Introduction
Navigating the landscape of HIPAA compliance is crucial for any organization that handles protected health information (PHI). The stakes are higher than ever, with potential fines and loss of funding looming over non-compliance. Therefore, understanding the essential steps to achieve compliance is paramount. This article outlines ten critical actions organizations can take to meet the stringent requirements of HIPAA while simultaneously enhancing their overall data security. As regulations continue to evolve, organizations must consider how to effectively adapt their compliance strategies to mitigate risks and safeguard sensitive information.
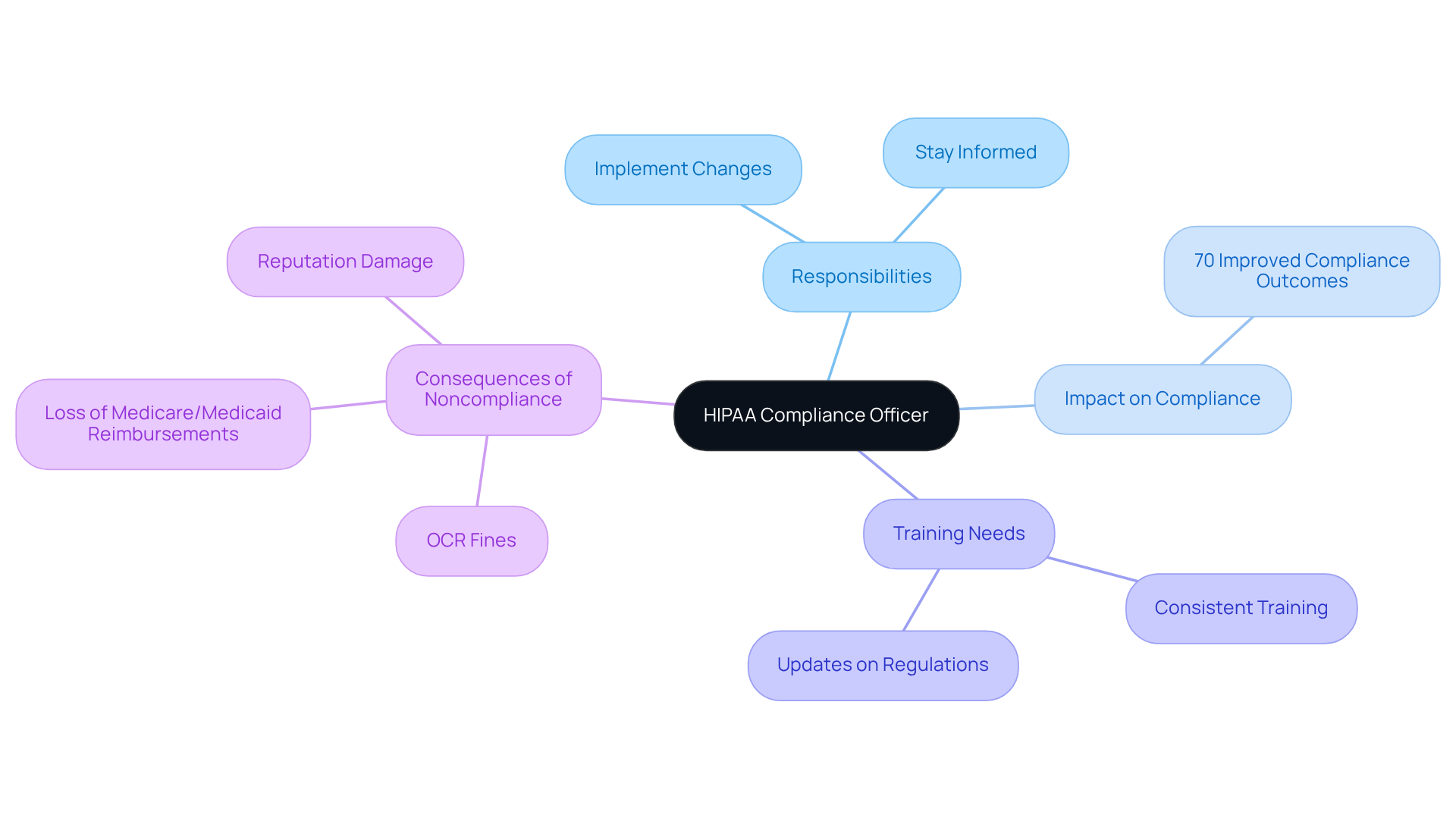
Neutech: Designate a HIPAA Compliance Officer
Appointing a dedicated is essential for ensuring adherence to all privacy regulations within your organization. This individual must have a thorough understanding of and be empowered to implement necessary changes effectively. Consistent training and updates on evolving are crucial for this officer, enabling them to stay informed about legal modifications and adherence expectations.
Research indicates that approximately 70% of organizations with experience significantly improved compliance outcomes, particularly in regulated sectors such as healthcare and . As the landscape of evolves in 2026, the role of the will become increasingly critical in , including the necessity for expedited breach notifications and comprehensive .
Noncompliance with these regulations can lead to severe repercussions, such as Office for Civil Rights (OCR) fines and the loss of Medicare and Medicaid reimbursements. This underscores the vital importance of the ‘s role in .
