Introduction
The rapid expansion of the Internet of Things (IoT) is reshaping industries, with projections suggesting that the market could reach $1 trillion by 2025. As organizations seek to leverage the potential of connected devices, it is essential to understand the core components of IoT software. This understanding is crucial for developing secure and scalable solutions.
However, alongside the promise of innovation lies the challenge of addressing security vulnerabilities and ensuring that systems can adapt to future demands. Developers must consider how to implement best practices that not only enhance security but also guarantee scalability in this dynamic landscape.
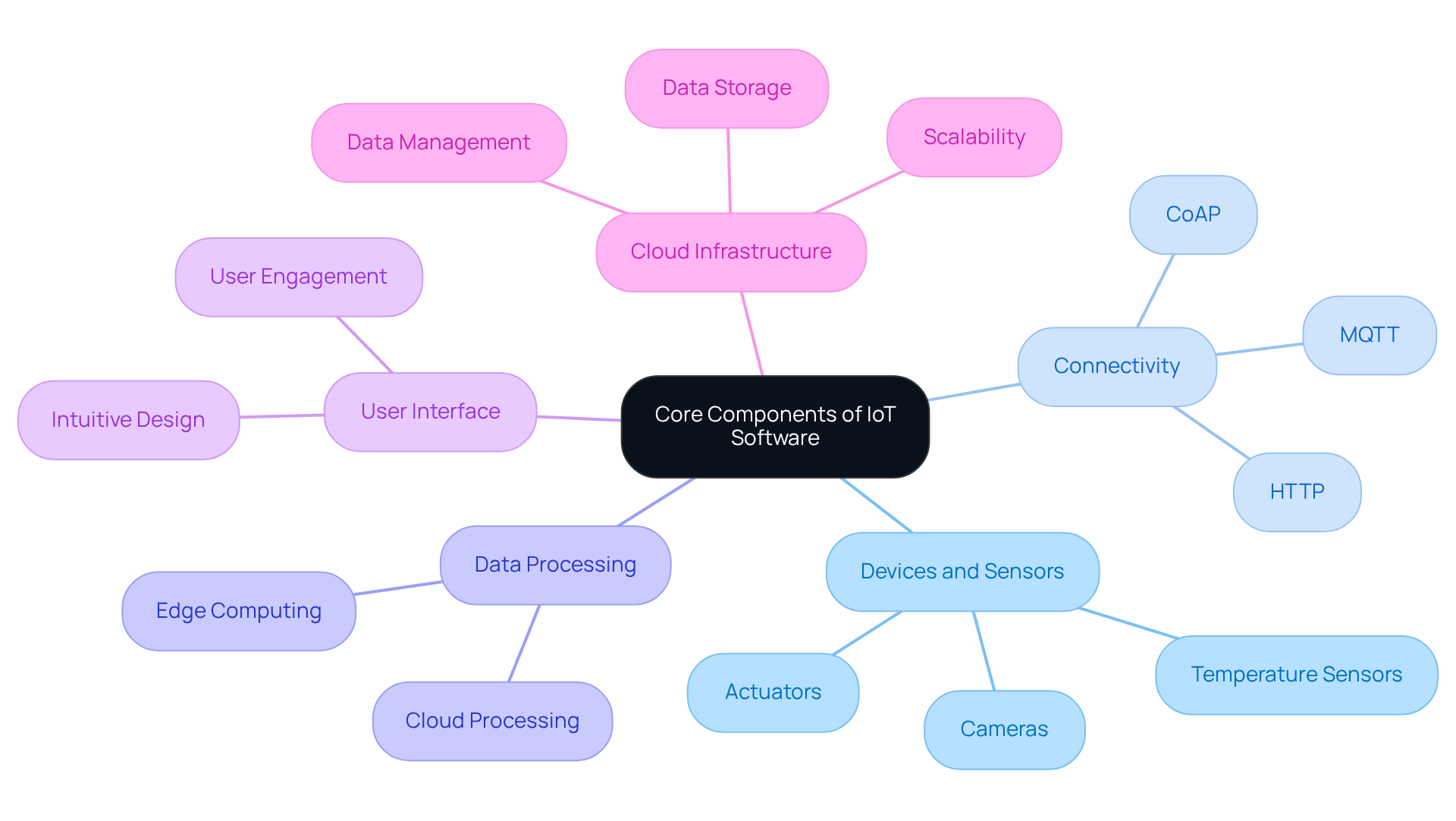
Identify Core Components of IoT Software
To effectively develop IoT software, it is essential to identify and understand its core components:
-
Devices and Sensors: These physical components collect data from the environment, ranging from simple temperature sensors to advanced cameras and actuators. Their role is crucial, as they form the foundation of any IoT system.
