Introduction
In regulated industries such as finance and healthcare, the stakes for software security are at an all-time high. Stringent compliance requirements, including HIPAA and GDPR, dictate the management of sensitive data, presenting organizations with the dual challenge of ensuring robust protection while navigating complex regulations. This article delves into essential best practices for software testing security, providing insights into tailored methodologies, continuous monitoring, and the integration of security throughout the software development lifecycle.
How can organizations effectively navigate these challenges to enhance their security posture and maintain compliance in an ever-evolving threat landscape?
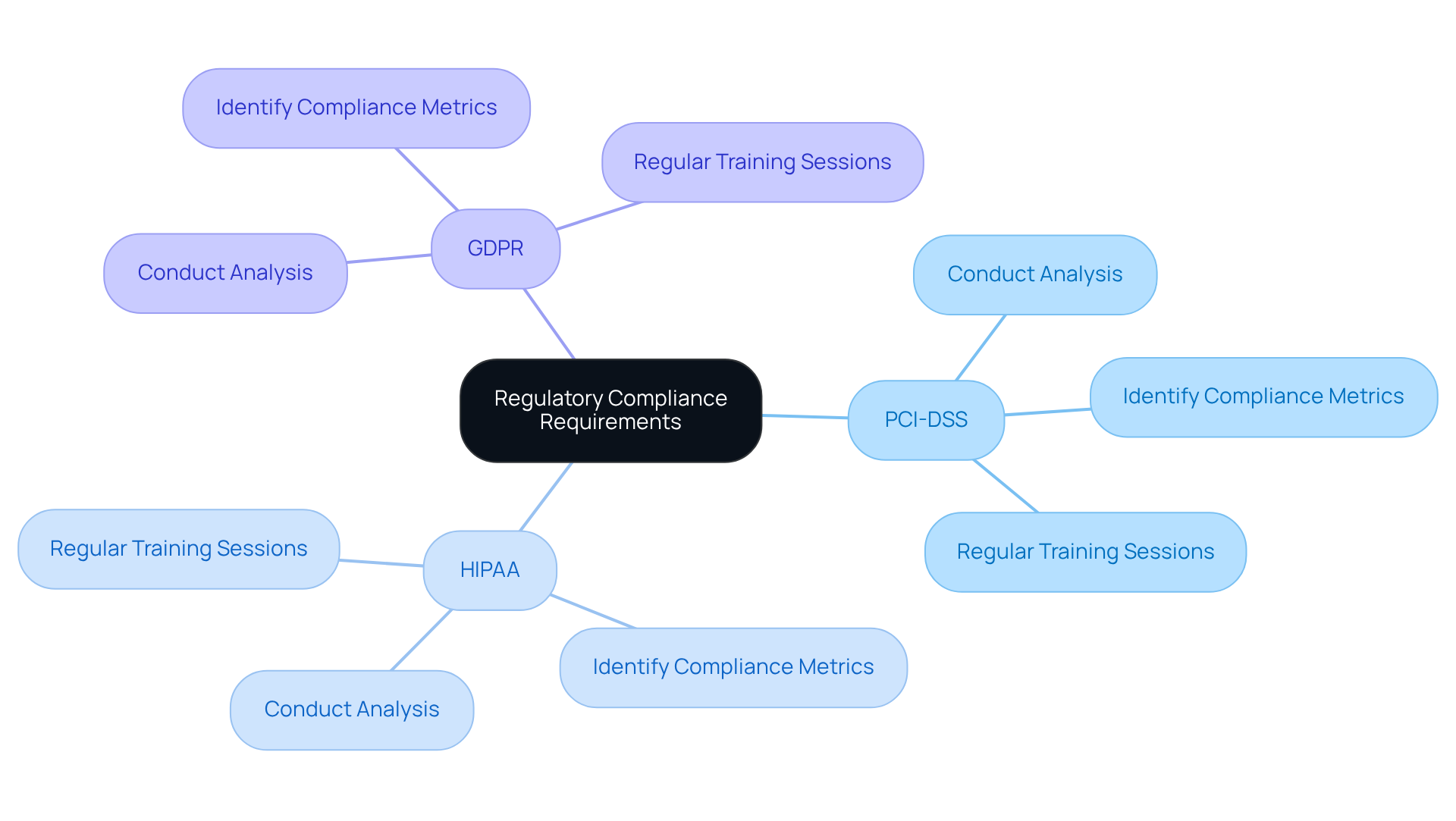
Understand Regulatory Compliance Requirements
In regulated industries such as finance and healthcare, understanding specific compliance requirements is crucial. Regulations like PCI-DSS, HIPAA, and GDPR dictate how data must be handled, stored, and protected. Organizations must conduct a thorough analysis of applicable regulations to ensure their software evaluation processes comply. This involves identifying key compliance metrics and integrating them into the evaluation framework.
