Introduction
In an era marked by the prevalence of cyber threats, hedge fund managers encounter the significant challenge of securing their software development processes amidst a complex regulatory landscape. By integrating security measures from the outset and adhering to established best practices, these financial leaders can safeguard sensitive information while simultaneously enhancing their operational integrity.
Nevertheless, with the continuous evolution of compliance requirements and the persistent risk of breaches, how can they effectively balance the implementation of security measures with the demands for innovation and productivity?
Integrate Security from the Start: Principles of Secure Software Development
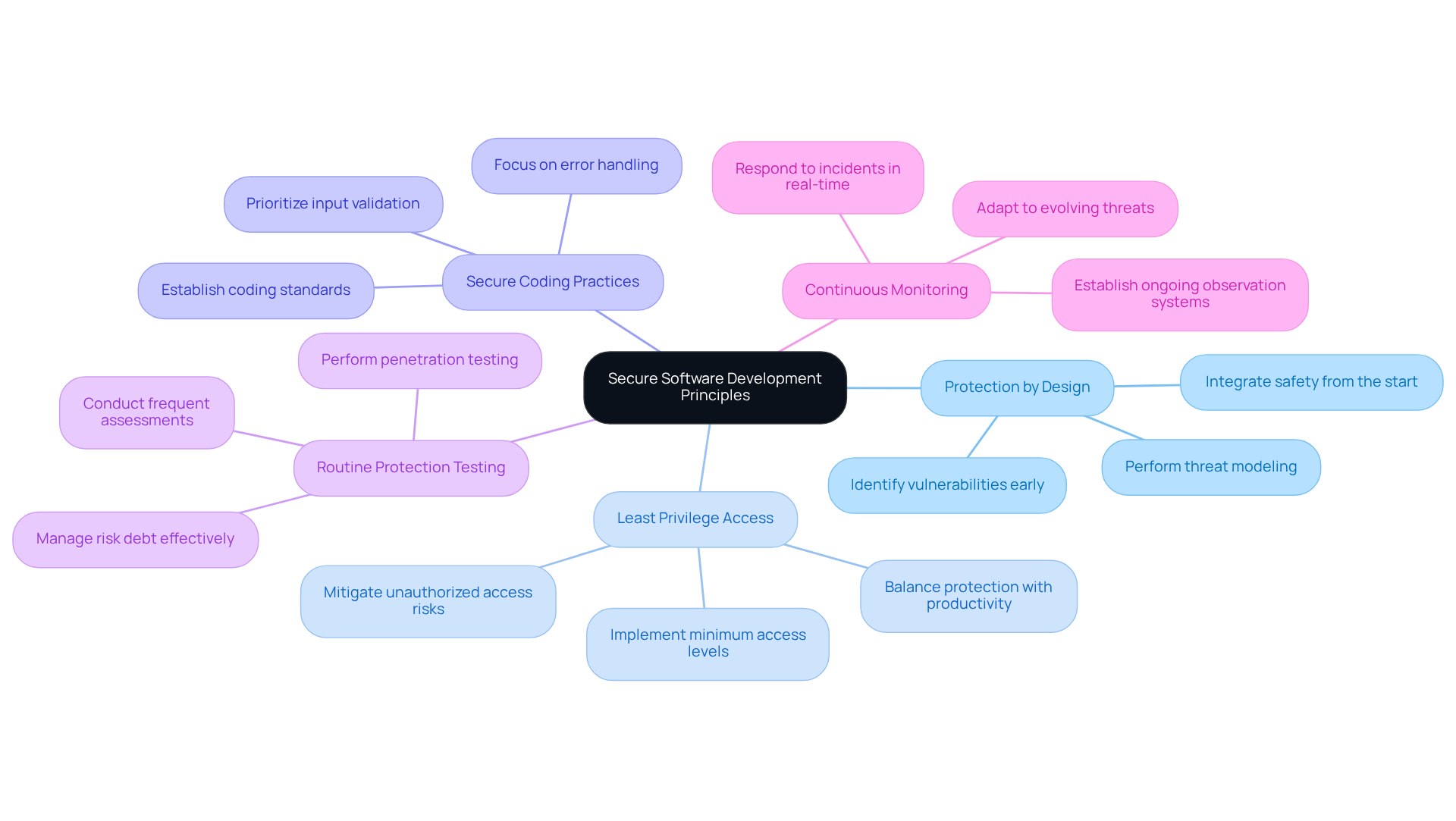
To effectively develop software, teams should adopt the following principles:
- Safety: Safety considerations must be integrated from the initial design phase. This includes assessing and identifying potential vulnerabilities before coding begins, ensuring that security protection is a fundamental element rather than an afterthought. It is crucial to avoid common pitfalls, such as neglecting security requirements or underestimating the complexity of implementing safety measures.
