Introduction
Navigating the landscape of software security audits is crucial for hedge fund managers, particularly in a regulatory environment that demands strict compliance. Understanding essential frameworks and best practices enables these professionals to safeguard sensitive data and enhance operational resilience against cyber threats. As the cybersecurity landscape evolves, it is vital for hedge funds to ensure that their audit practices remain effective and adaptive. This article explores best practices for executing software security audits, providing insights that empower investment managers to stay ahead of emerging risks and regulatory challenges.
Understand Regulatory Requirements for Software Security Audits
Hedge investment managers must familiarize themselves with the regulatory environment governing software security. Key regulations include the SEC’s directives on cybersecurity, which mandate that firms implement measures to safeguard sensitive data. A thorough understanding of these requirements is essential for identifying the specific standards that software systems must adhere to. Regularly reviewing compliance guidelines is crucial for firms to remain compliant with evolving laws.
For instance, the SEC emphasizes the importance of risk assessments, which should be integral components of any software security audit. Additionally, employing frameworks such as NIST and ISO can provide guidance, ensuring that all aspects of security protocols are thoroughly addressed.
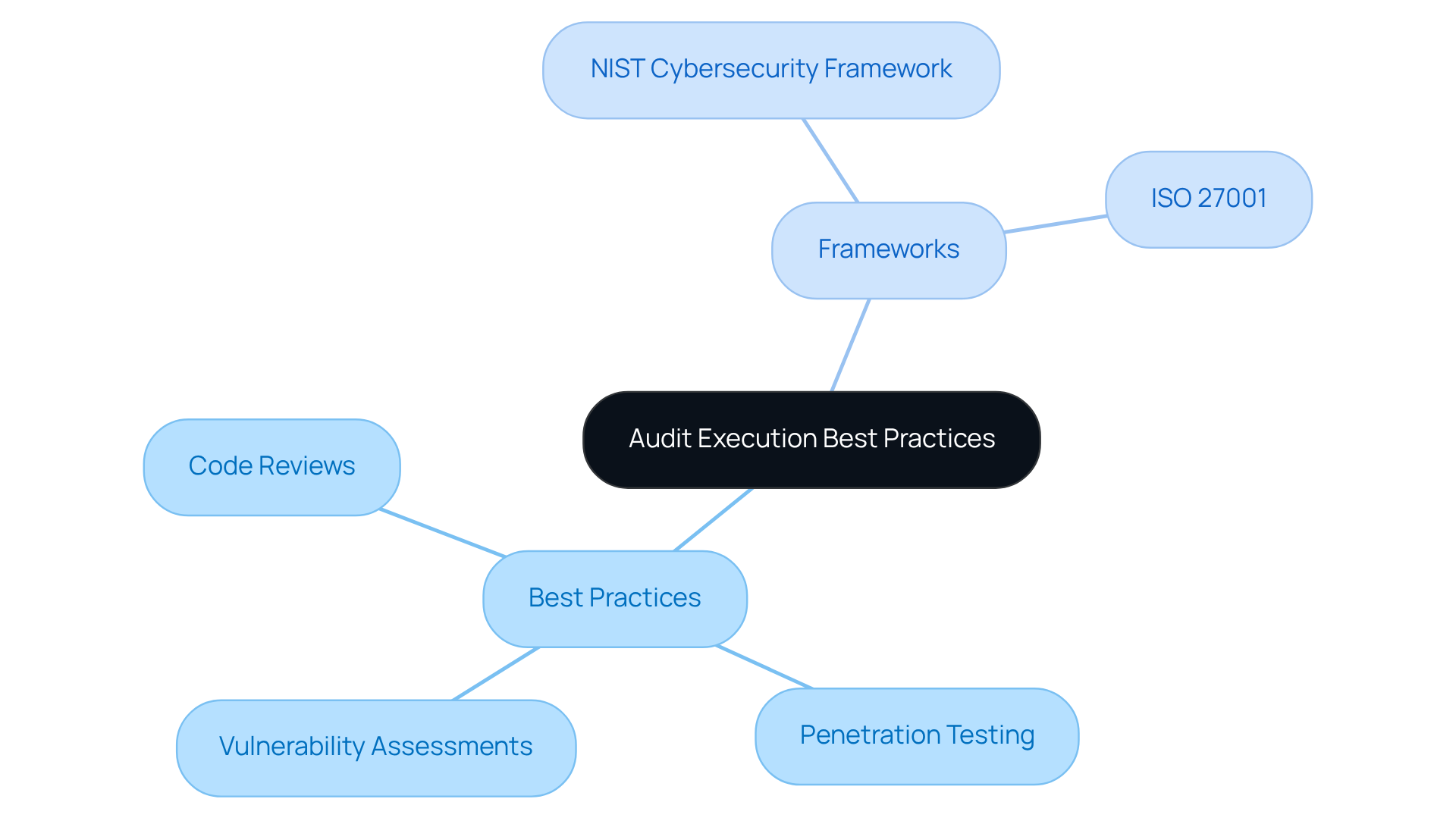
Implement Best Practices and Frameworks for Audit Execution
To conduct effective software protection evaluations, managers must adopt best practices such as:
- Regular assessments
By utilizing established frameworks like the NIST Cybersecurity Framework and ISO 27001, they can systematically identify and mitigate risks. For example, regular security testing can reveal weaknesses in software before they can be exploited; studies show that 73% of successful breaches in the business sector originate from vulnerabilities in web applications.
Furthermore, the integration of automated tools for continuous monitoring enhances the evaluation process by providing immediate insights into vulnerability status. This is particularly crucial given that 67% of U.S. businesses have experienced a breach in the past 24 months, underscoring the need for investment firms to prioritize protective measures.
Establishing a clear review timetable and maintaining detailed records of findings and corrective actions are essential for ensuring compliance, as 75% of information protection firms conduct penetration tests to meet regulatory standards. This proactive approach not only aligns with regulatory expectations but also strengthens the overall protection framework, enabling hedge fund investments to navigate the complexities of software security effectively.