For instance, financial organizations must ensure their systems can withstand rigorous evaluations and demonstrate adherence to protective procedures. Additionally, regular training sessions for development and evaluation teams on compliance updates can significantly enhance understanding and implementation.
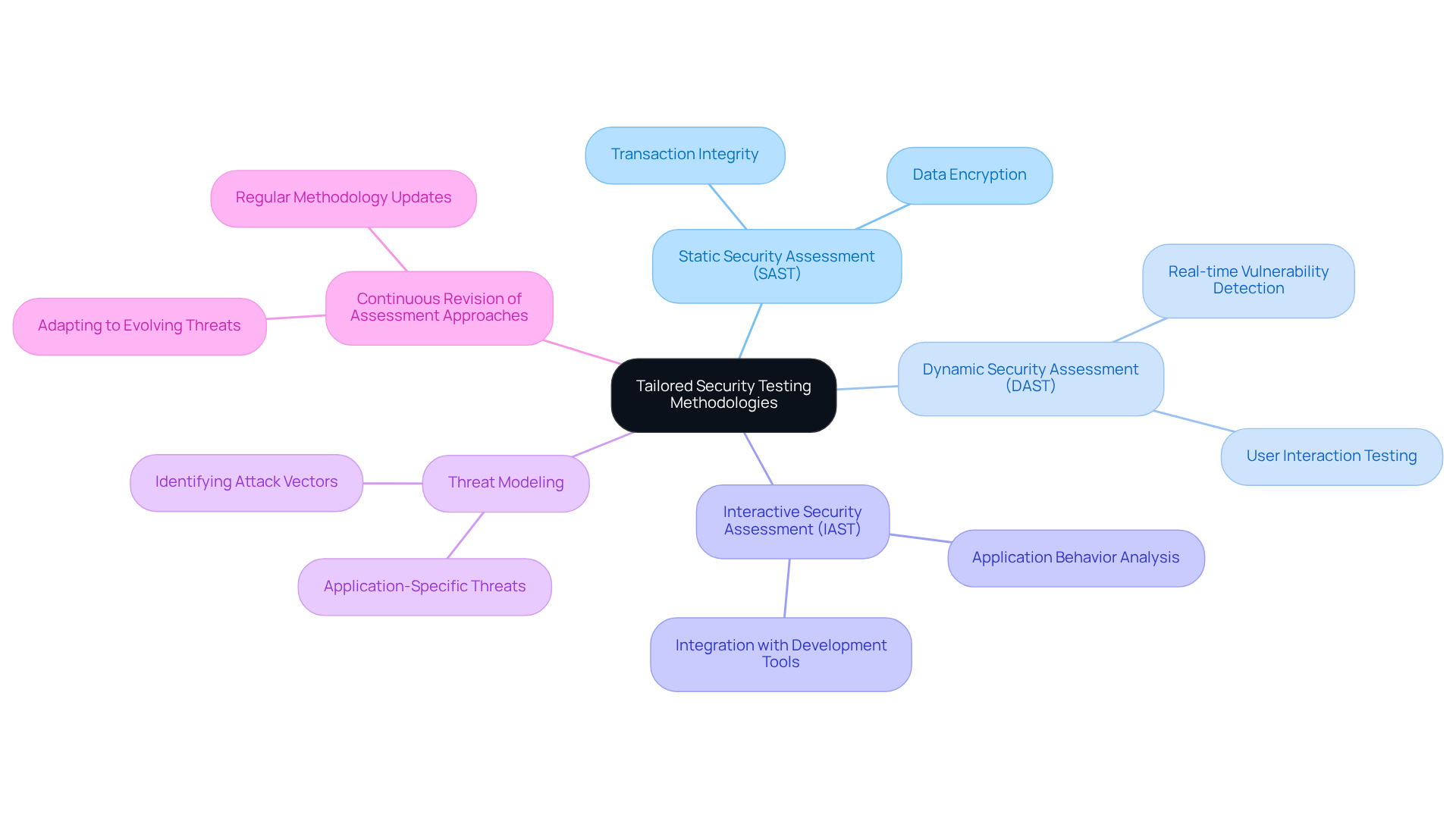
Implement Tailored Security Testing Methodologies
To effectively safeguard systems in regulated sectors, organizations must adopt customized assessment methodologies. This approach involves a combination of:
- Static security assessment (SAST)
- Dynamic security assessment (DAST)
- Interactive security assessment (IAST)
to comprehensively address potential vulnerabilities. For example, a financial services program may necessitate specific tests aimed at ensuring transaction integrity and data encryption.