-
Connectivity: This encompasses the communication protocols that enable equipment to connect to the internet or other networks. Common protocols include MQTT, HTTP, and CoAP, each serving specific use cases and requirements.
-
Data Processing: After data collection, processing is necessary. This can occur on the hardware itself through edge computing or in the cloud, depending on the application’s needs. The choice between these methods impacts latency and efficiency.
-
User Interface: An intuitive interface is essential for effective engagement with the IoT system, enabling users to monitor and manage equipment seamlessly. This enhances user experience and operational efficiency.
-
Cloud Infrastructure: This component is where information is stored, analyzed, and managed. Cloud services offer the scalability and adaptability required to manage the extensive quantities of information produced by IoT technologies, with organizations progressively embracing cloud infrastructure for their software IoT solutions.
According to industry forecasts, the IoT market is predicted to attain $1 trillion by 2025, with the count of connected IoT units expected to rise to 39 billion by 2030. Understanding these components enables developers to create robust and scalable IoT solutions that effectively meet user needs. As Michael S. Blanco states, “IoT is all about the interconnectivity of physical gadgets and their usage as a source of data for AI and ML to feed upon, while AI and ML are the ones to process the data.” Furthermore, developers should be aware of common pitfalls in IoT development, such as security challenges related to equipment and fragmented standards. As the IoT landscape evolves, integrating advanced technologies and ensuring security will be paramount for successful deployments.