- Least Privilege Access: The Principle of Least Privilege (PoLP) should be implemented to ensure that users and systems have only the minimum level of access necessary for their functions. This approach significantly mitigates the risk of unauthorized access and limits potential damage from compromised credentials. As cybersecurity expert Kumar Ramachandran states, “The principle minimizes the attack surface, diminishing avenues a malicious actor can use to access sensitive data.” However, organizations often face challenges in balancing security with user productivity and ensuring consistent enforcement across systems.
- Secure Coding Practices: Establishing coding standards that prioritize security is essential, including input validation, error handling, and robust authentication mechanisms. These practices help reduce common vulnerabilities that attackers might exploit. Recognizing that human error is a significant factor in cybersecurity incidents makes security training even more critical.
- Regular Testing: Frequent assessments, such as penetration testing and code reviews, should be conducted to identify and address vulnerabilities early in the development process. With 71% of organizations issuing software updates at least weekly, regular testing is vital for maintaining integrity. Organizations must also be mindful of the potential for risk debt if testing processes are not adequately managed.
- Continuous Monitoring: A system for ongoing observation of applications should be established to identify and respond to incidents in real-time. This proactive approach is essential in today’s rapidly evolving threat landscape, where a breach can occur at any moment. Continuous monitoring enables organizations to quickly identify and address vulnerabilities, further enhancing their security posture.
By incorporating these principles into the development process, organizations can create software that effectively safeguards sensitive information.
Understand Compliance Requirements: Navigating Regulations in Software Development
