Introduction
In an era where cyber threats are more pronounced than ever, the financial sector – especially hedge funds – stands at a pivotal crossroads. The demand for robust application security testing services has escalated, fueled by the imperative to safeguard sensitive data and comply with stringent regulations. This article explores ten essential application security testing services that hedge funds should consider to strengthen their defenses. As investment firms navigate an increasingly intricate cyber landscape, how can they effectively implement these testing strategies to mitigate risks and protect their operations?
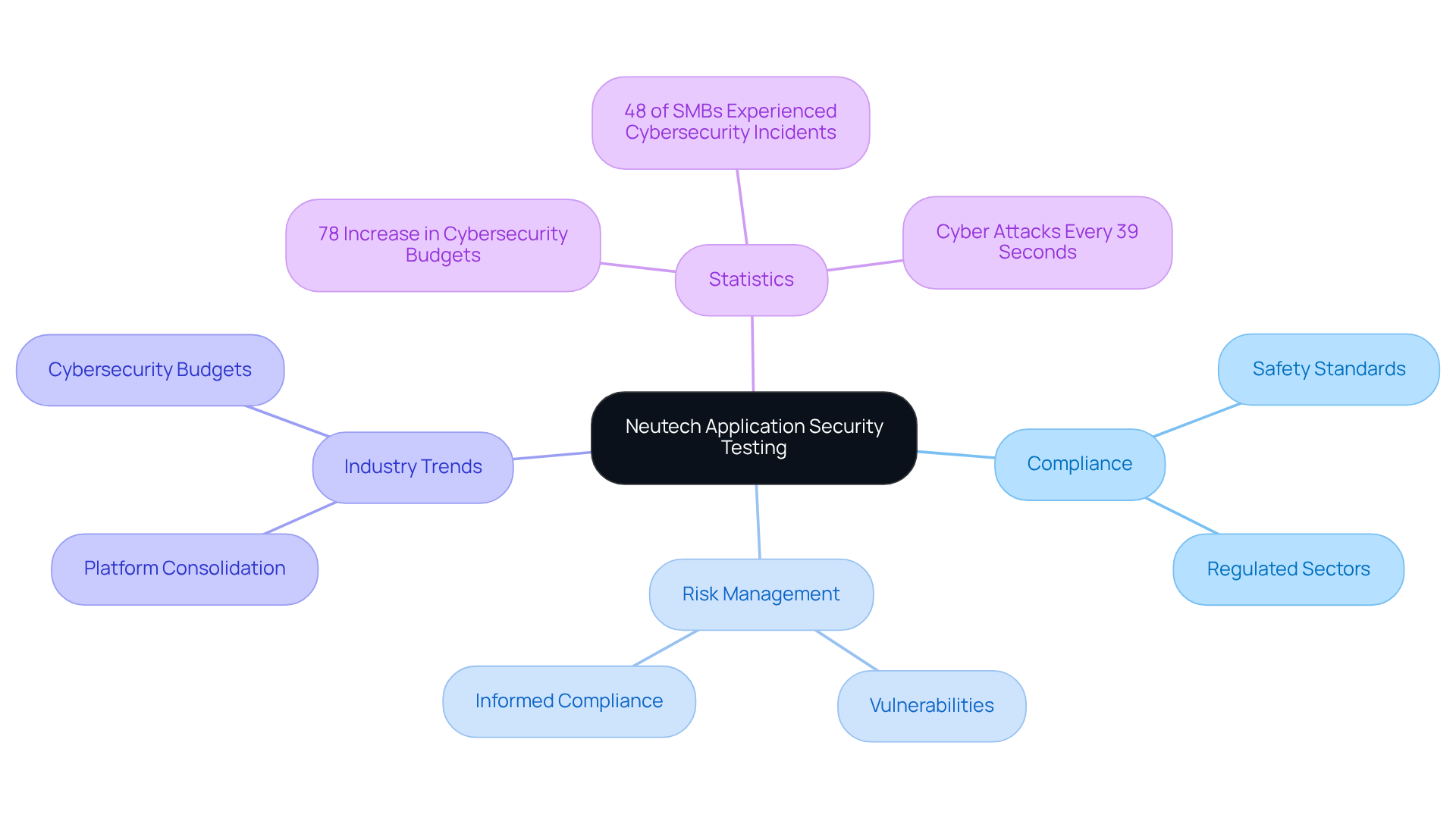
Neutech: Tailored Application Security Testing Services for Regulated Industries
tailored for regulated sectors, particularly . By prioritizing , Neutech ensures that . Their experienced team, equipped with extensive industry knowledge, delivers comprehensive that effectively tackle the unique challenges faced by investment groups.