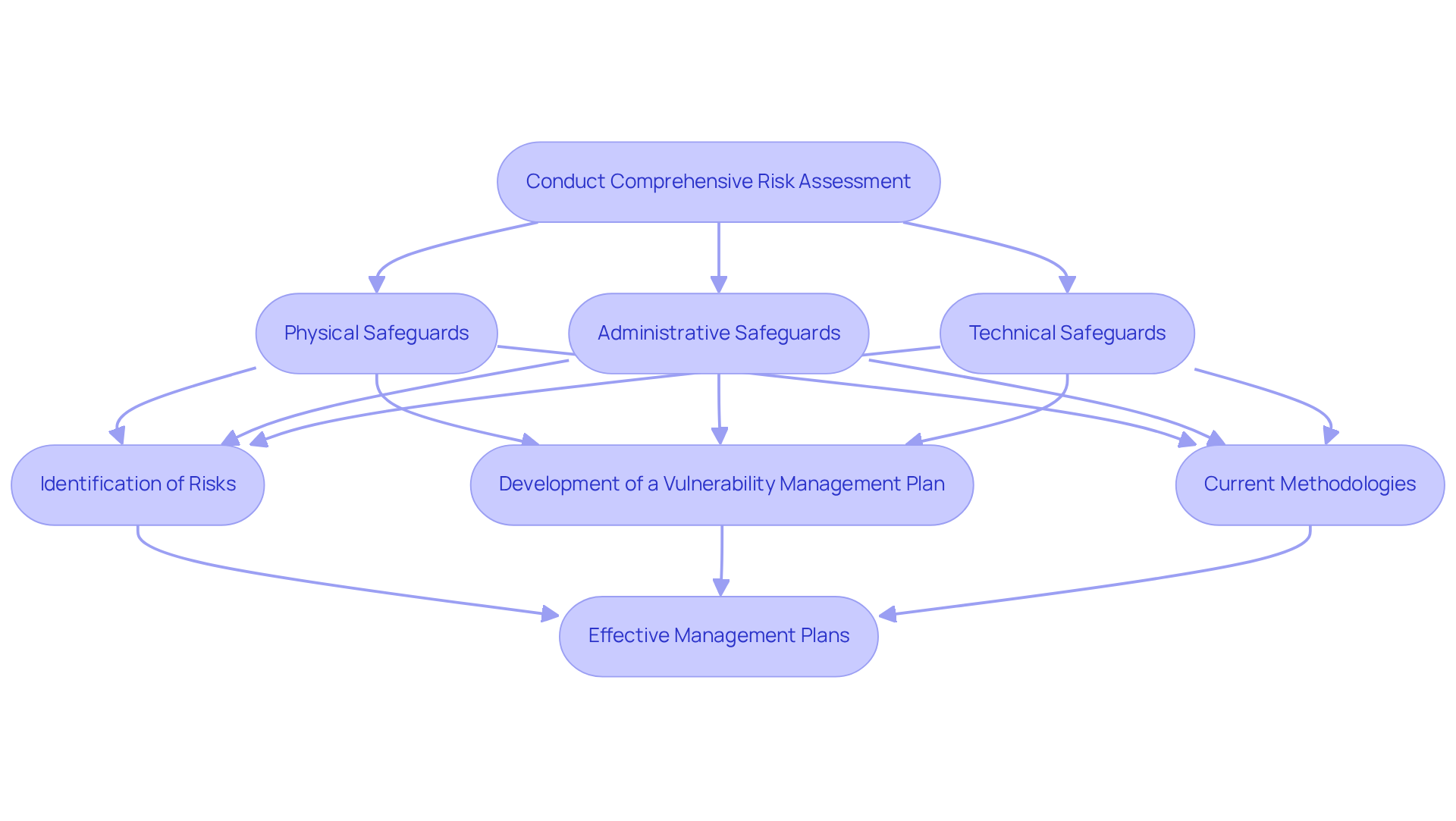
Perform a Comprehensive Risk Assessment
Conducting a comprehensive vulnerability evaluation is crucial for identifying , as outlined in the . This assessment should cover three primary areas: physical, administrative, and technical safeguards. Recent data indicates that only 53% of . Furthermore, 67% of healthcare organizations have experienced attacks utilizing lookalike domains, underscoring the necessity for thorough evaluations.
Key components of a include:
- Identification of Risks: Assess all potential threats to PHI, including unauthorized access, data breaches, and system vulnerabilities. Documentation of findings must meticulously include all identified threats and the methodologies employed in the assessment, in accordance with the .
- Development of a : Formulate a structured plan that addresses identified weaknesses, detailing specific actions to mitigate threats. This plan should include timelines for implementation, assign responsibilities to relevant personnel, and highlight the importance of ongoing training for staff on .
Current methodologies for evaluating threats in healthcare IT typically involve a blend of qualitative and quantitative approaches, employing tools such as automated assessment software and manual penetration testing. to enhance their management capabilities, facilitating real-time monitoring and reporting. Notably, 36% of healthcare institutions have reported an increase in , emphasizing the critical need for .
Examples of effective management plans encompass strategies for securing electronic systems, implementing robust access controls, and ensuring regular training for staff on . By addressing these elements, organizations can significantly reduce their vulnerability to risks and enhance their overall regulatory compliance using a .
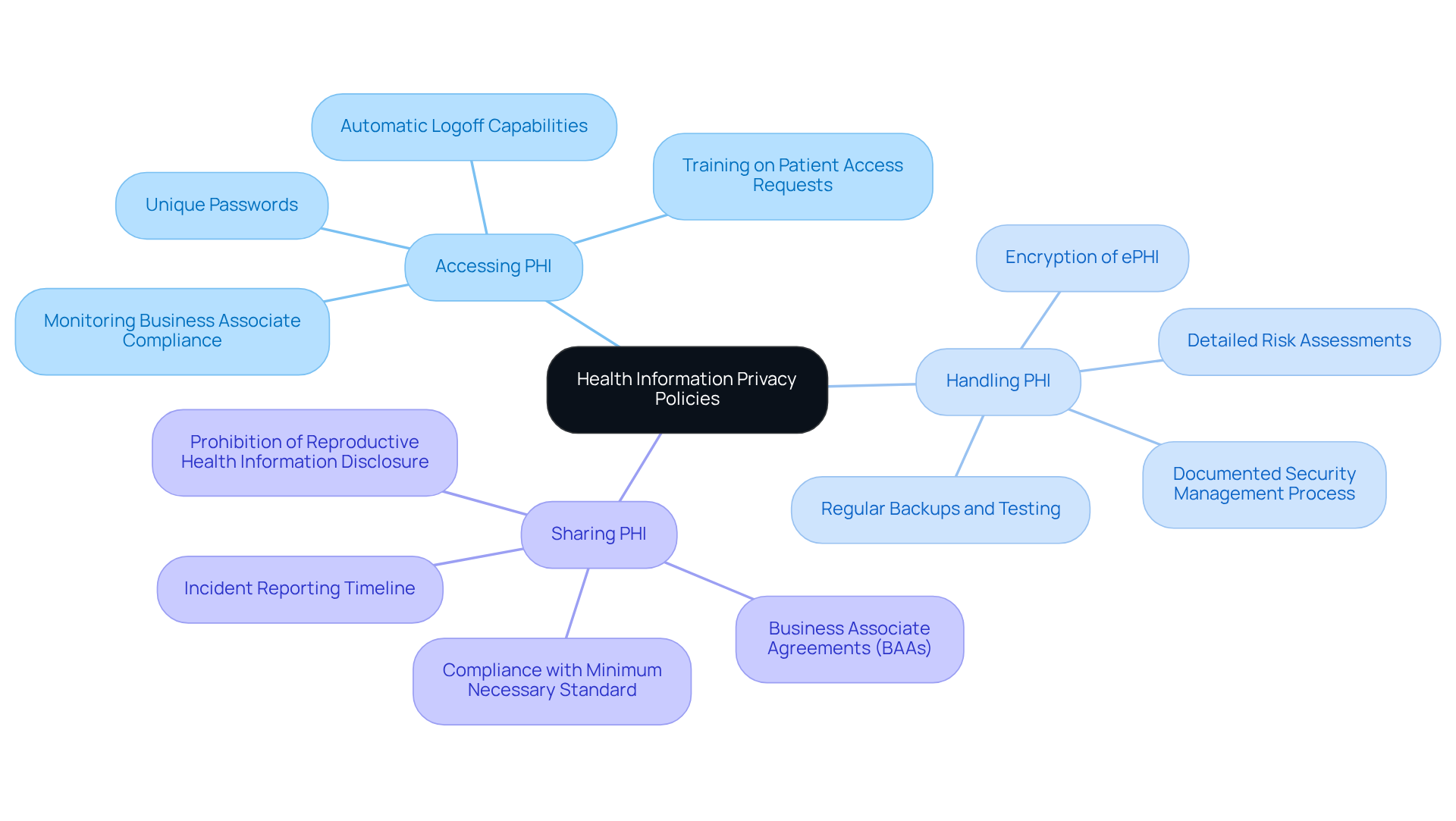
Implement Necessary Policies and Procedures
Develop and implement that address all aspects of . This encompasses , handling, and sharing (PHI). It is are readily accessible to all employees and are .