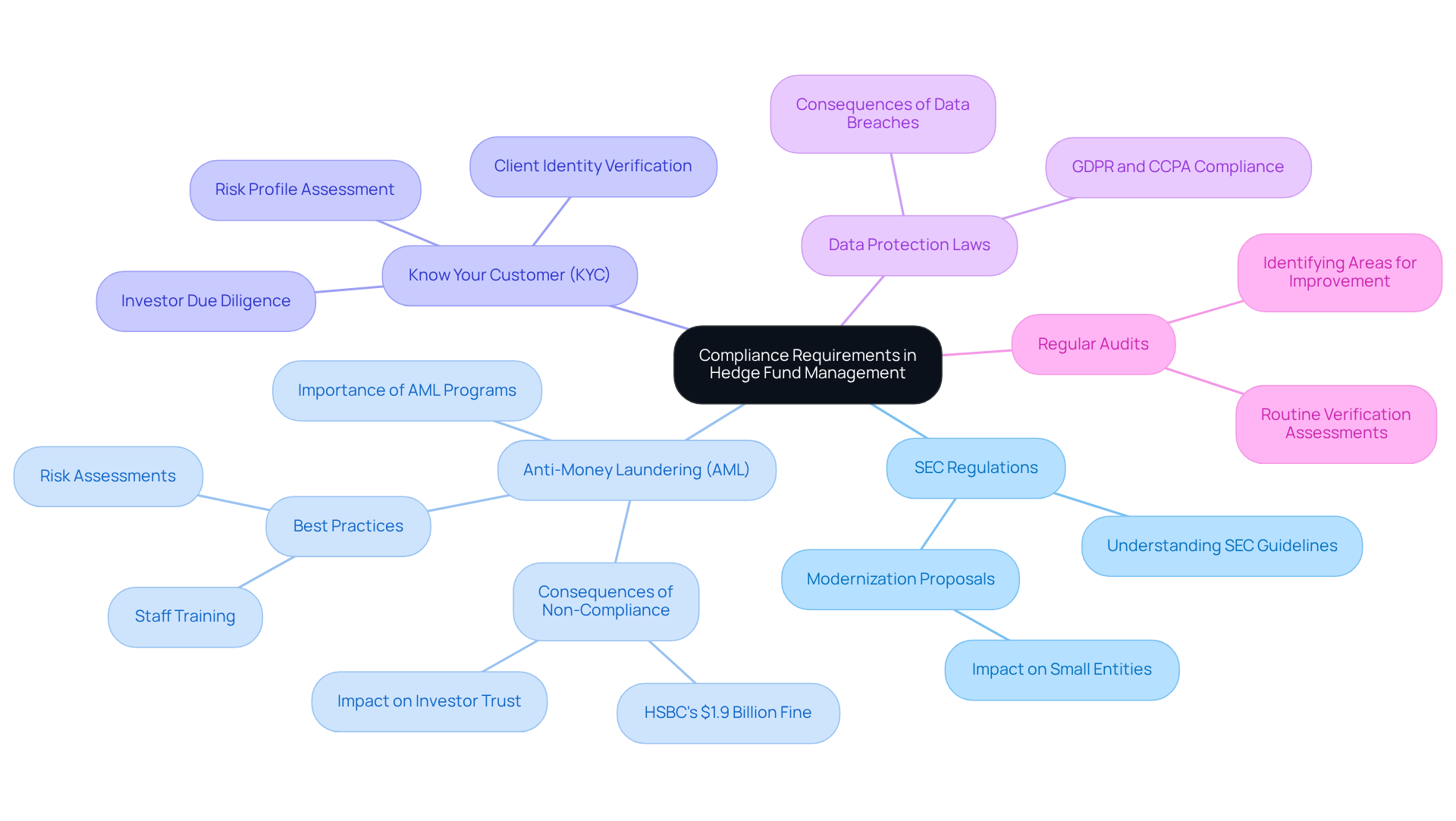
Hedge fund managers must navigate a complex landscape of compliance requirements to ensure operational integrity and mitigate risks. Key areas of focus include:
- SEC Regulations: Familiarity with the regulations is essential for understanding trading practices and reporting obligations. Recent proposals aim to modernize these regulations, particularly for smaller entities, ensuring they are better equipped to meet regulatory challenges.
- Anti-Money Laundering (AML): Implementing AML measures is crucial for detecting and preventing money laundering activities. The consequences of non-compliance can be severe; for instance, HSBC faced a $1.9 billion fine for failing to prevent money laundering due to inadequate monitoring systems and poorly trained staff. Hedge fund vehicles must prioritize AML adherence to protect their operations and maintain investor trust.
- Know Your Customer (KYC): Establishing KYC processes is vital for verifying client identities and assessing risk profiles. This process not only aids in upholding regulations but also is linked to ineffective AML systems, which can lead to asset freezes and regulatory inquiries. Institutional limited partners increasingly demand proof of strong AML controls during due diligence, underscoring the importance of KYC in the current regulatory environment.
- Data Protection Laws: Adhering to data protection laws such as GDPR or CCPA is mandatory. These laws impose strict guidelines for handling personal data, and failure to comply can result in significant penalties, complicating the operational landscape for hedge funds.
- Regular Audits: Conducting regular audits is crucial to ensure that all procedures conform to regulatory standards. These audits help identify areas for improvement and emphasize the importance of maintaining strong regulatory frameworks. For example, a private equity consultant faced penalties for overlooking AML warning signs, highlighting the necessity for ongoing diligence in regulatory practices.