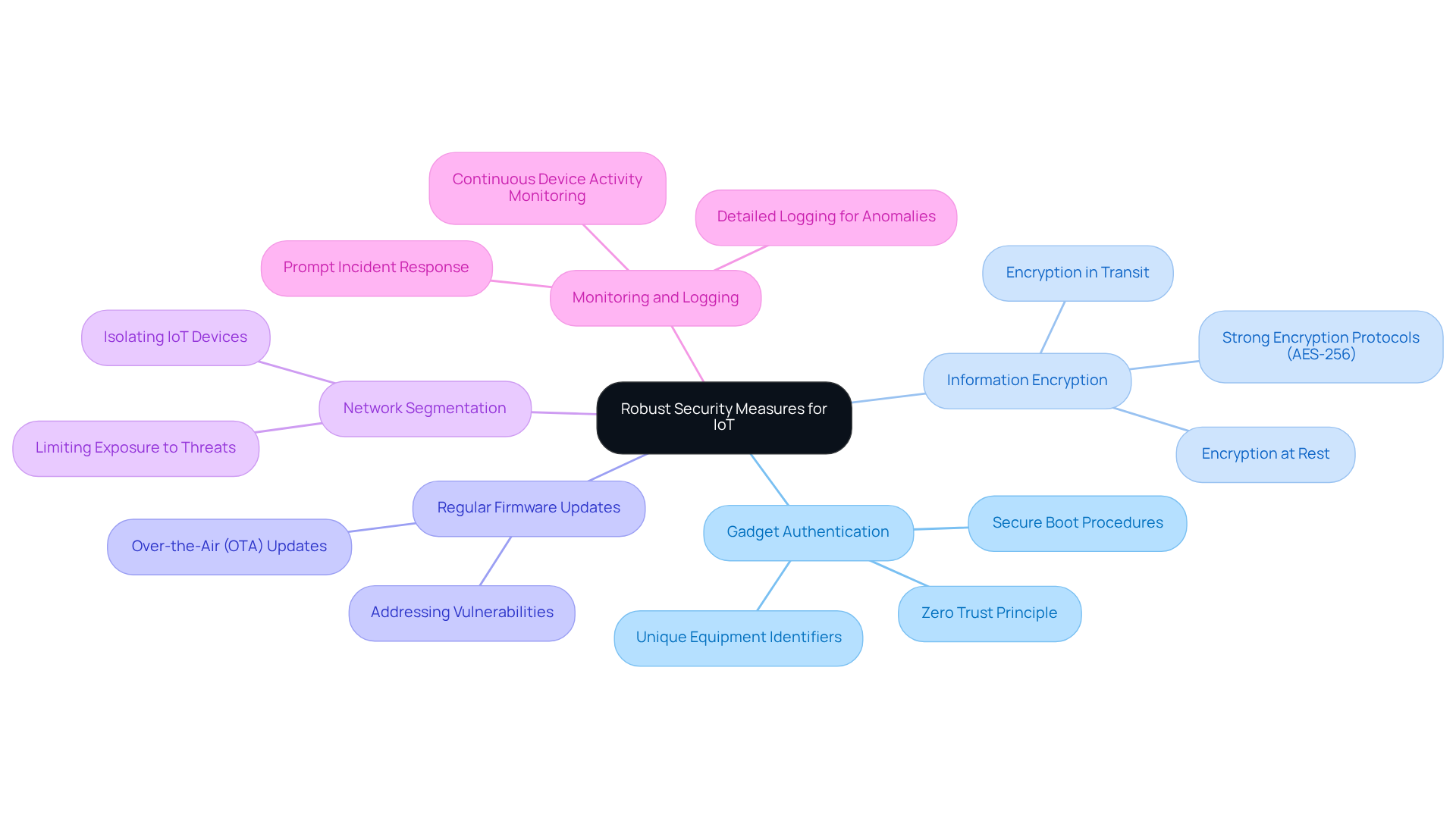
Implement Robust Security Measures
To secure software IoT systems effectively, it is paramount to implement a multi-layered security approach. Key strategies include:
-
Gadget Authentication: All gadgets must be verified before linking to the network. This can be accomplished through secure boot procedures and unique equipment identifiers, ensuring that only trusted units gain access. As emphasized in the principle of zero trust, every IoT device should be treated as untrusted until proven otherwise.
-
Information Encryption: Encrypting information both in transit and at rest is essential to protect sensitive details from unauthorized access. Utilizing strong encryption protocols, such as AES-256, fortifies data security.
-
Regular Firmware Updates: Keeping firmware current is essential for addressing vulnerabilities. Implementing over-the-air (OTA) updates streamlines this process, ensuring equipment is safeguarded against emerging threats.
-
Network Segmentation: Isolating IoT equipment on separate networks limits exposure to potential threats. This strategy helps contain breaches and protects essential networks from widespread attacks.
-
Monitoring and Logging: Continuous monitoring of device activity and maintaining detailed logs are vital for detecting anomalies. Prompt responses to potential security incidents can significantly mitigate risks.
Statistics show that 60% of all breaches involve the human element, highlighting the necessity for robust authentication measures. By implementing these strong security measures, organizations can significantly lower the risk of cyber threats and uphold the integrity of their networks, particularly in the context of software IoT.