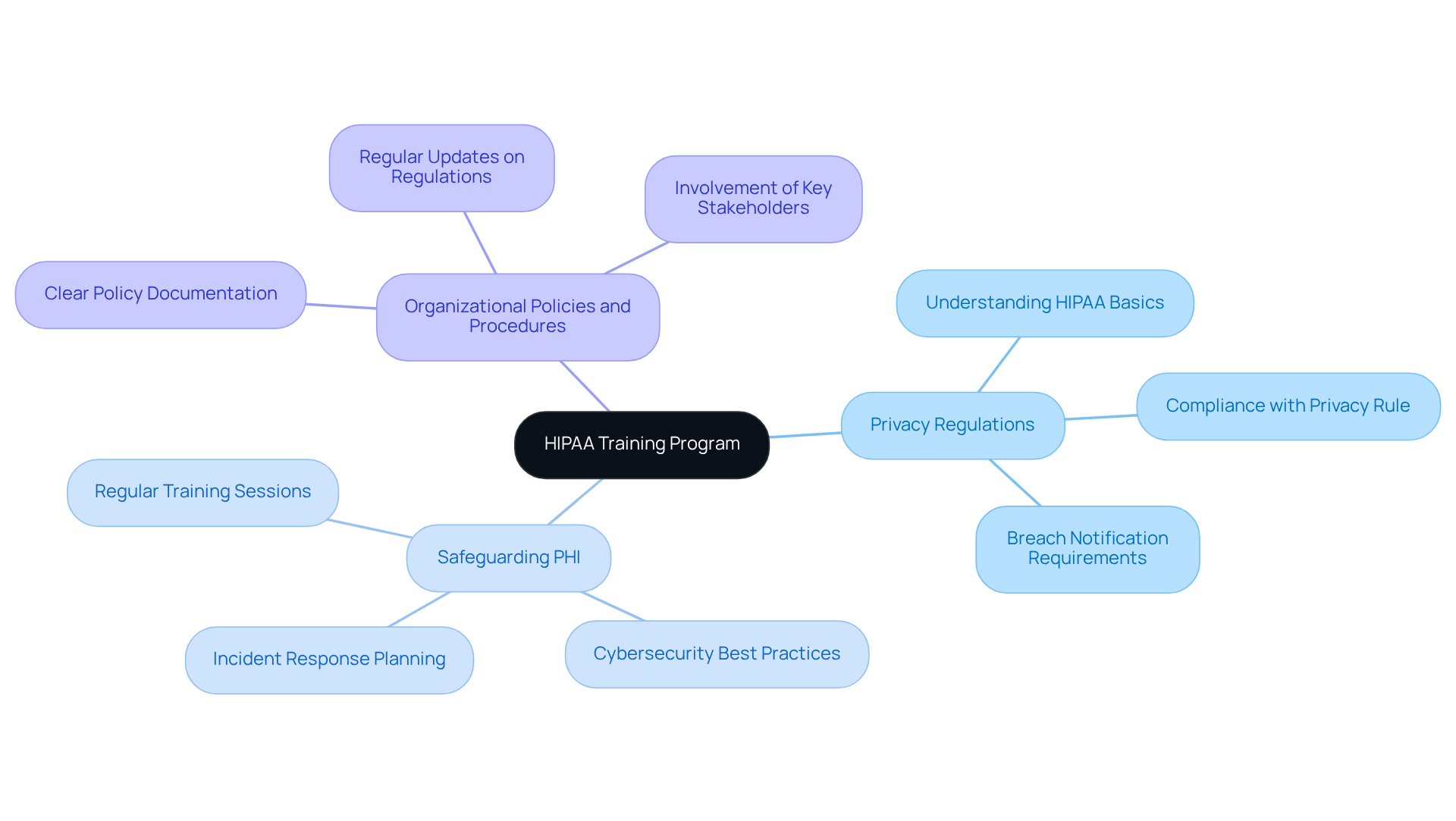
Train Employees on HIPAA Regulations
Establish a comprehensive that addresses , emphasizes the importance of , and outlines the of your organization. This training should be conducted regularly and to reflect any changes in regulations or organizational policies.