By understanding and applying these compliance requirements, hedge fund managers can enhance their operational integrity and mitigate risks associated with regulatory non-compliance.
Implement Best Practices: Strategies for Secure Software Development
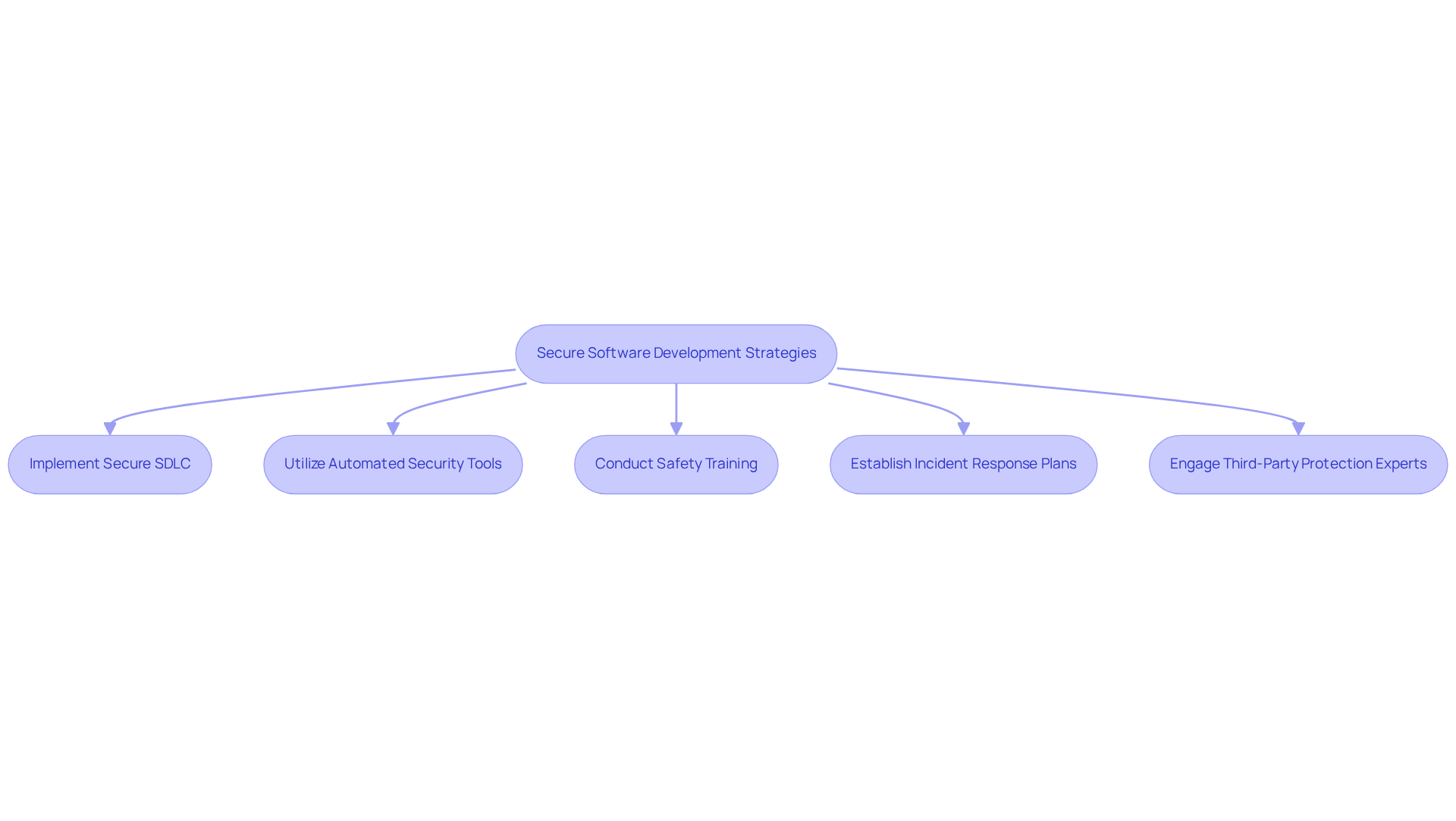
To enhance the security of software development, managers should adopt several key practices:
- Implementing a software development lifecycle (SDLC) is essential to incorporate protection at every stage, from planning and design to deployment and maintenance.