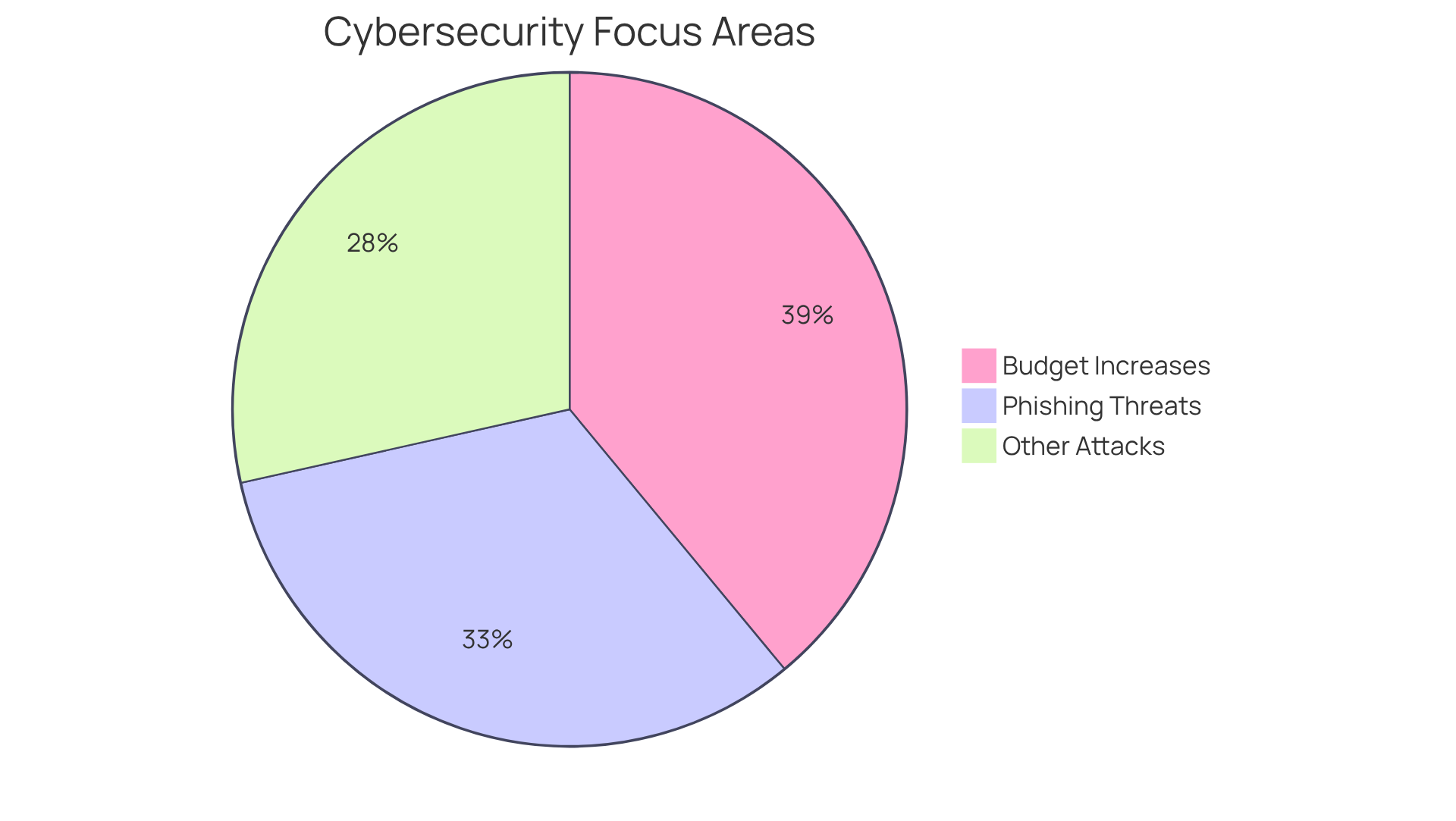
This proactive approach not only safeguards against vulnerabilities but also aligns with . For instance, the Gartner report highlights platform consolidation as a pivotal aspect of future software safeguarding. Furthermore, with over the past year, the demand for robust protective measures in today’s evolving market landscape is clear.
As Warren Buffett aptly noted, “,” underscoring the vital role of informed compliance and risk management in software security.
Static Application Security Testing (SAST): Proactive Code Vulnerability Detection
(SAST) is essential for identifying prior to program execution. This proactive strategy enables investment groups to detect , early in the . By incorporating SAST into their development workflows, can establish a robust , thereby significantly mitigating the risk of exploitation.
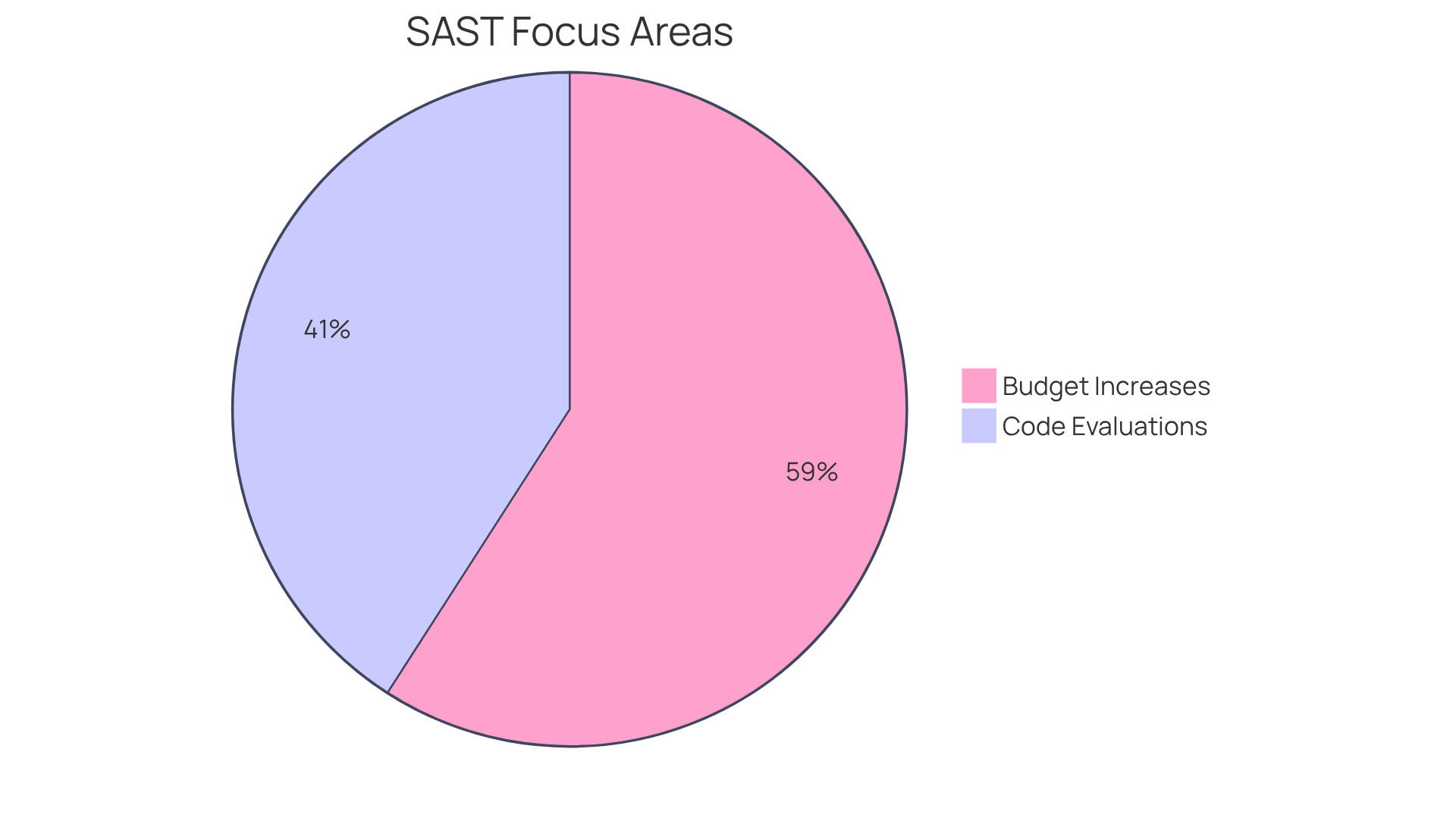
Recent trends indicate that organizations are placing greater emphasis on SAST as a component of their , with 54% of significant code changes undergoing thorough evaluations. This shift highlights the increasing acknowledgment of the necessity for , particularly in high-stakes environments like finance. Moreover, advancements in SAST tools have improved their efficacy, facilitating quicker identification and remediation of vulnerabilities, which is vital for maintaining compliance and operational integrity amid evolving threats.