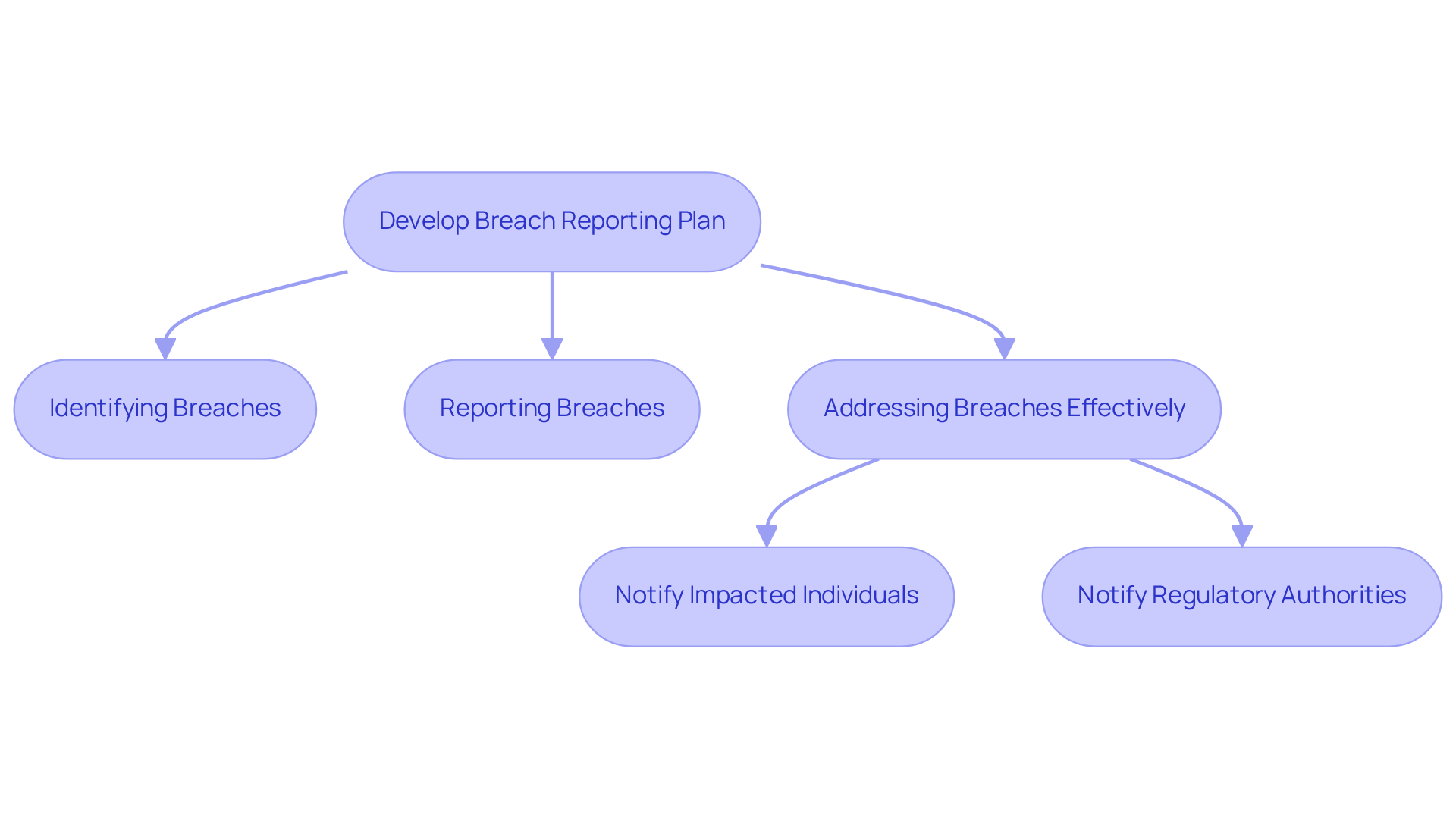
Develop a Breach Reporting Plan
Develop a comprehensive that delineates the to undertake in the event of a . This plan must include procedures for:
- Addressing breaches effectively
Furthermore, it should provide for:
This ensures .
Monitor and Audit Compliance Efforts
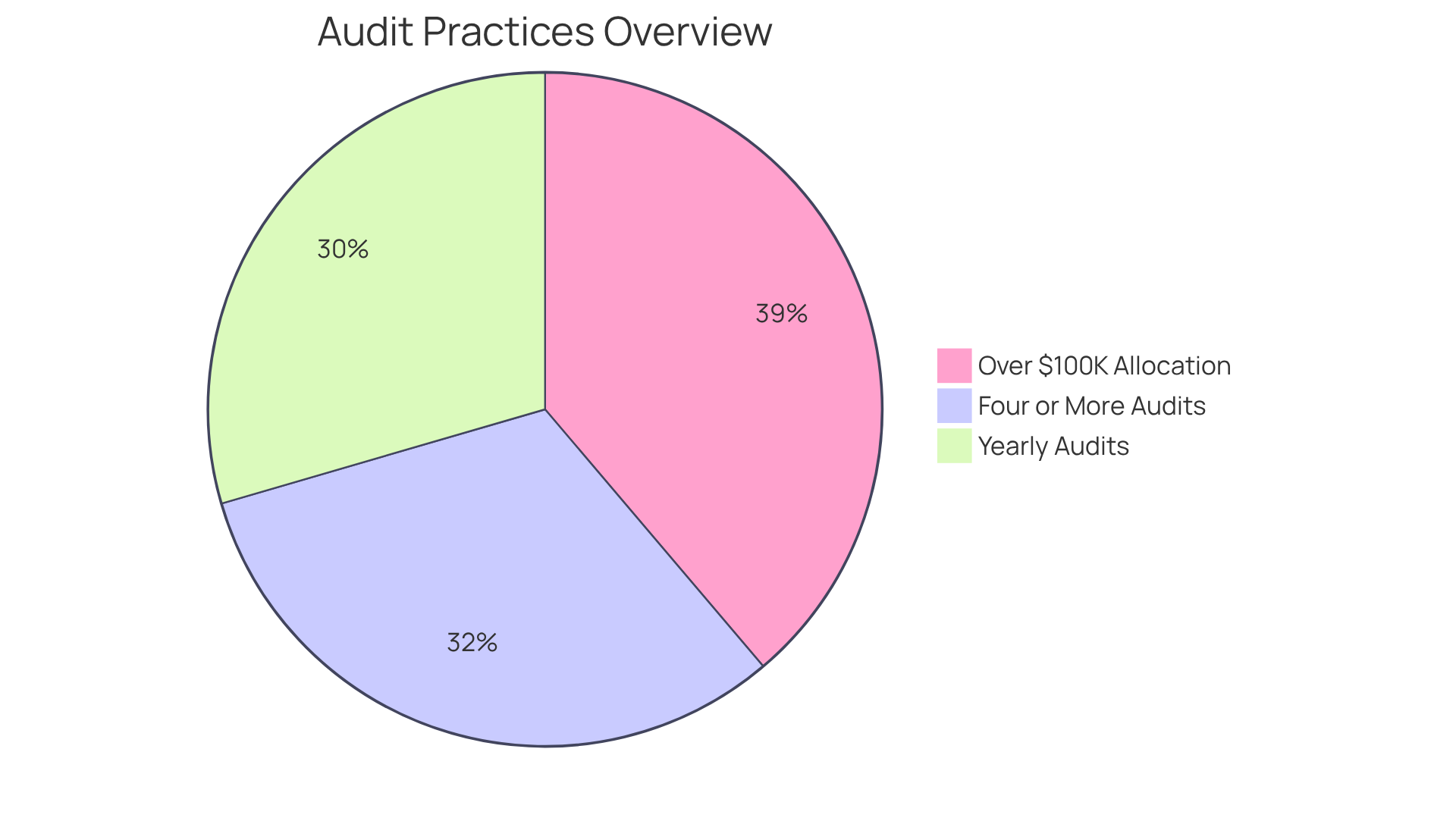
Implementing a is essential for evaluating an entity’s adherence to the . Regular assessments of policies, procedures, and employee compliance are . Notably, 54% of entities conduct yearly audits, demonstrating a commitment to maintaining high standards. Furthermore, 58% of establishments performed four or more audits in 2025, underscoring the growing emphasis on compliance and risk management. These audits not only identify but also ensure that adherence efforts align with evolving regulations, such as those outlined in the . By leveraging insights from these evaluations, organizations can make informed adjustments to their practices, thereby enhancing their overall . Additionally, 71% of enterprise firms allocate , highlighting the importance of thorough evaluations in safeguarding protected health information (PHI). Moreover, 42% of executives reported that , illustrating technology’s role in compliance efforts. Establishing a culture of through regular monitoring and auditing can substantially reduce risks associated with noncompliance.