- Utilize tools: Implementing tools for static and dynamic code analysis is crucial for identifying vulnerabilities during the development process.
- Provide training: Regular instruction for developers on secure coding practices and emerging threats is necessary to enhance security.
- Establish protocols: Creating and upholding incident response strategies allows for swift action in tackling breaches and minimizing harm.
- Engage experts: Collaborating with external consultants to conduct thorough assessments and audits of software systems is highly beneficial.
By following these strategies, hedge fund managers can significantly reduce the risk of breaches and ensure adherence to compliance requirements through the implementation of secure software.
Monitor and Evolve: Ensuring Ongoing Security and Compliance
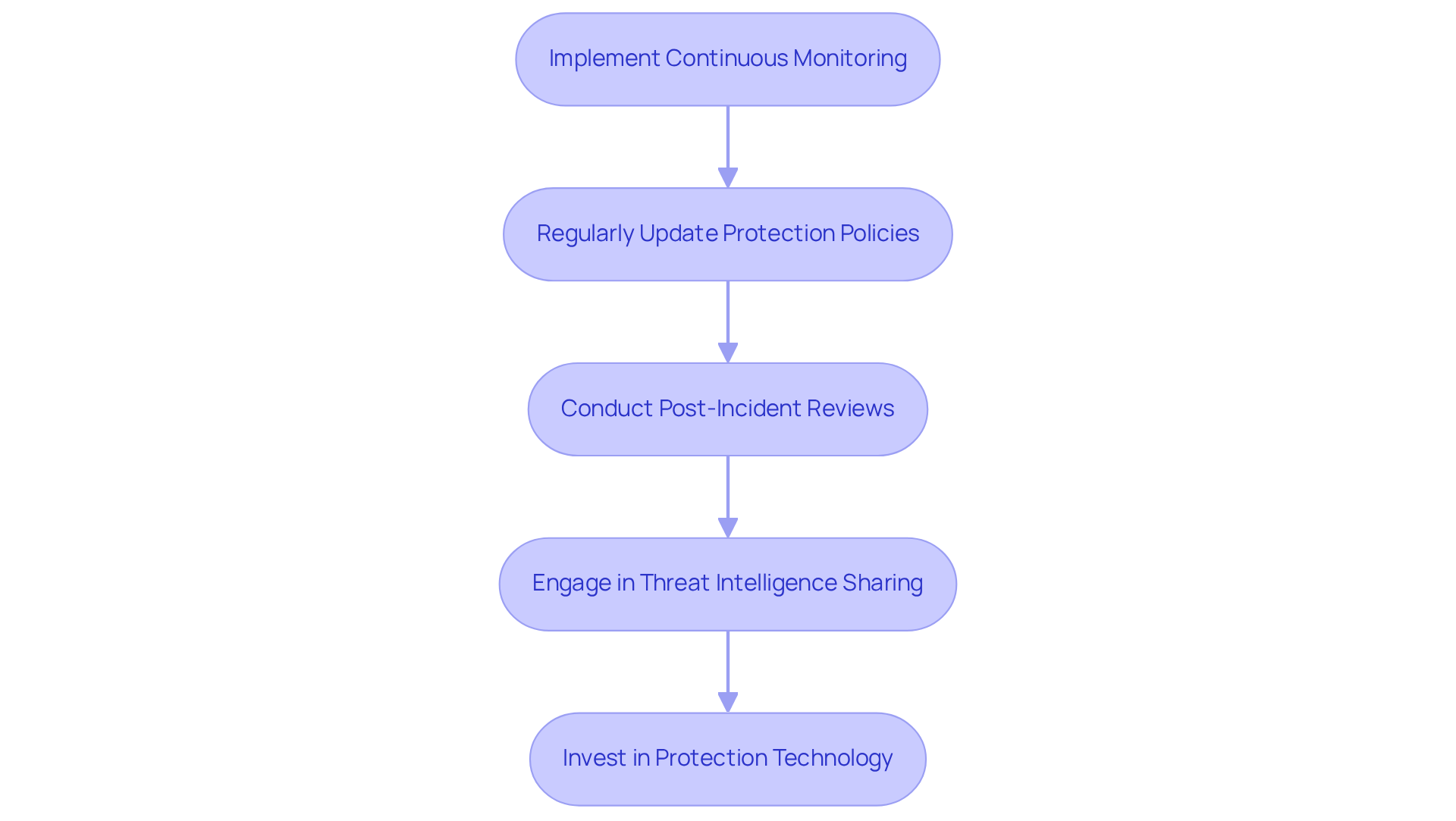
To maintain a robust security posture, hedge fund managers should undertake the following steps:
- Implement Monitoring: Employ information and event management (SIEM) systems to diligently monitor applications and networks for any suspicious activities.
- Regularly Update Protection Policies: Routinely review and revise protection policies and procedures to ensure alignment with evolving regulations and emerging threats. This includes training, where awareness programs, such as the ones offered by industry experts, will be essential. As Michael Soohoo emphasizes, “It’s not just remote access or privileged accounts.”
- Conduct Post-Incident Reviews: After any incident, carry out a comprehensive assessment to identify vulnerabilities and enhance future response strategies. This practice not only aids in swift recovery but also strengthens long-term safety frameworks. Notably, approximately half of firms reported experiencing a breach in the past 12 months, highlighting the critical nature of this step.
- Engage in Information Sharing: Actively participate in industry forums to exchange information regarding emerging threats and best practices. This collaborative approach can significantly enhance defenses against sophisticated cyber threats.