Additionally, with over the past year, the focus on SAST reflects a broader commitment to enhancing protective measures. Hedge investment groups should prioritize the early integration of SAST in their development processes to effectively address various threats, including the prevalent risk of phishing.
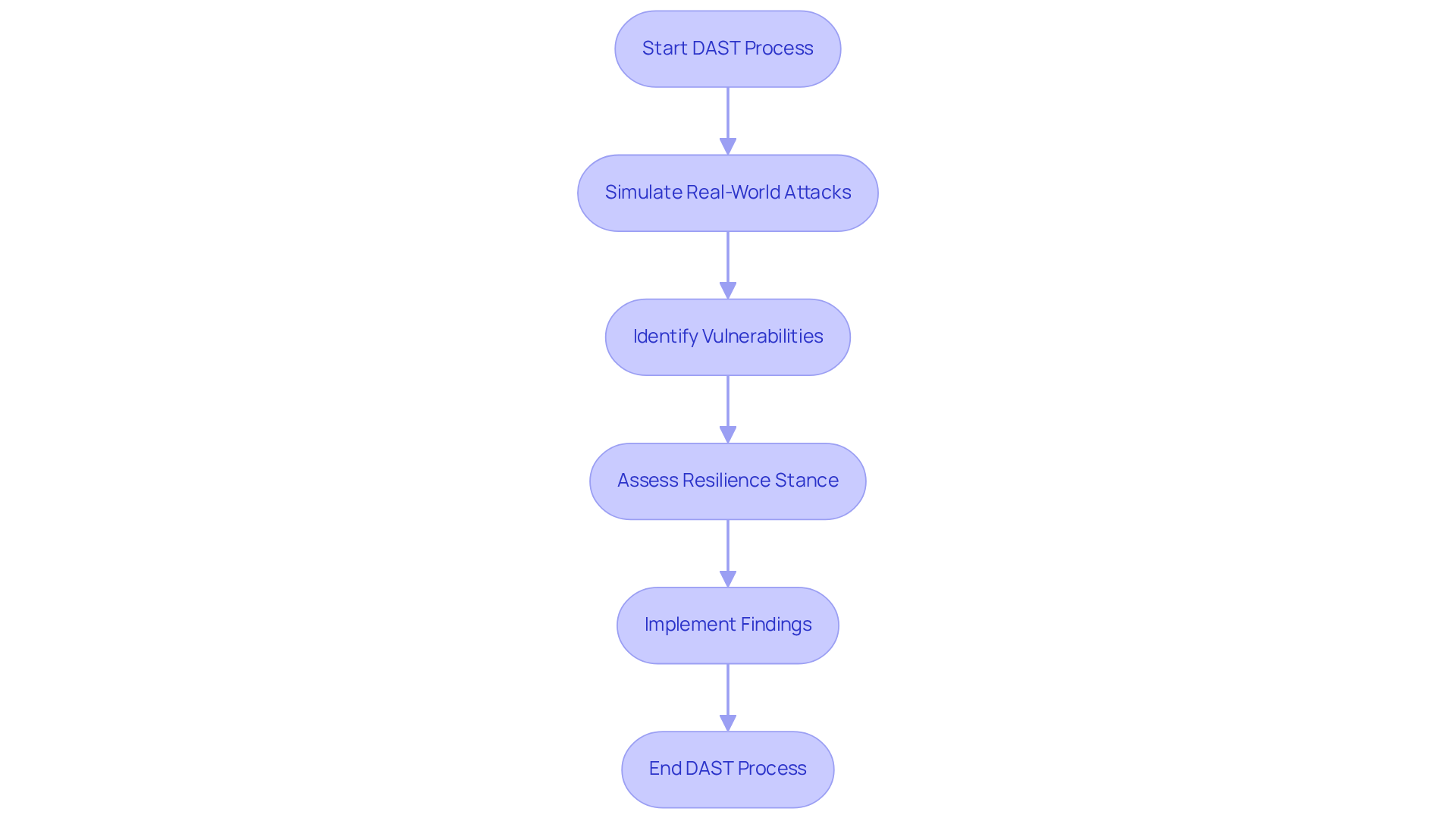
Dynamic Application Security Testing (DAST): Real-Time Vulnerability Assessment
serves as a proactive method that simulates real-world attacks on running systems. This enables organizations to identify vulnerabilities that could be exploited in real-time. For investment groups, this approach is particularly significant, as it allows them to assess the resilience stance of their applications under actual operating conditions. By implementing DAST, can uncover , thereby ensuring .