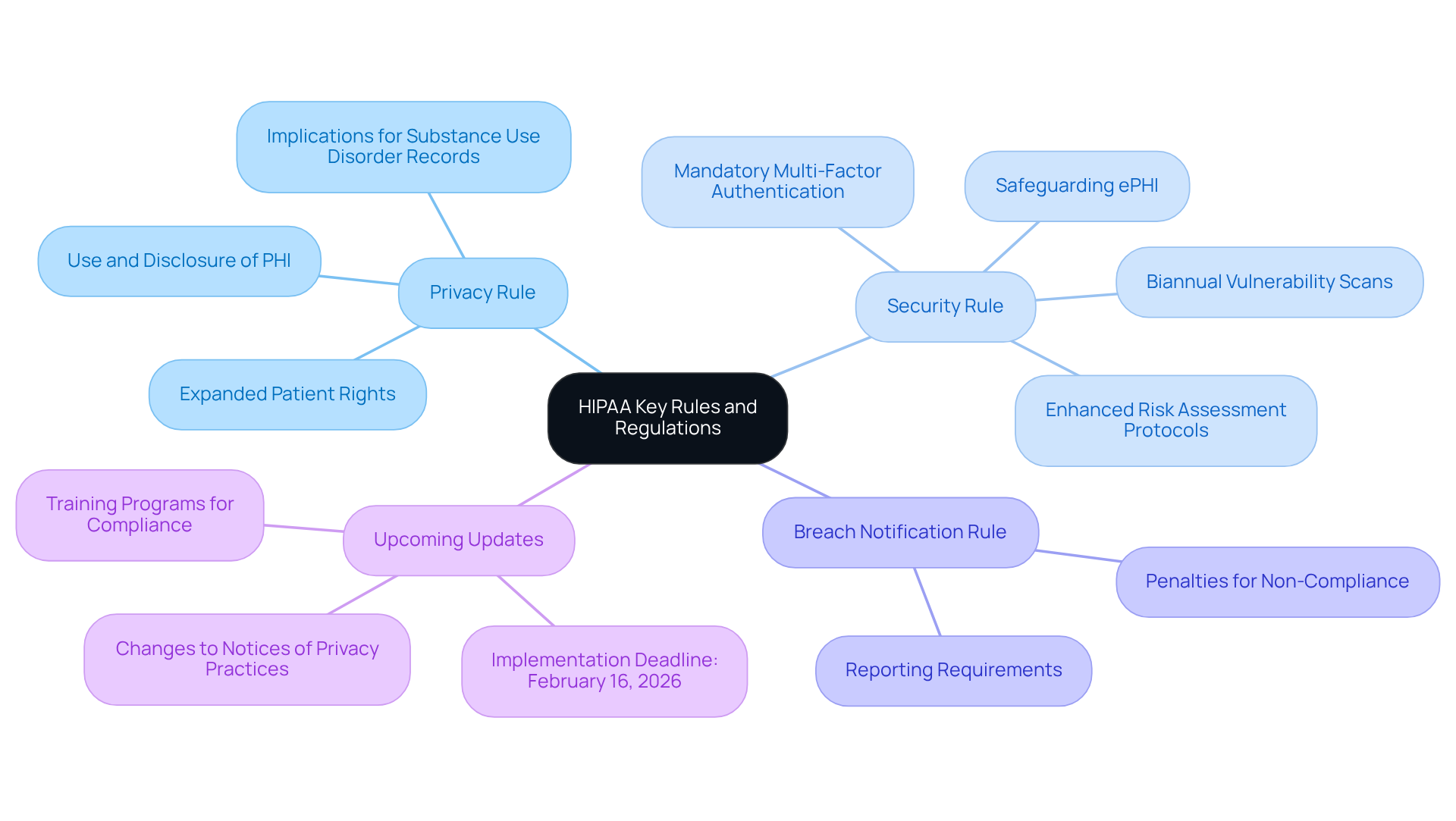
Understand HIPAA’s Key Rules and Regulations
Healthcare entities must have a comprehensive understanding of the , particularly the . This knowledge is crucial, as it directly impacts daily operations and compliance efforts. The Privacy Rule governs the use and disclosure of protected health information (PHI), while the Security Rule sets standards for safeguarding electronic PHI (ePHI). With upcoming updates, organizations are required to adapt to new mandates, including:
- Enhanced risk assessment protocols
- Biannual vulnerability scans
All of which must be implemented by February 16, 2026.
are vital for ensuring that . These programs should highlight the implications of on operational workflows and stress the importance of maintaining . Recent statistics indicate that approximately 70% of healthcare organizations are aware of the key regulations; however, many still encounter challenges with full compliance, underscoring the need for ongoing education and training.
Current interpretations of the Privacy Rule and Security Rule are evolving, especially in response to recent updates designed to strengthen patient rights and enhance cybersecurity measures. Organizations must remain informed about these changes to effectively navigate the complexities of and ensure that their operations align with regulatory expectations.
