Best Practices for Financial Software Application Development Security

Introduction
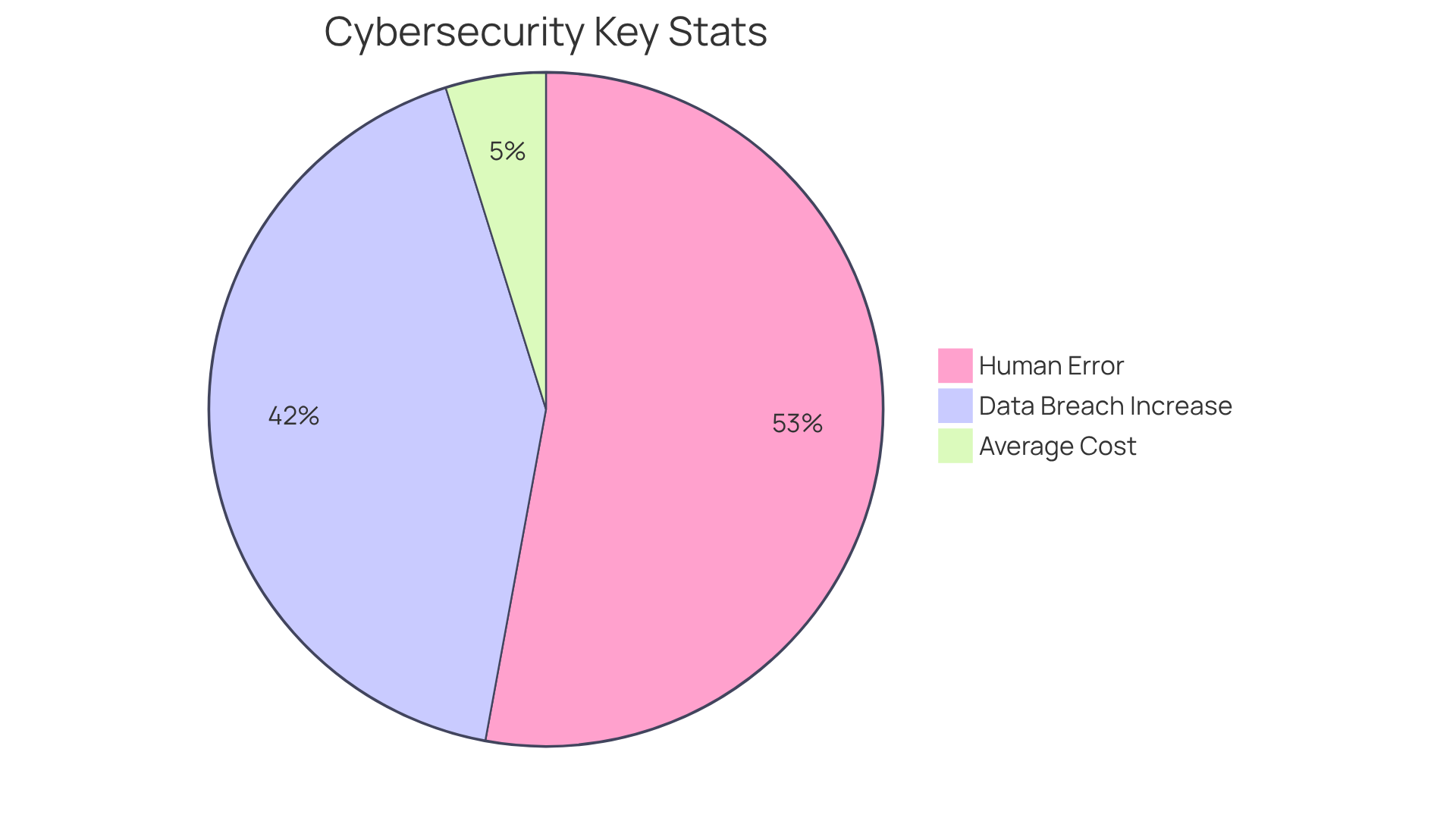
In an era where financial institutions increasingly face cyberattacks, the significance of security in software application development is paramount. Recent statistics indicate a staggering 72% rise in data breaches, compelling organizations to confront not only financial consequences but also a considerable erosion of customer trust. This article explores best practices for ensuring robust security and compliance in financial software development, providing developers with strategies to safeguard sensitive data and navigate intricate regulatory landscapes.