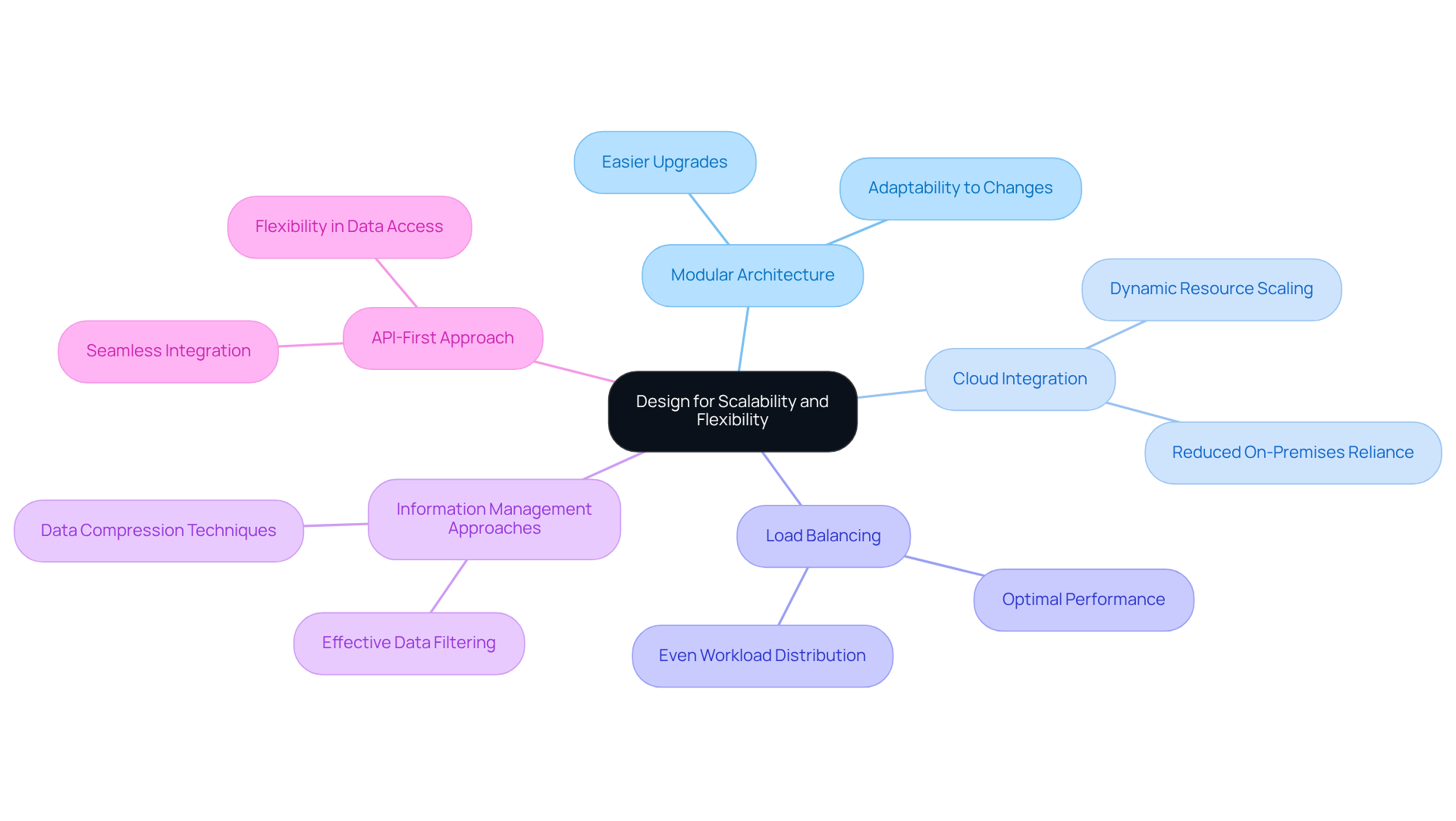
Design for Scalability and Flexibility
Creating scalable and flexible software IoT solutions is essential for long-term success. To achieve this, organizations should consider the following best practices:
-
Modular Architecture: Implement a modular design that allows for the addition or removal of components as necessary. This approach facilitates easier upgrades and maintenance, ensuring that the system can adapt to changing requirements.
-
Cloud Integration: Leverage cloud services for information storage and processing. This enables dynamic scaling of resources based on demand, significantly reducing the reliance on on-premises infrastructure.
-
Load Balancing: Employ load balancing techniques to distribute workloads evenly across servers. This ensures optimal performance during peak usage times, enhancing the overall efficiency of the IoT network.