Moreover, integrating threat modeling into the evaluation process is crucial, as it aids in identifying potential attack vectors that are specific to the application. It is also essential to consistently revise assessment approaches to reflect the evolving threat environment, thereby maintaining robust protection.
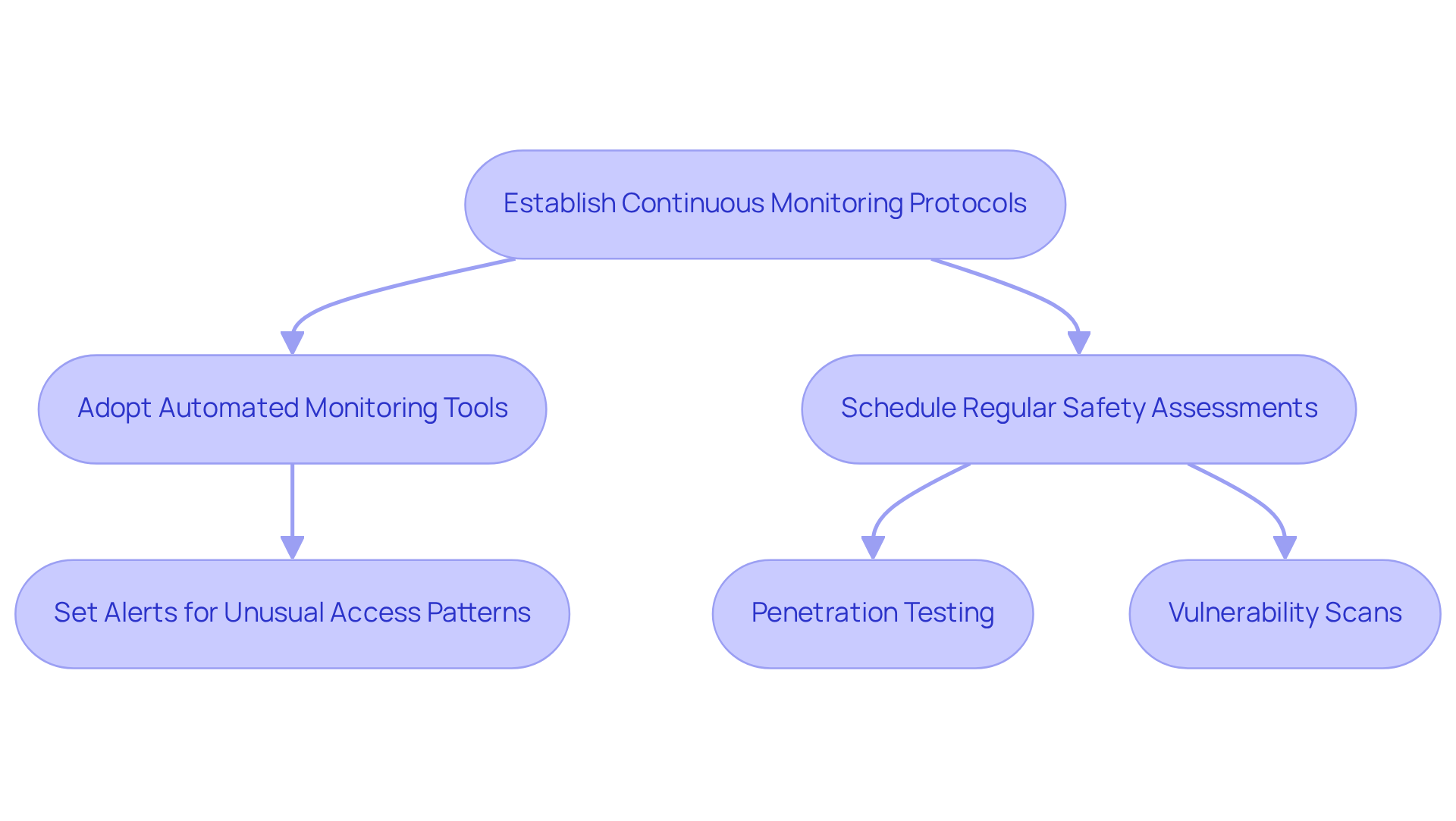
Establish Continuous Monitoring and Assessment Protocols
Ongoing monitoring is essential for the timely identification and resolution of threats. Organizations must adopt automated monitoring tools capable of detecting anomalies and potential breaches as they arise. This process includes:
- Establishing alerts for unusual access patterns or data transfers.