How can organizations effectively incorporate advanced technologies and proactive measures to protect their applications from evolving threats?
Understand the Importance of Security and Compliance in Financial Software Development
In the financial services sector, the integrity and protection of software applications are paramount. Financial institutions handle sensitive information, including personal details and transaction specifics, making them prime targets for cyberattacks. The repercussions of overlooking safety can be severe, resulting in information breaches that cost organizations an average of $8.19 million per incident in 2023, along with regulatory penalties and considerable loss of customer confidence. Notably, data breaches increased by 72% in 2023, with over 3,205 incidents impacting more than 353 million Americans, underscoring the urgent need for robust protective measures.
Integrating protection and adherence into the software development lifecycle is essential. Compliance with regulations such as GDPR and PCI DSS is crucial, as these frameworks are designed to safeguard consumers and ensure that institutions operate transparently and securely. By prioritizing safety and compliance, organizations can mitigate risks, enhance their reputation, and maintain a competitive edge in the market. Furthermore, it is important to recognize that 90% of all cyber incidents stem from human error or behavior, highlighting the necessity for proactive measures. The economic sector must acknowledge that the cost of inaction far outweighs the investment in secure development practices. Additionally, organizations utilizing AI and automation for protection have detected and managed breaches 80 days faster and saved nearly $1.9 million compared to those without such applications, emphasizing the critical importance of investing in advanced protective measures.
Implement Robust Security Measures to Protect Sensitive Data
To safeguard sensitive information in financial software application development, developers must implement a comprehensive multi-layered security strategy. This strategy encompasses several key components:
-
Information Encryption: It is essential to utilize robust encryption standards, such as AES-256, to secure sensitive information both at rest and in transit. This practice ensures that intercepted data remains unreadable, significantly mitigating the risk of unauthorized access. As Rich Crawford articulates, “Data encryption serves as your first and most critical line of defense in information protection.”
-
Access Controls: Stringent access controls must be established to limit who can view or manipulate sensitive information. Role-based access control (RBAC) effectively ensures that only authorized personnel can access critical data, thereby minimizing exposure to potential breaches.
-
Multi-Factor Authentication (MFA): Enforcing MFA for all users accessing the application adds a vital layer of protection. This requirement compels users to provide two or more verification factors, making unauthorized access considerably more challenging. Given that 79% of organizations experienced attempted or actual payments fraud in 2024, the significance of MFA cannot be overstated.
-
Regular Safety Audits: Frequent assessments and vulnerability evaluations are necessary to identify and rectify potential weaknesses within the application. This proactive approach is crucial for maintaining a strong security posture against evolving threats, particularly as privacy regulations are projected to encompass 70-75% of the global population by the end of 2026.
-
Secure APIs: It is imperative that all APIs integrated into the application adhere to best practices for authentication and information handling. Secure APIs play a critical role in safeguarding information exchanges and preventing unauthorized access.
By implementing these best practices in financial software application development, banking organizations can significantly diminish the risk of data breaches and enhance the overall protection of their applications. As the landscape of monetary technology evolves, it is vital to stay ahead of security trends, such as the increasing adoption of multi-factor authentication, to maintain trust and compliance in a highly regulated environment.