-
Information Management Approaches: Utilize effective information handling techniques, such as compression and filtering, to manage large volumes of data without overwhelming the infrastructure. This is crucial for maintaining system performance and reliability.
-
API-First Approach: Develop APIs that facilitate seamless integration with other platforms and services. This allows for greater flexibility in how data is accessed and utilized, supporting diverse operational needs.
By adhering to these practices, organizations can create networks using software IoT that not only meet current demands but are also well-prepared for future expansion.
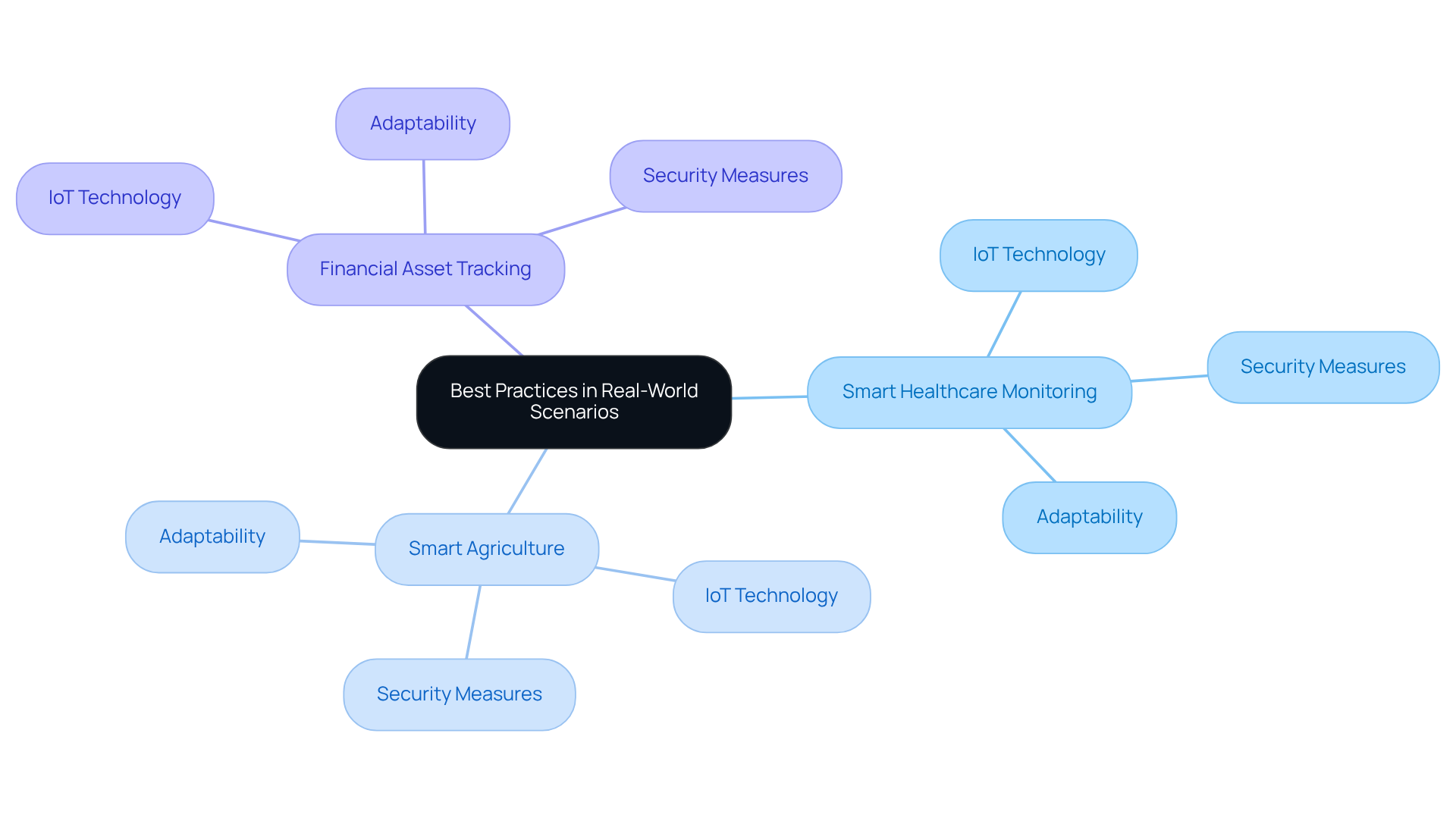
Apply Best Practices in Real-World Scenarios
To illustrate the effectiveness of the discussed best practices, consider the following real-world scenarios:
-
Smart Healthcare Monitoring: A healthcare provider implemented IoT technology to monitor patient vitals remotely. By employing modular architecture and cloud integration, they expanded their infrastructure using software IoT to support thousands of devices. This approach ensured information security through encryption and regular updates.