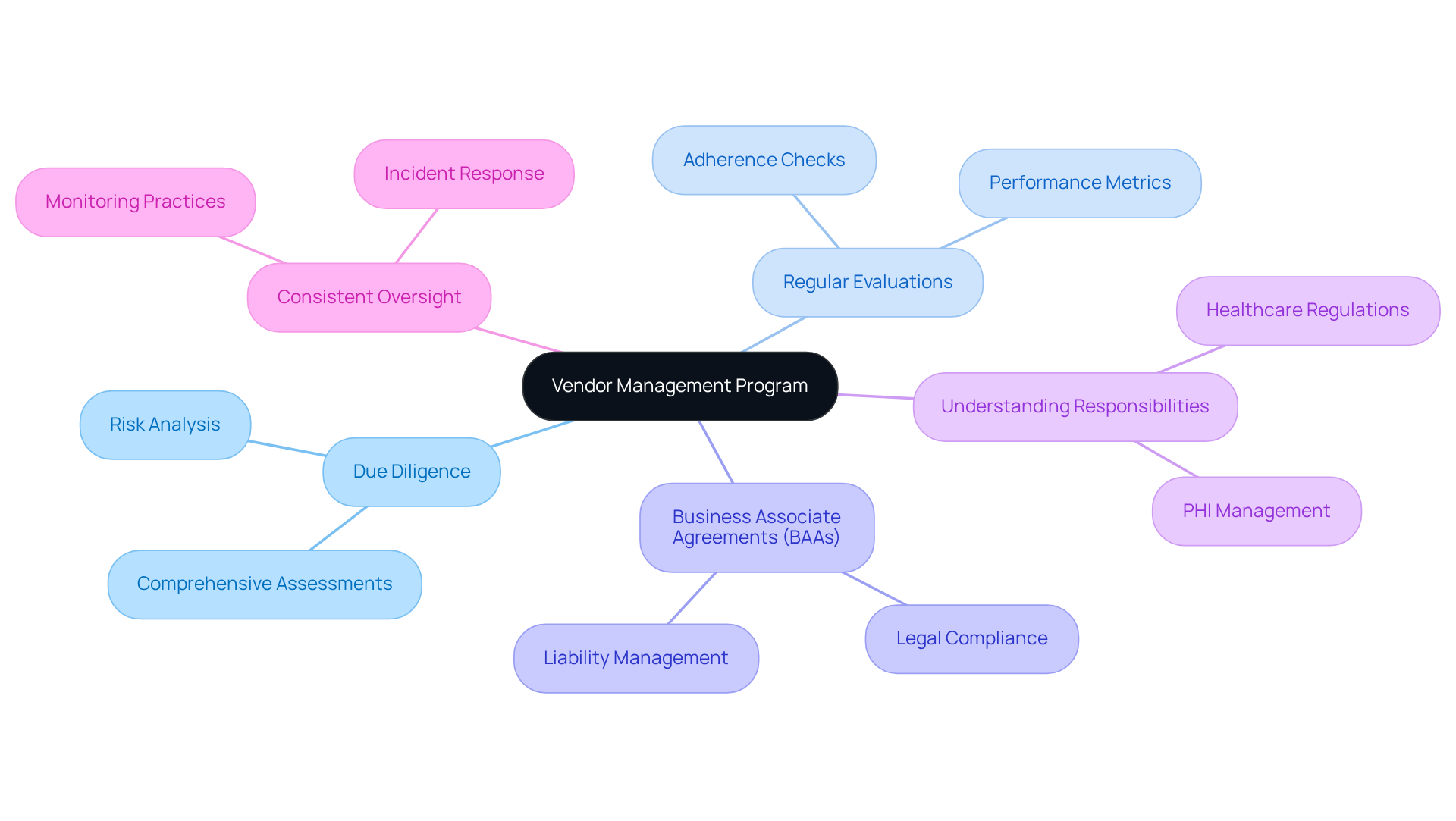
Manage Third-Party Vendor Compliance
Establish a that incorporates and . This program should also include the creation of (BAAs) with all vendors managing (PHI). It is fully understand their responsibilities under , and is crucial.
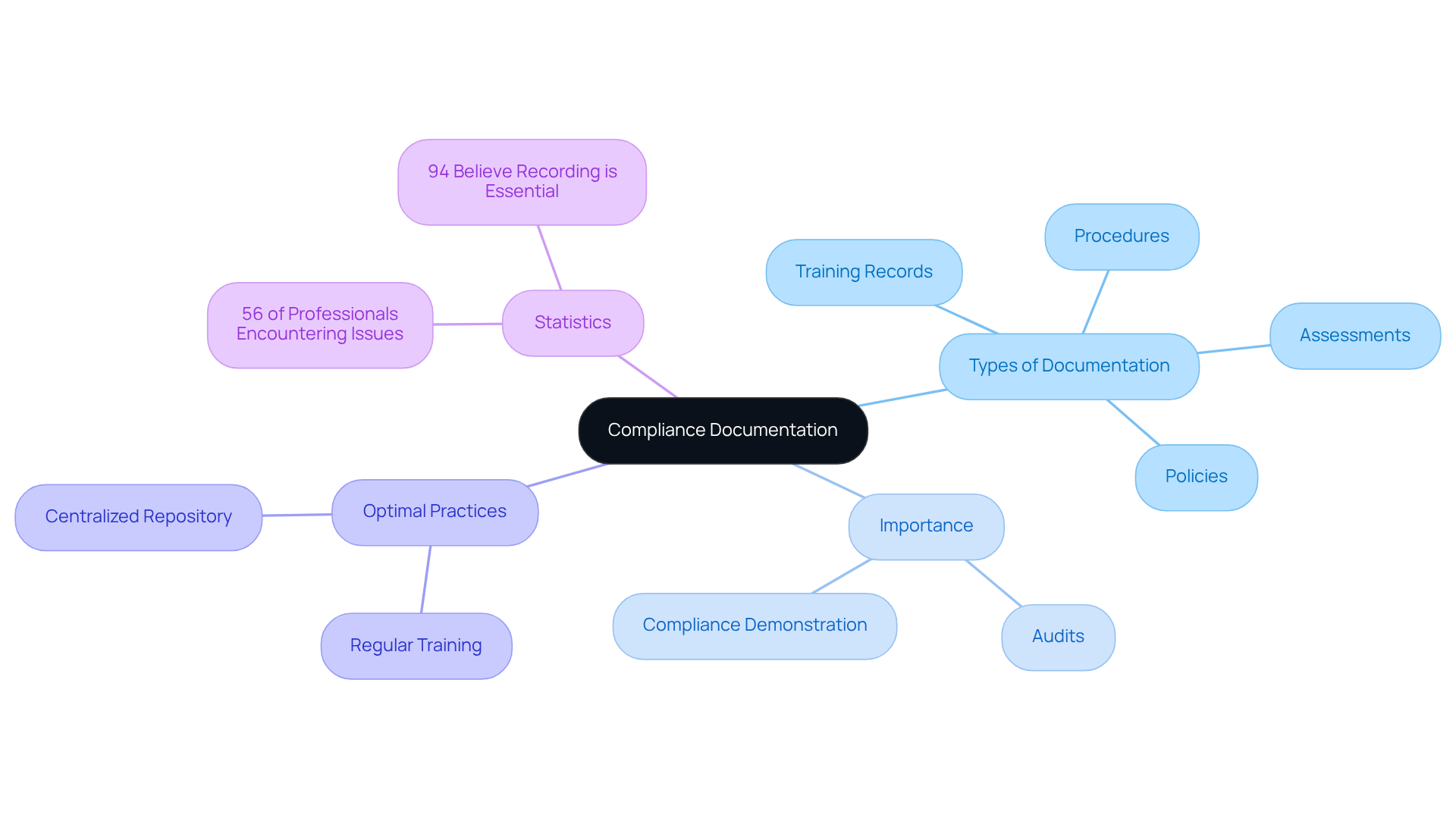
Create Comprehensive Compliance Documentation
To ensure , organizations must create and maintain , including policies, procedures, training records, and assessments of potential issues. This documentation is essential during audits and reviews, as it demonstrates compliance with . Regular updates are vital; a significant 56% of risk and regulatory professionals have reported encountering at least one regulatory issue in the past three years, often stemming from inadequate documentation.