Adhere to Regulatory Standards for Compliance and Risk Management
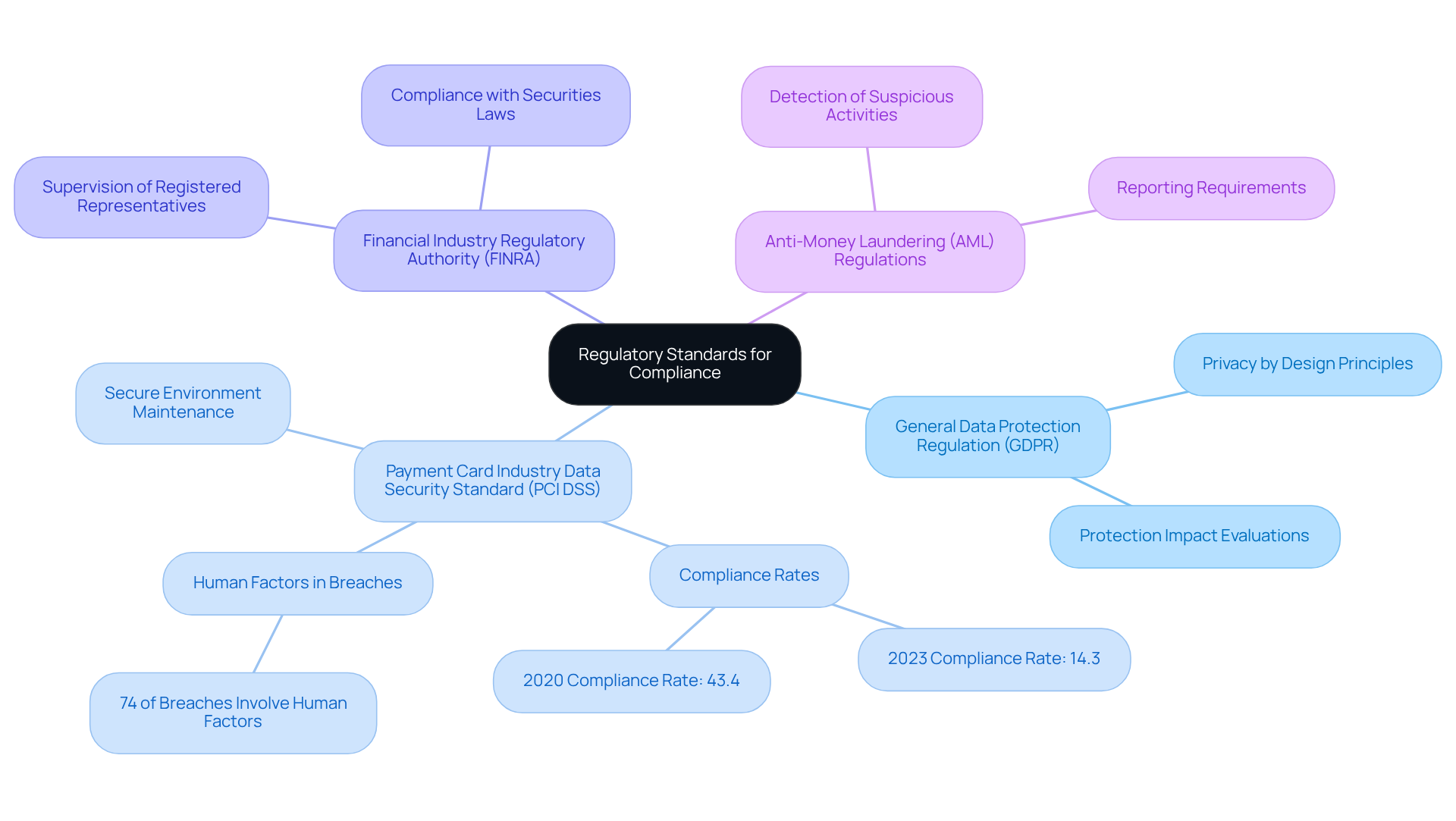
Compliance with regulatory standards is essential in the financial services industry, as adherence to key regulations safeguards both organizations and their customers. Developers must prioritize the following regulations:
-
General Data Protection Regulation (GDPR): This regulation enforces stringent protection measures for the personal information of EU citizens. Organizations must apply privacy by design principles and perform protection impact evaluations to ensure compliance.
-
Payment Card Industry Data Security Standard (PCI DSS): This standard is critical for any organization handling credit card information. It requires the maintenance of a secure environment to protect cardholder information. Alarmingly, adherence rates are disturbingly low; only 14.3% of organizations were fully PCI compliant in 2023, a significant drop from 43.4% in 2020. By 2026, the urgency for compliance will increase, as non-compliance can result in severe penalties and reputational damage. Furthermore, 74% of breaches involve human factors, underscoring the importance of training and awareness in regulatory efforts.
-
Financial Industry Regulatory Authority (FINRA): FINRA regulations require firms to establish robust systems to supervise the activities of their registered representatives, ensuring compliance with securities laws and protecting investors.
-
Anti-Money Laundering (AML) Regulations: Institutions must implement measures to detect and report suspicious activities indicative of money laundering or fraud, thereby reinforcing the integrity of the economic system.