In 2026, the faces increasing threats, with 75 percent of protection experts reporting a rise in attacks over the past 12 months. Specialists, including Preeti Wadhwani, emphasize the that emerge during execution. Wadhwani states, “These tools are vital for that happen at runtime, following the development process, and can improve an organization’s defense posture.”
As the evolves, incorporating DAST into becomes essential for maintaining robust defenses against sophisticated cyberattacks.
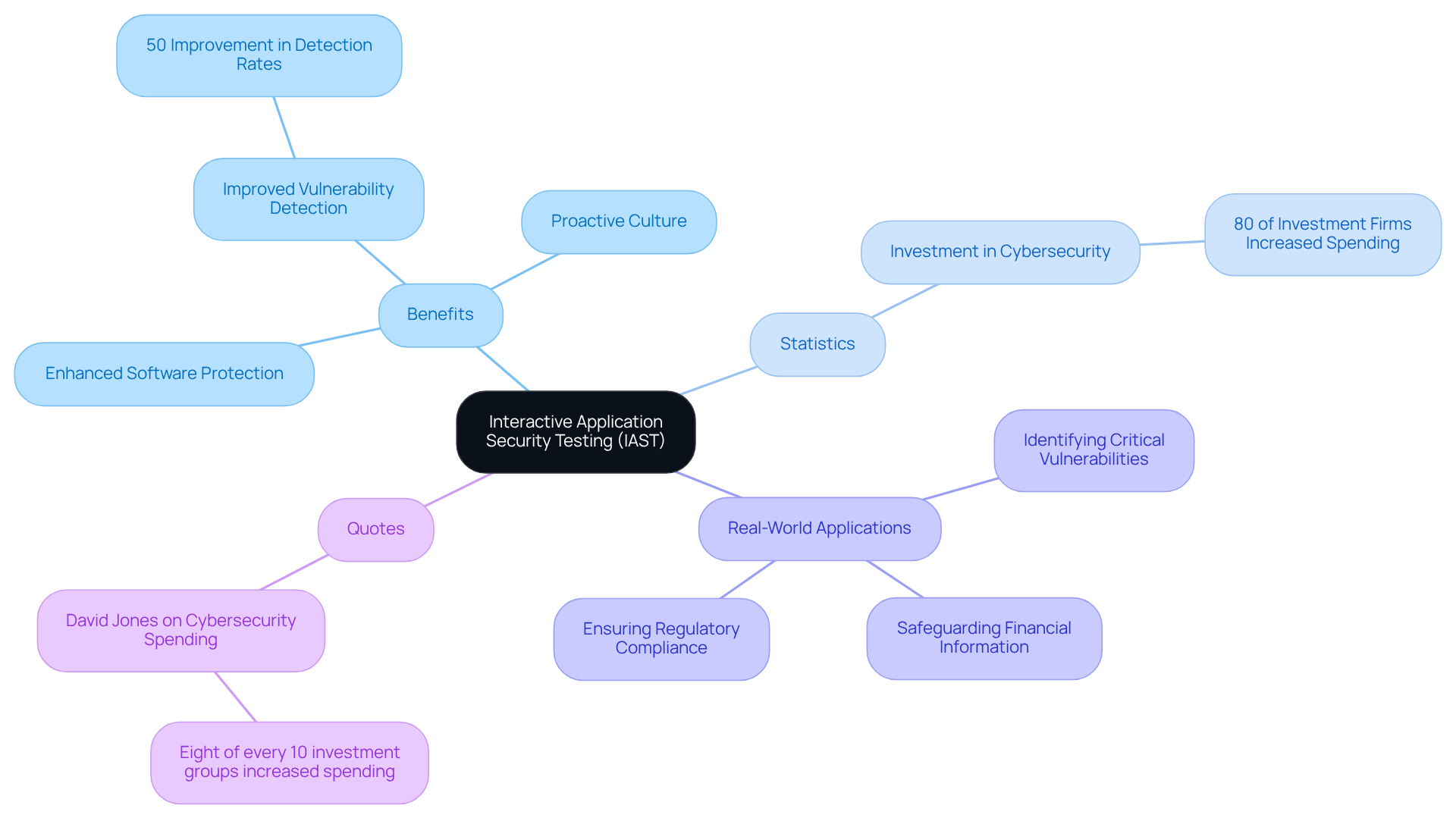
Interactive Application Security Testing (IAST): Combining Static and Dynamic Approaches
Interactive (IAST) effectively merges the strengths of static and dynamic testing methodologies by analyzing programs in real-time during execution. This dual approach provides immediate feedback to developers, allowing them to address vulnerabilities as they emerge. For , adopting IAST is particularly crucial, as it significantly enhances through continuous observation and assessment of both code and runtime behaviors.
Statistics reveal that IAST can improve by up to 50%, making it an essential tool for facing escalating cyber threats. Real-world applications of IAST within investment portfolios have demonstrated its ability to identify critical vulnerabilities before exploitation, thereby safeguarding sensitive financial information and ensuring compliance with .
The integration of IAST not only streamlines the testing process but also cultivates a within development teams, ensuring that security is a fundamental aspect of the . As highlighted by David Jones, “Eight of every 10 investment groups and other financial firms increased spending on in 2025,” this underscores the growing recognition of the need for robust security measures like IAST. Furthermore, with , the application of IAST in investment groups has never been more imperative.