- Scheduling regular safety assessments, such as penetration testing and vulnerability scans, which are part of software testing security, to evaluate the effectiveness of existing protective measures.
For example, a healthcare application necessitates continuous monitoring of patient data access to ensure compliance with HIPAA regulations. By fostering an environment of ongoing evaluation, organizations can swiftly respond to emerging threats and maintain a robust protective posture.
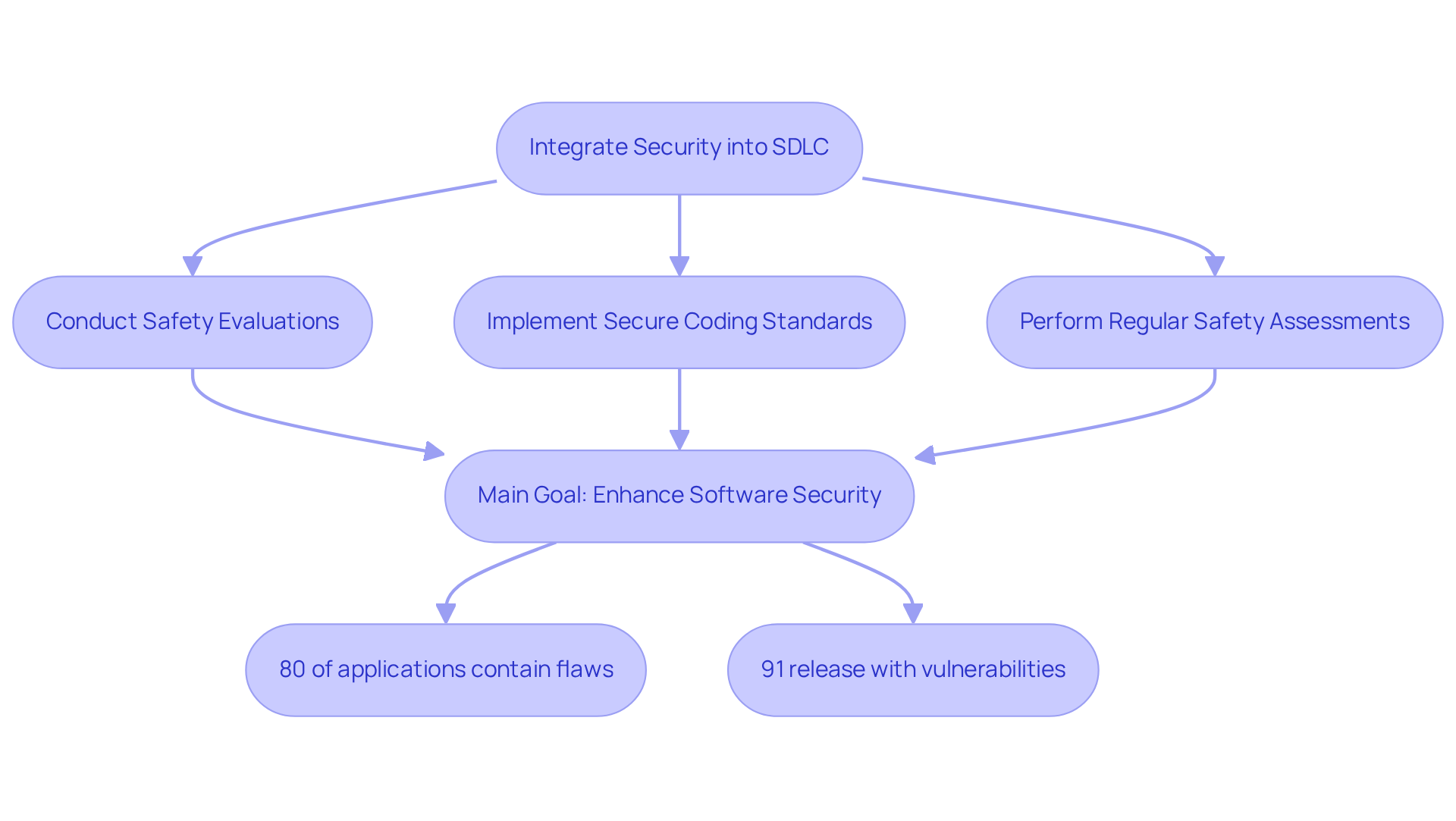
Integrate Security into the Software Development Lifecycle
Incorporating software testing security into the software development lifecycle (SDLC) is essential for ensuring that safety considerations are integrated from the outset. Adopting a DevSecOps methodology enables organizations to enhance software testing security by embedding security into every phase of development, from planning to deployment. Key practices include:
- Conducting thorough safety evaluations during the design phase
- Implementing secure coding standards
- Performing regular safety assessments throughout the development process
For instance, utilizing automated testing tools within CI/CD pipelines facilitates the early detection of vulnerabilities, significantly reducing the costs and efforts associated with addressing them later.
Recent statistics reveal that:
- 80% of applications contain at least one flaw
- 91% of software organizations release products with known vulnerabilities
By cultivating a culture focused on software testing security, organizations can enhance their software’s resilience against evolving threats, ultimately improving compliance and trust within regulated industries. As Krzysztof Sajna, a Senior Engineering Manager, notes, “Addressing safety concerns during the development process is far simpler than making costly adjustments afterward.”
Moreover, the EU NIS 2 directive requires a formal, documented SSDLC process, underscoring the regulatory compliance obligations that are particularly relevant for hedge fund managers. Organizations must also be aware of common pitfalls when implementing a DevSecOps approach, such as the urgency to release software quickly, which can inadvertently introduce vulnerabilities into the system. The cyberattack on Jaguar Land Rover serves as a stark reminder of the tangible consequences of neglecting software testing security in the SDLC, costing the British economy over $2 billion and affecting approximately 5,000 organizations. By integrating security early in the development process, firms can mitigate risks and enhance the overall quality of their software.