By adhering to these regulations, software developers involved in financial software application development can mitigate legal risks and enhance customer trust, positioning their applications as secure and compliant in a rapidly evolving regulatory landscape. Additionally, compliance can be leveraged as a strategic advantage, transforming it from a mere barrier to innovation into a tool for building trust and reducing risk across various markets.
Leverage Advanced Technologies for Enhanced Security and Compliance
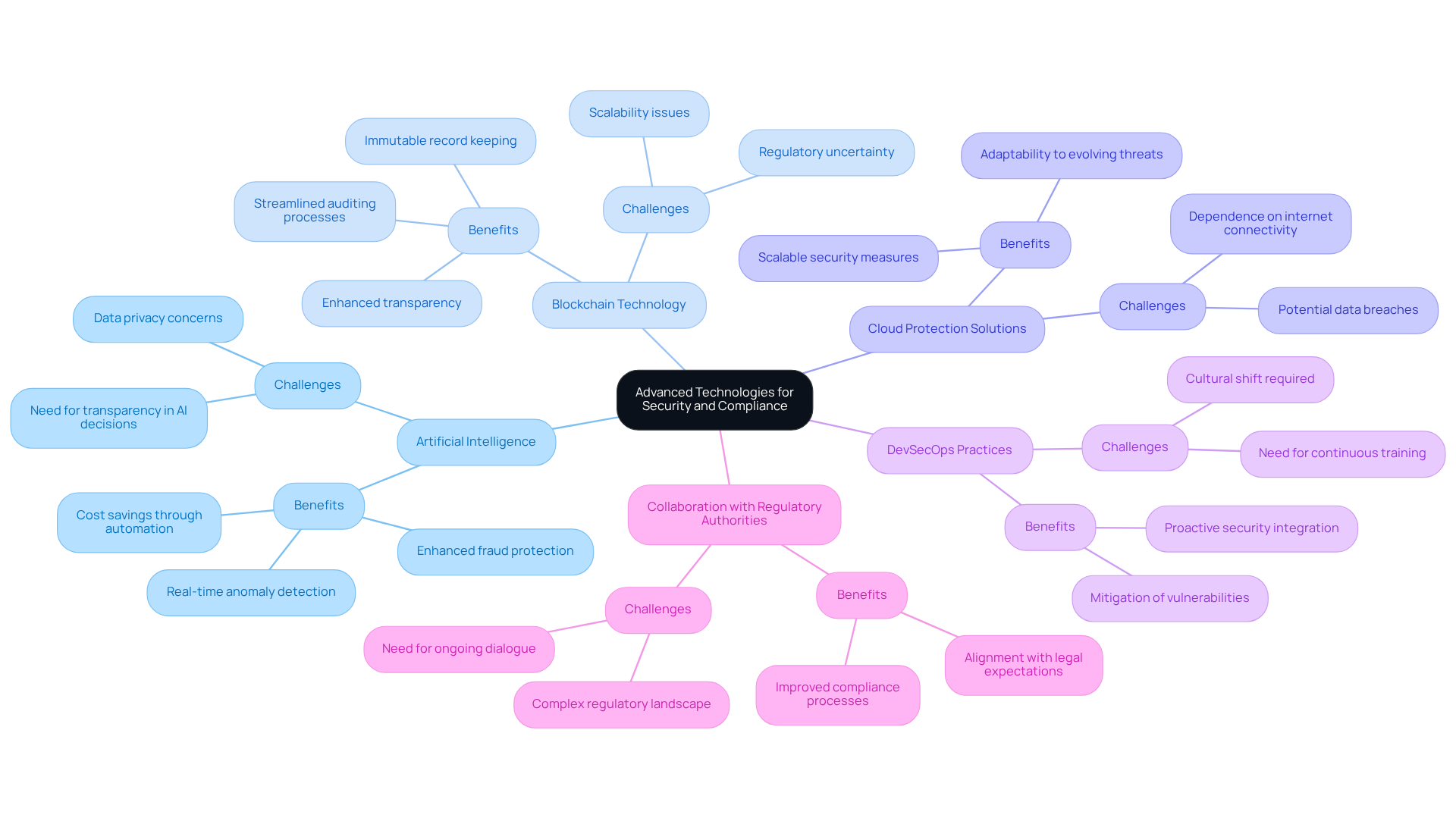
Integrating advanced technologies into financial software application development significantly enhances protection and compliance efforts. Key technologies to consider include:
-
Artificial Intelligence (AI): AI is essential for identifying anomalies and potential risks in real-time, allowing organizations to respond swiftly to breaches. Its ability to process large volumes of information quickly provides timely insights, which are critical for maintaining robust security measures. Notably, AI is projected to contribute $15.7 trillion to the global economy by 2030, underscoring its transformative potential across various sectors, including finance.