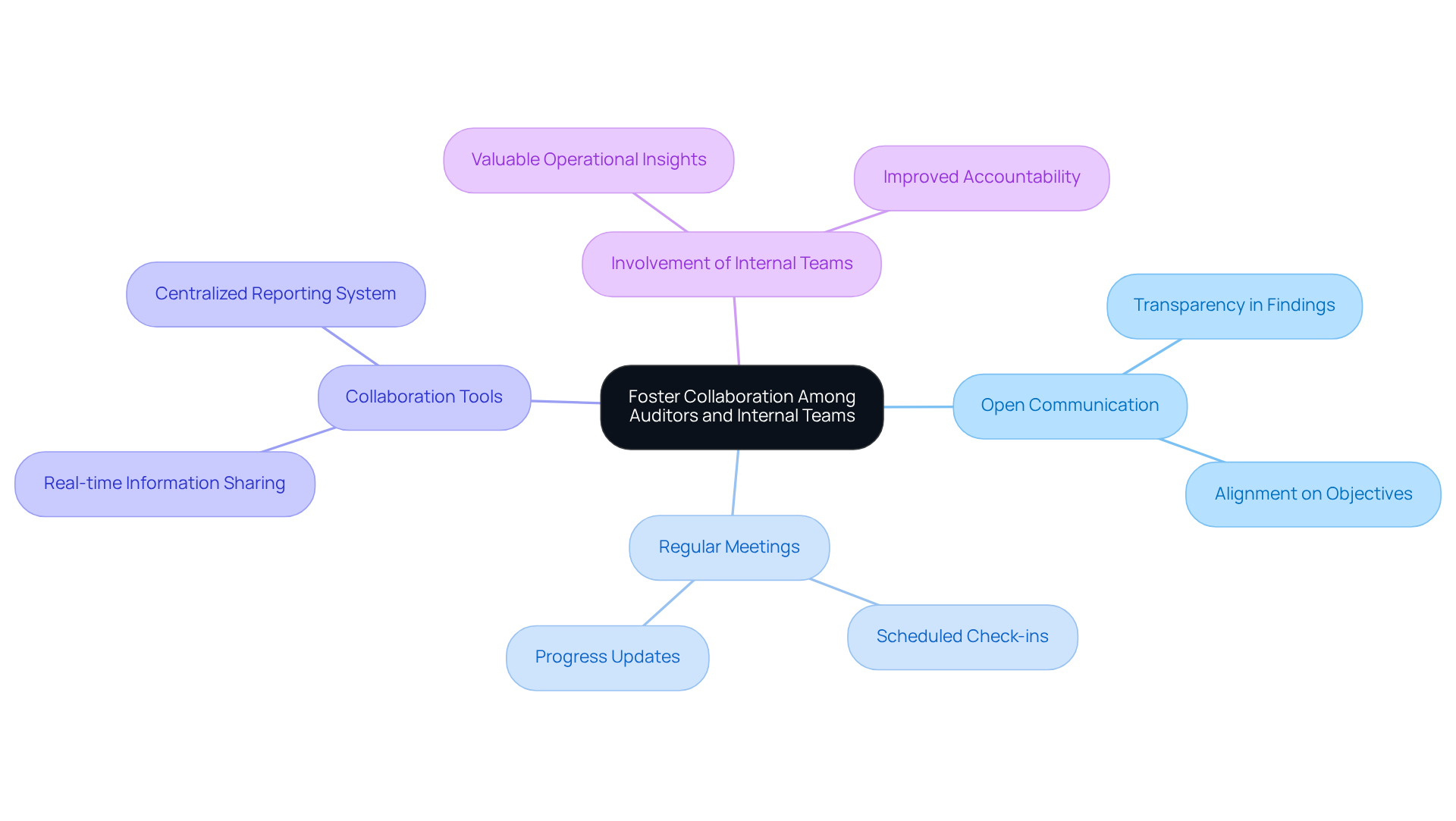
Foster Collaboration Among Auditors and Internal Teams
Cooperation between auditors and internal teams is crucial for the success of software security audits. Hedge fund managers should foster collaboration between auditors and IT staff to ensure alignment on evaluation objectives and findings, enhancing transparency throughout the review process.
For example, establishing a communication framework and monitoring remediation efforts significantly improves accountability and streamlines communication. Involving internal teams in the software security audit not only provides valuable insights but also aids in identifying vulnerabilities, leading to more comprehensive and effective evaluation outcomes.
This approach cultivates a culture of collaboration and continuous improvement in safety practices.
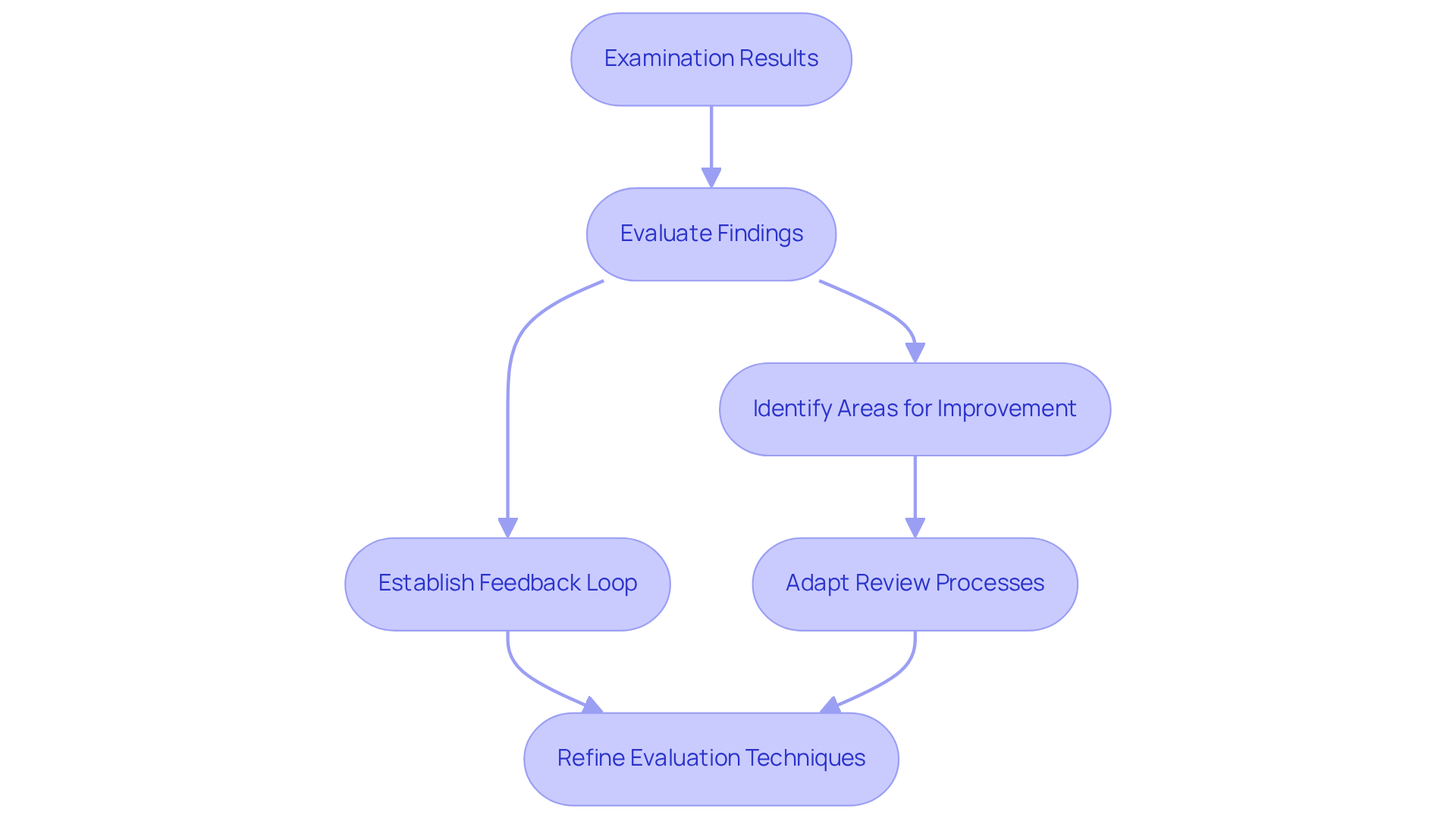
Adapt and Evolve Audit Practices Based on Findings
Hedge fund managers should view examination results as opportunities for enhancement rather than mere compliance assessments. It is essential to evaluate findings after each assessment and identify areas for improvement in security procedures. Establishing a feedback loop, where evaluation results inform future assessment strategies, can lead to more effective security measures. For instance, if a specific vulnerability is repeatedly identified, this may signal a need for additional training for development teams or a review of coding practices.
Moreover, staying informed about industry trends can help adapt their review processes to address new challenges effectively. Continuously refining evaluation techniques based on findings ensures that the organization remains resilient against evolving risks. Notably, eight out of ten investment companies and financial firms increased their security budgets in 2025, underscoring the necessity for ongoing enhancement in protective measures.
Additionally, as illustrated by Innovative Network Solutions, implementing a comprehensive security framework can significantly mitigate risks identified through a security audit. The persistent threats reported by the FBI and vulnerabilities highlighted by Google researchers concerning third-party tools emphasize the importance to integrate best practices, thereby fostering a culture of security awareness.
Conclusion
Hedge fund managers must prioritize mastering software security audits to ensure compliance with evolving regulatory standards and protect sensitive data. By gaining a thorough understanding of the regulatory landscape and implementing best practices, firms can establish a robust framework that safeguards their software systems against cyber threats. This proactive strategy not only meets compliance requirements but also strengthens the overall security posture, which is crucial for navigating the complexities of today’s financial environment.