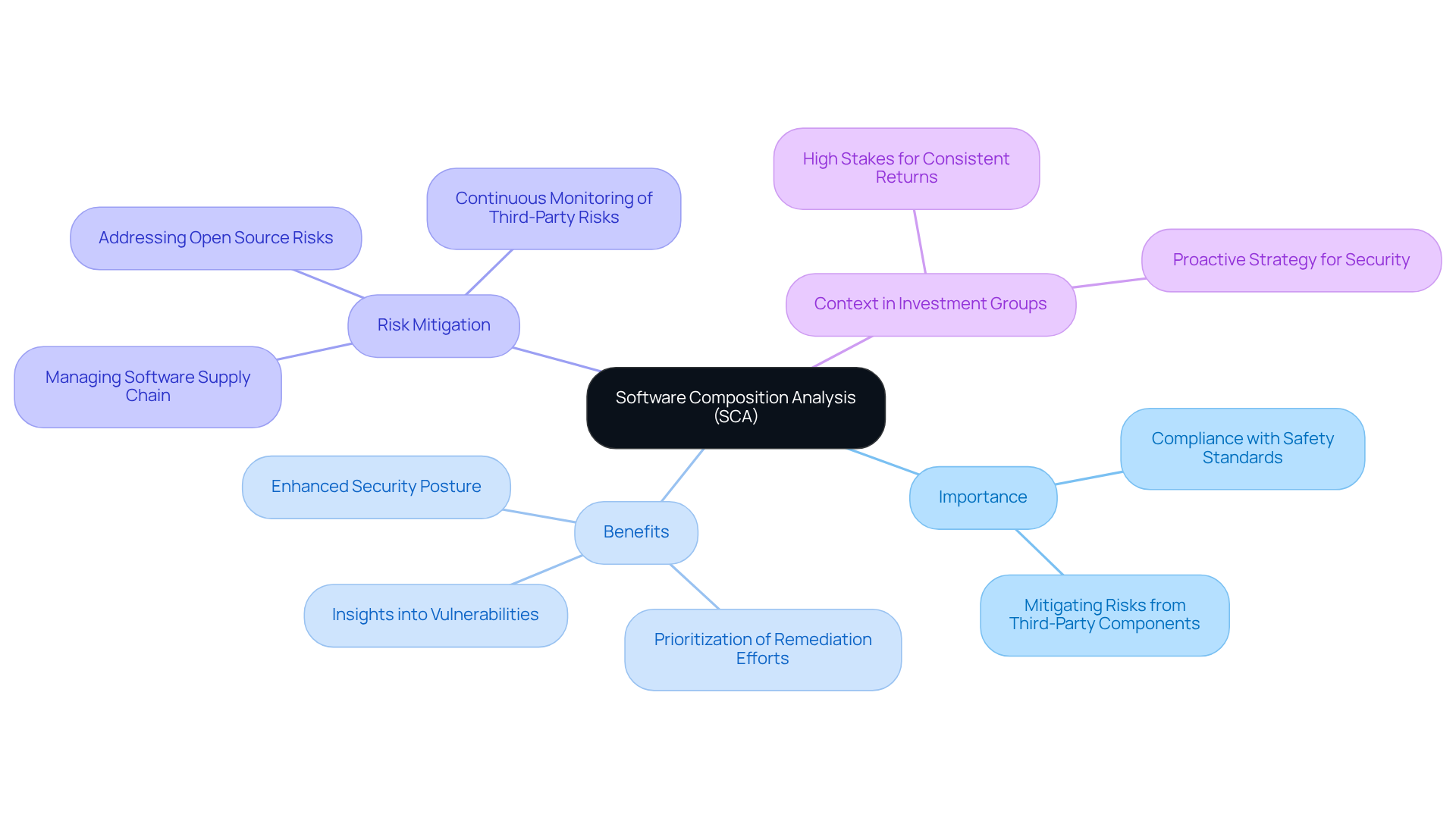
Software Composition Analysis (SCA): Securing Third-Party Components
plays a critical role in identifying and managing vulnerabilities within used in applications. For , SCA is not just a recommended practice; it is essential for maintaining and mitigating risks associated with external software. By implementing SCA, investment groups can effectively manage their , thereby significantly lowering the risk of that often arise from vulnerabilities in third-party components.
This proactive strategy is particularly vital considering that over 90% of modern applications incorporate some form of , which can harbor hidden risks if not adequately managed. Moreover, , including contextual information that assists in prioritizing remediation efforts. This capability is crucial for investment groups, where the stakes are high and the demand for consistent returns is relentless.
By leveraging SCA, investment groups can enhance their , ensuring that their systems remain resilient against .