Conclusion
Ensuring robust software testing security in regulated industries transcends mere compliance; it is essential for protecting sensitive data and maintaining stakeholder trust. By comprehending and applying best practices tailored to specific regulatory frameworks, organizations can significantly bolster their security posture and mitigate risks linked to software vulnerabilities.
This article delineates four fundamental practices:
- Understanding regulatory compliance requirements
- Adopting tailored security testing methodologies
- Establishing continuous monitoring protocols
- Integrating security throughout the software development lifecycle
Each of these components is crucial in formulating a comprehensive security strategy that addresses both current and emerging threats while ensuring adherence to regulations such as PCI-DSS, HIPAA, and GDPR.
The importance of these practices extends beyond compliance; they are vital for cultivating a security-oriented culture within organizations. By prioritizing software testing security, organizations not only shield themselves from potential breaches but also enhance their reputation and reliability in the eyes of clients and regulatory bodies. Embracing these best practices will pave the way for a more secure future in software development, ensuring that compliance and security are inextricably linked in regulated industries.
Frequently Asked Questions
Why is understanding regulatory compliance requirements important in regulated industries?
Understanding regulatory compliance requirements is crucial in regulated industries such as finance and healthcare because it dictates how data must be handled, stored, and protected.
What are some examples of regulations that organizations need to comply with?
Examples of regulations include PCI-DSS, HIPAA, and GDPR.
What steps should organizations take to ensure compliance in their software evaluation processes?
Organizations should conduct a thorough analysis of applicable regulations, identify key compliance metrics, and integrate them into their evaluation framework.
What specific considerations must financial organizations keep in mind regarding compliance?
Financial organizations must ensure their systems can withstand rigorous evaluations and demonstrate adherence to protective procedures.
How can organizations enhance their understanding and implementation of compliance requirements?
Regular training sessions for development and evaluation teams on compliance updates can significantly enhance understanding and implementation.