-
Blockchain Technology: Blockchain provides a secure and transparent method for documenting transactions, making it nearly impossible for unauthorized individuals to alter information. This immutability fosters trust and enhances compliance in financial transactions. For instance, implementing blockchain can streamline auditing processes, granting regulators real-time access to verified information and thereby improving overall compliance. However, challenges such as scalability and regulatory uncertainty must be addressed to fully harness blockchain’s advantages.
-
Cloud Protection Solutions: Employing cloud-based protection options offers scalable and adaptable measures, enabling organizations to respond to evolving threats and compliance requirements. This flexibility is crucial in an environment where regulatory frameworks are constantly changing.
-
DevSecOps Practices: Integrating security into the DevOps process ensures that safety considerations are embedded at every stage of development, from design to deployment. This proactive approach mitigates vulnerabilities and enhances the overall security posture of financial software application development.
-
Collaboration with Regulatory Authorities: Engaging with regulatory authorities is vital for ensuring compliance and navigating the complexities of financial regulations. This collaboration aids organizations in aligning their practices with legal expectations and industry standards.
By leveraging these technologies, financial institutions can not only fortify their security frameworks but also streamline regulatory processes, facilitating easier compliance with requirements. The integration of blockchain technology, in particular, is anticipated to transform compliance in finance by enhancing transparency and efficiency, making it a crucial element for organizations aiming to succeed in 2026 and beyond.
Conclusion
In the realm of financial software application development, prioritizing security and compliance is essential. Financial institutions face increasing cyber threats and stringent regulatory frameworks, making robust protective measures crucial. Integrating security practices throughout the development lifecycle safeguards sensitive information against potential breaches, fostering trust among customers and stakeholders.
This article highlights key strategies for enhancing security, including:
- Multi-layered security measures
- Adherence to regulatory standards
- Adoption of advanced technologies
Employing encryption and access controls, along with leveraging artificial intelligence and blockchain, forms a comprehensive approach to risk management. Additionally, regular audits and collaboration with regulatory authorities are vital for maintaining compliance and adapting to evolving threats.
The financial services sector stands at a critical juncture where the stakes of security and compliance are higher than ever. Organizations must take proactive steps to implement these best practices, not only to protect sensitive data but also to position themselves as leaders in a competitive market. By embracing a culture of security and compliance, financial institutions can mitigate risks, enhance their reputation, and build customer trust, paving the way for sustainable success in the ever-evolving landscape of financial technology.
Frequently Asked Questions
Why is security and compliance important in financial software development?
Security and compliance are crucial in financial software development because financial institutions handle sensitive information, making them prime targets for cyberattacks. Overlooking safety can lead to severe repercussions, including costly information breaches and regulatory penalties.
What are the financial implications of data breaches in 2023?
In 2023, the average cost of a data breach for organizations was $8.19 million per incident. Additionally, data breaches increased by 72%, affecting over 353 million Americans.
What regulations should financial institutions comply with?
Financial institutions should comply with regulations such as GDPR (General Data Protection Regulation) and PCI DSS (Payment Card Industry Data Security Standard) to safeguard consumers and ensure transparency and security.
How can organizations mitigate risks in financial software development?
Organizations can mitigate risks by integrating protection and compliance into the software development lifecycle, prioritizing safety measures, and investing in secure development practices.
What percentage of cyber incidents are caused by human error?
Approximately 90% of all cyber incidents stem from human error or behavior, highlighting the need for proactive measures in security.
What are the benefits of using AI and automation for security in financial software?
Organizations utilizing AI and automation for protection have detected and managed breaches 80 days faster and saved nearly $1.9 million compared to those without such applications.
What is the cost of inaction regarding security in financial software development?
The cost of inaction regarding security in financial software development far outweighs the investment in secure development practices, emphasizing the importance of proactive security measures.