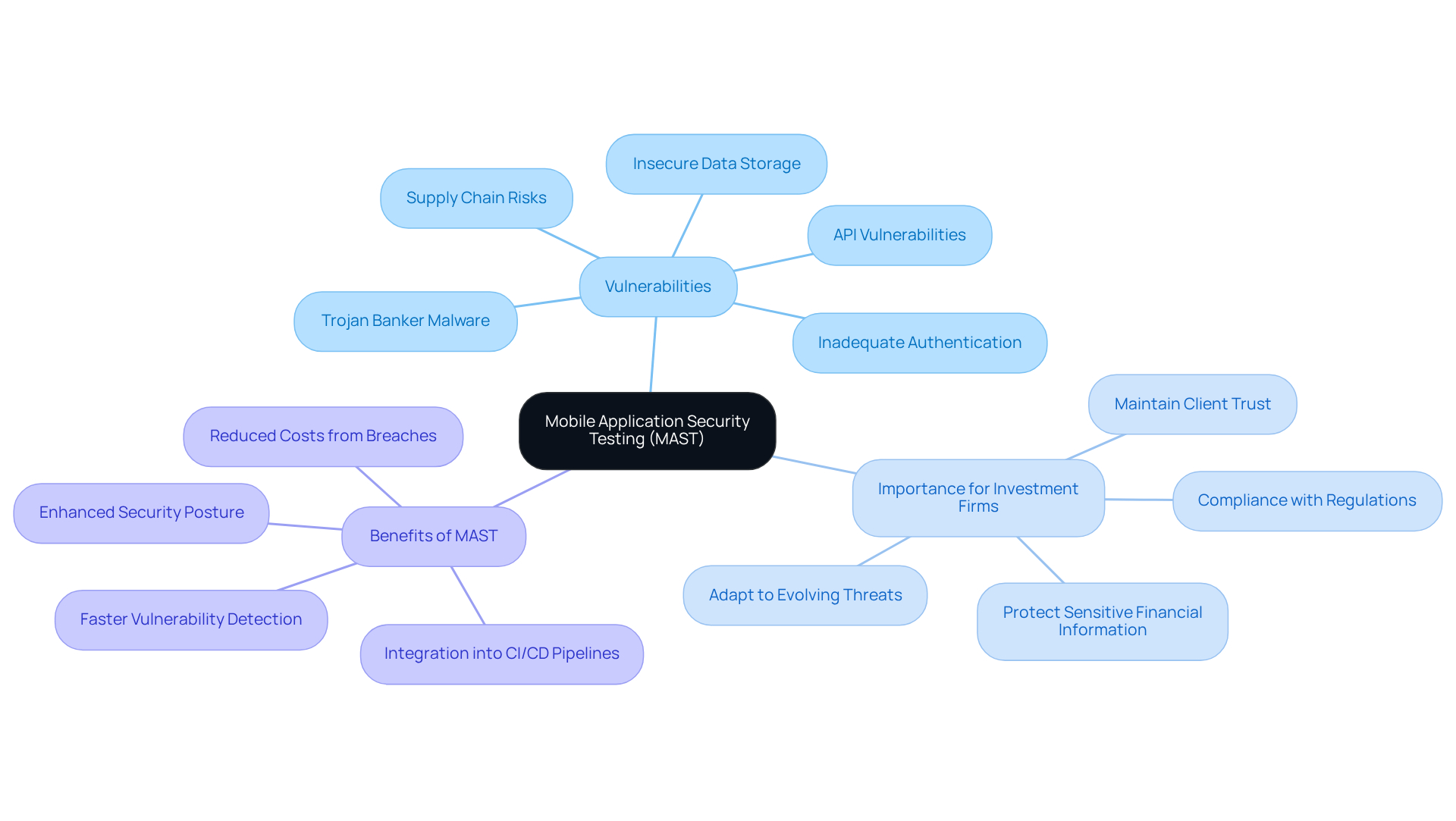
Mobile Application Security Testing (MAST): Safeguarding Mobile Applications
(MAST) plays a crucial role in identifying vulnerabilities that are specific to mobile software, including insecure data storage and . As investment groups increasingly rely on mobile platforms for transactions and data access, the implementation of MAST becomes essential for ensuring the security of these tools. By adopting MAST, can effectively protect and maintain the trust of their clients.
Manual Application Penetration Testing: Leveraging Human Expertise
Manual Application involves skilled experts who simulate real-world attacks to identify vulnerabilities within applications. This method is particularly effective for , as it allows for a of that automated tools may overlook. By employing manual testing, investment groups gain critical insights into their and can implement .

Runtime Application Self-Protection (RASP): Real-Time Application Defense
(RASP) represents a vital technology that integrates protective measures directly within applications, enabling them to detect and respond to threats in real-time. For investment groups facing increasing risks from – such as code injection and data breaches – RASP is essential for safeguarding their operations. Statistics reveal a rise in application-layer attacks, particularly within the sector, underscoring the urgent need for .
By adopting RASP, can maintain the integrity of their software even in the face of persistent threats. This technology not only identifies vulnerabilities but also mitigates them immediately, offering a proactive defense mechanism. Real-world implementations of RASP have demonstrated its effectiveness in enhancing , allowing firms to comply with stringent regulatory requirements while protecting sensitive financial data.
Moreover, as investment pools navigate an increasingly perilous cyber landscape, the adoption of RASP aligns with their strategic focus on resilience and risk management. With 78% of companies , integrating RASP into security protocols is becoming standard practice, ensuring that investment groups can operate securely and efficiently in a volatile market. Additionally, facing the sector, reported by 65% of respondents in the 2025 Survey, highlighting the specific risks that investment firms must address. This context reinforces the critical role of RASP in mitigating such threats and bolstering the overall cybersecurity posture.
API Security Testing: Protecting Application Interfaces
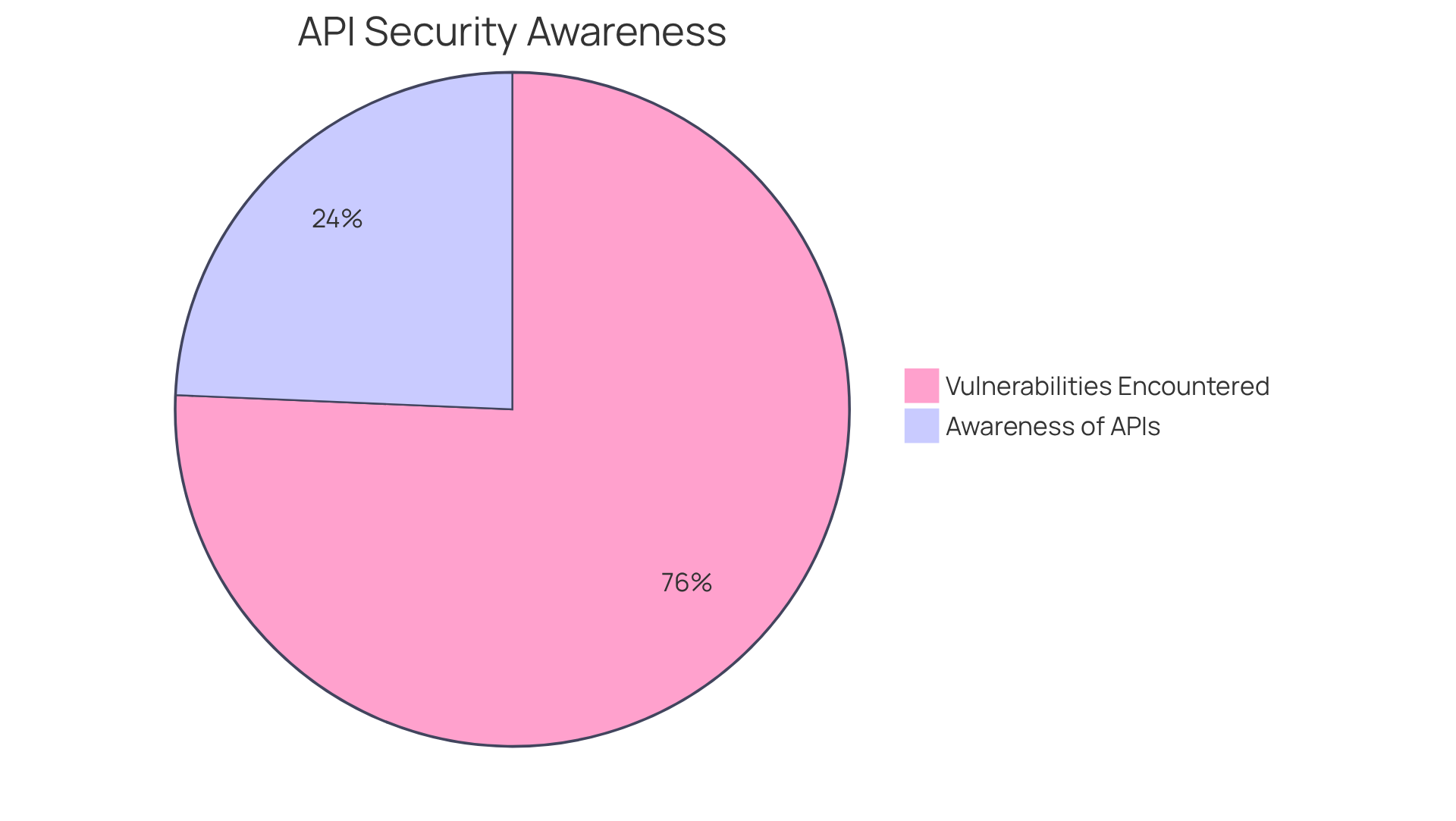
is essential for identifying vulnerabilities in application programming interfaces (APIs) that attackers may exploit. For , which often manage sensitive financial data, securing APIs is vital as they facilitate the exchange of information between different systems. A recent study revealed that in the previous year, underscoring the necessity for investment groups to prioritize API protective measures. Furthermore, the percentage of participants aware of which APIs share sensitive data decreased from 40% in 2023 to 27% in 2024, highlighting a growing knowledge gap that must address.
Conducting thorough assessments enables investment firms to safeguard their applications from unauthorized access and maintain the integrity of data exchanges. This is particularly crucial given that the in the sector reached approximately $832,801. By proactively addressing these vulnerabilities, investment firms can mitigate risks associated with high market volatility and regulatory compliance pressures. The primary focus for (CISOs) over the next 12 months includes securing APIs, which is a critical area for hedge funds navigating the competitive landscape.