Key insights highlight the necessity of:
- Regular vulnerability assessments
- Effective collaboration between auditors and internal teams
- A commitment to continuous improvement based on audit findings
By adopting established frameworks such as NIST and ISO, and promoting open communication, hedge funds can systematically identify and mitigate risks. This approach leads to more comprehensive evaluations and fortified defenses against cyber threats.
As the cybersecurity landscape evolves, it is essential for hedge fund managers to remain vigilant and adaptable. Embracing a culture of continuous improvement and leveraging insights from past audits can significantly enhance security measures. By prioritizing these best practices, hedge funds not only fulfill regulatory requirements but also strengthen their defenses against emerging threats, ensuring long-term resilience in an increasingly complex environment.
Frequently Asked Questions
What are the key regulatory requirements for software security audits in hedge investment management?
Hedge investment managers must understand the SEC’s directives on cybersecurity, which require firms to implement strong protective measures for sensitive data.
Why is it important for hedge funds to stay updated on regulatory changes?
Regularly reviewing updates from regulatory bodies is essential for hedge funds to remain compliant with evolving laws and to ensure that their software systems meet specific compliance standards.
What components should be included in a software security audit according to the SEC?
The SEC emphasizes the importance of risk evaluations and incident response strategies as integral components of any software security audit.
Which frameworks can be employed to ensure compliance in software security audits?
Frameworks such as NIST (National Institute of Standards and Technology) and ISO (International Organization for Standardization) can provide structured approaches for compliance in software security audits.
List of Sources
- Understand Regulatory Requirements for Software Security Audits
- Case Study: Hedge Fund Faces Compliance Confusion (https://inscnet.com/case-studies/hedge-fund-faces-compliance-confusion)
- New SEC Regulation S‑P Amendments: Impact on Private Fund Managers (https://eisneramper.com/insights/financial-services/sec-regulation-s-p-private-fund-1225)
- sec.gov (https://sec.gov/newsroom/press-releases/2025-132-sec-division-examinations-announces-2026-priorities)
- SEC’s new cyber-security rules put boards on the hook | Governance Intelligence (https://governance-intelligence.com/regulatory-compliance/secs-new-cyber-security-rules-put-boards-hook)
- Implement Best Practices and Frameworks for Audit Execution
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- 120+ Penetration Testing Statistics for 2026 (https://brightdefense.com/resources/penetration-testing-statistics)
- 83 Penetration Testing Statistics: Key Facts and Figures (https://getastra.com/blog/security-audit/penetration-testing-statistics)
- 205 Cybersecurity Stats and Facts for 2026 (https://vikingcloud.com/blog/cybersecurity-statistics)
- Foster Collaboration Among Auditors and Internal Teams
- 9 Quotes that Capture the State of Offensive Security (https://netspi.com/blog/executive-blog/security-industry-trends/quotes-on-the-state-of-offensive-security)
- diligent.com (https://diligent.com/resources/blog/top-20-quotes-cyber-risk-virtual-summit)
- solutionsreview.com (https://solutionsreview.com/cybersecurity-awareness-month-quotes-and-commentary-from-industry-experts-in-2025)
- Cybersecurity Quotes That Define the Future of Digital Protection (https://medium.com/@cyberpromagazine/cybersecurity-quotes-that-define-the-future-of-digital-protection-64897c07bfc6)
- Adapt and Evolve Audit Practices Based on Findings
- Case Study: Hedge Fund Faces Compliance Confusion (https://inscnet.com/case-studies/hedge-fund-faces-compliance-confusion)
- Majority of hedge funds boosted cybersecurity spending in 2025 (https://cybersecuritydive.com/news/hedge-funds-cybersecurity-spending-2025/809488)
- The audit feedback loop: Audit season’s critical, but overlooked final step — Thoropass (https://thoropass.com/blog/the-audit-feedback-loop)