-
Smart Agriculture: An agricultural company utilized IoT sensors to monitor soil conditions and crop health. They designed their system with flexibility in mind, allowing for the easy integration of new sensors as technology advanced. This adaptability improved their yield and reduced costs.
-
Financial Asset Tracking: A hedge fund leveraged IoT technology to track assets in real-time. By implementing robust security measures and ensuring data integrity through encryption, they maintained compliance with regulatory standards while enhancing operational efficiency.
These examples demonstrate how the application of best practices can lead to successful implementations of software IoT that are secure, scalable, and adaptable to changing needs.
Conclusion
The successful development of software for the Internet of Things (IoT) relies on a thorough understanding of its essential components, robust security measures, and a design approach that emphasizes scalability and flexibility. By integrating these elements, organizations can create IoT solutions that are effective and resilient against emerging threats while being adaptable to future demands.
Key insights highlight the necessity of identifying core components, including:
- devices and sensors
- connectivity protocols
- data processing methods
- user interfaces
- cloud infrastructure
Furthermore, implementing stringent security practices-such as device authentication, data encryption, and regular firmware updates-ensures that IoT systems remain secure. Additionally, adopting a modular architecture and leveraging cloud services provide the scalability and flexibility required to meet evolving business needs.
Ultimately, the effective deployment of IoT solutions demands a proactive approach to security and a commitment to established best practices in design and implementation. As the IoT landscape continues to grow, embracing these strategies will enhance operational efficiency and protect critical data and infrastructure. Organizations must prioritize these practices to thrive in a rapidly changing technological environment and fully harness the potential of IoT innovations.
Frequently Asked Questions
What are the core components of IoT software?
The core components of IoT software include devices and sensors, connectivity, data processing, user interface, and cloud infrastructure.
What role do devices and sensors play in IoT systems?
Devices and sensors are physical components that collect data from the environment, ranging from simple temperature sensors to advanced cameras and actuators. They form the foundation of any IoT system.
What is meant by connectivity in IoT?
Connectivity refers to the communication protocols that enable equipment to connect to the internet or other networks. Common protocols include MQTT, HTTP, and CoAP, each serving specific use cases and requirements.
How is data processed in IoT applications?
Data processing can occur on the hardware itself through edge computing or in the cloud, depending on the application’s needs. The choice between these methods affects latency and efficiency.
Why is a user interface important in IoT systems?
An intuitive user interface is essential for effective engagement with the IoT system, allowing users to monitor and manage equipment seamlessly, which enhances user experience and operational efficiency.
What is the significance of cloud infrastructure in IoT?
Cloud infrastructure is where information is stored, analyzed, and managed. It offers the scalability and adaptability needed to handle the extensive data produced by IoT technologies.
What are the predictions for the IoT market?
The IoT market is predicted to reach $1 trillion by 2025, with the number of connected IoT units expected to rise to 39 billion by 2030.
What are some common pitfalls in IoT development?
Common pitfalls in IoT development include security challenges related to equipment and fragmented standards.
How do AI and ML relate to IoT?
AI and ML process the data collected by IoT devices, enhancing the interconnectivity of physical gadgets and their usage as a source of data.