Real-world examples illustrate the effectiveness of robust API protection measures. Organizations that have enhanced their API protection protocols have reported significant reductions in unauthorized access incidents. As Rupesh Chokshi, Senior Vice President and General Manager of Application Protection, noted, “Our research indicates that API protection has not yet become a key component in a comprehensive safety strategy.” As the financial environment evolves, investment pools must remain vigilant, ensuring that their API protection strategies are not only reactive but also proactive, adapting to new threats and maintaining compliance with industry regulations.
Continuous Testing and Integration: Embedding Security in the SDLC
Incorporating (SDLC) is essential for investment firms. This approach facilitates the throughout the development process. By adopting such proactive measures, firms not only enhance their but also ensure compliance with stringent industry regulations.
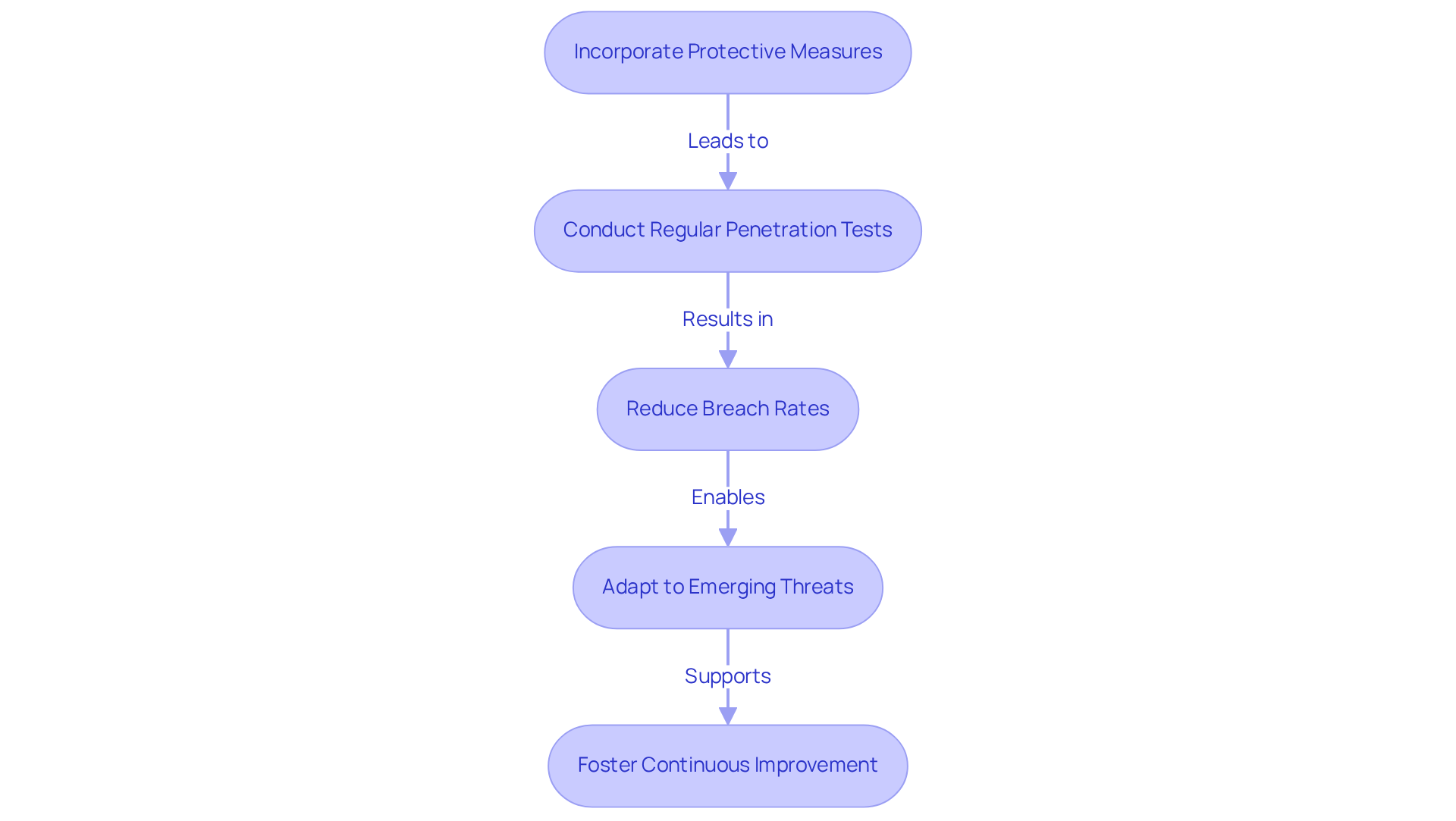
For example, organizations are at the forefront of , with over 70% conducting regular tests to bolster their , often as mandated by compliance standards. By integrating protection into the SDLC, investment firms can significantly reduce the . Organizations that perform quarterly penetration tests experience breach rates that are 53% lower than those that test less frequently. Alarmingly, 68% of organizations that suffered breaches had not conducted a penetration test in the year preceding their incidents, highlighting the dangers of infrequent testing.
Transitioning to ongoing protection verification allows investment firms to swiftly adapt to emerging threats, ensuring that their applications remain resilient against evolving cyber risks. This continuous assessment is vital in a landscape where 80% of senior IT leaders perceive their organizations as underprepared for cyberattacks. Furthermore, 92% of U.S. and European organizations increased their overall last year, reflecting a growing recognition of the need for enhanced protective measures.
Ultimately, not only safeguards sensitive financial data but also fosters a , aligning with the strategic objectives of hedge funds. As Mohammed Khalil, a cybersecurity architect at DeepStrike, observes, “The trajectory is toward continuous security validation, a state where at any given moment, an organization has recently tested its key assets for weaknesses.
Conclusion
The landscape of application security testing for hedge funds has become increasingly complex, necessitating a tailored approach to safeguard sensitive financial data against evolving threats. By leveraging a combination of methodologies, including:
- Static Application Security Testing (SAST)
- Dynamic Application Security Testing (DAST)
- Interactive Application Security Testing (IAST)
investment firms can establish a robust defense framework. This framework not only identifies vulnerabilities but also mitigates risks in real-time, which is essential for ensuring compliance with stringent regulations and maintaining client trust.
Key insights from the article underscore the importance of proactive measures in application security. The integration of:
- Software Composition Analysis (SCA)
- Mobile Application Security Testing (MAST)