- Invest in Protection Technology: Continuously assess and invest in solutions that can fortify defenses against evolving threats. Staying ahead of technological advancements is crucial for maintaining compliance and safeguarding sensitive data, including fines of up to $250,000 per day for NYDFS violations.
By diligently monitoring and adapting security practices, hedge fund managers can ensure their software remains secure and compliant within a rapidly changing regulatory landscape.
Conclusion
Incorporating security into software development is essential for hedge fund managers who aim to protect sensitive financial data and maintain regulatory compliance. By embedding security principles from the outset, organizations can create a robust framework that safeguards their assets and enhances operational integrity. This commitment to secure software development is not merely a technical requirement; it is a strategic necessity in today’s complex financial landscape.
Key practices emphasize the importance of proactive measures, such as:
- Implementing security by design
- Adhering to compliance regulations
- Conducting regular assessments
Strategies like:
- Continuous monitoring
- Secure coding practices
- Engaging third-party experts
are vital for identifying vulnerabilities and mitigating risks. Furthermore, understanding compliance requirements, including SEC regulations and AML protocols, is crucial for maintaining investor trust and avoiding severe penalties.
As the threat landscape continues to evolve, hedge fund managers must prioritize ongoing security measures and adapt their strategies accordingly. By fostering a culture of security awareness and investing in advanced protective technologies, organizations can defend against cyber threats while ensuring compliance with emerging regulations. Embracing these best practices empowers hedge funds to navigate the complexities of software development, safeguarding their operations and enhancing their reputation in the financial sector.
Frequently Asked Questions
What is the importance of integrating security from the start of software development?
Integrating security from the start ensures that safety considerations are part of the initial design phase, allowing for threat modeling and identification of potential vulnerabilities before coding begins. This approach makes protection a fundamental element rather than an afterthought.