Optimal practices involve , ensuring that all documentation is readily accessible and up-to-date. Furthermore, organizations should conduct regular to underscore the importance of documentation, given that
Additionally, with anticipated changes in 2026 emphasizing , organizations must ensure that their rather than mere paperwork. Appointing a designated for oversight is also crucial for maintaining effective compliance. By prioritizing thorough documentation and adhering to these updated requirements, organizations can not only meet but also enhance their operational integrity and foster trust with stakeholders.
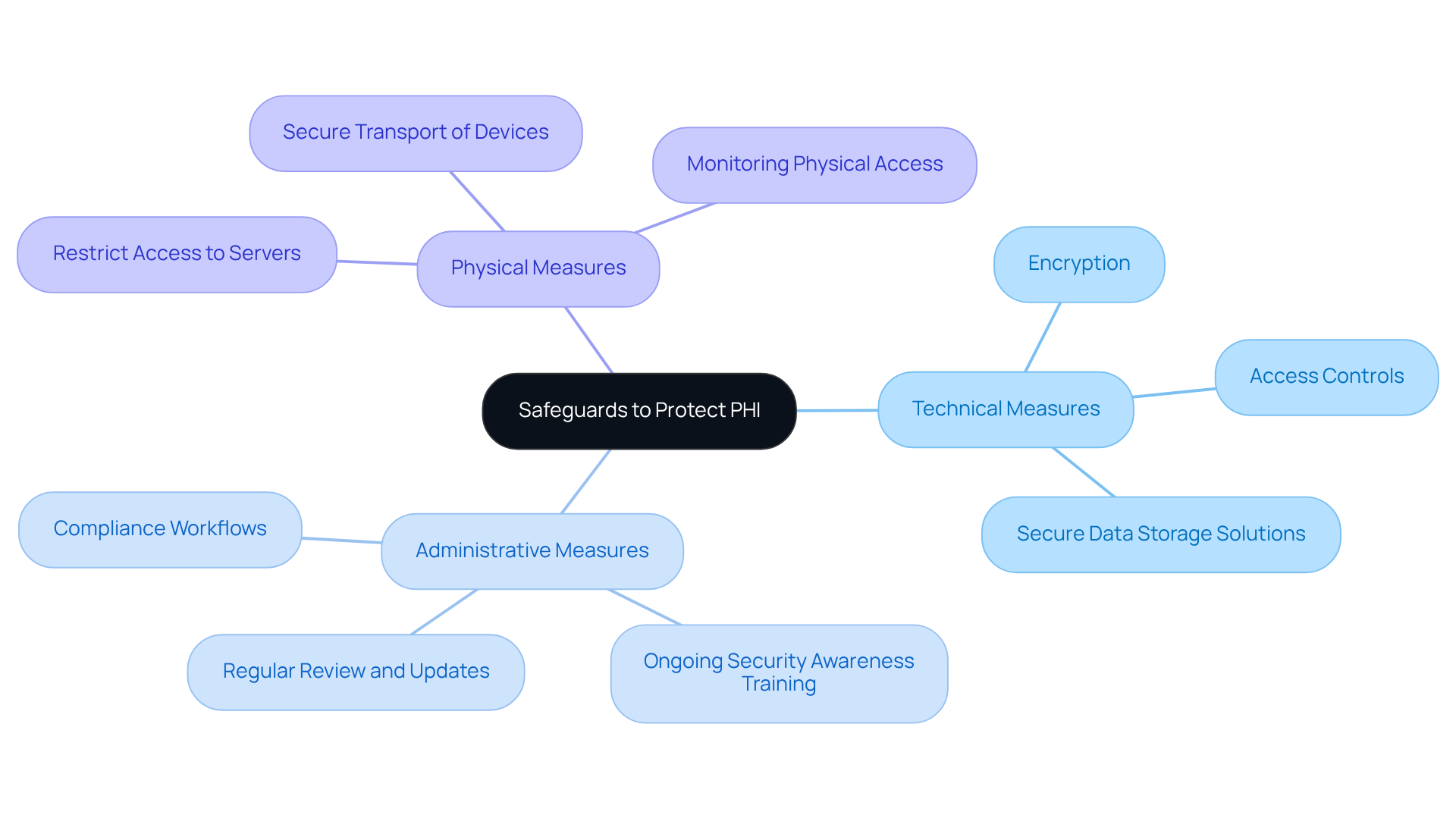
Implement Safeguards to Protect PHI
To protect PHI, it is essential to establish and enforce a comprehensive set of , which include technical, administrative, and physical measures. Key components of these safeguards involve:
Furthermore, it is crucial to to effectively address .
Conclusion
Establishing a robust framework for HIPAA compliance transcends mere regulatory obligation; it is essential for safeguarding the integrity and confidentiality of sensitive health information. By adhering to the outlined steps, organizations can significantly bolster their compliance posture and mitigate risks associated with noncompliance. The proactive appointment of a dedicated Compliance Officer, along with comprehensive risk assessments and effective training programs, constitutes the foundation of a resilient compliance strategy.
Key elements include:
- A thorough understanding of HIPAA’s rules
- The implementation of necessary policies and procedures
- The development of a breach reporting plan
- Regular monitoring and auditing of compliance efforts
- The management of third-party vendor relationships
- Maintaining comprehensive compliance documentation
In conclusion, the significance of HIPAA compliance extends beyond legal adherence; it cultivates trust and confidence among patients and stakeholders alike. Organizations are urged to prioritize these compliance steps not merely as a checklist but as an integral component of their operational ethos. By committing to these practices, entities can foster a culture of compliance that not only protects sensitive health information but also enhances overall organizational integrity and reputation within the healthcare landscape.
Frequently Asked Questions
Why is appointing a Compliance Officer important for HIPAA compliance?
A dedicated Compliance Officer is essential for ensuring adherence to privacy regulations, possessing a thorough understanding of health information privacy laws and being empowered to implement necessary changes effectively.
What are the qualifications needed for a Compliance Officer?
The Compliance Officer must have a comprehensive understanding of health information privacy regulations and should receive consistent training and updates on evolving healthcare regulations.
What impact does having a dedicated HIPAA Officer have on compliance outcomes?
Research indicates that approximately 70% of organizations with dedicated HIPAA Officers experience significantly improved compliance outcomes, especially in regulated sectors like healthcare and financial services.
What changes to HIPAA compliance are expected in 2026?
The role of the Compliance Officer will become increasingly critical, particularly regarding expedited breach notifications and comprehensive audit logs as the landscape of HIPAA compliance evolves.
What are the consequences of noncompliance with HIPAA regulations?
Noncompliance can lead to severe repercussions, including fines from the Office for Civil Rights (OCR) and the loss of Medicare and Medicaid reimbursements.
What is the purpose of conducting a comprehensive risk assessment?