is crucial for securing third-party components and mobile platforms, respectively. Additionally, the adoption of manual penetration testing and Runtime Application Self-Protection (RASP) enhances the overall security posture by providing thorough analysis and real-time defense capabilities. Continuous testing and integration within the software development lifecycle (SDLC) further ensure that vulnerabilities are addressed promptly, thereby reducing the risk of breaches.
Investment firms must acknowledge the critical nature of these application security testing services in navigating the current cyber landscape. As threats continue to escalate, adopting a comprehensive and proactive security strategy is not merely advisable; it is essential for safeguarding sensitive information and ensuring operational integrity. By prioritizing these essential services, hedge funds can protect their assets while fostering a culture of security that aligns with their long-term strategic objectives.
Frequently Asked Questions
What services does Neutech provide?
Neutech specializes in tailored application security testing services for regulated industries, particularly investment firms, focusing on compliance and risk management to ensure financial software meets stringent safety standards.
Why is compliance and risk management important for software security?
Compliance and risk management are vital for software security as they help safeguard against vulnerabilities and align with emerging trends in software protection, ultimately ensuring that organizations are informed and prepared against potential risks.
What is Static Application Security Testing (SAST)?
Static Application Security Testing (SAST) is a proactive strategy that identifies vulnerabilities within source code before program execution, allowing investment groups to detect critical issues early in the development lifecycle.
How does SAST benefit hedge funds?
By incorporating SAST into their development workflows, hedge funds can establish a strong protective foundation for their applications, significantly mitigating the risk of exploitation and enhancing compliance with security standards.
What recent trends are influencing the use of SAST?
Recent trends show that organizations are increasingly emphasizing SAST in their cybersecurity strategies, with 54% of significant code changes undergoing thorough evaluations, reflecting a commitment to secure coding practices.
What is Dynamic Application Security Testing (DAST)?
Dynamic Application Security Testing (DAST) is a method that simulates real-world attacks on running systems, allowing organizations to identify vulnerabilities that could be exploited in real-time.
Why is DAST important for investment groups?
DAST is important for investment groups as it helps assess the resilience of applications under actual operating conditions and uncovers vulnerabilities that static testing might miss, ensuring comprehensive protection.
What are the current threats facing the financial sector?
The financial sector is facing increasing threats, with 75% of protection experts reporting a rise in attacks over the past 12 months, highlighting the need for effective security measures like DAST.
How can investment groups improve their defense posture against cyberattacks?
Investment groups can improve their defense posture by implementing DAST technology to identify weaknesses that emerge during execution, thereby enhancing their overall cybersecurity strategy.