What does the principle of least privilege access entail?
The principle of least privilege (PoLP) ensures that users and systems have only the minimum level of access necessary for their functions, which mitigates the risk of unauthorized access and limits potential damage from compromised credentials.
What are secure coding practices?
Secure coding practices involve establishing coding standards that prioritize security, including input validation, error handling, and robust authentication mechanisms. These practices help reduce common vulnerabilities that attackers might exploit.
Why is routine protection testing necessary in software development?
Routine protection testing, such as penetration testing and code reviews, is necessary to identify and address vulnerabilities early in the development process. Frequent assessments help maintain the integrity of software, especially as 71% of organizations issue updates at least weekly.
What is the role of continuous monitoring in software security?
Continuous monitoring involves the ongoing observation of applications to identify and respond to incidents in real-time. This proactive approach is crucial in today’s rapidly evolving threat landscape, allowing organizations to quickly identify and address vulnerabilities.
How can hedge fund managers benefit from incorporating these security principles?
By incorporating these principles into the development process, hedge fund managers can create secure software that effectively safeguards sensitive financial information, thereby enhancing their overall security posture.
List of Sources
- Integrate Security from the Start: Principles of Secure Software Development
- paloaltonetworks.com (https://paloaltonetworks.com/cyberpedia/what-is-the-principle-of-least-privilege)
- Key Cyber Security Statistics for 2026 (https://sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics)
- 30 SSCS statistics that matter for software security teams | ReversingLabs (https://reversinglabs.com/blog/software-supply-chain-security-by-the-numbers-30-key-stats-that-matter)
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Understand Compliance Requirements: Navigating Regulations in Software Development
- SEC.gov | SEC Proposes Amendments to the Small Entity Definitions for Investment Companies and Investment Advisers for Purposes of the Regulatory Flexibility Act (https://sec.gov/newsroom/press-releases/2026-1-sec-proposes-amendments-small-entity-definitions-investment-companies-investment-advisers-purposes)
- AML for Private Equity & Hedge Funds: Are Investors at Risk? (https://riddlecompliance.com/aml-for-private-equity-hedge-funds-are-investors-at-risk)
- Case Studies – ACA Group (https://acaglobal.com/resources/case-studies)
- The Power Of Evidence: AML Case Studies Reinforcing The Need For Compliance (https://financialcrimeacademy.org/aml-case-studies)
- The biggest AML blunders: 6 case studies and lessons learned | NorthRow (https://northrow.com/blog/the-biggest-aml-blunders-6-case-studies-and-lessons-learned)
- Implement Best Practices: Strategies for Secure Software Development
- 41 Cybersecurity Quotes to Protect Your Digital Life (https://acecloudhosting.com/blog/cybersecurity-quotes)
- How Financial Services IT Leaders Can Build a Secure, Compliant Software Factory (https://biztechmagazine.com/article/2026/02/how-financial-services-it-leaders-can-build-secure-compliant-software-factory)
- 30 SSCS statistics that matter for software security teams | ReversingLabs (https://reversinglabs.com/blog/software-supply-chain-security-by-the-numbers-30-key-stats-that-matter)
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- Monitor and Evolve: Ensuring Ongoing Security and Compliance
- Majority of hedge funds boosted cybersecurity spending in 2025 (https://cybersecuritydive.com/news/hedge-funds-cybersecurity-spending-2025/809488)
- Cybersecurity Regulations for Financial Services for 2026 and Beyond (https://hypr.com/blog/top-financial-services-cybersecurity-regulations)
- Hedge funds step up cybersecurity spending amid rising threats and regulatory pressure – Hedgeweek (https://hedgeweek.com/hedge-funds-step-up-cybersecurity-spending-amid-rising-threats-and-regulatory-pressure)
- TOP 25 COMPLIANCE QUOTES (of 106) | A-Z Quotes (https://azquotes.com/quotes/topics/compliance.html)