A comprehensive risk assessment is crucial for identifying potential weaknesses in systems and processes related to Protected Health Information (PHI).
What areas should a HIPAA risk assessment cover?
The assessment should cover physical, administrative, and technical safeguards related to PHI.
What are key components of a HIPAA risk assessment?
Key components include the identification of risks, documentation of findings, and the development of a vulnerability management plan that addresses identified weaknesses.
How can organizations enhance their threat evaluation methodologies?
Organizations can employ a blend of qualitative and quantitative approaches, utilizing tools like automated assessment software and manual penetration testing, as well as adopting AI-powered platforms for real-time monitoring.
What should a vulnerability management plan include?
It should detail specific actions to mitigate threats, timelines for implementation, assigned responsibilities, and ongoing training for staff on cybersecurity best practices.
What policies and procedures should organizations implement for HIPAA compliance?
Organizations should develop comprehensive policies and procedures addressing all aspects of health information privacy regulations, including clear guidelines for accessing, handling, and sharing PHI.
How often should HIPAA policies and procedures be updated?
Policies and procedures should be regularly updated to reflect any changes in regulations and must be readily accessible to all employees.
List of Sources
- Neutech: Designate a HIPAA Compliance Officer
- vanreincompliance.com (https://vanreincompliance.com/blog/case-studies-in-hipaa-compliance-lessons-learned)
- outsidegc.com (https://outsidegc.com/blog/hipaa-changes-coming-in-2026)
- HIPAA IT Security in 2026 (https://charlotteitsolutions.com/hipaa-it-security-in-2026)
- Is Your Organization Ready for the 2026 HIPAA Update? (https://pbmares.com/is-your-organization-ready-for-the-2026-hipaa-update)
- Perform a Comprehensive Risk Assessment
- OCR’s Latest HIPAA Guidance: Strategic Measures to Protect Your Systems and Data (https://bakerdonelson.com/ocrs-latest-hipaa-guidance-strategic-measures-to-protect-your-systems-and-data)
- HIPAA Enforcement Trends: Protecting Patient Privacy and Data Security (https://jimersonfirm.com/blog/2026/01/hipaa-enforcement-trends-protecting-patient-privacy-and-data-security)
- Healthcare Cybersecurity Statistics 2024 (https://ispartnersllc.com/blog/healthcare-cybersecurity-statistics)
- 80+ Healthcare Data Breach Statistics 2026 (https://getastra.com/blog/security-audit/healthcare-data-breach-statistics)
- censinet.com (https://censinet.com/perspectives/7-metrics-that-matter-healthcare-risk-today)
- Implement Necessary Policies and Procedures
- hipaajournal.com (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- outsidegc.com (https://outsidegc.com/blog/hipaa-changes-coming-in-2026)
- Critical HIPAA Updates for 2026 (https://corsicatech.com/blog/hipaa-updates-security-rules)
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- Train Employees on HIPAA Regulations
- compliancy-group.com (https://compliancy-group.com/hipaa-compliance-quotes)
- vanreincompliance.com (https://vanreincompliance.com/blog/case-studies-in-hipaa-compliance-lessons-learned)
- outsidegc.com (https://outsidegc.com/blog/hipaa-changes-coming-in-2026)
- More than half of employees don’t understand HIPAA rules | Medical Economics (https://medicaleconomics.com/view/more-than-half-of-employees-don-t-understand-hipaa-rules)
- hipaajournal.com (https://hipaajournal.com/over-90-of-organizations-now-provide-annual-hipaa-refresher-training)
- Develop a Breach Reporting Plan
- 80+ Healthcare Data Breach Statistics 2026 (https://getastra.com/blog/security-audit/healthcare-data-breach-statistics)
- HIPAA Breach Notification Rule (https://ama-assn.org/practice-management/hipaa/hipaa-breach-notification-rule)
- compliancy-group.com (https://compliancy-group.com/hipaa-compliance-quotes)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- Monitor and Audit Compliance Efforts
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- The HIPAA Journal Annual Survey (https://hipaajournal.com/hipaa-journal-annual-survey)
- The Value of an Effective HIPAA Compliance Program Amid OCR HIPAA Audits | News & Events | Clark Hill PLC (https://clarkhill.com/news-events/news/the-value-of-an-effective-hipaa-compliance-program-amid-ocr-hipaa-audits)
- 2024 HIPAA Trends and Statistics (https://securitymetrics.com/blog/2024-hipaa-trends)
- 115 Compliance Statistics You Need To Know in 2023 – Drata (https://drata.com/blog/compliance-statistics)
- Understand HIPAA’s Key Rules and Regulations
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- hipaajournal.com (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- HIPAA’s February 16 Deadline: A Strategic Moment for Privacy Governance (https://seyfarth.com/news-insights/hipaas-february-16-deadline-a-strategic-moment-for-privacy-governance.html)
- Critical HIPAA Updates for 2026 (https://corsicatech.com/blog/hipaa-updates-security-rules)
- Manage Third-Party Vendor Compliance
- HIPAA BAA Best Practices: Choosing The Right Business Associate (https://drcatalyst.com/blog/choosing-the-right-business-associate-hipaa-baa-best-practices)
- Is Your Organization Ready for the 2026 HIPAA Update? (https://pbmares.com/is-your-organization-ready-for-the-2026-hipaa-update)
- varonis.com (https://varonis.com/blog/healthcare-cybersecurity-statistics)
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- January 2026 OCR Cybersecurity Newsletter (https://hhs.gov/hipaa/for-professionals/security/guidance/cybersecurity-newsletter-january-2026)
- Create Comprehensive Compliance Documentation
- HIPAA Compliance in 2026: Everything You Need to Know (https://venn.com/learn/hipaa-compliance)
- Critical HIPAA Updates for 2026 (https://corsicatech.com/blog/hipaa-updates-security-rules)
- 130+ Compliance Statistics & Trends to Know for 2026 (https://secureframe.com/blog/compliance-statistics)
- 94% of compliance officers say: No documentation? It’s not done (https://ama-assn.org/practice-management/physician-health/94-compliance-officers-say-no-documentation-it-s-not-done)
- The Wait Is Over: Information Blocking Enforcement Is Officially Here | Insights | Holland & Knight (https://hklaw.com/en/insights/publications/2026/02/the-wait-is-over-information-blocking-enforcement-is-officially-here)
- Implement Safeguards to Protect PHI
- 2026 HIPAA Changes: New Security Rule Requirements (https://hipaavault.com/resources/2026-hipaa-changes)
- Healthcare Data Breach Statistics (https://hipaajournal.com/healthcare-data-breach-statistics)
- hipaajournal.com (https://hipaajournal.com/hipaa-updates-hipaa-changes)
- outsidegc.com (https://outsidegc.com/blog/hipaa-changes-coming-in-2026)
