regulations like GDPR in 2026, is key to successful application development and maintaining compliance.
List of Sources
- Understand Regulatory Requirements and Industry Standards
- New HIPAA Regulations in 2026 (https://hipaajournal.com/new-hipaa-regulations)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- HIPAA Updates and HIPAA Changes in 2026 (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- CNIL Publishes New Recommendations for AI System Development and GDPR Compliance – Pearl Cohen (https://pearlcohen.com/cnil-publishes-new-recommendations-for-ai-system-development-and-gdpr-compliance)
- Evaluate Build vs. Buy Decisions for Custom Applications
- Build vs. Buy Analysis: Which Is Right for You? (https://appdirect.com/blog/build-vs-buy-factors-to-consider-when-making-a-software-decision)
- Build vs. Buy: Navigating the Software Decision for Your Business (https://acceldata.io/blog/build-vs-buy-choosing-the-right-software-approach)
- Data Dashboards at State DOTs | GIS in Transportation | Planning, Environment & Realty | FHWA (https://gis.fhwa.dot.gov/case_studies/Data_Dashboards_at_State_DOTs.aspx)
- Build vs. Buy: 5 Things to Consider When You Need Software (https://progress.com/blogs/build-vs.-buy-5-things-to-consider-when-you-need-software)
- Involve End-Users in the Development Process
- Software Development Metrics That Matter in 2026 – Crossbridge Global Partners (https://gocrossbridge.com/blog/software-development-metrics)
- 2026 Customer Success Industry Market Statistics and Growth (https://custify.com/blog/customer-success-statistics)
- Software Development Statistics for 2026: Key Facts & Trends (https://itransition.com/software-development/statistics)
- Customer Success Metrics: What to Track in 2026 | Gainsight Software (https://gainsight.com/blog/customer-success-metrics-what-to-track-in-2026)
- Designing for healing: A case study on designing a user-focused mental health services app (https://medium.com/design-bootcamp/designing-for-healing-a-case-study-on-designing-a-user-focused-mental-health-services-app-68e4c390f34d)
- Implement Strong Security Protocols from the Start
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Top Cybersecurity Statistics for 2026 | Cobalt (https://cobalt.io/blog/top-cybersecurity-statistics-for-2026)
- 30 Cybersecurity Statistics You Must Know in 2026 | GitProtect.io (https://gitprotect.io/blog/cybersecurity-statistics-2026)
- 20+ Application Security Statistics & Trends in 2026 (https://aimultiple.com/application-security-statistics)
- Cybersecurity Facts and Stats as of 2026 (https://preveil.com/blog/cybersecurity-statistics)